The digital transformation has revolutionized industries across the globe, bringing unprecedented connectivity and efficiency. At the heart of this revolution lie Operational Technology (OT) and Internet of Things (IoT) systems, the unsung heroes powering our nation’s critical infrastructure. From keeping the lights on and water flowing to ensuring smooth transportation and manufacturing, these systems are the bedrock of our economy and public safety. However, as connectivity expands, so does the attack surface, introducing a new era of cyber-physical risks. This article delves into 10 critical OT and IoT systems that are particularly vulnerable to cyber attacks, highlighting why these often-overlooked components demand urgent attention from boardrooms to control rooms.
The Invisible Battleground: Why OT and IoT Security is Paramount
For years, cybersecurity discussions in executive boardrooms predominantly focused on safeguarding IT networks, cloud infrastructure, and enterprise data. While these remain crucial, a more insidious threat lurks deeper within our industrial ecosystems: the vulnerabilities of Level 0 and Level 1 devices within OT and IoT environments. These are not your typical servers or workstations; they are the sensors, relays, drives, actuators, and embedded controllers that directly interact with physical processes, effectively controlling the real world.
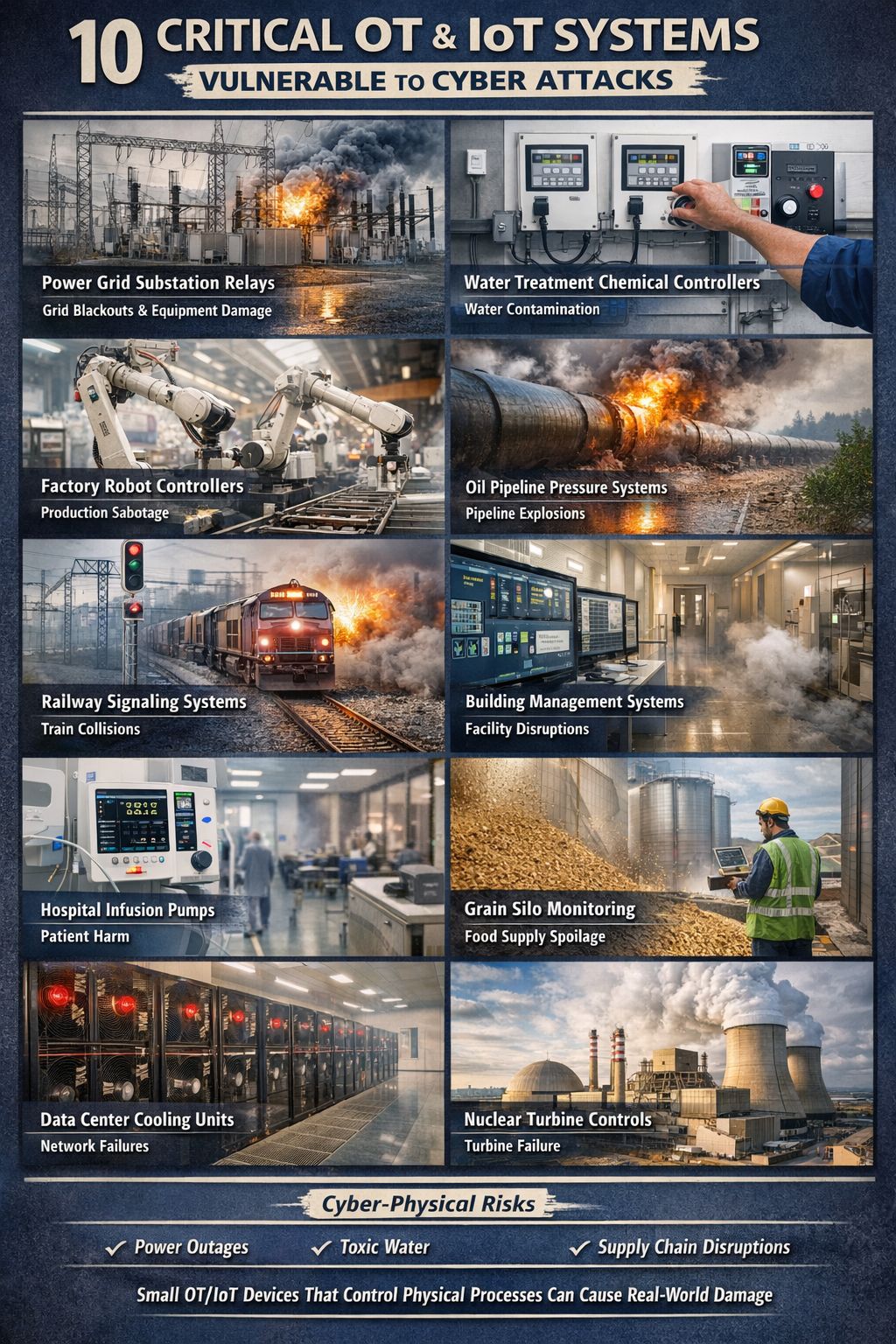
The image provided starkly illustrates the potential consequences of neglecting these often “invisible” devices. When these components, many of which were never designed with cybersecurity in mind, are compromised, the result isn’t merely a data breach. It’s a physical event—power outages, pipeline ruptures, water contamination, supply chain disruptions, and even industrial equipment destruction. The severity of these potential outcomes underscores the urgent shift in perspective required for modern cybersecurity strategies: it’s no longer just about protecting data; it’s about protecting physics.
The Accelerating Threat Landscape for OT and IoT
The security landscape for Operational Technology (OT) and Industrial Control Systems (ICS) is evolving rapidly and becoming increasingly dangerous. Recent reports indicate a significant rise in cyber incidents targeting these critical environments. A 2025 report highlights a 146% increase in sites suffering physical impairment due to cyber attacks in 2024 compared to 2023, with the number of affected sites jumping from 412 to 1,015. Moreover, nation-state attacks with physical consequences tripled in 2024, demonstrating a clear escalation in sophisticated threats. This trend is further supported by observations that OT-focused attacks increased by over 65% in 2024 alone, with 42% of companies experiencing at least one ICS disruption due to a cyber incident.
A key driver of this heightened vulnerability is the prevalence of legacy equipment that operates on “insecure-by-design” protocols, lacking fundamental security features like authentication and encryption. These systems, often decades old, were built in an era of perceived isolation, where physical security was the primary defense. Today, as digital transformation connects these systems to broader enterprise IT networks, cloud systems, remote access pathways, and the Industrial IoT (IIoT), their inherent weaknesses become critical attack vectors. The OT:ICEFALL disclosures, for example, revealed 56 vulnerabilities stemming from these insecure-by-design practices in devices from 10 OT vendors, affecting systems like Distributed Control Systems (DCS), Programmable Logic Controllers (PLC), and Remote Terminal Units (RTU).
The consequences are dire. Modern ransomware groups such as LockBit, Black Basta, and Play are now primarily targeting OT systems, moving beyond mere data theft to directly impact physical operations. The increase in zero-day vulnerabilities in PLCs, HMIs, and gateways, often driven by nation-state actors, further complicates the defensive efforts. This confluence of factors underscores why visibility and protection down to Level 0/1 devices are no longer optional for critical infrastructure operators.
The Top 10 Vulnerable OT and IoT Systems
The visual highlights ten specific categories of OT and IoT systems that are particularly susceptible to cyber attacks, each with the potential for catastrophic real-world consequences. Understanding these vulnerabilities is the first step toward robust cyber-physical security.
1. Power Grid Substation Relays: The Linchpin of Electrical Distribution
Function: Substation relays are critical components within electrical grids, designed to detect faults and initiate protective actions, such as opening circuit breakers to isolate a faulty section of the grid. They are the guardians of power flow, preventing cascading failures and equipment damage. Many of these rely on legacy protocols that lack modern security features.
Cyber Attack Scenario: A compromised substation relay could be manipulated to incorrectly trip circuit breakers, leading to localized or widespread power outages. Attackers might also prevent relays from functioning correctly during genuine grid faults, leading to extensive equipment damage from sustained overcurrents or voltage imbalances. The Stuxnet malware, though not directly targeting relays, demonstrated the potential to manipulate individual components to cause physical damage, providing a conceptual blueprint for such attacks. The image depicts a power substation engulfed in flames, a stark visualization of the havoc a cyber attack on these relays could wreak.
Real-world Impact: Grid blackouts, extensive equipment damage, economic disruption, and loss of essential services (e.g., hospitals, emergency services) reliant on a stable power supply.
2. Water Treatment Chemical Controllers: Safeguarding Public Health
Function: These controllers precisely manage the dosage of chemicals, like chlorine or fluoride, into public water supplies to ensure safety and potability. They regulate pumps, monitor levels, and adjust flow rates based on real-time data from sensors.
Cyber Attack Scenario: An attacker could gain control over these systems to alter chemical concentrations. This could involve either reducing essential chemical levels, leading to contamination and potential spread of waterborne diseases, or increasing them to dangerous, toxic levels, directly harming the population. The image shows a technician adjusting a control panel, symbolizing the precise yet vulnerable nature of these systems.
Real-world Impact: Widespread water contamination, public health emergencies, panic, costly remediation efforts, and loss of public trust in essential services. Attacks on Emerson’s Ovation and ControlWave systems, identified in the OT:ICEFALL vulnerabilities, highlight the exposure of such critical infrastructure components.
3. Factory Robot Controllers: The Silent Saboteurs of Production
Function: Factory robot controllers orchestrate the precise movements and actions of industrial robots on manufacturing lines. They are central to automated production processes, ensuring accuracy, speed, and efficiency.
Cyber Attack Scenario: Malicious actors could reprogram robot controllers to perform erroneous or destructive actions. This might include damaging products, misaligning components, causing robots to collide with each other or human workers, or even rendering entire production lines inoperable. The image of robotic arms in a factory setting, with the overlay of “Production Sabotage,” clearly illustrates this threat.
Real-world Impact: Production stoppage, significant financial losses due to damaged equipment and products, reputational damage, supply chain disruptions, and potential physical harm to personnel.
4. Oil Pipeline Pressure Systems: Explosive Risks from Digital Compromise
Function: These systems monitor and regulate the pressure within oil and gas pipelines, ensuring safe and efficient transportation of hydrocarbons. They utilize various sensors and control valves to maintain optimal flow and prevent dangerous pressure fluctuations.
Cyber Attack Scenario: An attacker could manipulate pressure readings or directly control valves to create dangerous pressure imbalances. This could lead to pipeline ruptures, explosions, and significant environmental damage. The image of a flaming pipeline illustrates the catastrophic physical consequences.
Real-world Impact: Pipeline explosions, environmental disasters (oil spills), loss of life, severe economic disruption, and massive cleanup and repair costs. Flat network architectures, common in OT environments, allow attackers to move laterally and compromise such critical systems once a foothold is gained.
5. Railway Signaling Systems: The Digital Keys to Safe Transit
Function: Railway signaling systems are the backbone of safe and efficient rail transportation. They control train movements, track switches, and provide vital speed and status information to train operators, preventing collisions and ensuring operational integrity.
Cyber Attack Scenario: A compromise of signaling systems could lead to catastrophic train collisions by manipulating signals to give false clearances, switching tracks incorrectly, or disabling safety interlocks. Attackers could also cause widespread delays and gridlock across the rail network. The image depicts a train collision in progress, highlighting the potential for mass casualties and destruction.
Real-world Impact: Train collisions, mass casualties, extensive infrastructure damage, major transportation disruptions, and severe economic consequences.
6. Building Management Systems (BMS): The Nerve Center of Modern Structures
Function: Building Management Systems integrate and control various building services, including HVAC (heating, ventilation, and air conditioning), lighting, security access, elevators, and fire suppression systems. They are crucial for maintaining comfortable, safe, and energy-efficient building operations. Honeywell’s building controllers, for instance, have been identified with vulnerabilities.
Cyber Attack Scenario: An attacker could gain control over a BMS to disrupt critical services. This could involve shutting down HVAC in a data center, leading to server overheating and network failures; disabling security systems, allowing unauthorized access; or even manipulating fire suppression systems. The image shows a modern control room, symbolizing the centralized control these systems offer and their vulnerability.
Real-world Impact: Facility disruptions, data center failures, compromise of physical security, energy waste, occupant discomfort, and potential safety hazards. Critical vulnerabilities have been found in widely deployed building automation frameworks like Johnson Controls/Tridium Niagara and ABB’s Cylon ASPECT, NEXUS, MATRIX, allowing for full system compromise.
7. Hospital Infusion Pumps: Direct Threats to Patient Life
Function: Hospital infusion pumps are highly precise medical devices used to deliver fluids, medications, and nutrients into a patient’s body in controlled amounts. They are vital for critical patient care, from pain management to chemotherapy.
Cyber Attack Scenario: A cyber attack on networked infusion pumps could allow an attacker to alter dosage rates, leading to under-dosing or, more critically, over-dosing, which could result in severe patient harm or even death. The image of an infusion pump next to a hospital bed, with “Patient Harm” as the risk, is a chilling reminder of these stakes.
Real-world Impact: Direct patient harm, loss of life, medical malpractice lawsuits, damage to hospital reputation, and widespread panic within healthcare systems. The increasing connectivity of medical devices, often treated as IoT, introduces significant security challenges.
8. Grain Silo Monitoring Systems: Protecting Our Food Supply
Function: Grain silo monitoring systems continuously track environmental conditions such as temperature, humidity, and moisture levels within large grain storage facilities. These parameters are crucial for preventing spoilage, infestation, and spontaneous combustion.
Cyber Attack Scenario: An attacker could manipulate sensor data, causing operators to believe conditions are safe when in fact they are deteriorating. This could lead to massive spoilage of stored grain, affecting agricultural supplies and potentially impacting the global food chain. Alternatively, an attacker could trigger conditions that lead to fires or explosions in silos. The image depicts a worker with a laptop overlooking vast grain silos, highlighting the reliance on these monitoring systems.
Real-world Impact: Food supply spoilage, significant economic losses for agricultural industries, food shortages, and potential humanitarian crises.
9. Data Center Cooling Units: The Keepers of the Digital Realm
Function: Data center cooling units are fundamental to maintaining the optimal temperature and humidity within server halls. Without efficient cooling, servers overheat, leading to component failure, data loss, and network outages.
Cyber Attack Scenario: A compromise of these cooling units could lead to them being shut down or operated inefficiently. This would cause critical server infrastructure to overheat, resulting in widespread network failures, data loss, and significant downtime for various digital services. The image shows rows of cooling units within a data center, emphasizing their critical role.
Real-world Impact: Network failures, data loss, extensive downtime for cloud services and enterprise applications, significant financial losses, and reputational damage for affected organizations. Honeywell has had multiple high-severity vulnerabilities in products like Experion PKS and PlantCruise which could lead to network access or even remote code execution.
10. Nuclear Turbine Controls: The Ultimate High-Stakes Target
Function: Nuclear turbine controls are responsible for managing the steam turbines that generate electricity in nuclear power plants. These systems are highly regulated and critical for safe and stable power generation, operating under strict safety protocols.
Cyber Attack Scenario: While nuclear power plants have extensive defensive layers, a successful attack on turbine controls could potentially lead to a turbine failure event. This wouldn’t necessarily cause a nuclear meltdown due to multiple safety systems, but it could result in severe damage to the plant, prolonged shutdowns, and significant financial and energy supply disruption. The image shows a nuclear power plant with smoke stacks, indicating the energy generation and inherent risks.
Real-world Impact: Turbine failure, prolonged plant shutdown, massive financial losses, energy supply disruptions, and potential public fear and anxiety, even if direct nuclear safety is maintained. Attacks on critical industrial embedded devices from vendors like Emerson (PACSystem and Ovation) have shown the potential for sabotage within energy sectors.
The Overlooked Depths: Level 0 and Level 1 Devices
The recurring theme across these ten vulnerabilities is the focus on devices often considered “deeper” in the system—the Level 0 and Level 1 devices. These are the embedded controllers, sensors, and actuators that directly interface with the physical world. Cyber-physical systems theory categorizes these as follows:
- Level 0: The Physical Process: This level represents the actual physical processes and equipment, such as turbines, valves, pumps, and motors.
- Level 1: Intelligent Devices & I/O: This level consists of the sensors (e.g., temperature, pressure, flow), actuators (e.g., motor drivers, valve positioners), and intelligent devices like PLCs (Programmable Logic Controllers) and RTUs (Remote Terminal Units) that directly monitor and control the Level 0 physical processes. They are the immediate interface between the digital and physical realms.
Joe Weiss PE CISM CRISC ISA Fellow, a recognized OT security expert, has repeatedly warned that many of the most dangerous vulnerabilities reside within these lower levels. Why? Because these devices were often engineered for reliability and function in isolated environments, not with sophisticated cyber-defenses. They typically:
- Lack inherent security features: No strong authentication, encryption, or logging capabilities. Protocols like Modbus, DNP3, and PROFINET were built when isolation was the primary security measure.
- Are “invisible” to traditional IT security: They often fall outside asset inventories and are not monitored by standard security tools, making them blind spots.
- Cannot support modern security controls: Their limited processing power, memory, and specialized operating systems prevent the installation of agents or complex security software.
- Are designed for longevity, not rapid updates: The operational imperative of critical infrastructure means these devices might run for decades without modification, making patching extremely difficult or impossible without significant downtime.
- Provide direct physical control: A compromise at this level directly translates into a physical command, bypassing higher-level security layers that might be in place.
When these devices are compromised, the impact is not just data theft; it’s tangible, physical, and potentially life-threatening.
Addressing the Challenge: Visibility, Protection, and Executive Action
Given the severe impact of cyber-physical attacks, protecting critical infrastructure demands a proactive and comprehensive approach that extends beyond traditional IT cybersecurity. Executives responsible for these critical operations must ask fundamental questions:
- Do we have a complete inventory of our OT systems, including level 0/1 devices?
A complete and accurate asset inventory is the foundational step for any robust cybersecurity program. For OT and IIoT, this means identifying every connected device, its function, location, vendor, firmware version, and network connections—especially the Level 0/1 devices that often go uncataloged. Without this visibility, it’s impossible to understand the attack surface or implement targeted defenses. Traditional IT asset management tools often cannot discover or properly categorize these specialized industrial devices.
- Can these devices be remotely manipulated or spoofed?
Many legacy OT protocols lack authentication and integrity checks, making them susceptible to manipulation or spoofing. An attacker who gains network access to an OT segment might be able to send malicious commands to a PLC or sensor, or impersonate a legitimate device, with devastating physical consequences. Understanding these capabilities is vital for assessing risk and implementing protective measures like network segmentation, unidirectional gateways, and protocol anomaly detection.
- What happens to our physical process if one of these devices fails or is intentionally altered?
This question encourages a shift from a purely digital threat model to a cyber-physical one. It requires incident response planning that considers not just data recovery, but also the physical impact, safety implications, and operational continuity of a compromised system. This involves developing mitigation strategies for physical events, understanding interdependencies, and performing tabletop exercises to simulate these unique scenarios.
Essential Strategies for Safeguarding Critical OT and IoT
- Comprehensive Asset Inventory: Implement specialized OT/IIoT asset discovery and inventory solutions to gain full visibility into all devices, including Level 0/1, their configurations, and network connections.
- Network Segmentation: Break down flat OT networks into smaller, isolated segments using firewalls and unidirectional gateways. This limits lateral movement for attackers and prevents IT-to-OT and OT-to-OT compromises.
- Secure Remote Access: Implement strong authentication, least privilege, and multi-factor authentication for all remote access points to OT networks. Using hardware-enforced remote access can significantly enhance security.
- Vulnerability Management: Regularly identify and assess vulnerabilities in OT and IIoT devices, including those highlighted in reports like OT:ICEFALL. Prioritize patching where possible, and implement compensating controls for unpatchable legacy systems.
- Anomaly Detection and Continuous Monitoring: Deploy intrusion detection systems (IDS) specifically designed for OT protocols to monitor for unusual behavior, malicious commands, and deviations from normal operating parameters.
- Secure-by-Design Principles: For new deployments or system upgrades, prioritize vendors and solutions that incorporate security by design, including secure boot, encrypted communications, and robust authentication.
- Personnel Training and Awareness: Educate OT engineers and IT security teams on the unique threats and best practices for securing cyber-physical systems.
- Incident Response and Recovery Planning: Develop specific incident response plans for cyber-physical attacks, including procedures for safely shutting down processes, isolating affected components, and restoring operations, with a strong focus on physical safety.
- Threat Intelligence Sharing: Participate in industry-specific information sharing and analysis centers (ISACs) to stay informed about emerging threats and attack methodologies targeting critical infrastructure.
- Regulatory Compliance: Adhere to and exceed relevant industry standards and regulatory requirements (e.g., NERC-CIP, ISA/IEC 62443) to ensure a baseline of security measures.
The Future of Critical Infrastructure Security
The reality is simple: protecting critical infrastructure in the interconnected age requires a profound understanding of the vulnerabilities lurking in our OT and IoT systems. As observed in recent years, the number of successful OT cyber attacks with physical consequences, as well as the number of impacted sites, is on an alarming upward trajectory. The distinction between IT and OT security must vanish, replaced by a holistic cyber-physical security strategy. Organizations that grasp this truth first, and act decisively, will be the ones capable of preventing the next major cyber-physical incident.
The integrity of our industrial operations, the safety of our communities, and the stability of our economies depend on it. This is not merely an IT problem; it is an enterprise-wide imperative demanding board-level attention and C-suite leadership. The threats are real, the consequences are severe, and the time to act is now.
Is your organization equipped to prevent the next major cyber-physical incident? Do you have full visibility into your Level 0 and Level 1 OT and IoT devices? Let IoT Worlds help you navigate the complexities of securing your critical infrastructure. Our experts specialize in identifying, assessing, and mitigating vulnerabilities in operational technology and industrial IoT environments. Reach out to us today to schedule a consultation and fortify your defenses against the escalating cyber-physical threats.
Email us at info@iotworlds.com to protect your physical processes from digital compromise.