In the intricate landscape of modern cybersecurity, a paradigm shift is underway. The traditional, tool-centric approach to security operations is giving way to a more dynamic, workflow-centric methodology. High-performing security operations centers (SOCs) are no longer defined by the sheer number of security tools they deploy, but rather by how seamlessly these tools integrate to facilitate efficient and effective workflows. This evolution is driven by the imperative to keep pace with an ever-growing volume and sophistication of cyber threats, while simultaneously combating issues like alert fatigue and resource constraints. The answer lies in the synergistic integration of three foundational pillars: the Security Operations Center (SOC), Security Information and Event Management (SIEM), and Security Orchestration, Automation, and Response (SOAR). Together, these three elements form an end-to-end flow, creating a robust framework for detecting, analyzing, and responding to cyber threats with unprecedented speed and precision.
This comprehensive guide will delve into each of these critical components, explaining their individual roles, core functionalities, and how their integration forms the backbone of a truly modern security architecture. We will explore the human intelligence layer of the SOC, the visibility and detection core provided by SIEM, and the automation and orchestration engine that SOAR represents. Finally, we will examine the tangible outcomes and benefits of this unified approach, emphasizing how it leads to reduced Mean Time to Detect (MTTD), Mean Time to Respond (MTTR), minimized analyst fatigue, standardized incident handling, and ultimately, a significantly improved overall security posture defined by enhanced maturity.
The Foundation: Understanding the “Big Three”
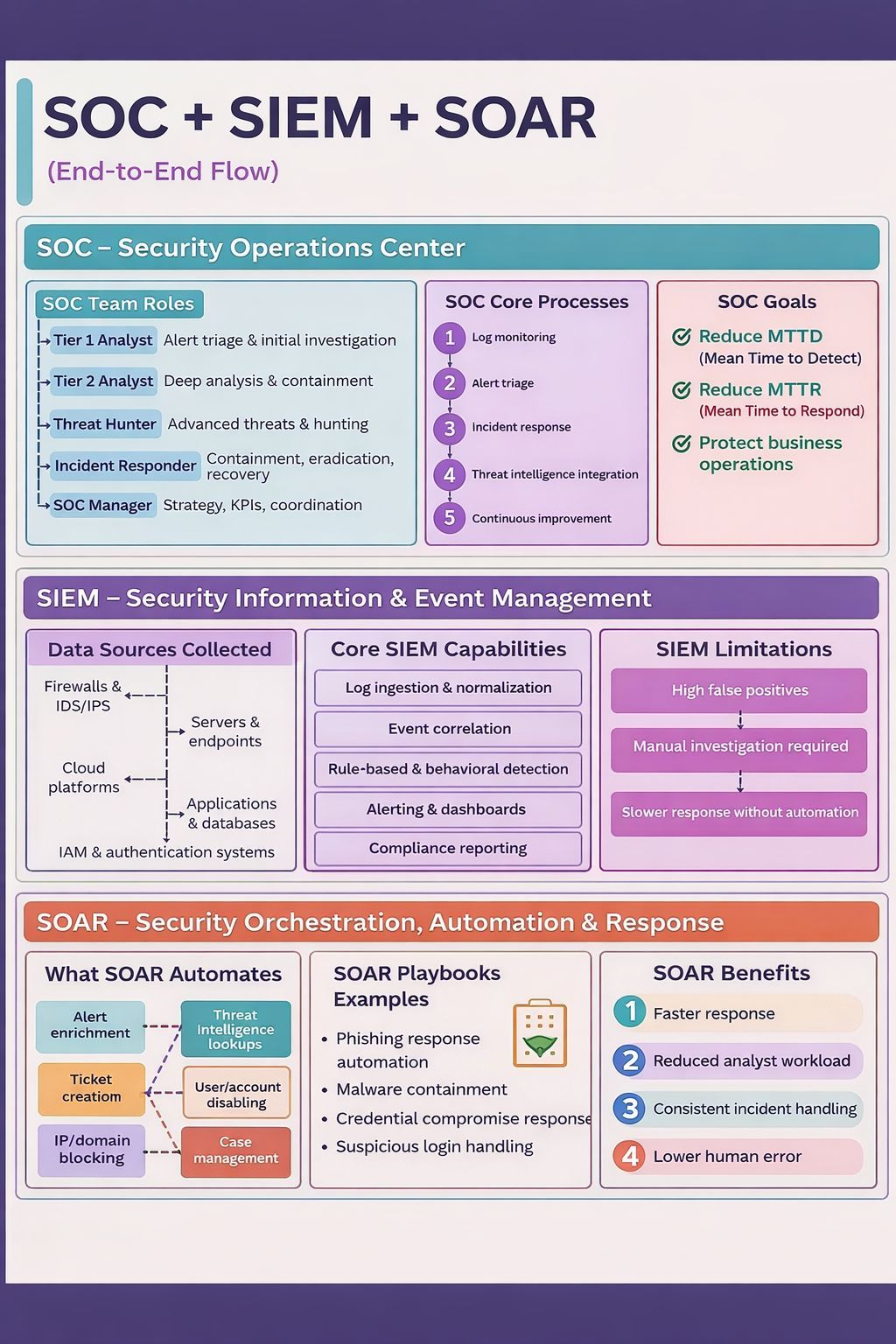
Before diving into the specifics of each component, it’s crucial to grasp the overarching relationship between SOC, SIEM, and SOAR. While often discussed in the same breath, they serve distinct yet complementary functions. Think of it this way: the SOC is the brain and nervous system, the SIEM is the eyes and ears, and SOAR is the hands and reflexes. Without one, the others cannot operate at their full potential.
- SOC (Security Operations Center): This is the organizational entity – the team of dedicated security professionals, processes, and technology – responsible for continuously monitoring an organization’s security posture, identifying and analyzing threats, and orchestrating appropriate responses. It’s the human intelligence layer that transforms raw security data into actionable decisions.
- SIEM (Security Information and Event Management): This is the technological bedrock, a centralized platform designed to aggregate, normalize, and correlate security event data from various sources across an organization’s IT infrastructure. It provides comprehensive visibility and acts as the primary detection engine, identifying potential security incidents.
- SOAR (Security Orchestration, Automation, and Response): This is the intelligent automation layer that operationalizes and accelerates incident response. It integrates disparate security tools, automates repetitive tasks, and orchestrates complex workflows (known as playbooks) to streamline the entire incident management lifecycle.
The power of this combination lies in its ability to create a security ecosystem where human expertise, data-driven insights, and intelligent automation work in concert. A common misconception treats these components as interchangeable or alternative solutions, leading to costly mistakes and a false sense of security. Organizations that understand these critical distinctions are better positioned to make informed investment decisions and build resilient cybersecurity strategies.
The Human Intelligence Layer: The Security Operations Center (SOC)
At the heart of any effective cybersecurity strategy is the Security Operations Center (SOC). More than just a room full of screens, a SOC is a dedicated team of security professionals, defined processes, and supporting technologies working in concert to proactively monitor, detect, analyze, and respond to cyber threats. It’s the nerve center where human intelligence transforms raw security data into actionable decisions and containment strategies.
What is a SOC? The People, Processes, and Technology
A SOC is primarily an organization, a team of individuals equipped with the expertise to safeguard an organization’s digital assets. It’s a structured unit focused on 24/7 surveillance of an organization’s security posture. This involves a continuous cycle of threat monitoring, vulnerability management, incident detection, and response coordination. The processes within a SOC are meticulously designed to ensure consistency, efficiency, and adherence to best practices in cybersecurity. These processes define how alerts are handled, how investigations are conducted, and how incidents are formally managed from detection to resolution. While technology is undeniably crucial, it serves as an enabler for the people and processes within the SOC. Without skilled analysts and well-defined workflows, even the most advanced security tools yield limited value.
SOC Team Roles: Specialization for Effectiveness
A high-performing SOC typically comprises a multi-tiered team, with each role playing a vital part in the security workflow. This specialization ensures that alerts are efficiently triaged, thoroughly investigated, and effectively responded to.
Tier 1 Analyst: The First Line of Defense
The Tier 1 Analyst is the initial point of contact for security alerts. Their primary responsibility involves alert triage and initial investigation. This includes:
- Monitoring security dashboards and alerts: Continuously keeping an eye on incoming alerts from various security tools, including the SIEM.
- Initial assessment: Determining the legitimacy and severity of an alert based on established protocols and available context.
- Basic data collection: Gathering initial information related to the alert, such as source and destination IPs, usernames, and event timestamps.
- Escalation: Escalating confirmed or suspicious alerts to Tier 2 analysts for deeper investigation.
The goal of the Tier 1 analyst is to quickly filter out false positives and identify genuine threats that warrant further attention, thereby reducing the burden on higher-tier analysts.
Tier 2 Analyst: Deep Dive and Containment
When an alert is escalated from Tier 1, it lands in the hands of a Tier 2 Analyst. This role demands a deeper understanding of security incidents and more advanced analytical skills. Their responsibilities include:
- Deep analysis: Conducting in-depth investigations into escalated alerts, utilizing a wider range of security tools and threat intelligence.
- Attack chain mapping: Understanding the progression of an attack and identifying all affected systems.
- Containment strategies: Formulating and sometimes executing initial containment measures to prevent further spread of an attack.
- Evidence collection: Meticulously collecting and preserving evidence for forensic analysis and post-incident review.
Tier 2 analysts are critical for moving beyond initial detection to understanding the scope and impact of an incident.
Threat Hunter: Proactive Defense
Threat Hunters represent a more proactive and specialized role within the SOC. Unlike analysts who react to alerts, threat hunters actively search for hidden threats that may have evaded existing security controls. Their work involves:
- Proactive search: Employing advanced techniques and tools to hunt for indicators of compromise (IOCs) and indicators of attack (IOAs) within the network.
- Hypothesis testing: Developing hypotheses about potential threats and using data to prove or disprove them.
- Utilizing threat intelligence: Leveraging the latest threat intelligence to identify emerging attack vectors and adversary tactics.
- Developing new detections: Creating new rules and signatures for the SIEM and other security tools based on their findings.
Threat hunting is a crucial component of a mature SOC, helping to uncover sophisticated and persistent threats before they can cause significant damage.
Incident Responder: The Crisis Manager
The Incident Responder takes charge when an active security incident has been confirmed. Their primary focus is on minimizing the impact of the incident and restoring operations. Key responsibilities include:
- Containment: Implementing measures to stop the spread of the attack and isolate affected systems.
- Eradication: Removing the threat from the environment, including malware, malicious configurations, and unauthorized access.
- Recovery: Restoring affected systems and data to their pre-incident state, ensuring business continuity.
- Post-incident analysis: Documenting the incident, lessons learned, and recommending improvements to prevent recurrence.
Incident responders are often on the front lines during a crisis, requiring calm under pressure and decisive action.
SOC Manager: Orchestrating the Entire Operation
The SOC Manager oversees the entire Security Operations Center. This leadership role is responsible for the strategic direction, operational efficiency, and overall effectiveness of the SOC. Their duties include:
- Strategy development: Defining the SOC’s mission, vision, and long-term goals in alignment with the organization’s overall security strategy.
- KPIs and metrics: Establishing and tracking key performance indicators (KPIs), such as MTTD and MTTR, to measure SOC performance.
- Team coordination: Managing and motivating the SOC team, ensuring clear communication and collaboration.
- Technology oversight: Selecting, implementing, and optimizing security tools and platforms used by the SOC.
- Stakeholder communication: Reporting to senior management on security posture, incidents, and strategic initiatives.
The SOC Manager is crucial for ensuring that the SOC operates as a cohesive and high-performing unit.
SOC Core Processes: The Engine of Security Operations
Beyond the individual roles, the SOC operates on a set of well-defined core processes that ensure a systematic and effective approach to cybersecurity.
1. Log Monitoring: The Foundation of Visibility
At the absolute base of all SOC activity is log monitoring. This involves the continuous collection and review of logs generated by virtually every device, application, and system within an organization’s network. Logs provide a forensic trail of activity, offering crucial insights into what is happening across the IT environment. Effective log monitoring is the first step towards detecting anomalies and potential security incidents.
2. Alert Triage: Filtering the Noise
Given the sheer volume of logs and potential alerts, robust alert triage is essential. This process involves swiftly evaluating incoming alerts to distinguish between legitimate threats and false positives. Efficient triage prevents alert fatigue among analysts and ensures that critical alerts receive immediate attention. It’s the initial filter that determines the next course of action for any security event.
3. Incident Response: From Detection to Resolution
Incident response is the systematic approach to handling security incidents. It encompasses all stages from initial detection and analysis to containment, eradication, recovery, and post-incident activities. A well-defined incident response plan is critical for minimizing the impact of security breaches and ensuring a timely and effective resolution.
4. Threat Intelligence Integration: Staying Ahead of Adversaries
Threat intelligence involves gathering, processing, and analyzing information about current and emerging cyber threats. Integrating this intelligence into SOC operations enhances the ability to predict, detect, and respond to attacks. It provides context to alerts, helps identify new attack techniques, and refines detection rules, allowing the SOC to stay a step ahead of malicious actors.
5. Continuous Improvement: Evolving with the Threat Landscape
The cybersecurity landscape is constantly evolving, and so too must the SOC. Continuous improvement is a vital process that involves regularly reviewing SOC operations, analyzing incident data, identifying areas for enhancement, and adapting processes and technologies to address new threats and vulnerabilities. This iterative approach ensures the SOC remains effective and resilient over time.
SOC Goals: Driving Toward Security Excellence
The primary objective of a SOC is to minimize risk and protect business operations. This translates into several key measurable goals:
- Reduce MTTD (Mean Time to Detect): This metric measures the average time it takes for a SOC to identify a security incident from the moment it occurs. A lower MTTD indicates a more proactive and efficient detection capability.
- Reduce MTTR (Mean Time to Respond): This metric measures the average time it takes for a SOC to fully resolve a security incident after it has been detected. A lower MTTR signifies a faster and more effective response capability, minimizing the impact of incidents.
- Protect Business Operations: Ultimately, all SOC activities converge on this overarching goal. By efficiently detecting and responding to threats, the SOC safeguards critical business functions, data, and reputation, ensuring operational continuity and resilience.
These goals are intrinsically linked. Achieving lower MTTD and MTTR directly contributes to stronger protection of business operations.
The Visibility & Detection Core: Security Information and Event Management (SIEM)
While the SOC provides the human intelligence layer, the Security Information and Event Management (SIEM) system is the technological powerhouse that fuels its operations. SIEM is the eyes and ears of the SOC, providing the comprehensive visibility and detection capabilities necessary to identify threats across a complex IT environment. It acts as the centralized analytics engine, ingesting, normalizing, correlating, and analyzing vast quantities of security event data.
Data Sources Collected: The Information Nexus
A robust SIEM solution is designed to collect security event data from an incredibly diverse array of sources across an organization’s infrastructure. This extensive data collection is fundamental to achieving a holistic view of the security posture. Key data sources include:
- Firewalls & IDS/IPS: Logs from firewalls (which control network traffic) and Intrusion Detection/Prevention Systems (IDS/IPS, which monitor for malicious activity) provide critical insights into network-level threats and unauthorized access attempts.
- Servers & Endpoints: Logs from servers (both physical and virtual) and endpoint devices (workstations, laptops, mobile devices) offer detailed information about user activity, application execution, and potential malware infections.
- Cloud Platforms: With the increasing adoption of cloud services (IaaS, PaaS, SaaS), logs from cloud environments (e.g., AWS, Azure, Google Cloud) are crucial for monitoring cloud resource access, configuration changes, and compliance.
- Applications & Databases: Application logs provide insights into user interactions, potential exploits, and data access patterns, while database logs track queries, modifications, and access attempts, safeguarding sensitive information.
- IAM & Authentication Systems: Identity and Access Management (IAM) systems and authentication logs are vital for tracking user logins, failed attempts, privilege escalations, and account lockouts, helping to detect unauthorized access and insider threats.
By ingesting data from these varied sources, the SIEM creates a consolidated repository of security information, enabling comprehensive analysis that would be impossible with isolated tools.
Core SIEM Capabilities: Turning Data into Intelligence
Once collected, the SIEM leverages several core capabilities to transform raw log data into actionable security intelligence.
Log Ingestion & Normalization: Speaking a Common Language
The first step after collection is log ingestion, where data is pulled into the SIEM. Crucially, given the disparate nature of log sources, this data needs to be normalized. Normalization involves converting log data from various formats into a common, standardized schema. This makes it possible to compare and correlate events from different systems, regardless of their original log format. Without normalization, correlating events across diverse sources would be an insurmountable challenge.
Event Correlation: Connecting the Dots
Event correlation is the cornerstone of SIEM’s detection capabilities. It involves analyzing relationships between seemingly unrelated events from different data sources to identify patterns that indicate a security incident. For example, a single failed login attempt on its own might not be suspicious, but multiple failed login attempts from a new geographic location, followed by a successful login using different credentials on a different system, could be correlated by the SIEM to flag a potential brute-force attack or credential stuffing. Statistical analysis and algorithms are used to identify these complex relationships.
Rule-Based & Behavioral Detection: Identifying Known and Unknown Threats
SIEM systems employ two primary methods for detecting threats:
- Rule-Based Detection: This involves using predefined rules that specify conditions indicative of malicious activity. For example, a rule might trigger an alert if a specific number of failed login attempts occur within a given timeframe. Rule-based detection is effective for identifying known attack patterns and compliance violations.
- Behavioral Detection: This more advanced capability involves establishing a baseline of normal activity for users, systems, and applications. The SIEM then monitors for deviations from this baseline. For instance, if a user who typically accesses only specific internal resources suddenly attempts to access a large volume of external cloud storage, the SIEM’s behavioral analytics might flag this as anomalous and potentially malicious activity. This helps in detecting zero-day threats and sophisticated attacks that don’t conform to known signatures.
Alerting & Dashboards: Visualizing the Security Landscape
SIEM systems provide robust alerting mechanisms to notify SOC analysts of detected threats in real-time. These alerts can be configured based on severity, source, and destination. Beyond alerts, SIEMs offer customizable dashboards that provide a visual representation of an organization’s security posture. These dashboards present key metrics, incident trends, and aggregated security data, allowing analysts and managers to quickly grasp the overall security status and pinpoint areas of concern.
Compliance Reporting: Meeting Regulatory Requirements
For many organizations, regulatory compliance (e.g., GDPR, HIPAA, PCI DSS) is a significant concern. SIEM solutions assist with compliance by providing detailed logs and reports that demonstrate adherence to specific security controls and policies. They can generate audit trails, access reports, and incident summaries required for regulatory assessments, simplifying the compliance burden.
SIEM Limitations: The Need for Evolution
Despite its powerful capabilities, SIEM is not without its limitations, particularly in the context of rapidly evolving threats and increasing alert volumes. Recognizing these limitations highlights the crucial role SOAR plays in enhancing the overall security architecture.
High False Positives: The Needle in the Haystack Problem
One of the most significant challenges with SIEM is the potential for generating a high volume of false positives. Tuning SIEM rules to be comprehensive can lead to many legitimate activities being flagged as suspicious. This “noise” can overwhelm analysts, making it difficult to identify genuine threats amidst the flood of irrelevant alerts.
Manual Investigation Required: A Time Sink
Even with sophisticated correlation and detection, many SIEM alerts require manual investigation by SOC analysts. This involves gathering additional context, verifying the alert’s legitimacy, and determining the appropriate response. This manual effort is time-consuming and can lead to slower response times, especially for complex incidents.
Slower Response Without Automation: The Gap in Action
While SIEM excels at detection and providing visibility, its inherent design does not include robust automation capabilities for incident response. Without an integrated automation layer, the transition from detection to action is often manual, leading to a slower Mean Time to Respond (MTTR). This delay can be critical in the face of fast-moving threats, where every minute counts in minimizing damage. This limitation underscores the necessity of SOAR.
The Automation & Orchestration Engine: Security Orchestration, Automation, and Response (SOAR)
In the modern security landscape, where alert volumes are astronomical and threats evolve at breakneck speed, relying solely on human intervention for every security event is unsustainable. This is where Security Orchestration, Automation, and Response (SOAR) steps in as the indispensable third pillar. SOAR is the force multiplier that operationalizes response, acting as the intelligent automation layer that connects disparate security tools and accelerates the entire incident management lifecycle. While SIEM provides the “eyes” for detection, SOAR provides the “hands” and “reflexes” for swift and consistent action.
What is SOAR? A Paradigm Shift in Incident Response
SOAR is a platform and a methodology designed to integrate security tools, automate repetitive tasks, orchestrate complex workflows, and guide human responders through security incidents. It’s the central nervous system of the SOC, bridging SIEMs, EDR platforms, firewalls, threat intelligence feeds, ticketing systems, and cloud services to enable coordinated detection and response. SOAR is not a replacement for analysts; rather, it empowers them by reducing manual toil, improving consistency, and freeing them to focus on high-value investigations and threat hunting.
Key Functions and Capabilities of SOAR
SOAR platforms offer a suite of functionalities that are crucial for modern security operations:
Orchestration: Integrating Diverse Security Tools
Orchestration is the ability of SOAR to connect and integrate various security tools and systems (e.g., SIEM, EDR, firewalls, threat intelligence platforms, vulnerability scanners, identity management systems) regardless of vendor. It acts as a central hub, allowing these tools to communicate and exchange information seamlessly. This enables coordinated actions across the entire security stack, eliminating manual handoffs and speeding up response times.
Automation: Eliminating Repetitive Tasks
Automation is the core capability that allows SOAR to execute predefined actions without human intervention. These automated actions can range from simple tasks to complex sequences. Examples include:
- Alert Enrichment: Automatically gathering additional context about an alert (e.g., querying threat intelligence databases for an IP address, looking up user information in an identity system).
- Blocking IPs/Domains: Automatically configuring firewalls or web application firewalls (WAFs) to block malicious IP addresses or domains.
- Disabling User Accounts: Automatically disabling compromised user accounts in an identity management system.
- Ticket Creation: Automatically creating, updating, and closing incident tickets in a case management system.
By automating these repetitive and time-consuming tasks, SOAR significantly reduces the workload on SOC analysts (thus addressing alert fatigue) and ensures a rapid initial response.
Case Management: Centralized Incident Tracking
SOAR platforms typically include robust case management capabilities. This allows SOC teams to track incidents from detection to resolution, documenting every step of the investigation and response. Key aspects of case management include:
- Centralized incident repository: Storing all information related to an incident, including alerts, evidence, analyst notes, and actions taken.
- Workflow management: Guiding analysts through a structured incident response process.
- Auditing and compliance: Providing a clear audit trail of all activities for regulatory compliance and post-incident review.
- Collaboration: Facilitating collaboration among SOC team members and other stakeholders involved in incident response.
Playbooks: Structured Response Workflows
Playbooks are at the heart of SOAR’s automation and orchestration capabilities. A playbook is a pre-defined, automated, or semi-automated workflow that outlines the steps to be taken in response to a specific type of security incident. These are essentially standardized procedures translated into executable actions. Playbooks ensure consistency, reduce human error, and accelerate incident response by providing a clear, step-by-step guide for handling various threats.
What SOAR Automates: Practical Applications
SOAR’s automation capabilities are broad and can be applied across numerous security operations tasks. These automations are often triggered by alerts from the SIEM or other security tools.
- Alert Enrichment: As soon as an alert is generated, SOAR can automatically perform lookups against threat intelligence feeds, asset management databases, and identity systems to gather additional context. This provides analysts with a richer understanding of the alert without manual research.
- Ticket Creation: For every validated alert or identified incident, SOAR can automatically create a corresponding ticket in a case management system, assigning it to the appropriate analyst or team.
- IP/Domain Blocking: If a malicious IP address or domain is identified (e.g., from a phishing campaign or malware C2), SOAR can instantly push commands to firewalls or proxies to block that entity across the network.
- User/Account Disabling: In cases of suspected user account compromise, SOAR can automatically disable the affected account in Active Directory or an identity provider, preventing further unauthorized access.
- Threat Intelligence Lookups: This is often part of alert enrichment, where SOAR queries external and internal threat intelligence sources to determine the reputation of suspect IPs, domains, hashes, or URLs.
- Case Management: SOAR integrates directly with case management systems, automating their updates, closures, and the archival of evidence, ensuring meticulous record-keeping.
SOAR Playbooks Examples: Actionable Scenarios
Playbooks are the blueprints for automated response. Here are common examples of how SOAR playbooks operationalize security workflows:
- Phishing Response Automation: Upon detection of a phishing email (e.g., from email security gateway or reported by a user), a SOAR playbook can automatically:
- Extract URLs and attachments.
- Check URLs and file hashes against threat intelligence.
- Quarantine the email from other inboxes.
- Block malicious sender IPs/domains at the firewall.
- Create a dedicated incident ticket.
- Notify the user who reported the email.
- Malware Containment: If an EDR (Endpoint Detection and Response) solution detects malware on an endpoint, a SOAR playbook can trigger actions such as:
- Isolating the infected endpoint from the network.
- Collecting forensic data from the endpoint.
- Blocking the malware’s C2 (Command and Control) IP addresses.
- Scanning other endpoints for similar malware.
- Creating a critical incident ticket.
- Credential Compromise Response: If a SIEM or IAM system alerts on a suspected credential compromise (e.g., multiple failed logins, impossible travel scenario), a SOAR playbook can:
- Force a password reset for the affected user.
- Temporarily disable the user account.
- Initiate multi-factor authentication (MFA) re-enrollment.
- Review recent login activity for the account.
- Alert HR/legal if needed.
- Suspicious Login Handling: Beyond credential compromise, a playbook for suspicious logins might involve:
- Geo-IP lookup to identify unusual login locations.
- Contextual data enrichment (e.g., querying asset management for the device, identity management for user roles).
- Automated user challenge (e.g., sending an MFA push notification for verification).
- If challenge fails, temporary account lockout.
These playbooks drastically reduce the Mean Time to Respond (MTTR) by executing complex sequences of actions in seconds, much faster than a human analyst could.
SOAR Benefits: The Impact on Security Operations
The implementation of SOAR brings a multitude of significant benefits that transform the efficiency and effectiveness of a SOC.
1. Faster Response: Minimizing Impact
By automating repetitive tasks and orchestrating actions across multiple tools, SOAR drastically reduces the time it takes to respond to security incidents. This faster response is critical in minimizing the impact of breaches, limiting data exfiltration, and preventing lateral movement by attackers. A rapid response can make the difference between a minor incident and a major crisis. Industry reports indicate that organizations with a mature SOC+SIEM+SOAR ecosystem achieve an MTTR of less than 4 hours, a stark contrast to the weeks or months often seen in less integrated environments.
2. Reduced Analyst Workload: Combating Burnout
Alert fatigue and repetitive manual tasks are major contributors to SOC analyst burnout. SOAR alleviates this burden by automating many of the mundane, high-volume tasks that consume analysts’ time. This frees up analysts to focus on more complex investigations, threat hunting, and strategic security initiatives, improving job satisfaction and retaining valuable talent.
3. Consistent Incident Handling: Standardization and Reliability
Playbooks enforce a standardized approach to incident handling. Every time a specific incident type occurs, the SOAR platform executes the predefined playbook, ensuring that all necessary steps are taken consistently and according to best practices. This eliminates variability that can arise from different analysts handling incidents in their own way, leading to more reliable and auditable outcomes.
4. Lower Human Error: Precision in Execution
Manual processes are inherently prone to human error. Whether it’s missing a step in a procedure, entering incorrect data, or overlooking a critical detail, human mistakes can have significant consequences in security operations. SOAR automates these steps, executing them with precision and consistency every time, thereby significantly lowering the likelihood of errors during incident response.
The synergy of SIEM and SOAR is often described as “SIEM acts as the ‘Eyes’ by detecting events, while SOAR acts as the ‘Hands’ by taking action”. This integration solves the issue of alert fatigue, reduces MTTR, and transforms raw data into actionable intelligence.
The Outcome: A Resilient and Mature Security Posture
The seamless integration of SOC, SIEM, and SOAR culminates in a dramatically improved security posture for any organization. This unified architecture transitions security operations from a reactive, firefighting mode to a proactive, highly efficient, and resilient defense system. The benefits are not just theoretical; they translate into tangible, measurable improvements that directly impact an organization’s ability to withstand cyber threats.
Reduced Mean Time to Detect (MTTD)
One of the most critical outcomes of a well-integrated SOC+SIEM+SOAR ecosystem is a significantly reduced Mean Time to Detect (MTTD). SIEM’s comprehensive data collection, advanced correlation rules, and behavioral analytics ensure that security events are identified promptly and accurately. The continuous monitoring processes within the SOC further refine this detection capability. With a lowered MTTD, organizations can identify potential breaches much earlier in their lifecycle, before they have a chance to proliferate and cause widespread damage. Industry benchmarks suggest that mature organizations achieve an MTTD of less than 24 hours (nflo.tech). This early detection capability is paramount in minimizing the “dwell time” of attackers within a network.
Reduced Mean Time to Respond (MTTR)
Equally, if not more, important is the substantial reduction in Mean Time to Respond (MTTR). This is where SOAR truly shines. Upon detection of an incident by the SIEM and triage by the SOC, SOAR’s automated playbooks and orchestration capabilities kick into high gear. Tasks such as alert enrichment, IP blocking, account disabling, and containment actions are executed with machine speed and precision. This eliminates much of the manual back-and-forth, analyst research, and tool switching that typically prolong response times. The result is an MTTR that can be measured in minutes or hours rather than days or weeks (nflo.tech), allowing organizations to contain, eradicate, and recover from incidents with unprecedented efficiency.
Minimized Analyst Fatigue
The relentless barrage of security alerts is a leading cause of burnout and high turnover among SOC analysts. An integrated architecture addresses this directly. SOAR automates the repetitive, low-value, high-volume tasks, freeing analysts from the mundane. This includes the initial alert triage, context gathering, and routine response actions. Analysts are then able to focus their expertise on complex investigations, proactive threat hunting, and strategic security initiatives – the very activities that require human critical thinking and judgment. By minimizing alert fatigue and empowering analysts to work on more stimulating challenges, this integrated approach contributes to higher job satisfaction and improved retention of critical cybersecurity talent.
Standardized and Repeatable Incident Handling
Consistency is key in incident response. SOAR playbooks ensure that every incident of a particular type is handled according to a predefined, standardized procedure. This eliminates the variability that can arise from different analysts approaching the same incident in different ways. The result is a highly repeatable process, which not only improves efficiency but also reduces the risk of errors and ensures that all necessary steps (e.g., evidence collection, stakeholder notification) are consistently followed. This standardization is invaluable for audit purposes and for building a reliable, predictable security operation.
Improved Overall Security Maturity
Ultimately, the synergy of SOC, SIEM, and SOAR leads to a significant leap in an organization’s overall security maturity. This maturity is not just about having individual tools; it’s about how effectively these tools, people, and processes work together as a cohesive unit. The formula for security maturity can be succinctly expressed as:
\text{Security Maturity} = \text{Visibility (SIEM)} + \text{People & Process (SOC)} + \text{Automation (SOAR)}
- Visibility (SIEM): Provides the foundational understanding of what is happening across the entire IT landscape.
- People & Process (SOC): Offers the human expertise, structured workflows, and strategic oversight to make sense of the data and drive decisions.
- Automation (SOAR): Delivers the speed, consistency, and scalability required to operationalize response and reduce manual burden.
Together, these elements create a security program that is not only robust in its defenses but also agile and adaptive in its response to an ever-changing threat landscape. This holistic approach ensures that an organization is not just reacting to threats but is proactively building a resilient and future-proof cybersecurity posture.
The Future of Security Operations: AI in the SOC
The architecture of modern security operations continues to evolve, with artificial intelligence (AI) playing an increasingly pivotal role. AI is not a replacement for SOC, SIEM, or SOAR, but rather an enhancement that seamlessly integrates with the existing stack to amplify its capabilities. Agentic AI, in particular, is designed to work within this reality, plugging into the existing ecosystem to streamline triage, investigation, and response.
Enhancing Triage with AI
AI can significantly improve alert triage by accepting alerts from both SIEM and direct integrations with various detection tools. It can normalize alert formats, extract relevant context, and link duplicate alerts to a single case. Crucially, AI can suppress noisy or low-confidence signals and prioritize alerts based on impact and exposure, helping to reduce queue bloat and optimize analyst workflows.
Accelerating Investigation with AI
Investigations are often hampered by fragmented data and manual enrichment. AI helps by automatically querying across available sources in parallel, including log data, endpoint activity, and cloud telemetry. This allows for faster, deeper, and more consistent investigations, providing analysts with comprehensive context without manual effort. Furthermore, AI, particularly large language models (LLMs) like Gemini, can be integrated into the SOAR workflow to provide intelligent analysis and generate human-readable reports, accelerating the sharing of actionable intelligence. This integration of AI within the SOC+SIEM+SOAR framework represents the cutting edge of cybersecurity operations, further reducing MTTD and MTTR, and enabling security teams to handle ever-increasing volumes of data and threats more effectively.
Conclusion: Building a Resilient Digital Future
Modern security is unequivocally workflow-centric. The days of relying on a disparate collection of tools to stem the tide of cyber threats are long gone. The current threat landscape demands a cohesive, integrated, and intelligent approach – one that only the synergistic power of SOC, SIEM, and SOAR can truly deliver.
The Security Operations Center provides the essential human intelligence layer, a dedicated team with specialized roles and streamlined processes for monitoring, analysis, and strategic coordination. The SIEM acts as the foundational visibility and detection core, aggregating, normalizing, and correlating vast amounts of security data to provide a comprehensive understanding of the organization’s security posture. Crucially, SOAR serves as the automation and orchestration engine, transforming alerts into rapid, consistent, and error-free responses, thereby multiplying the effectiveness of the SOC team.
Together, these three pillars form an end-to-end flow that dramatically reduces Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR), minimizes the burden of analyst fatigue, ensures standardized and repeatable incident handling, and cultivates a significantly higher level of overall security maturity. This integrated architecture is not merely an assemblage of technologies; it is a strategic imperative for any organization committed to building a resilient digital future. Understanding these distinctions and investing in their seamless integration is the foundation of a truly conscious and effective cybersecurity strategy.
At IoT Worlds, we understand the complexities of modern security operations and the critical need for an integrated approach. Our expertise lies in helping organizations design, implement, and optimize SOC, SIEM, and SOAR solutions that are tailored to their unique needs, ensuring maximum efficiency and robust protection. From strategic consulting to full-scale platform deployment and continuous optimization, we empower businesses to navigate the intricate cybersecurity landscape with confidence.
Unlock the full potential of your security operations. To learn how IoT Worlds can help you build an intelligent, automated, and resilient security posture, reach out to us today.
Email us at info@iotworlds.com to schedule a consultation.