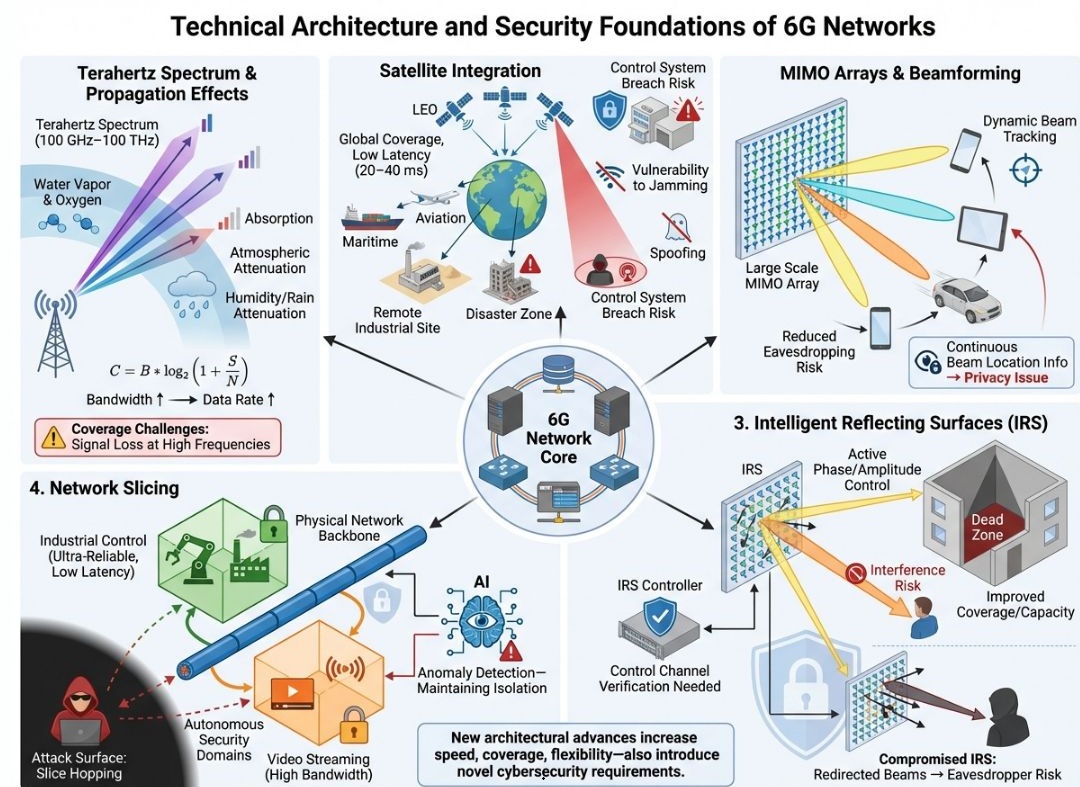
The telecommunications industry stands on the precipice of its next major revolution: 6G. While 5G brought about significant advancements in speed and connectivity, 6G promises a fundamental architectural shift, transcending mere incremental improvements. This isn’t just about faster downloads; it’s about building a hyper-connected, intelligent, and truly immersive world where the physical and digital realms converge seamlessly. This transformation, however, comes with its own set of technical complexities and, critically, a new frontier for cybersecurity.
As we peer into the future of connectivity, understanding the core pillars and the inherent security foundations of 6G networks becomes paramount. This article will delve into the groundbreaking technical innovations that define 6G and explore the novel cybersecurity challenges and solutions that must be integrated from the ground up, not as an afterthought.
The Dawn of a New Era: 6G’s Vision and Core Principles
The evolution from 5G to 6G is driven by an insatiable demand for higher data rates, ultra-low latency, and pervasive connectivity, aiming to support a future far more integrated with AI, immersive realities, and ubiquitous IoT. The vision for 6G extends beyond merely connecting devices; it seeks to create a truly intelligent network fabric that can understand, anticipate, and adapt to human and environmental needs.
Beyond 5G: A Leap in Capabilities
Compared to its predecessor, 6G is projected to offer performance benchmarks that redefine what’s possible in wireless communication. With data rates potentially reaching terabits per second (Tbps), latencies in the microsecond range, and connectivity for billions of devices, 6G will enable applications that are currently aspirational. High-definition holographic communications, multi-sensory Extended Reality (XR), and advanced industrial automation will become commonplace. This leap will be facilitated by a blend of new spectrum utilization, advanced antenna technologies, and a fundamentally redesigned network architecture.
Key Drivers for 6G Development
Several key drivers are propelling the research and development into 6G. The proliferation of IoT devices, the growing demand for real-time data processing at the edge, and the emergence of compute-intensive applications like AI and machine learning all necessitate a network capable of far greater capacity and intelligence. Furthermore, the ambition for truly global connectivity, reaching remote and underserved areas, underscores the importance of integrating non-terrestrial networks. Beyond performance metrics, 6G is also envisioned to be more energy-efficient and sustainable, addressing growing environmental concerns.
The 6G Technical Pillars: Reshaping Connectivity
The foundational pillars of 6G represent a paradigm shift in how wireless communication will be conceived, designed, and deployed. These innovations aim to push the boundaries of speed, coverage, and flexibility, creating an unprecedented level of connectivity.
Harnessing the Terahertz (THz) Spectrum
One of the most significant advancements in 6G revolves around the exploitation of the terahertz (THz) frequency band, spanning from approximately 100 GHz to 10 THz. This move into higher frequencies offers a tantalizing promise: massive contiguous bandwidths capable of supporting extraordinarily high data rates.
Unlocking Massive Data Rates
The fundamental relationship between bandwidth (B) and data rate (C) is described by Shannon’s formula:
where S is the average received signal power and N is the average noise power. This equation clearly illustrates that increasing bandwidth directly translates to a proportional increase in data rate, assuming a constant signal-to-noise ratio. The THz spectrum, with its vast available bandwidth, is therefore critical for achieving the Tbps speeds envisioned for 6G. These unprecedented speeds will enable applications like instantaneous holographic communication and real-time brain-computer interfaces.
Propagation Challenges in the THz Band
However, venturing into the THz spectrum is not without its challenges. Signals at these extremely high frequencies are highly susceptible to atmospheric attenuation.
- Absorption and Atmospheric Attenuation: Water vapor and oxygen molecules in the atmosphere absorb THz radiation, leading to significant signal loss over distance.
- Humidity/Rain Attenuation: Rain, fog, and humidity further exacerbate signal degradation, making reliable long-range communication difficult in certain weather conditions.
These propagation effects result in shorter communication ranges and necessitate innovative solutions for maintaining coverage and signal integrity. Overcoming these “coverage challenges: signal loss at high frequencies” is a key research area for 6G.
Satellite-Cellular Integration: Global Connectivity and Resilience
6G networks are envisioned to provide truly ubiquitous connectivity, moving beyond the limitations of traditional terrestrial cellular infrastructure. This will be achieved through the deep integration of satellite networks, particularly those comprising Low Earth Orbit (LEO) satellites.
Seamless Global Coverage and Low Latency
LEO satellites orbit closer to Earth than geostationary satellites, significantly reducing signal propagation delay and thus achieving lower latency, typically in the range of 20−40 ms. This characteristic, coupled with their ability to cover vast geographical areas, makes them ideal for extending 6G connectivity to:
- Remote Industrial Sites: Providing reliable communication for automation and monitoring in areas lacking terrestrial infrastructure.
- Maritime and Aviation: Enabling seamless connectivity for ships and aircraft, crucial for navigation, communication, and onboard services.
- Disaster Zones: Offering resilient communication channels when terrestrial networks are damaged or unavailable, crucial for emergency response and recovery efforts.
This integration provides a revolutionary communication solution for remote and hard-to-reach areas, ensuring seamless global connectivity.
Security Implications of Satellite Integration
While offering immense benefits, satellite integration introduces new security vulnerabilities.
- Vulnerability to Jamming: Satellite communication can be susceptible to jamming attacks, where malicious actors intentionally interfere with satellite signals, disrupting service.
- Spoofing: The risk of spoofing, where false signals mimic legitimate ones, could compromise navigation and communication systems.
- Control System Breach Risk: The complex control systems managing satellite constellations and their integration with terrestrial networks present a significant attack surface. A breach could lead to widespread service disruption or even control of satellite assets.
These risks necessitate robust security measures, including advanced encryption, anti-jamming technologies, and resilient control system architectures.
Intelligent Reflecting Surfaces (IRS): Overcoming Signal Obstacles
To combat the inherent signal loss at higher frequencies and address coverage gaps, 6G will leverage a novel technology known as Intelligent Reflecting Surfaces (IRS). These are practically passive surfaces embedded with an array of reconfigurable meta-materials that can intelligently manipulate incident electromagnetic waves.
Active Phase/Amplitude Control
Unlike traditional reflective surfaces, IRS can actively control the phase and amplitude of reflected signals. This ability allows them to constructively or destructively interfere with signals, effectively reshaping the wireless environment.
- Eliminating “Dead Zones”: By intelligently reflecting signals around obstacles like buildings or terrain, IRS can fill coverage gaps, ensuring ubiquitous connectivity where traditional signals might fail.
- Improved Coverage and Capacity: IRS can enhance signal strength at desired receivers, thereby improving overall network coverage and increasing network capacity by optimizing signal propagation paths. They can also reduce interference by intelligently steering signals away from unintended receivers.
Security Challenges with IRS
The programmable nature of IRS also introduces new security vulnerabilities:
- Interference Risk: A compromised IRS could be manipulated to deliberately cause interference, disrupting legitimate communication channels.
- Compromised IRS: Redirected Beams to Eavesdropper Risk: Malicious actors could potentially gain control of an IRS and redirect legitimate communication beams towards an eavesdropping device, enabling unauthorized interception of data.
- Control Channel Verification Needed: The control channels used to program and manage IRS must be rigorously secured and verified to prevent unauthorized access and manipulation.
Robust authentication and encryption protocols for IRS control channels, along with continuous monitoring for anomalous behavior, will be crucial.
MIMO Arrays and Dynamic Beamforming: Precision and Privacy
Massive Multiple-Input Multiple-Output (MIMO) technology, already a cornerstone of 5G, will evolve further in 6G. Coupled with advanced dynamic beamforming, these technologies will enable unparalleled precision in signal transmission and reception.
Large Scale MIMO Arrays and Dynamic Beam Tracking
6G networks will deploy even larger scale MIMO arrays, with potentially hundreds or thousands of antenna elements. These arrays, combined with sophisticated signal processing, will enable highly directional beams that can be dynamically tracked to individual devices. This “dynamic beam tracking” precisely follows user movement, ensuring optimal signal strength and minimizing interference.
Benefits: Reduced Eavesdropping Risk
The highly directional nature of dynamic beamforming inherently reduces the risk of eavesdropping. Because the signal is tightly focused on the intended receiver, it is much harder for an unauthorized party to intercept the transmission. This precision enhances the confidentiality of communications.
Privacy Issues: Continuous Beam Location Information
However, the precision of dynamic beam tracking also raises significant privacy concerns. The network’s ability to continuously track the exact location of a device and its user through beam information could be exploited for surveillance or unauthorized location tracking. This “continuous beam location info → privacy issue” necessitates stringent data protection regulations and privacy-preserving mechanisms within the 6G architecture.
The Security Challenge: Building Defensible 6G Networks
The advanced architectural features of 6G, while enabling unprecedented capabilities, also introduce new and complex cybersecurity requirements. Security can no longer be an afterthought; it must be intrinsically woven into the fabric of the network design.
Network Slicing: Tailored Services, New Attack Surfaces
Network slicing, a concept introduced in 5G, will be a fundamental architectural component of 6G. It allows for the creation of multiple virtual networks (slices) on a shared physical infrastructure, each tailored to specific service requirements.
Dedicated, Ultra-Reliable Domains
Network slicing enables the creation of highly customized and isolated network environments. For instance:
- Industrial Control (Ultra-Reliable, Low-Latency): A dedicated slice can be provisioned for critical industrial applications, guaranteeing ultra-low latency and ultra-high reliability for real-time control systems. This is vital for applications like remote surgery or autonomous factory operations.
- Autonomous Security Domains: Slices can be designed with specific security policies and isolation mechanisms to create autonomous security domains for sensitive data or critical infrastructure.
- Video Streaming (High Bandwidth): Another slice could be optimized for high-bandwidth applications like 8K video streaming or multi-sensory XR experiences, guaranteeing the necessary throughput.
This isolation improves resource allocation and allows for specialized security policies within each slice.
Novel Attack Surfaces: “Slice Hopping”
While offering isolation, network slicing also introduces new attack vectors.
- Attack Surface: Slice Hopping: A significant concern is “slice hopping,” where an attacker gains unauthorized access to one slice and then attempts to bridge into other, more sensitive slices on the same physical infrastructure. This could lead to a compromise of critical services or data.
- AI for Anomaly Detection – Maintaining Isolation: To counter such threats, AI-driven anomaly detection will be crucial. By continuously monitoring traffic patterns and behavior within each slice, AI systems can identify deviations from normal operation, flag potential “slice hopping” attempts, and trigger automated countermeasures to maintain isolation.
The complexity of orchestrating and securing these diverse slices demands sophisticated AI-based network orchestration and rigorous security protocols.
The Essential Role of AI in 6G Security
Artificial Intelligence is not just a consumer of 6G’s capabilities; it is an intrinsic enabler and guardian of its security. From dynamic resource allocation to proactive threat detection, AI will be central to maintaining the integrity and resilience of 6G networks.
AI-Driven Automated Network Management
6G networks will widely use AI-driven automated network management to achieve dynamic resource allocation, fault prediction, and self-optimization. This intelligence extends directly to security operations. AI can analyze vast amounts of network data in real-time, identifying subtle patterns that indicate emerging threats or vulnerabilities long before human operators could detect them.
Predictive Security and Self-Healing Networks
Beyond detection, AI in 6G security will enable predictive capabilities. Machine learning models can be trained to predict potential attack vectors based on historical data and current threat intelligence. This allows for proactive bolstering of defenses and the implementation of self-healing mechanisms, where the network can automatically reconfigure itself to isolate compromised components and restore service. This is a significant shift from reactive security measures to proactive and anticipatory defense.
Challenges of AI in Security
The reliance on AI also presents its own set of challenges. The security of the AI models themselves becomes critical—they must be protected from adversarial attacks that could manipulate their decisions or introduce biases. Furthermore, the ethical implications of AI-driven surveillance and automated decision-making in security contexts will require careful consideration and robust governance frameworks.
A Holistic Approach to 6G Cybersecurity
The novel architectural advances in 6G, with their increased speed, coverage, and flexibility, inherently introduce novel cybersecurity requirements. A multi-layered, holistic approach is essential to address the diverse threats that will emerge in this hyper-connected ecosystem.
End-to-End Security by Design
Security in 6G must be “by design” and “by engineering,” rather than an add-on. This means incorporating security considerations at every stage of the network’s lifecycle, from initial concept to deployment and ongoing operation. Every component, from the THz transceivers to the satellite control systems and network slices, must be built with security as a primary objective. This includes robust 360-degree cybersecurity and privacy-by-engineering principles.
Quantum-Resilient Security
The advent of quantum computing poses a significant long-term threat to current cryptographic standards. 6G networks, with their projected lifespan extending beyond the “quantum supremacy” threshold, must incorporate quantum-resilient cryptographic algorithms from the outset. This requires significant research and development into post-quantum cryptography to protect data confidentiality and integrity against future quantum attacks.
Zero-Trust Architectures
The inherent complexity and distributed nature of 6G networks necessitate the adoption of zero-trust security models. In a zero-trust environment, no user, device, or application is implicitly trusted, regardless of its location or previous authentication. Every access request is rigorously authenticated, authorized, and continuously verified. This approach minimizes the impact of potential breaches by containing unauthorized access to the smallest possible scope.
Regulatory Frameworks and Standardization
Developing robust international regulatory frameworks and standardization efforts will be crucial for 6G security. These frameworks will address issues such as:
- Spectrum Allocation and Regulation: Ensuring fair and secure use of the THz spectrum.
- Data Privacy and Governance: Establishing clear guidelines for the collection, processing, and storage of user data, especially given the continuous location tracking capabilities.
- Interoperability and Security Protocols: Standardizing secure communication protocols and interfaces to ensure seamless and safe interaction between diverse network components and operators.
International collaboration is essential to create a globally interoperable and secure 6G ecosystem.
Specific Security Considerations for 6G Components
Each of the technical pillars of 6G presents unique security challenges that require tailored solutions.
Securing the Terahertz Spectrum
The sheer bandwidth of the THz spectrum, while a boon for data rates, also presents challenges for secure transmission. The high atmospheric attenuation that limits range can, in some ways, act as a natural security feature, making long-range interception more difficult. However, short-range, high-bandwidth eavesdropping remains a concern. Advanced physical layer security mechanisms, such as ultra-dense short-range links and interference management techniques, will be vital to securing THz communications.
Mitigating Satellite Integration Risks
Beyond jamming and spoofing, securing satellite integration involves:
- Secure Launch and Operation: Protecting satellites from physical and cyberattacks during launch and throughout their operational lifespan.
- Resilient Ground Station Infrastructure: Ensuring the physical and cyber security of ground stations that control satellites and receive their data.
- Distributed Ledger Technologies: Exploring the use of blockchain and other distributed ledger systems for secure authentication and data integrity across satellite and terrestrial networks, enhancing the trustworthiness of global communication.
Defending Intelligent Reflecting Surfaces
Securing IRS goes beyond control channel verification. It requires:
- Tamper-Resistant Hardware: Designing IRS with hardware that resists physical tampering and unauthorized modification.
- Secure Software and Firmware Updates: Ensuring that any software or firmware updates for IRS are digitally signed and verified to prevent the injection of malicious code.
- Decentralized Control Mechanisms: Exploring decentralized control architectures where no single point of compromise can take down an entire IRS network.
Addressing MIMO and Beamforming Privacy
The privacy implications of continuous beam location tracking can be addressed through:
- Privacy-Preserving Data Aggregation: Aggregating location data in a way that protects individual identities while still providing necessary network management information.
- On-Device Processing: Performing some location-sensitive processing directly on the user’s device, minimizing the amount of raw location data transmitted to the network.
- Differential Privacy: Employing techniques that inject noise into location data to obscure individual movements while preserving overall statistical trends.
- User Consent and Control: Giving users granular control over their location data and transparently communicating how it is used.
Impacts and Applications of a Secure 6G
A securely built 6G network will unlock a myriad of transformative applications and significantly impact various sectors, fostering innovation and economic growth.
Enhanced Immersive Experiences
The combination of ultra-high data rates, extremely low latency, and pervasive connectivity will revolutionize immersive experiences. High-fidelity holographic communications, truly seamless multi-sensory Extended Reality (XR), and realistic digital twins will move from science fiction to everyday reality. Security is paramount here to protect personal data within these immersive spaces and prevent malicious manipulation of virtual environments.
Revolutionizing Industrial Automation and IoT
For industries, 6G will provide the backbone for advanced industrial automation. Ultra-reliable low-latency communications will enable precise remote control of machinery, real-time analytics for predictive maintenance, and highly efficient autonomous factories. The vast Internet of Things (IoT) ecosystem will flourish, with billions of connected devices across satellite, aerial, and terrestrial domains, demanding energy efficiency, robust security, and seamless interoperability. Securing these interconnected industrial systems from cyber-physical attacks is a critical concern, as a breach could have catastrophic real-world consequences.
Smart Cities and Autonomous Systems
Smart cities will leverage 6G for intelligent traffic management, smart grids, environmental monitoring, and public safety applications. Autonomous vehicles, drones, and other robotic systems will rely on 6G for real-time communication, precise navigation, and critical decision-making. The integrity and security of these communications are non-negotiable, as compromised systems could lead to accidents or widespread disruption.
Healthcare Advancements
In healthcare, 6G will enable remote surgery, real-time patient monitoring with high-fidelity data, and personalized medicine through ubiquitous sensors and AI analytics. The extreme sensitivity of medical data necessitates the highest levels of security and privacy within the 6G framework.
Addressing Global Challenges
Beyond technological marvels, a secure 6G infrastructure can play a vital role in addressing global challenges. Its global coverage can bridge the digital divide, providing connectivity to underserved populations. Resilient communication in disaster zones can significantly improve emergency response and recovery efforts. However, these applications rely fundamentally on the trustworthiness and security of the underlying network.
Open Research Challenges and Future Outlook
While the vision for 6G is compelling, significant research and development are still required to fully realize its potential and address the inherent challenges.
Spectrum Availability and Regulation
Further research is needed to optimize the use of the THz spectrum, including developing efficient modulation and coding schemes suitable for these frequencies, and devising novel techniques to mitigate atmospheric attenuation. Internationally harmonized spectrum allocation and regulation will be critical to facilitate global deployment and avoid interference issues.
Hardware and Infrastructure Requirements
The deployment of 6G will necessitate new hardware infrastructure, including advanced THz transceivers, intelligent reflecting surfaces, and highly integrated edge computing capabilities. Miniaturization, energy efficiency, and cost-effectiveness of these components are key research areas. Building out this extensive infrastructure globally will require massive investment and coordinated efforts.
Energy Efficiency and Sustainability
The vast scale and computational demands of 6G, coupled with the energy-intensive nature of some of its core technologies (like THz communication), raise concerns about energy consumption. Research into energy-efficient protocols, green AI algorithms, and sustainable network designs is paramount to ensure 6G’s environmental responsibility.
Interoperability and Standardization
Achieving seamless interoperability between diverse 6G technologies, including satellite, terrestrial, and future aerial platforms, is a major challenge. International standardization bodies will play a crucial role in developing common architectures, protocols, and interfaces to ensure a unified and coherent 6G ecosystem.
Continual Evolution of Security Paradigms
The cybersecurity landscape is constantly evolving. 6G security must be dynamic and adaptable, capable of responding to new threats and attack methodologies. This requires continuous research into advanced encryption, AI-driven threat intelligence, and innovative defensive strategies that can stay ahead of malicious actors. New security paradigms will emerge, such as self-evolving security, where AI actively learns and adapts the network’s defenses based on real-time threat intelligence.
The journey to 6G is not merely a technological upgrade; it’s a fundamental reimagining of our connected world. By prioritizing security from the ground up and embracing innovation across all architectural layers, we can build a 6G network that is not only ultra-fast and ubiquitous but also fundamentally trustworthy and resilient. The future of connectivity depends on it.
Unlock the Future of IoT with IoT Worlds
The complexities of 6G networks and their profound impact on the Internet of Things demand expert insight and strategic guidance. At IoT Worlds, we are at the forefront of understanding these transformative technologies, offering comprehensive solutions and consulting to help businesses navigate the evolving landscape of hyper-connectivity. Whether you’re looking to integrate next-generation wireless into your industrial operations, explore secure IoT deployments, or simply understand the implications of 6G for your enterprise, our team of experts is ready to assist.
Don’t let the future of connectivity catch you unprepared. Reach out to us today to discuss how we can help you harness the power of 6G and secure your IoT ecosystem.
Contact us for unparalleled expertise and innovative solutions: info@iotworlds.com