The Internet of Things (IoT) has rapidly transitioned from a futuristic concept to an omnipresent reality, profoundly reshaping industries, homes, and individual lives. From smart thermostats optimizing energy consumption to sophisticated industrial sensors enhancing operational efficiency, IoT devices are now integral to our daily existence. Billions of interconnected devices constantly exchange data, learn from their environments, and execute actions, creating unprecedented levels of convenience, automation, and insight. However, this transformative power comes with an inherent challenge: security.
The very essence of IoT – its pervasive connectivity and data-rich interactions – also presents a vast attack surface for malicious actors. The promise of a seamlessly connected world can only be fully realized if the underlying infrastructure is robustly secured. Without a proactive and comprehensive approach to security, the burgeoning IoT ecosystem risks becoming a breeding ground for cyberattacks, data breaches, and privacy violations. This article delves into the critical importance of IoT security and systematically explores its essential elements, offering a guide to building and maintaining a resilient and trustworthy connected future.
Understanding the Imperative of IoT Security
The sheer scale and diversity of IoT deployments make security an exceptionally complex yet non-negotiable aspect. Unlike traditional IT systems, IoT often involves resource-constrained devices, diverse communication protocols, and lengthy product lifecycles, all of which introduce unique security vulnerabilities. The consequences of neglecting IoT security can range from minor inconveniences to catastrophic failures, making it a paramount concern for developers, manufacturers, businesses, and end-users alike.
Why IoT Security is Critically Important
The foundational reasons for prioritizing IoT security are multifaceted, touching upon data integrity, operational continuity, privacy, and public trust.
Protecting Sensitive Data
IoT devices are voracious data collectors. They gather everything from personal health metrics via wearables, financial transaction data from smart payment systems, and sensitive environmental readings in industrial settings, to intimate details of daily life through smart home assistants. This data, often transmitted and stored in vast quantities, represents a treasure trove for cybercriminals if not adequately protected. A breach can lead to identity theft, financial fraud, industrial espionage, and severe reputational damage for organizations. The imperative here is not just to prevent unauthorized access but also to ensure the integrity and availability of this data.
Preventing Cyberattacks and System Exploitation
Weakly secured IoT devices are not merely targets; they can act as unwitting accomplices or launchpads for larger, more devastating cyberattacks. The infamous Mirai botnet, which leveraged hundreds of thousands of compromised IoT devices (like IP cameras and DVRs) to launch massive Distributed Denial of Service (DDoS) attacks, serves as a stark reminder of this threat. A single vulnerable device can become the entry point into an entire network, allowing attackers to lateral movement, escalate privileges, and compromise critical infrastructure or sensitive data within an organization. This makes every IoT device, no matter how seemingly insignificant, a potential link in a much larger attack chain.
Ensuring User Privacy
Many IoT devices, by their very nature, delve deep into personal spaces and routines. Smart cameras monitor homes, voice assistants listen for commands, and wearables track health and location data. Without stringent security and privacy safeguards, the data collected by these devices can be misused, exposing intimate details of individuals’ lives. Ensuring user privacy is not just a matter of compliance with regulations like GDPR or CCPA; it is fundamental to building trust and fostering widespread adoption of IoT technologies. Users must feel confident that their personal information is protected and that they have control over its collection and usage.
Maintaining System Reliability and Operational Continuity
In sectors like healthcare, smart grids, transportation, and critical infrastructure, IoT devices play pivotal roles in controlling vital operations. A security failure in these environments can have dire consequences, ranging from severe disruptions and economic losses to life-threatening situations. Imagine a smart hospital system compromised, affecting patient care, or a smart grid attacked, leading to widespread power outages. Robust IoT security measures are essential for ensuring the continuous and reliable operation of these mission-critical systems, thereby safeguarding public safety and economic stability.
Building Trust in Technology
The long-term success and widespread adoption of IoT hinge significantly on public trust. If security incidents become commonplace, or if users perceive their data and privacy to be at risk, the enthusiasm for connected technologies will wane. Strong security practices, transparent data handling, and a commitment to user protection are crucial for fostering confidence in IoT. This trust is not only vital for consumer markets but also for industrial and enterprise deployments where the stakes are even higher. Ultimately, a secure IoT ecosystem builds a foundation for continued innovation and integration into all facets of society.
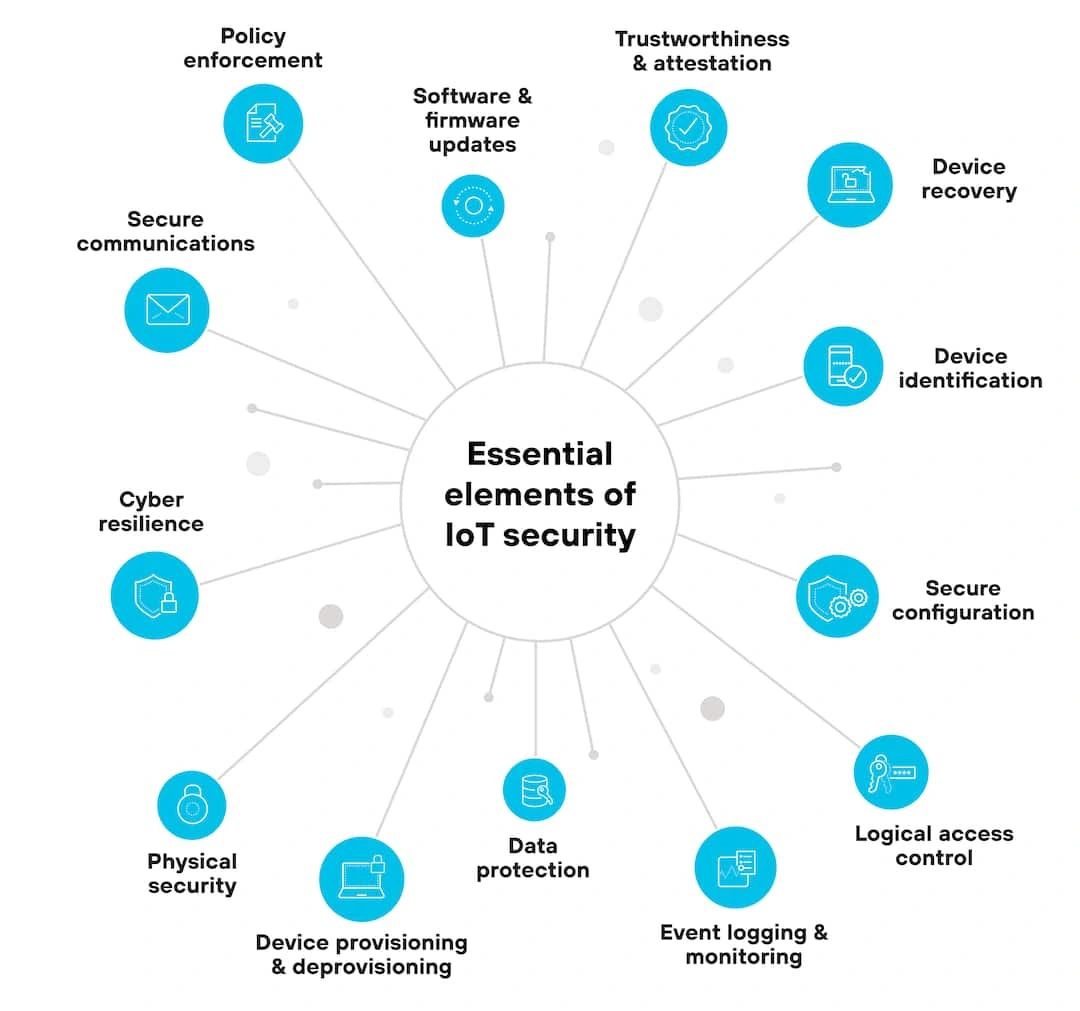
The Essential Elements of IoT Security
Building a secure IoT ecosystem requires a holistic approach, integrating security considerations at every stage of the device lifecycle, from design and development to deployment and eventual decommissioning. The following elements form the bedrock of a robust IoT security strategy, addressing various facets of protection, resilience, and operational integrity.
Policy Enforcement
Policy enforcement refers to the mechanisms and rules governing how IoT devices operate within a system, interact with each other, and access resources. It ensures that devices adhere to predefined security postures and operational guidelines. This isn’t just about setting rules; it’s about actively monitoring and enforcing them to prevent unauthorized actions and maintain system integrity.
Defining Granular Access Policies
At its core, policy enforcement involves defining precise permissions and restrictions for each device and user within the IoT ecosystem. This includes specifying what data a device can access, which networks it can communicate with, and what actions it is authorized to perform. For instance, a smart light bulb should only have permissions to receive commands for illumination control and report its status, not to access sensitive personal data or administer other network devices. The principle of least privilege, where devices are granted only the minimum necessary permissions to perform their functions, is paramount here.
Implementing Network Segmentation
Network segmentation is a critical policy enforcement strategy that involves dividing a network into smaller, isolated segments. This limits the blast radius of a potential breach. If one IoT device in a segment is compromised, the attacker’s ability to move laterally to other segments or critical systems is severely restricted. For example, operational technology (OT) networks in industrial environments should be strictly segmented from enterprise IT networks, and guest Wi-Fi networks should be isolated from smart home devices.
Automating Policy Application and Monitoring
Manual policy enforcement is neither scalable nor effective in complex IoT environments. Automation is crucial for applying policies consistently across a large number of devices and for continuously monitoring compliance. This involves using tools for automated configuration management and real-time anomaly detection. If a device deviates from its defined policy – for instance, attempting to communicate with an unauthorized server – the system should automatically flag the event, block the action, and alert administrators.
Software and Firmware Updates
The ability to securely update software and firmware is an often-underestimated yet absolutely critical element of IoT security. Vulnerabilities are discovered continuously, and devices need to be patchable throughout their operational lifespan to remain secure. Static, unupdatable devices are ticking time bombs in an evolving threat landscape.
Over-the-Air (OTA) Update Mechanisms
Secure Over-the-Air (OTA) update capabilities are essential. Devices must be able to receive and install updates remotely, efficiently, and reliably. This process requires robust authentication of the update source, encryption of the update package to prevent tampering during transmission, and integrity checks (e.g., digital signatures) to verify that the firmware has not been altered. A compromised update mechanism can be catastrophic, allowing attackers to introduce malicious firmware.
Regular Vulnerability Patching
Manufacturers must commit to providing regular security patches for their devices. This means dedicating resources to monitoring for new vulnerabilities, developing patches, and disseminating them effectively. Consumers and enterprises, in turn, must prioritize applying these updates promptly. Delaying updates leaves devices exposed to known exploits.
Secure Boot and Rollback Protection
Secure boot mechanisms ensure that only authenticated and authorized software can run on a device. This prevents attackers from loading malicious code at startup. Additionally, rollback protection prevents attackers from reverting a device to an older, vulnerable firmware version. These features are crucial at the hardware and low-level software layers to establish a trustworthy execution environment.
Trustworthiness and Attestation
Trustworthiness and attestation relate to the ability to verify the authenticity, integrity, and operational state of an IoT device. In a world where devices may be geographically dispersed and operate autonomously, proving their trustworthiness is fundamental.
Hardware Root of Trust
A hardware root of trust (HRoT) is a foundational element for trustworthiness. This is a trusted component, usually a secure enclave or module within the device’s hardware, that cannot be tampered with. It acts as the anchor for all security operations, storing cryptographic keys and executing security-critical functions. The HRoT ensures that the device boots securely and that its identity is genuine.
Remote Attestation
Remote attestation is the process by which a device cryptographically proves its current software and hardware state to a remote challenger (e.g., a server or another device). This allows the challenger to verify that the device is running legitimate, untampered firmware and has not been compromised. If the attestation fails, the device can be isolated or restricted from accessing sensitive resources, preventing a compromised device from infecting the wider network.
Device Identity Management
Each IoT device needs a unique and verifiable identity, ideally established at the point of manufacture. This identity is crucial for authentication, authorization, and audit trails. Strong device identity relies on cryptographic keys and certificates, ensuring that only legitimate devices can join the network and participate in communications. This prevents impersonation and spoofing attacks.
Device Recovery
Even with the most robust security measures, compromises can occur. The ability to safely and effectively recover a compromised device is paramount for maintaining system resilience and minimizing downtime.
Secure Reset and Re-provisioning
If a device is compromised or malfunctions, there must be a secure mechanism to reset it to a known good state. This often involves securely wiping sensitive data and re-provisioning the device with fresh identities and configurations. The recovery process itself must be secure to prevent attackers from re-introducing malicious software during the reset.
Redundancy and Failover Mechanisms
For critical IoT applications, building in redundancy and failover mechanisms is essential. If one device or component fails or is compromised, a backup system can seamlessly take over, ensuring continuous operation. This might involve duplicate hardware, data replication, or software-defined failover solutions.
Incident Response and Forensics
Effective device recovery is closely tied to a well-defined incident response plan. When a device is compromised, it’s crucial to quickly detect the incident, isolate the affected device, analyze the nature of the breach, and apply corrective measures. Forensic capabilities, including secure logging and tamper-proof storage of event data, aid in understanding how a compromise occurred and preventing future incidents.
Device Identification
Precise and unambiguous device identification is the cornerstone of any secure IoT system. Without knowing exactly which device is which, effective authentication, authorization, and management become impossible.
Unique Device Identifiers
Every IoT device must possess a unique, unalterable identifier, often burned into the hardware during manufacturing. This could be a serial number, a MAC address, or a cryptographic identifier. This identifier forms the basis for all further security operations.
Secure Onboarding and Provisioning
The process of bringing a new device into the IoT ecosystem (onboarding) must be highly secure. This involves verifying the device’s identity, securely provisioning it with credentials (e.g., digital certificates, symmetric keys), and configuring its initial security policies. Automated, secure provisioning platforms are often used to manage this at scale, minimizing human error and potential vulnerabilities.
Device Lifecycle Management
Device identification is not a one-time event; it’s part of a continuous lifecycle. This includes tracking devices from manufacturing through deployment, operation, and eventual decommissioning. The ability to revoke a device’s identity and effectively de-provision it when it is no longer in use is critical to prevent dormant or discarded devices from becoming security liabilities.
Secure Configuration
Misconfigurations are a leading cause of security breaches. Secure configuration involves ensuring that all IoT devices are deployed and maintained with security-hardened settings from the outset, rather than relying on default or insecure options.
Eliminating Default Passwords and Insecure Settings
Perhaps the most basic yet frequently overlooked security measure is changing default passwords and disabling unnecessary services. Many IoT devices ship with easily guessable default credentials or have open ports and services that are not required for their operation, creating immediate attack vectors. Secure configuration mandates changing these defaults and hardening settings.
Principle of Least Functionality
Devices should only have the functionality enabled that is strictly necessary for their intended purpose. Unused ports, protocols, or services should be disabled to reduce the attack surface. For example, a temperature sensor doesn’t need a web server or SSH access.
Automated Configuration Management
Given the potentially vast number of IoT devices, manual configuration is impractical and prone to errors. Automated configuration management tools and platforms are essential for consistently applying secure configurations across all devices, ensuring compliance with established security policies, and detecting any deviations.
Logical Access Control
Logical access control governs who or what (users, other devices, applications) can access specific resources or perform actions within the IoT ecosystem. It extends beyond simple authentication to encompass granular authorization decisions.
Role-Based Access Control (RBAC)
RBAC is a common and effective approach where access permissions are assigned based on a user’s or device’s role within the system. For instance, an administrator would have full control, an operator might have read-only access to monitoring data, and a device would only have permissions relevant to its assigned function. This simplifies management and ensures appropriate segregation of duties.
Multi-Factor Authentication (MFA)
Where human interaction with IoT systems or device management platforms is required, Multi-Factor Authentication (MFA) adds a crucial layer of security. Requiring more than one form of verification (e.g., a password and a one-time code from a mobile app) significantly reduces the risk of unauthorized access even if one credential is compromised.
Context-Aware Access Control
Advanced logical access control systems incorporate context into their decision-making. This means considering factors like the device’s location, time of day, network trustworthiness, or even the behavioral patterns of a user or device before granting access. If a device attempts to access a resource from an unusual location or at an odd time, it might trigger additional authentication challenges or automatically deny access.
Event Logging and Monitoring
No security system is impregnable. When an incident occurs, comprehensive event logging and continuous monitoring are vital for detection, investigation, and response.
Centralized Log Management
IoT devices generate a vast amount of operational and security data. Centralizing these logs in a secure, tamper-proof repository is crucial. This allows for correlation of events across multiple devices and systems, providing a holistic view of the network’s security posture.
Real-time Threat Detection and Alerting
Automated tools for real-time monitoring and anomaly detection are essential. These systems analyze log data and network traffic for suspicious patterns – such as unusual device behavior, failed login attempts, or unauthorized data transfers – and generate immediate alerts to security personnel. Machine learning and AI are increasingly being used to enhance these detection capabilities, identifying sophisticated threats that might evade rule-based systems.
Audit Trails and Forensic Readiness
Robust logging provides an invaluable audit trail, documenting every significant event, action, and access attempt within the IoT ecosystem. This data is critical for forensic investigations after a security incident, helping to determine the scope of a breach, how it occurred, and what data was affected. Logs must be protected from tampering and stored for an appropriate duration to meet compliance and investigative requirements.
Data Protection
Protecting the data collected, processed, and transmitted by IoT devices is perhaps the most visible aspect of IoT security. This encompasses safeguarding data confidentiality, integrity, and availability at every stage of its lifecycle.
Encryption in Transit and at Rest
All sensitive data transmitted between IoT devices and back-end systems should be encrypted using strong cryptographic protocols (e.g., TLS/SSL). Equally important is encrypting data stored on the device itself (data at rest) and within cloud or edge storage solutions. This ensures that even if data is intercepted or a storage medium is compromised, the information remains unintelligible to unauthorized parties.
Data Anonymization and Minimization
Where possible, data anonymization techniques should be employed to remove personally identifiable information, especially for aggregated data or data used for analytics. The principle of data minimization dictates that IoT devices should only collect and retain the absolute minimum amount of data required for their function, reducing the potential impact of a breach.
Secure Storage Solutions
Whether data is stored on the device (edge), in a local gateway, or in the cloud, the storage solutions must be secure. This includes access controls, encryption, intrusion detection, and regular vulnerability scanning of storage infrastructure. For devices with limited storage, secure temporary storage and timely transmission to more robust solutions are critical.
Device Provisioning and Deprovisioning
The secure lifecycle management of devices, from their initial deployment to their removal from service, is a continuous security concern.
Secure Initial Provisioning
As mentioned under device identification, the initial enrollment of a device into the network must be secure. This often involves establishing cryptographic identities, configuring network access, and linking the device to its owner or management platform. Automated, tamper-resistant provisioning processes are crucial.
Certificate Management
Many IoT security mechanisms rely on digital certificates for identity and secure communication. Robust certificate management – including secure issuance, renewal, and revocation – is vital. A compromised or expired certificate can render a device or an entire system vulnerable.
Secure Deprovisioning and Data Wiping
When an IoT device reaches its end-of-life or is retired, it must be securely de-provisioned. This involves revoking its access credentials, removing its identity from the system, and securely wiping any sensitive data stored on the device to prevent data remnants from falling into the wrong hands. Physical destruction might be necessary for highly sensitive cases.
Physical Security
While much of IoT security focuses on cyber aspects, the physical security of devices is equally important, particularly for devices deployed in accessible or hostile environments.
Tamper Detection and Resistance
IoT devices, especially those in unprotected locations, should be designed with tamper detection mechanisms. This could include sensors that detect attempts to open the device enclosure or modify its hardware. Tamper-resistant enclosures can also deter physical attacks.
Environmental Hardening
Devices deployed in harsh industrial environments or public spaces need to be physically robust and resistant to environmental factors like extreme temperatures, moisture, dust, or vibration. Physical damage can compromise security mechanisms or make the device vulnerable to exploitation.
Location Security (for Gateways and Critical Devices)
Gateways, controllers, and other critical IoT infrastructure often require enhanced physical security, similar to traditional IT data centers. This includes restricted access, surveillance, and environmental controls to protect against theft, vandalism, and unauthorized physical manipulation.
Cyber Resilience
Cyber resilience goes beyond simply preventing attacks; it’s about an organization’s ability to anticipate, withstand, recover from, and adapt to cyber threats and failures without significant disruption to services. For IoT, this means designing systems that can continue to function even when components are under attack or compromised.
Redundancy and Decentralization
Architecting IoT systems with redundancy and decentralization helps to build resilience. If a single point of failure (e.g., a central server) is compromised, the distributed nature of the system allows other components to continue operating, mitigating the impact. Edge computing, where processing occurs closer to the data source, can also enhance resilience by reducing reliance on a central cloud.
Self-Healing and Automated Recovery
Advanced resilient systems can automatically detect failures or compromises and initiate self-healing actions. This might involve isolating a faulty device, re-routing traffic, or automatically deploying backup configurations. The goal is to minimize human intervention and speed up recovery times.
Continuous Security Assessment and Improvement
Cyber resilience is an ongoing journey, not a destination. Regular vulnerability assessments, penetration testing, and continuous security audits are essential for identifying weaknesses and adapting the security posture to emerging threats. Learning from incidents and continually refining security practices are hallmarks of cyber resilience.
Secure Communications
The vast majority of IoT devices communicate constantly, making securing these communication channels paramount. Without secure communication, all other security measures can be undermined.
End-to-End Encryption
All data exchanged between devices, gateways, and cloud platforms should be protected by end-to-end encryption. This means that data is encrypted at the source and remains encrypted until it reaches its intended recipient, preventing eavesdropping and tampering during transit. Encryption protocols like TLS/SSL are standard for internet-based communications, while specialized protocols might be used for constrained devices.
Mutual Authentication
Beyond authenticating the sender, secure communication often requires mutual authentication, where both parties verify each other’s identity before establishing a connection. This prevents both impersonation of devices and spoofing of back-end servers.
Secure Protocol Design
The communication protocols themselves must be inherently secure, designed to withstand various attacks such as replay attacks, man-in-the-middle attacks, and denial-of-service attempts. Choosing and implementing secure communication protocols is a critical aspect of IoT system design.
The IoT Security Lifecycle: A Continuous Journey
Implementing these essential elements is not a one-time task but an ongoing commitment throughout the entire lifecycle of an IoT device and system.
Security by Design
The most effective IoT security begins at the drawing board. Incorporating security considerations from the initial design phase – “security by design” – is far more effective and cost-efficient than trying to bolt on security retroactively. This involves threat modeling, secure coding practices, and selecting secure hardware components.
Secure Development and Testing
During development, rigorous testing, including penetration testing and vulnerability assessments, is crucial to identify and remediate security flaws before deployment. Adhering to secure coding guidelines and employing static and dynamic code analysis tools also contributes significantly.
Secure Deployment and Operation
Maintaining security in operational environments requires continuous monitoring, proactive patch management, and a robust incident response capability. Regular audits and reviews of security configurations are also essential.
Secure Decommissioning
Even when a device is retired, its potential as a security risk persists. Secure de-provisioning and data wiping procedures ensure that sensitive information does not fall into the wrong hands and that the device can no longer be exploited.
The Human Factor in IoT Security
While technology forms the backbone of IoT security, the human element remains a critical component that often gets overlooked. Employees, administrators, and even end-users play a significant role in upholding or undermining security.
Security Awareness Training
For employees involved in managing or developing IoT systems, comprehensive security awareness training is indispensable. This includes education on best practices, recognizing social engineering attempts, and understanding their role in maintaining the security posture of the organization.
Vendor Selection and Supply Chain Security
Organizations deploying IoT solutions must carefully vet their hardware and software vendors. The security practices of every entity in the supply chain, from component manufacturers to software providers, can introduce vulnerabilities. Due diligence in vendor selection is paramount.
User Education and Empowerment
For consumer IoT, educating users about the importance of strong passwords, timely updates, and understanding privacy settings is crucial. Empowering users with clear, actionable security advice can significantly enhance the overall security of their connected environments.
The Future of IoT Security: Emerging Trends and Challenges
The IoT landscape is constantly evolving, bringing new security challenges and innovations. Staying ahead of these trends is vital for maintaining a robust security posture.
AI and Machine Learning for Threat Detection
Artificial intelligence and machine learning are increasingly being leveraged to enhance IoT security, particularly in areas like anomaly detection, predicting sophisticated attacks, and automating response mechanisms. These technologies can process vast amounts of data to identify patterns indicative of threats that human analysts might miss.
Blockchain for Trust and Identity
Blockchain technology offers potential solutions for secure device identity management, data integrity, and decentralized access control in highly distributed IoT environments. Its immutable ledger and cryptographic properties can reinforce trust among disparate devices.
Quantum-Resistant Cryptography
As quantum computing advances, the cryptographic algorithms currently used to secure IoT communications may become vulnerable. The development and adoption of quantum-resistant cryptography will be essential to future-proof IoT security.
Regulatory Landscape Evolution
Governments and regulatory bodies worldwide are increasingly recognizing the need for IoT security standards and regulations. The evolving legal landscape will shape how devices are designed, secured, and deployed, pushing for greater accountability and transparency from manufacturers and service providers.
Conclusion
The Internet of Things offers a future brimming with unprecedented opportunities for convenience, efficiency, and innovation. However, unlocking this potential responsibly hinges entirely on our collective ability to embed robust security into every facet of the IoT ecosystem. From the foundational elements of policy enforcement and secure configuration to critical capabilities like cyber resilience and secure communications, each piece of the security puzzle plays a vital role.
Neglecting IoT security is not merely a technical oversight; it is a profound risk to data privacy, operational continuity, public safety, and ultimately, the trust that underpins our connected world. As developers, engineers, businesses, and consumers, we all share a responsibility to champion and implement these essential security measures. By committing to security by design, continuous vigilance, and adaptive strategies, we can ensure that the Internet of Things remains a force for good, empowering a future that is not only connected but also secure and reliable.
Are you ready to elevate your IoT security strategy and transform your connected world with peace of mind? Whether you’re grappling with complex industrial IoT deployments or securing consumer-grade devices, IoT Worlds offers unparalleled expertise and solutions tailored to your unique needs. Don’t compromise on the security of your critical assets and sensitive data. Take the proactive step towards a more secure and resilient IoT future.
For a comprehensive assessment of your IoT security posture, expert guidance, and cutting-edge security solutions, reach out to us today.
Email us at info@iotworlds.com to discuss how we can help you build and maintain an impenetrable IoT ecosystem. Your secure connected future starts now.