The manufacturing sector is undergoing a profound transformation. The vision of Industry 4.0—smart factories where AI-powered robots collaborate seamlessly with humans, supply chains adjust in real-time, and digital twins simulate entire production lines—is rapidly becoming a reality. This digital revolution promises unprecedented efficiency, flexibility, and innovation. However, as factories become more connected, they also become more vulnerable.
The uncomfortable truth is that most factories today are becoming connected faster than they are becoming cyber resilient. Robots are connected, Manufacturing Execution Systems (MES) platforms are integrated, and production data flows across plants, suppliers, and cloud platforms. But are our factories truly prepared for a cyber disruption? The answer, for many, is a resounding no.
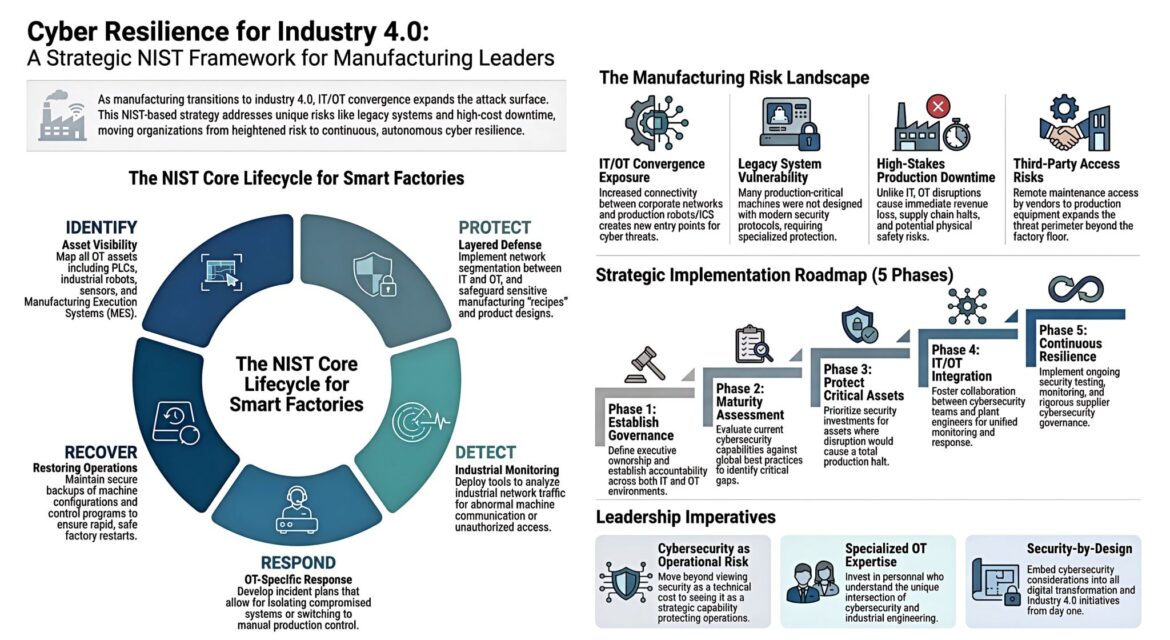
Traditional IT cybersecurity paradigms are insufficient for the unique demands of the factory floor. The convergence of Information Technology (IT) and Operational Technology (OT), the prevalence of legacy industrial systems, the unacceptable cost of downtime, and the expanding threat perimeter due to third-party access, all necessitate a fundamental shift in how we approach security in manufacturing. Cybersecurity in Industry 4.0 must be treated as operational resilience, not just IT defense tactics.
This comprehensive guide will explore the critical aspects of achieving cyber resilience in smart factories, drawing upon a strategic framework rooted in the NIST Core Lifecycle. We will delve into the unique manufacturing risk landscape, outline a practical implementation roadmap, and discuss the leadership imperatives essential for success.
The Manufacturing Risk Landscape: A New Battlefield
The very elements that define Industry 4.0—interconnectivity, automation, and data exchange—also introduce significant vulnerabilities that traditional factories never faced. Understanding this new risk landscape is the first step toward building robust cyber resilience.
IT/OT Convergence Exposure
The integration of IT and OT environments is a cornerstone of smart manufacturing. Corporate networks are now intrinsically linked with production robots and Industrial Control Systems (ICS). While this convergence unlocks immense operational efficiencies and real-time insights, it simultaneously creates new entry points for cyber threats. A breach in the IT network can potentially spill over into the OT domain, impacting physical processes, and vice versa. This blurring of lines demands a unified security strategy that accounts for the distinct characteristics of both IT and OT ecosystems.
Legacy System Vulnerability
One of the most significant challenges stems from the pervasive presence of legacy industrial systems. Decades-old Programmable Logic Controllers (PLCs), Human-Machine Interfaces (HMIs), and other controllers were never designed with modern cybersecurity in mind. They often lack robust authentication mechanisms, encryption capabilities, and readily available security patches. These systems, critical to production, represent significant vulnerabilities that attackers can exploit. Integrating them into a connected environment without adequate protection is akin to building a modern fortress with gaping holes in its foundations.
High-Stakes Production Downtime
Unlike typical IT disruptions, which might lead to data loss or service unavailability, cyber incidents in industrial settings can have far more severe consequences. Malware or ransomware attacks can halt production lines, cause immediate revenue loss, disrupt global supply chains, and even lead to physical safety risks for workers. A few hours of downtime can translate into millions of dollars in losses and significant reputational damage. This makes “downtime is not acceptable” a core principle that must drive cybersecurity investments and strategies in smart factories.
Third-Party Access Risks
The modern manufacturing ecosystem often involves a complex web of external entities, including vendors, contractors, and service providers. Remote maintenance access and vendor connectivity to production equipment are increasingly common, expanding the security perimeter far beyond the physical confines of the factory floor. Each third-party connection represents a potential vector for attack, requiring rigorous vetting, stringent access controls, and continuous monitoring to mitigate risks. The security posture of a smart factory is only as strong as its weakest link, and often, that link lies with an external partner.
The NIST Core Lifecycle for Smart Factories
To navigate this complex risk landscape and build effective cyber resilience, a structured approach is essential. The National Institute of Standards and Technology (NIST) Cybersecurity Framework offers a robust lifecycle that can be adapted for smart factories, comprising five core functions: Identify, Protect, Detect, Respond, and Recover. This iterative framework provides a practical roadmap for organizations to manage and reduce their cybersecurity risk.
Identify: Know Your Factory
The “Identify” function emphasizes the crucial first step: gaining a comprehensive understanding of all assets, systems, capabilities, and risks within the factory environment. This involves much more than just cataloging IT assets.
Asset Visibility
Mapping all Operational Technology (OT) assets is paramount. This includes PLCs, industrial robots, sensors, Manufacturing Execution Systems (MES), Human-Machine Interfaces (HMIs), and any other device that controls or monitors industrial processes. A detailed inventory should go beyond simply listing devices to include their software versions, network configurations, vulnerabilities, and interdependencies. Without this foundational knowledge, it’s impossible to effectively protect what you don’t know you have.
Risk Assessment
Once assets are identified, conduct thorough risk assessments to understand potential threats and vulnerabilities. This involves evaluating the likelihood of an incident and the potential impact it could have on operations, safety, and business continuity. Prioritize risks based on their severity and allocate resources accordingly.
Business Environment
Understand the factory’s mission, critical functions, and dependencies. Which processes are essential for production? What are the regulatory compliance requirements? How does a cyber incident affect these? This contextual understanding helps in making informed decisions about security investments.
Governance
Establish clear roles, responsibilities, and accountability for cybersecurity within the organization. This includes defining policies, procedures, and communication channels for managing cyber risks.
Protect: Design for Containment
The “Protect” function focuses on implementing safeguards to ensure the delivery of critical infrastructure services. For smart factories, this means not only preventing attacks but also designing systems that can contain a breach, limiting its spread and impact.
Layered Defense and Network Segmentation
Implement a layered defense strategy, also known as defense in depth. This involves deploying multiple security controls across different layers of the network and systems. A critical aspect of this is robust network segmentation, separating IT and OT networks. Within the OT network itself, further segmentation can be applied to isolate critical production segments from less sensitive areas. This significantly limits an attacker’s lateral movement, even if they manage to breach an initial perimeter.
Access Control
Implement stringent access control mechanisms for both physical and logical access to systems and data. This includes strong authentication (e.g., multi-factor authentication), role-based access control (RBAC) to ensure individuals only have access commensurate with their job functions, and regular review of access privileges.
Data Security
Safeguard sensitive manufacturing “recipes,” product designs, intellectual property, and operational data. This involves encryption, data loss prevention (DLP) solutions, and secure storage practices. Protecting this data is crucial not only for business competitiveness but also to prevent adversaries from understanding and manipulating production processes.
Maintenance and Configuration Management
Ensure secure baseline configurations for all devices and regularly patch and update systems to address known vulnerabilities. This is particularly challenging for legacy OT systems, but strategies like virtual patching or compensating controls can be employed.
Awareness and Training
Educate all employees, from the shop floor to executive leadership, about cybersecurity risks and their role in maintaining a secure environment. Human error remains a significant factor in successful cyberattacks, making continuous training essential.
Detect: Watch the Industrial Network
Even with robust protective measures, no system is entirely impenetrable. The “Detect” function is about developing and implementing activities to identify the occurrence of a cybersecurity event in a timely manner.
Industrial Monitoring
Deploy specialized tools and technologies to continuously monitor industrial network traffic for abnormal machine communication or unauthorized access. Traditional IT security tools are often inadequate for OT environments, as they may not understand industrial protocols or the unique behavior of control systems. Solutions include Intrusion Detection Systems (IDS), Security Information and Event Management (SIEM) systems tailored for OT, and behavioral analytics tools that learn normal operational patterns and flag deviations.
Continuous Vulnerability Detection
Regularly perform vulnerability scans and penetration testing on both IT and OT networks to proactively identify weaknesses that attackers could exploit. This should include assessments of legacy systems.
Anomaly Detection
Leverage machine learning and AI to detect anomalies in operational data and network traffic. Unusual sensor readings, unexpected PLC commands, or changes in communication patterns could all indicate a cyber intrusion.
Event Logging
Implement comprehensive logging across all critical systems and consolidate logs for centralized analysis. This provides crucial forensic data in the event of an incident.
Respond: Protect Production First
The “Respond” function focuses on developing and implementing activities to take action regarding a detected cybersecurity incident. In a smart factory, the primary objective of any response plan must be to protect production and safety.
OT-Specific Incident Response Plans
Develop detailed incident response plans tailored specifically for OT environments. Unlike IT, where containing a breach might involve shutting down servers, in OT, this could have severe physical consequences. Plans should prioritize human safety, environmental protection, and then production continuity.
Isolation and Containment Strategies
Define clear procedures for isolating compromised systems or segments of the network to prevent further spread of an attack. This might involve air-gapping specific machines or triggering fail-safe mechanisms.
Manual Production Control
Include provisions for switching to manual production control if automated systems are compromised. This ensures critical operations can continue, albeit at a reduced capacity, minimizing downtime and economic impact.
Communication and Coordination
Establish clear communication protocols for informing relevant stakeholders, including management, incident response teams, and regulatory bodies. Coordinate closely between IT and OT teams during an incident to ensure a unified and effective response.
Analysis and Eradication
After containing an incident, conduct thorough forensic analysis to understand the root cause, eradicate the threat, and prevent recurrence.
Recover: Restart the Factory
The “Recover” function involves developing and implementing activities to restore any capabilities or services that were impaired due to a cybersecurity incident. The goal is to ensure rapid, safe factory restarts.
Secure Backups and Restore Procedures
Maintain secure, isolated, and regularly tested backups of machine configurations, PLC programs, HMI projects, and critical operational data. These backups are essential for restoring systems to a known good state after an attack. Crucially, these backups must be protected from the same attack vectors that targeted the operational systems.
Disaster Recovery Plans
Develop comprehensive disaster recovery plans that outline the steps for bringing critical production systems back online after a significant cyber event. These plans should be regularly tested and updated.
Business Continuity Planning
Integrate cyber incident recovery into broader business continuity planning. This ensures that the organization can continue to operate essential business functions even amidst significant disruption.
Lessons Learned
After each incident (or recovery exercise), conduct a thorough post-mortem analysis to identify lessons learned and implement improvements to the cyber resilience program. This continuous feedback loop is vital for long-term improvement.
Strategic Implementation Roadmap (5 Phases)
Moving from a heightened risk posture to continuous, autonomous cyber resilience is a journey, not a destination. A structured, phased implementation roadmap helps organizations systematically build and mature their cybersecurity capabilities.
Phase 1: Establish Governance
The foundation of any successful cyber resilience program is strong governance. This phase focuses on defining executive ownership and establishing clear accountability across both IT and OT environments.
Executive Sponsorship
Secure buy-in and active support from senior leadership. Cybersecurity must be seen as a strategic business imperative, not merely an IT concern. This ensures adequate resources, budget, and organizational priority for cyber resilience initiatives.
Cross-Functional Leadership
Form a dedicated steering committee or task force comprising representatives from IT, OT, engineering, legal, risk management, and executive leadership. This multidisciplinary approach ensures all perspectives are considered and fosters collaboration.
Policy Development
Develop and formally document cybersecurity policies and procedures specific to the smart factory environment. These policies should align with relevant industry standards and regulatory requirements.
Budget Allocation
Allocate sufficient budget for cybersecurity investments, including technology, personnel, training, and ongoing services. This proactive investment is always less costly than reactive recovery from a major cyber incident.
Phase 2: Maturity Assessment
Before embarking on significant investments, it’s crucial to understand the current state of cyber resilience. This phase involves evaluating existing cybersecurity capabilities against global best practices to identify critical gaps.
Current State Analysis
Conduct a comprehensive assessment of the factory’s current cybersecurity posture for both IT and OT systems. This can involve third-party audits, vulnerability assessments, and penetration testing.
Gap Analysis
Compare the current state against recognized frameworks like NIST CSF or IEC 62443 to identify specific areas where the organization falls short.
Prioritization
Based on the gap analysis and risk assessment, prioritize the identified gaps and vulnerabilities. Not all gaps can be addressed simultaneously, so focus on those that pose the greatest risk to critical operations.
Baseline Establishment
Establish a baseline of cybersecurity maturity from which progress can be measured. This provides a clear benchmark for future improvements.
Phase 3: Protect Critical Production Assets
With governance in place and a clear understanding of current maturity, the focus shifts to protecting the assets whose disruption would cause a total production halt. This phase demands targeted investments.
Asset Prioritization
Identify and categorize critical production assets based on their impact on operations, safety, and business continuity if compromised. This involves understanding interdependencies between systems.
Targeted Security Investments
Prioritize security investments for these critical assets. This may include implementing specialized OT security solutions, advanced network segmentation, robust access controls, and more frequent vulnerability management for these specific components.
Disaster Recovery and Business Continuity for Critical Assets
Develop detailed recovery plans specifically for these high-priority assets, ensuring that mechanisms are in place for rapid restoration.
Implementation of Protective Controls
Deploy technical and administrative controls identified in the “Protect” function, focusing first on the most critical assets.
Phase 4: IT/OT Integration
Effective cyber resilience in smart factories hinges on seamless collaboration between IT and OT teams. This phase focuses on fostering this integration for unified monitoring and response.
Collaborative Teams
Create cross-functional teams that bring together IT security professionals and plant engineers. These teams should share knowledge, expertise, and responsibilities for securing the interconnected environment.
Unified Monitoring Systems
Implement Security Operations Center (SOC) solutions that can ingest and analyze data from both IT and OT environments. This provides a holistic view of the threat landscape and enables faster detection of anomalies.
Shared Processes and Procedures
Develop common processes for incident response, threat intelligence sharing, and vulnerability management that are understood and followed by both IT and OT personnel.
Cross-Training
Provide cross-training opportunities for IT and OT staff to enhance their understanding of each other’s domains. IT professionals can learn about industrial protocols and operational imperatives, while OT engineers can gain insights into cybersecurity best practices.
Phase 5: Continuous Resilience
Cyber threats are constantly evolving, so cyber resilience cannot be a one-time project. This final phase emphasizes ongoing efforts to maintain and continuously improve the security posture.
Ongoing Security Testing and Monitoring
Implement continuous security testing, including regular penetration testing, vulnerability assessments, and security audits. Maintain continuous monitoring of both IT and OT networks for suspicious activity.
Rigorous Supplier Cybersecurity Governance
Extend cybersecurity requirements to the supply chain. Vet third-party vendors for their security posture and enforce contractual obligations regarding cybersecurity. This is crucial given the risks associated with third-party access.
Threat Intelligence Sharing
Participate in industry-specific threat intelligence sharing programs to stay informed about emerging threats and vulnerabilities relevant to the manufacturing sector.
Continuous Improvement
Regularly review and update cybersecurity policies, procedures, and technologies based on new threats, technological advancements, and lessons learned from incidents or exercises. Cyber resilience must be an adaptive and evolving capability.
Leadership Imperatives: Driving the Shift
Beyond the technical roadmap, there are fundamental leadership shifts required to embed cyber resilience deeply within the organizational culture of a smart factory. These imperatives define a forward-thinking approach to security in the Industry 4.0 era.
Cybersecurity as Operational Risk
The narrative around cybersecurity must evolve from viewing it solely as a technical IT cost to recognizing it as a strategic operational risk. An outage caused by a cyberattack can severely impact production, supply chains, and safety. Therefore, managing cyber risk is synonymous with managing operational risk. This shift in perspective elevates cybersecurity to a board-level concern, necessitating proactive investment and integration into overall business strategy.
Specialized OT Expertise
The unique intersection of cybersecurity and industrial engineering requires specialized expertise. Organizations must invest in personnel who possess a deep understanding of both domains. This means either upskilling existing IT and OT teams or hiring dedicated industrial cybersecurity professionals. These individuals understand not only the intricacies of PLCs and SCADA systems but also the methods and motivations of threat actors targeting industrial environments.
Security-by-Design
Cybersecurity cannot be an afterthought; it must be embedded “by design” into all digital transformation and Industry 4.0 initiatives from day one. This proactive approach means considering security implications during the planning and design phases of new systems, processes, and factory upgrades, rather than attempting to bolt on security controls later. This ensures that security is an inherent characteristic of smart factory operations, not an additional layer. This also involves securing connected products and ensuring the entire lifecycle of a product, from design to end-of-life, considers security implications.
The Urgency of Action
The manufacturing sector has officially moved from experimentation to execution regarding Industry 4.0. The smart manufacturing market is projected to reach unprecedented valuations, with a significant portion of manufacturers already adopting or planning to adopt smart technologies. This rapid transformation underscores the urgency of building robust cyber resilience.
Fact remains: factories today invest millions in advanced automation and digital solutions, but often cyber resilience receives attention only after incidents happen. This reactive approach is no longer tenable in an era where cyberattacks can have devastating physical and economic consequences. The question for every manufacturing operation is not whether digital transformation works, but how fast they can deploy it across every facility, and critically, how securely.
The transition to a cyber-resilient smart factory requires a holistic approach that integrates technology, processes, and people. It demands a new mindset—one that sees cybersecurity as an enabler of innovation and operational continuity, rather than a hindrance. By embracing the NIST Core Lifecycle and prioritizing the leadership imperatives discussed, manufacturers can move from a state of heightened risk to one of continuous, autonomous cyber resilience, ensuring their smart factories are not just efficient, but also secure and robust against the evolving threat landscape. The future of manufacturing depends on it.
Your Path to Cyber Resilience Starts Here
Is your factory becoming cyber resilient as fast as it’s becoming connected? Don’t wait for an incident to reflect on the importance of cybersecurity. Partner with IoT Worlds to navigate the complexities of Industry 4.0 and build a truly resilient smart factory.
We offer expert guidance, strategic assessments, and tailored solutions to help you:
- Identify and protect your critical OT assets.
- Implement layered defenses and robust network segmentation.
- Develop OT-specific incident response and recovery plans.
- Foster seamless IT/OT integration.
- Achieve continuous cyber resilience with a security-by-design approach.
Ready to secure your smart factory’s future?
Contact us today to discuss your cyber resilience strategy: info@iotworlds.com