Power plants, the very heart of our modern society, literally fuel our daily lives. They are complex ecosystems of advanced machinery, intricate control systems, and critical infrastructure, all working in concert to generate and distribute the energy we depend on. In the 21st century, the efficiency and reliability of these power generation facilities hinge not only on mechanical integrity but increasingly on the robustness of their digital backbone. This digital transformation has brought immense benefits in terms of operational optimization and remote management, but it has also opened new avenues for potential vulnerabilities. The invisible battleground of cyberspace now extends directly into the operational technology (OT) networks of our critical energy infrastructure, making cybersecurity an indispensable component of power plant protection.
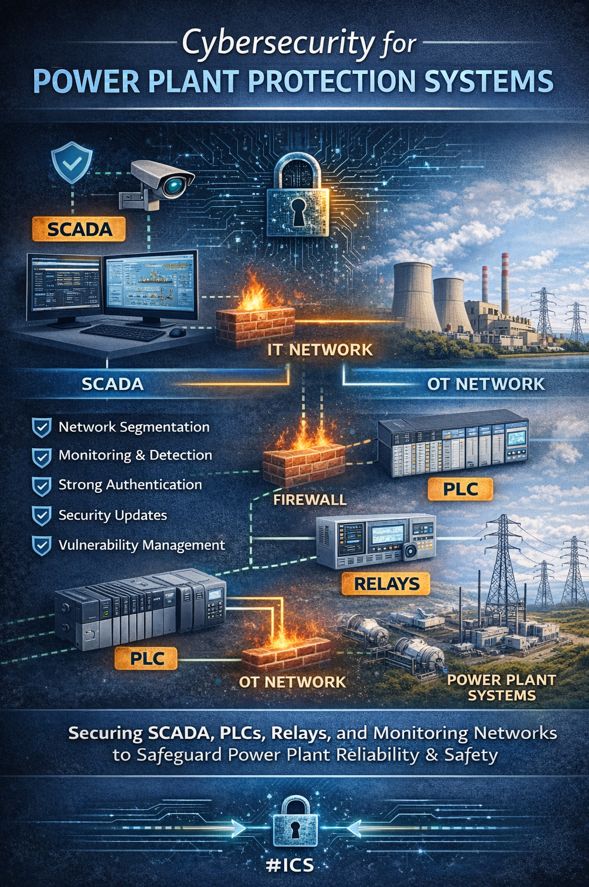
The interconnectedness of Information Technology (IT) and Operational Technology (OT) networks, once distinct and isolated, is now a defining characteristic of modern industrial control systems (ICS). This convergence, while offering unprecedented analytical capabilities and predictive maintenance opportunities, simultaneously presents an expanded attack surface for malicious actors. Safeguarding a nation’s power grid, therefore, requires a profound understanding of these integrated systems and a proactive, multi-layered approach to cybersecurity. This comprehensive guide delves into the essential cybersecurity practices for protecting power plant control systems, focusing on the critical roles of SCADA, PLCs, and protection relays in maintaining operational reliability and public safety.
The Foundation of Power Plant Operations: Understanding ICS Components
At the core of every modern power plant lie sophisticated industrial control systems (ICS). These are not merely computers but specialized hardware and software meticulously engineered to monitor, command, and control physical processes. Unlike typical IT systems where data confidentiality is often paramount, ICS prioritize continuous availability and real-time responsiveness. Any disruption, even momentary, can have severe consequences, ranging from equipment damage to widespread power outages. This fundamental difference necessitates a distinct cybersecurity philosophy, one that balances stringent security measures with the absolute requirement for uninterrupted operation.
Supervisory Control and Data Acquisition (SCADA) Systems
SCADA systems serve as the central nervous system of a power plant. They are distributed control systems that gather real-time data from various sensors and field devices across vast geographical areas, process this information, and present it to human operators through intuitive Human-Machine Interfaces (HMIs). Operators can then issue commands to control equipment remotely, adjust operational parameters, and respond to incidents.
In a power plant context, SCADA systems oversee a myriad of functions, including turbine control, generator synchronization, fuel handling, water treatment, and electrical grid management. They provide a macroscopic view of the entire operation, enabling optimization and ensuring stability. The data collected by SCADA systems is invaluable for long-term planning, predictive maintenance, and regulatory compliance.
From a cybersecurity perspective, the SCADA system’s role as the primary interface between human operators and physical processes makes it a high-value target. A compromised SCADA system could allow an attacker to shut down critical equipment, manipulate readings, or even initiate dangerous operational sequences, potentially leading to catastrophic failures or widespread service disruptions.
Programmable Logic Controllers (PLCs)
PLCs are rugged, industrial-grade computers designed to automate specific processes within the power plant. They act as the “brains” at the local level, receiving commands from the SCADA system or executing pre-programmed logic based on sensor inputs. PLCs directly control actuators such as valves, motors, circuit breakers, and relays, ensuring precise and real-time execution of operational sequences.
For instance, within a power plant, PLCs might manage the opening and closing of circuit breakers in a substation, control the flow of steam to a turbine, or regulate the speed of cooling pumps. Their deterministic nature and ability to operate in harsh industrial environments make them indispensable for critical process control. Unlike general-purpose computers, PLCs are built for reliability and longevity, often remaining in service for decades.
The cybersecurity implications for PLCs are profound. If a PLC is compromised, an attacker could directly manipulate physical processes, causing equipment damage, initiating unsafe conditions, or disrupting power generation. The longevity of PLCs also means that many older units may lack modern security features, making them particularly vulnerable if not properly secured within the network architecture. Hardening PLCs involves securing access to programming functions, ensuring firmware integrity, and providing physical safeguards.
Protection Relays
Protection relays are specialized devices designed to detect faults within the electrical grid and initiate appropriate actions to isolate the faulty section, thereby preventing damage to equipment and ensuring the stability of the power system. These devices operate rapidly and autonomously, often faster than human reaction times, to mitigate the impact of electrical disturbances like short circuits or overloads.
Modern protection relays are often microprocessor-based, incorporating advanced algorithms and communication capabilities. They constantly monitor electrical parameters such as voltage, current, and frequency. Upon detecting an anomaly that exceeds predefined thresholds, they send trip signals to circuit breakers to open and isolate the affected part of the grid.
While traditional relays were electromechanical and functioned in isolation, contemporary digital relays are often networked, communicating with each other, PLCs, and SCADA systems to provide comprehensive grid protection. This connectivity, while enhancing coordination and responsiveness, also introduces potential cybersecurity risks. A sophisticated cyberattack targeting protection relays could disable their protective functions, leading to cascade failures across the grid, or even trick them into tripping healthy circuits, causing unnecessary outages.
The Converging Landscape: IT and OT Networks
Historically, operational technology (OT) networks, which govern systems like SCADA, PLCs, and relays, were largely isolated from information technology (IT) networks. This “air gap” offered a basic level of security through obscurity and physical separation. However, the relentless drive for efficiency, data analytics, and remote management has led to a significant convergence of IT and OT environments. This convergence, while offering unprecedented control and data insights, has fundamentally altered the security posture of power plants.
The Evolution of Connectivity in Power Plants
The “air gap” model, while simple, was inherently inefficient for modern operations. Plant managers sought real-time data for enterprise resource planning, predictive maintenance, and regulatory reporting. Remote access became a necessity for technicians and engineers, especially in distributed power generation or grid management. This led to the gradual bridging of IT and OT networks, often through firewalls and specialized gateways.
Today, this convergence means that critical OT systems may be accessible, directly or indirectly, from the enterprise network, and in some cases, even the internet. While this connectivity enhances operational visibility and enables advanced analytics, it also means that cyber threats originating from the IT side – such as ransomware or phishing attacks – can potentially traverse into the OT domain. Adversaries recognize that compromising industrial systems can have far more severe impacts than disrupting corporate IT networks.
Distinguishing IT and OT Security Paradigms
It is crucial to understand that cybersecurity for OT environments cannot simply mirror IT security practices. While there are overlaps, the fundamental priorities and operational constraints differ significantly:
- Priorities: IT security typically prioritizes confidentiality, integrity, and availability (CIA triangle). For OT, the hierarchy is often reversed: availability, integrity, and then confidentiality. Continuous operation and safety are paramount. An outage or an erroneous control command can have physical, real-world consequences, including equipment damage, environmental harm, or loss of life.
- System Lifecycles: OT systems, like PLCs and relays, have much longer operational lifecycles, often spanning decades. This means they may run on older operating systems or firmware that cannot be easily updated or patched without risking stability. IT systems, in contrast, are typically refreshed and patched frequently.
- System Resiliency: OT systems are designed for extreme reliability and deterministic operation. Patches or updates that might be considered “safe” in an IT context could introduce latency or unexpected behavior in an OT system, leading to outages.
- Proprietary Protocols and Hardware: OT environments frequently use proprietary communication protocols and specialized hardware not commonly found in IT networks. This requires specialized security tools and expertise.
- Physical Consequences: A cyberattack on an OT system can have direct physical consequences, including equipment destruction, environmental damage, or dangers to human life. An IT attack typically results in data loss or financial impact.
Ignoring these distinctions and applying IT security measures indiscriminately to OT networks can lead to operational disruptions, system instability, and ultimately, undermine the very safety and reliability they are meant to protect.
The Imperative of Cybersecurity for Power Plant Protection
The rising tide of cyber threats explicitly targeting industrial control systems underscores the urgent need for robust cybersecurity in power plants. Nation-state actors, eco-terrorists, and even financially motivated cybercriminals increasingly view critical infrastructure as a lucrative target. The consequences of a successful cyberattack on a power plant are far-reaching and potentially devastating.
Potential Impacts of Cyber Attacks
- Equipment Damage and Destruction: Malicious manipulation of control parameters, such as voltage or current, could lead to severe equipment stress, overheating, or catastrophic failure of transformers, turbines, or generators.
- Operational Disruptions and Downtime: Attacks designed to disrupt normal operations can lead to unscheduled shutdowns, forcing a plant offline. This results in significant financial losses from lost generation and potential contractual penalties.
- Large-Scale Power Outages: A coordinated attack across multiple components or facilities could trigger widespread blackouts, impacting cities, regions, and even entire national grids, with severe economic and social repercussions.
- Safety and Environmental Hazards: Tampering with safety instrumented systems (SIS) or environmental controls could lead to dangerous pressure buildups, uncontrolled chemical releases (in certain plant types), or other incidents that endanger plant personnel and surrounding communities.
- Data Theft and Espionage: While not directly affecting operations, the theft of intellectual property, operational data, or classified information related to plant design and processes can be highly damaging, compromising national security or competitive advantage.
- Reputational Damage and Regulatory Penalties: A successful cyberattack can severely damage a power company’s reputation, erode public trust, and lead to substantial regulatory fines for non-compliance with cybersecurity standards.
The increasing connectivity means that without proper cybersecurity, critical assets are exposed to an ever-evolving threat landscape. Safeguarding these assets is not merely a technical challenge; it is a matter of national security, economic stability, and public safety.
Key Cybersecurity Practices for Power Plant Control Systems
Protecting the complex environment of a power plant requires a multi-faceted, “defense-in-depth” approach. This framework combines administrative, technical, and physical safeguards to create multiple layers of defense, making it significantly harder for an attacker to achieve their objectives. The following practices are fundamental to securing SCADA, PLCs, and protection relays.
Network Segmentation Between IT and OT Environments
Network segmentation is arguably the most critical defensive measure for power plant cybersecurity. It involves dividing the overall network into smaller, isolated segments based on function, criticality, and security posture. The most fundamental form of segmentation in a power plant is the robust separation between the IT (business) network and the OT (industrial control) network.
- Establishing Demilitarized Zones (DMZs): A properly designed architecture will include a secure DMZ between the IT and OT networks. This zone acts as a secure buffer, hosting services that require communication between both worlds, such as data historians, patch management servers, or remote access gateways. All traffic attempting to cross the IT/OT boundary must pass through and be inspected by devices within this DMZ.
- VLANs and Subnetting: Within the OT network itself, further segmentation using Virtual Local Area Networks (VLANs) and careful subnetting should be implemented. Critical control systems (e.g., PLCs, protection relays) should reside in logically separate network segments from less critical systems or engineering workstations. This limits the lateral movement of an attacker should one segment be compromised.
- Firewalls and Access Control Lists (ACLs): Industrial firewalls are deployed at the boundaries of each segment to control traffic flow. These firewalls are configured with strict Access Control Lists (ACLs) that permit only essential communication between segments based on the principle of least privilege. For example, a PLC network should only allow communication with its corresponding HMI or SCADA server, and only on specific ports and protocols.
- Unidirectional Gateways: For extremely critical data flows, such as outbound data from OT to IT for reporting, unidirectional gateways (also known as data diodes) can be employed. These hardware devices physically ensure that data can only flow in one direction, preventing any potential inbound attacks from reaching the OT network.
Effective network segmentation minimizes the blast radius of an attack, containing compromises to isolated segments and preventing them from spreading across the entire operational environment. It also facilitates targeted monitoring and detection efforts.
Continuous Monitoring & Threat Detection
Even with robust preventative measures, no system is entirely impenetrable. Continuous monitoring and threat detection are essential for identifying and responding to malicious activities in real-time. This involves a combination of technologies and processes tailored for the OT environment.
- Intrusion Detection/Prevention Systems (IDS/IPS): Specialized industrial IDS/IPS solutions are deployed within OT network segments. Unlike traditional IT IDS/IPS, these systems are designed to understand proprietary industrial protocols (e.g., Modbus, DNP3, IEC 61850) and detect anomalies in command structures or unusual traffic patterns indicative of an attack.
- Security Information and Event Management (SIEM) for OT: A SIEM system aggregates and analyzes security logs and events from various sources across both IT and OT networks. An OT-specific SIEM integrates data from PLCs, RTUs, SCADA servers, industrial firewalls, and network devices to provide a unified view of security posture and facilitate rapid incident response.
- Anomaly Detection: Machine learning and behavioral analytics are increasingly used to establish baseline “normal” behavior for industrial processes and network traffic. Any deviation from this baseline, such as unusual commands, unauthorized configuration changes to a PLC, or unexpected communication between devices, triggers an alert.
- Asset Inventory and Configuration Management: Maintaining an up-to-date inventory of all connected devices (PLCs, HMIs, relays, etc.) and their configurations is fundamental. Continuous monitoring ensures that no unauthorized devices are connected and that configurations remain consistent with security policies.
- Physical Security Monitoring: Given the physical consequences of OT attacks, integration of physical security systems, such as video surveillance in control rooms and restricted access areas, with cybersecurity monitoring can provide a holistic view and aid in correlating cyber and physical events.
Continuous monitoring enables early detection of threats, allowing operators and security teams to respond swiftly and mitigate potential damage. It’s a proactive stance that acknowledges the dynamic nature of cyber threats.
Strong Authentication & Access Control
Access control is the cybersecurity practice of restricting access to network resources and functions based on the identity of the user or device and its associated permissions. In power plant environments, strong authentication and granular access control are paramount to prevent unauthorized access and manipulation of critical systems.
- Multi-Factor Authentication (MFA): MFA should be implemented wherever possible, especially for remote access, privileged accounts, and access to critical control systems (SCADA, PLC programming interfaces, engineering workstations). This requires users to provide two or more verification factors (e.g., something they know like a password, something they have like a token, something they are like a fingerprint).
- Principle of Least Privilege: Users and systems should only be granted the minimum level of access and permissions necessary to perform their assigned tasks. For example, a plant operator might have read-only access to certain PLC parameters, while an engineer would have write access for configuration changes, but only when authorized and logged.
- Role-Based Access Control (RBAC): RBAC defines permissions based on a user’s role within the organization (e.g., SCADA operator, maintenance technician, system administrator). This streamlines permission management and ensures consistency.
- Session Management: Implement secure session management practices, including automatic logout after inactivity, limitations on session duration, and secure handling of session tokens.
- Device Authentication: Beyond human users, devices themselves should be authenticated before being allowed to communicate on the OT network. This can involve digital certificates or unique hardware identifiers.
- Secure Engineering Workstations (EWS): Engineering workstations, used for PLC programming and configuration, are high-privilege assets. They require stringent hardening, including golden images, MFA-backed access (perhaps via jump hosts), strict toolchain governance, and logging of programming actions.
Strong authentication and access control act as a gatekeeper, ensuring that only authorized and verified entities can interact with the power plant’s control systems.
Regular Security Updates and Patch Management
While OT systems often have unique challenges with patching, it remains a critical aspect of cybersecurity. Software vulnerabilities are constantly discovered, and attackers exploit these weaknesses to gain unauthorized access or cause disruption.
- Planned Patching Cycles (Maintenance Windows): Unlike IT, where continuous patching is common, OT patching often requires careful planning and coordination with operational teams. Patches must be rigorously tested in a non-production environment before deployment to ensure compatibility and prevent operational disruptions. This typically occurs during scheduled maintenance windows.
- Vendor Communication: Close collaboration with ICS vendors is essential to understand their patching policies, receive security advisories, and obtain verified updates specifically for industrial hardware and software.
- Virtual Patching/Compensating Controls: When immediate patching is not feasible due to operational constraints or legacy systems, virtual patching or compensating controls can be employed. Virtual patching utilizes IDS/IPS rules or firewall policies to block known exploit attempts for unpatched vulnerabilities. Other compensating controls might include further network segmentation or enhanced monitoring.
- Firmware Integrity: For devices like PLCs and relays, ensuring the integrity of firmware is crucial. Secure boot mechanisms and firmware signing can help detect and prevent the execution of malicious or unauthorized firmware.
- Vulnerability Management Program: A comprehensive vulnerability management program involves regularly scanning OT networks for known vulnerabilities, assessing their risk, and prioritizing remediation efforts. This process must account for the unique operational constraints of industrial environments.
Striking the right balance between security and operational continuity is key for patch management in power plants. While 100% immediate patching may not always be possible, a systematic and risk-based approach is vital.
Firewalls and Secure Communication Channels
Firewalls are the frontline defenders in network security, acting as gatekeepers that inspect and filter network traffic between different security zones. In a power plant, they are essential for secure communication. Beyond firewalls, ensuring the security of the communication channels themselves is equally important.
- Industrial-Grade Firewalls: Deploy industrial-grade firewalls specifically designed for OT environments. These firewalls are often ruggedized and capable of deep packet inspection for industrial protocols, providing more granular control over OT traffic than standard IT firewalls.
- Stateful Inspection and Deep Packet Inspection: Firewalls should utilize stateful inspection to track the state of network connections and only allow legitimate responses to outbound requests. Deep Packet Inspection (DPI) allows the firewall to examine the payload of industrial protocol packets, identifying malicious commands or anomalous data within the application layer.
- Virtual Private Networks (VPNs): For any remote access to the power plant network, VPNs must be used. VPNs create encrypted tunnels over public networks, ensuring the confidentiality and integrity of data in transit. Strong encryption algorithms and robust authentication for VPN access are critical.
- Encrypted Communication Protocols: Where possible, leverage encrypted versions of communication protocols within the OT network. For example, using Secure Shell (SSH) for remote terminal access instead of unencrypted Telnet, or implementing Transport Layer Security (TLS) for SCADA-HMI communication.
- IPsec for Process-Level Communications: For critical, real-time communications between PLCs or intelligent electronic devices (IEDs) across different zones, IPSec (Internet Protocol Security) can provide end-to-end encryption and authentication, protecting against eavesdropping and tampering.
- Demilitarized Zone (DMZ) Firewalls: As mentioned in network segmentation, firewalls guarding the DMZ are crucial. They meticulously control what traffic from the IT network can even reach the intermediary systems, let alone the internal OT network.
Firewalls and secure communication channels collectively create a robust barrier against external threats and ensure that legitimate communications are protected from interception or manipulation.
Beyond the Technical: A Holistic Approach to Power Plant Cybersecurity
While technical controls form the backbone of power plant cybersecurity, a truly resilient defense requires a holistic strategy encompassing people, processes, and continuous improvement.
Collaboration Between Specialists
The complexity of power plant cybersecurity demands a multidisciplinary approach. Effective protection relies heavily on seamless collaboration among:
- Cybersecurity Specialists: Experts in network security, incident response, vulnerability management, and threat intelligence.
- Automation Engineers: Deep understanding of PLCs, SCADA systems, control logic, and industrial processes.
- Power System Engineers: Expertise in grid operations, electrical principles, and the physical impacts of control system actions.
This collaboration ensures that security measures are technically sound, operationally feasible, and do not inadvertently compromise the safety or reliability of the power system. Misunderstandings between these groups can lead to security gaps or, conversely, operational disruptions from ill-conceived security implementations.
Security Awareness and Training
The human element remains one of the greatest vulnerabilities. Employees, from control room operators to maintenance technicians, must be educated on cybersecurity risks and best practices.
- Phishing and Social Engineering Training: Regular training to recognize and report phishing attempts and other social engineering tactics.
- Secure Access Practices: Training on strong password hygiene, multi-factor authentication usage, and secure remote access procedures.
- Incident Reporting: Empowering all personnel to recognize and report suspicious activities or potential security incidents immediately.
- Physical Security Protocols: Reinforcing the importance of physical security measures, such as badge access, visitor protocols, and preventing unauthorized device connections.
A well-informed workforce acts as an additional layer of defense, capable of identifying and preventing attacks that bypass automated systems.
Incident Response and Recovery Planning
Despite all preventative measures, a cyber incident is a real possibility. Having a well-defined and regularly tested incident response plan is crucial for minimizing the impact of an attack.
- Preparation: Establishing an incident response team, defining roles and responsibilities, creating communication protocols, and developing playbooks for various incident types.
- Detection and Analysis: Procedures for identifying, confirming, and categorizing security incidents. This heavily relies on effective monitoring and detection tools.
- Containment: Steps to prevent the incident from spreading and causing further damage, such as isolating affected systems or network segments.
- Eradication: Removing the root cause of the incident, such as malware or compromised accounts, and patching vulnerabilities.
- Recovery: Restoring affected systems and data to normal operation, which might involve restoring from secure backups or rebuilding systems.
- Post-Incident Lessons Learned: Analyzing the incident to identify weaknesses in security posture and improve future prevention and response capabilities.
Regular drills and tabletop exercises are vital to ensure the incident response team is prepared to act effectively under pressure.
Regular Audits and Compliance
Ongoing vigilance is essential. Power plants must adhere to industry-specific cybersecurity standards and regulations, such as those mandated by NERC CIP (North American Electric Reliability Corporation Critical Infrastructure Protection) in the US, or relevant national and international standards like IEC 62444 and NIST SP 800-82.
- Internal and External Audits: Regularly conducting security audits, both internal and by independent third parties, to assess compliance with regulations and identify gaps in security controls.
- Penetration Testing: Ethical hacking exercises to simulate real-world attacks, identify vulnerabilities, and test the effectiveness of existing defenses. These should be conducted cautiously in OT environments, often starting with network reconnaissance and vulnerability assessments rather than direct attacks on live systems.
- Vulnerability Assessments: Proactive scanning and analysis of systems to identify known security weaknesses that could be exploited by attackers.
- Documentation: Maintaining comprehensive documentation of security policies, procedures, network architectures, and control configurations is crucial for compliance, audits, and effective incident response.
Adherence to these standards and continuous validation of security measures ensure that power plants maintain a robust and compliant cybersecurity posture in the face of evolving threats.
Securing the Future: Digital Substations and Smart Grids
The energy sector is in a continual state of evolution, moving towards increasingly sophisticated and interconnected systems. Digital substations and smart grids represent the future of power distribution, promising greater efficiency, reliability, and renewable energy integration. However, this advancement also amplifies the cybersecurity challenges.
Digital Substations
Traditional substations rely on copper wiring and analog signals for control and communication. Digital substations, in contrast, leverage fiber optics and standardized digital communication protocols (like IEC 61850) for significantly enhanced data exchange, diagnostic capabilities, and flexibility.
While digital communication offers numerous operational benefits, it also means that more devices within the substation, including protection relays and control units, are connected to a network. This increased connectivity expands the potential attack surface. Cybersecurity in digital substations must therefore focus on securing these digital communication channels, ensuring the integrity of data exchange, and protecting intelligent electronic devices (IEDs) from compromise.
Smart Grids
Smart grids are advanced electrical grids that use information and communication technologies to gather information, such as information about the behavior of suppliers and consumers, in an automated fashion to improve the efficiency, reliability, economics, and sustainability of the production and distribution of electricity. This includes distributed power generation, microgrids, and demand-response systems.
The smart grid paradigm introduces an unprecedented level of complexity and connectivity, extending the attack surface from large centralized power plants to millions of distributed smart meters, sensors, and control devices. Securing the smart grid requires:
- End-to-End Security: Implementing security measures across the entire ecosystem, from generation to consumption points.
- Supply Chain Security: Ensuring the security of all components and devices integrated into the smart grid, from manufacture to deployment.
- Advanced Analytics and AI: Leveraging artificial intelligence and machine learning for real-time anomaly detection and predictive threat analysis across a massive, complex network.
- Secure Interoperability: Ensuring that diverse systems and devices from multiple vendors can communicate securely.
The transition to digital substations and smart grids necessitates an even greater emphasis on close collaboration between cybersecurity specialists, automation engineers, and power system engineers. Security must be designed in from the ground up – “security by design” – rather than being an afterthought.
Conclusion: Safeguarding Our Energy Lifeline
The reliability and safety of our energy infrastructure are non-negotiable. Modern power plants, with their intricate web of SCADA systems, PLCs, and protection relays, represent the critical nodes in this infrastructure. As the lines between IT and OT continue to blur, the threat landscape becomes more sophisticated and pervasive. The invisible battleground of cyberspace demands our unwavering attention and commitment to robust defense.
By diligently implementing key cybersecurity practices—network segmentation, continuous monitoring and threat detection, strong authentication and access control, regular security updates, and robust firewalls and secure communication channels—we build resilient defenses around our power plants. This is not merely a technical endeavor but a strategic imperative that requires ongoing vigilance, cross-functional collaboration, and a deep understanding of both cyber and physical risk. Securing these vital systems is a continuous journey, not a destination. It is about protecting the very heartbeat of our modern world, ensuring that the lights stay on, industries keep running, and communities thrive. The future of power depends on our ability to outpace threats and innovate equally in the realm of cybersecurity as we do in energy generation.
Are you ready to fortify your power plant’s defenses against the ever-evolving cyber landscape? IoT Worlds offers expert guidance and solutions tailored to the unique challenges of operational technology security. Protect your critical infrastructure, ensure uninterrupted operations, and safeguard public safety. Contact us today to discuss your specific cybersecurity needs.
Email us at info@iotworlds.com to learn more.