When the topic of data centers arises, the immediate images that often spring to mind are rows of humming servers, elaborate power infrastructure, and sophisticated cooling systems. While these components are undoubtedly vital, they represent only part of the story. The true unsung hero, the invisible force that orchestrates every digital interaction, every cloud workload, and every AI model training job, is the data center network path.
This path isn’t merely a series of cables connecting devices; it’s a meticulously engineered ecosystem designed for speed, resilience, and intelligence. A well-designed data center network path is the product of strategic architectural choices, advanced routing protocols, robust security measures, and precise automation, all working in concert to ensure that data flows seamlessly and efficiently from Point A to Point B. In today’s hyper-connected world, where microseconds can dictate success and failure, understanding this intricate dance of data is no longer a technical niche—it’s a business imperative.
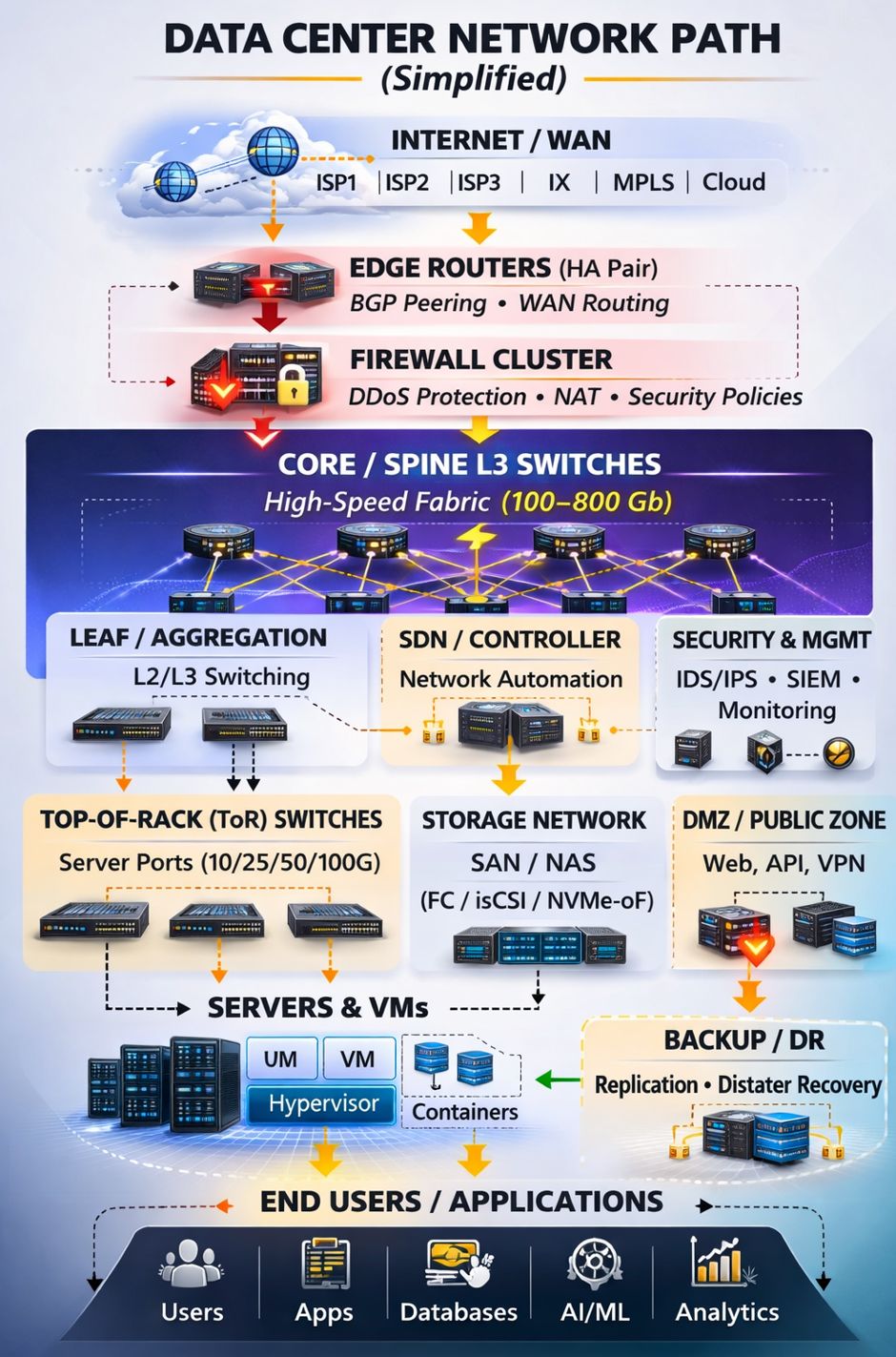
From the moment a user initiates a request to the rapid crunching of an AI algorithm, the network path is the silent conductor. It determines not just connectivity, but also:
- Low Latency: Where microseconds matter, the network path minimizes delays, crucial for real-time applications and user experience.
- Redundancy: Engineered for resilience, it eliminates single points of failure, ensuring continuous operation.
- Scalability: Built for future growth, it accommodates ever-increasing data volumes and user demands without disruption.
- Deterministic Performance: It provides predictable and stable traffic flow, crucial for mission-critical workloads.
- Operational Visibility: Real-time insights into network behavior enable proactive management and optimization.
As workloads become more distributed, and the demands of Artificial Intelligence (AI) and High-Performance Computing (HPC) continue to grow, the design of the network path transcends a mere infrastructure discussion. It evolves into a critical conversation about business continuity, competitive advantage, and the very foundation of digital success. In modern digital infrastructure, the network path isn’t just a component; it is the product. This article will unravel the complexities of this hidden powerhouse, simplifying its layers and demonstrating its profound impact.
The Journey Begins: Connecting to the Outside World
The digital heartbeat of any data center starts with its connection to the vast expanse of the internet and Wide Area Networks (WANs). This outer layer is the gateway through which all external traffic enters and exits the data center, making its design paramount for global reach and service availability.
Internet/WAN: The Global Gateway
At the very top of the data center network stack lies the Internet/WAN layer. This represents the external networks that connect the data center to the rest of the world. It’s the critical interface for everything from user requests to distributed cloud services and inter-datacenter communication.
Key components at this layer include:
- Internet Service Providers (ISPs): Typically, data centers connect to multiple ISPs (e.g.,
ISP1,ISP2,ISP3). This multi-homing strategy is crucial for redundancy, ensuring that if one ISP experiences an outage, traffic can be rerouted through others, maintaining service continuity. It also allows for traffic engineering, where specific traffic can be directed through the most performant or cost-effective ISP link. - Internet Exchange Points (IXs): These are physical infrastructure where multiple ISPs, content delivery networks (CDNs), and other network providers interconnect with each other directly. Connecting to IXs can reduce latency and improve peering efficiency by allowing traffic to exchange directly instead of transiting through intermediate networks.
- MPLS (Multiprotocol Label Switching): Often used for connecting to enterprise WANs or for internal data center-to-data center links, MPLS provides a high-performance routing technique that can prioritize certain types of traffic and create virtual private networks (VPNs) for secure and reliable communication over shared network infrastructure.
- Cloud: Data centers frequently interconnect directly with public cloud providers to facilitate hybrid cloud deployments, multi-cloud strategies, and direct data exchange with cloud-hosted services.
Edge Routers: The Traffic Directors
Immediately downstream from the Internet/WAN are the Edge Routers. These high-performance devices are the first point of entry (or last point of exit) for all IP traffic flowing into and out of the data center.
- High-Availability (HA) Pair: Edge routers are almost always deployed in an
HA Pairconfiguration. This means two or more routers operate together, providing redundancy and automatic failover. If one router fails, the other seamlessly takes over its duties, preventing any disruption to external connectivity. - BGP Peering: Border Gateway Protocol (BGP) is the routing protocol used to exchange routing information between different autonomous systems on the internet.
Edge RoutersutilizeBGP Peeringto communicate with the ISPs and other external networks, learning about available routes and advertising routes for the data center’s own IP addresses. This intelligent peering enables dynamic traffic management and resilience. - WAN Routing: Beyond BGP, these routers handle general
WAN Routing, making decisions about which path external traffic should take, often optimizing for factors like latency, cost, or available bandwidth.
Firewall Cluster: The First Line of Defense
Following the Edge Routers, all incoming and outgoing traffic passes through a Firewall Cluster. This critical layer is the first comprehensive security checkpoint for the data center.
- DDoS Protection: The firewall cluster is instrumental in defending against Distributed Denial of Service (DDoS) attacks by identifying and dropping malicious traffic before it can overwhelm internal systems.
- NAT (Network Address Translation): Firewalls often perform NAT, translating private internal IP addresses into public IP addresses and vice-versa. This conserves public IP addresses and adds a layer of security by hiding the internal network topology.
- Security Policies: Crucially, firewalls enforce
Security Policies. These rules dictate which types of traffic are allowed or denied based on source, destination, port, and application. They protect internal resources from unauthorized access and prevent sensitive data from exfiltrating the network.
The robust design of these initial layers ensures not only ubiquitous connectivity but also a resilient and secure perimeter, safeguarding the entire data center infrastructure from external threats and disruptions.
The Internal Highway: Fabric and Switching Architecture
Once traffic successfully navigates the external gateways and security perimeter, it enters the heart of the data center: the internal network fabric. This is where the majority of data center traffic—known as east-west traffic (server-to-server communication within the data center)—resides, and its efficient design is paramount for application performance.
Core / Spine L3 Switches: The Backbone of the Fabric
At the core of the internal network architecture are the Core / Spine L3 Switches. These powerful switches form the backbone of a modern data center network, typically employing a spine-leaf architecture.
- High-Speed Fabric (100-800 Gb): These switches are characterized by their immense aggregate bandwidth, creating a
High-Speed Fabriccapable of moving data at speeds ranging from100 Gbto800 Gband beyond. This high capacity is essential for supporting the intense traffic demands of modern applications, virtualization, and advanced workloads like AI/ML. - Spine-Leaf Architecture: This architecture, a type of Clos network, is the dominant topology in modern data centers due to its inherent advantages for east-west traffic. Instead of the traditional three-tier (core-aggregation-access) model which introduced chokepoints, spine-leaf offers a flat, high-bandwidth, and low-latency network.
- Spine Layer: Comprised of
Core / Spine L3 Switches, this layer is the backbone, connecting to every leaf switch. There are no direct connections between spine switches. - Consistent Latency: Every leaf switch is exactly two hops away from any other leaf switch (via a spine switch), providing
Consistent (fixed hop count)latency profile. This predictability is vital for applications requiring deterministic performance. - ECMP (Equal-Cost Multi-Path): Spine-leaf architectures leverage ECMP, where multiple equal-cost paths exist between any two points. This allows traffic to be distributed across all available links, maximizing
throughputandresilience. If a link fails, traffic is automatically routed over the remaining paths. - Scalability: The
Spine-leafmodel offersStrong (add spines/leaves)east–west scaling. Capacity can be expanded by adding more spine or leaf switches without requiring a complete redesign of the network. This makes it highly flexible for growth. - Failure Isolation:
a spine or leaf can fail without collapsing the entire network.
- Spine Layer: Comprised of
Leaf / Aggregation: Connecting the Racks
Directly connected to the spine layer are the Leaf / Aggregation switches. These switches aggregate traffic from the server racks and provide connectivity upwards to the spine.
- L2/L3 Switching: Leaf switches perform both Layer 2 (L2) and Layer 3 (L3) switching functions. L2 switching handles traffic within the same VLAN (Virtual Local Area Network), while L3 switching routes traffic between different VLANs or subnets. Their role is to provide connectivity to the
Top-of-Rack (ToR) Switchesand manage traffic within their connected server segments.
ToP-of-Rack (ToR) Switches: The Server Connectors
At the lowest level of the switching hierarchy, within each server rack, are the Top-of-Rack (ToR) Switches.
- Server Ports (10/25/50/100G):
ToR Switchesare directly connected to individual servers and other network devices within their respective racks. They provide high-speedServer Portsranging from10 Gbto100 Gb(and increasingly higher, as400Gand800Goptics emerge), ensuring ample bandwidth for all devices in the rack. - Physical Infrastructure: These switches are integral to the
physical infrastructureof the data center, directly connecting physical servers and enabling data flow to and from the applications running on them. The choices ofoptics and cablesat this layer are crucial for performance.
The Role of Software-Defined Networking (SDN)
Modern data center networks, especially those built on spine-leaf architectures, heavily leverage SDN / Controller technologies.
- Network Automation: An
SDN Controllercentralizes the control plane of the network, enablingNetwork Automation. This means policies can be defined globally and automatically pushed down to individual switches, simplifying configuration, reducing human error, and speeding up deployment of network changes. - Traffic Engineering: SDN allows for advanced
traffic engineering algorithmsto optimize performance, dynamically adjusting routes based on real-time network conditions. Google’s Jupiter network, for example, transformed its Clos fabric usingcentralized Software-Defined Networking (SDN) control for traffic engineering. - Programmability: SDN introduces programmability to the network, allowing administrators to programmatically control network behavior, allocate resources, and prioritize traffic, which is particularly beneficial for complex, dynamic workloads like those found in cloud and AI environments.
The combination of a robust, high-speed fabric with intelligent SDN control creates a network infrastructure that is not only fast and resilient but also highly adaptable and manageable, a prerequisite for the demands of the digital age.
Dedicated Networks: Storage, Security, and Management
Beyond the primary data forwarding path, modern data centers incorporate several specialized networks and zones critical for storing data, managing infrastructure, and isolating specific workloads. These dedicated segments ensure optimal performance, enhanced security, and efficient operations.
Storage Network: The Data Repository Backbone
Data is the lifeblood of any organization, and a robust Storage Network is essential for its efficient access, management, and protection. This network is typically separate from the main data network to avoid congestion and ensure high-speed access to storage resources.
Common technologies within the storage network include:
- SAN (Storage Area Network): A dedicated, high-speed network that allows servers to access shared pools of block-level storage. SANs are ideal for applications requiring high I/O performance, such as databases and virtualized environments.
- NAS (Network-Attached Storage): Provides file-level data storage services to computer networks. NAS devices are often used for file sharing, backups, and archiving.
- FC (Fibre Channel): The traditional high-speed protocol for SANs, offering low latency and high throughput.
- iSCSI (Internet Small Computer Systems Interface): A protocol that allows SCSI commands to be sent over a standard IP network, enabling block-level storage access over Ethernet infrastructure.
- NVMe-oF (NVMe over Fabrics): A newer technology designed for high-performance, low-latency access to NVMe (Non-Volatile Memory Express) flash storage over a network. It utilizes various network fabrics (Ethernet, Fibre Channel, InfiniBand) to extend the performance benefits of NVMe beyond local storage. This is becoming increasingly important for AI/ML workloads that demand extreme storage speeds.
The design of the Storage Network directly impacts application performance, data integrity, and disaster recovery capabilities. It represents a critical path for data persistence and retrieval.
DMZ / Public Zone: Secure Exposure for External Services
The DMZ (Demilitarized Zone) / Public Zone is a crucial network segment designed to host services that need to be accessible from the internet while protecting the internal network. It acts as a buffer between the untrusted external network and the trusted internal network.
Services often deployed in the DMZ / Public Zone include:
- Web Servers: Hosting public-facing websites and web applications.
- API Gateways: Providing secure entry points for external applications to interact with internal services.
- VPN Servers: Enabling secure remote access for users or branch offices to the internal network.
By isolating these services in a DMZ, even if a vulnerability is exploited in a public-facing application, the attacker’s access is contained within the DMZ, preventing direct compromise of sensitive internal systems. Firewalls heavily segment the DMZ from both the internet and the internal network, enforcing strict security policies.
Security & Management (IDS/IPS, SIEM, Monitoring): The Watchtowers
A dedicated network, or at minimum, dedicated segments and appliances, are required for Security & Mgmt functions. These systems are constantly at work, monitoring network activity, detecting threats, and providing essential operational insights.
- IDS/IPS (Intrusion Detection/Prevention Systems):
IDSpassively monitors network traffic for suspicious activity and alerts administrators.IPSactively inspects traffic and can take automated actions to block or mitigate threats in real-time.
- SIEM (Security Information and Event Management): A
SIEMsystem centralizes logs and security events from all network devices, servers, and applications. It performs correlation and analysis to identify security incidents, compliance breaches, and potential threats. - Monitoring Systems: These systems continuously track the performance and health of all network devices, servers, and services. They collect metrics on bandwidth utilization, latency, CPU usage, memory, and error rates, providing the operational intelligence needed to maintain
Deterministic performanceandOperational visibility. This often includes tools forqueueing and dropsandoversubscription ratios.
These security and management layers are not just technical components; they are the eyes and ears of the data center, ensuring its integrity, performance, and compliance posture. Integrating network manageability into the design is non-negotiable.
The Workload Engine: Servers, Virtualization, and Containers
At the heart of the data center, where all the processing takes place, sits the vibrant ecosystem of servers, virtual machines, and containers. This is where applications reside, data is crunched, and digital services come to life. The efficiency of the network path connecting these compute resources is critical for overall performance.
Servers & VMs (Hypervisor): The Foundational Compute
The bedrock of any data center comprises SERVERS & VMs. These physical and virtual machines execute the instructions that power all applications and services.
- Physical Servers: These are the robust hardware units housing CPUs, memory, storage, and network interface cards (NICs). They provide the raw computational power required.
- Virtual Machines (VMs): Most modern data centers extensively utilize virtualization. A
Hypervisor(a software layer) runs directly on the physical server, enabling multipleVMsto share the server’s hardware resources. Each VM operates as an isolated, independent computer, capable of running its own operating system and applications.- Benefits of VMs: Virtualization enhances resource utilization, simplifies management, and provides flexibility for deploying and scaling applications. It also plays a key role in achieving
failure isolationandpredictable latencyby abstracting hardware dependencies.
- Benefits of VMs: Virtualization enhances resource utilization, simplifies management, and provides flexibility for deploying and scaling applications. It also plays a key role in achieving
- UM (Underlying Machine): Refers to the physical server itself, upon which the hypervisor and subsequent VMs or containers run.
The network connectivity to these servers, typically through the Top-of-Rack (ToR) Switches, needs to be high-bandwidth and low-latency to support the intense east–west traffic that often occurs between VMs.
Containers: Agile and Efficient Application Packaging
Building on the concept of virtualization, Containers offer an even more lightweight and agile way to package and run applications.
- How Containers Work: Unlike VMs, containers share the host operating system’s kernel. Each container encapsulates an application and all its dependencies (libraries, binaries, configuration files) in an isolated environment.
- Benefits of Containers:
- Efficiency: They are much lighter than VMs, starting faster and consuming fewer resources.
- Portability: A containerized application runs consistently across different environments, from a developer’s laptop to a staging server or a production data center.
- Scalability: Containers can be rapidly deployed, scaled up or down, and managed, making them ideal for microservices architectures and dynamic cloud-native applications.
- Integration with VMs/Hypervisors: Containers often run within VMs for an added layer of isolation and security, combining the benefits of both technologies.
The network path must be optimized to support the dynamic nature of containerized environments, including rapid scaling and efficient inter-container communication, which often occurs at extremely high rates within a single server or across multiple servers over the leaf-spine fabric.
Backup / DR: Ensuring Data Protection and Business Continuity
While not directly a compute layer, the Backup / DR (Disaster Recovery) segment is intrinsically linked to the Servers & VMs layer. It ensures that the critical data and applications residing on these compute resources are protected and can be restored in the event of failure.
- Replication: Data from primary
Servers & VMsis continuously or periodically replicated to backup systems or a geographically separateDisaster Recovery Data Center. This can be block-level, file-level, or application-level replication. - Disaster Recovery: In the event of a catastrophic failure, these systems are used to restore services, minimizing downtime and data loss. This critically relies on the
Storage Networkfor fast data transfer during replication and recovery.
The network connectivity for Backup / DR needs to be robust, secure, and offer sufficient bandwidth to handle large data transfers, especially during initial synchronization and ongoing replication, without impacting primary application performance.
Together, the Servers & VMs with Hypervisor, Containers, and Backup / DR form the core engine of the data center, leveraging the high-speed internal fabric to deliver computational services and ensure data resilience.
The End-User Experience: Applications and Data Flow
Ultimately, the entire data center network path exists to serve applications and their end-users. Every layer, every switch, every protocol, contributes to the seamless delivery of digital services, transforming raw data into meaningful experiences.
End Users / Applications: The Digital Destination
The END USERS / APPLICATIONS represent the culmination of the data center’s purpose. This encompasses a diverse array of digital consumers and services.
- Users: Individuals interacting with web applications, mobile apps, streaming services, or enterprise systems. Their experience is directly tied to the performance and reliability of the underlying network path.
- Apps: The software applications themselves, whether they are customer-facing portals, internal enterprise resource planning (ERP) systems, or specialized industry solutions.
- Databases: The repositories where structured and unstructured data are stored and retrieved, critical for nearly all applications. Database performance is heavily dependent on low-latency access to the
Storage Networkand efficient communication with application servers over theLeaf / AggregationandToR Switches. - AI/ML (Artificial Intelligence/Machine Learning): These advanced workloads demand immense computational power and high-speed data transfer.
AI/MLmodel training, for example, generates vast amounts ofeast–west trafficbetween GPUs and storage, placing extreme pressure on the latency and bandwidth of theHigh-Speed Fabric. - Analytics: Processing and analyzing large datasets to derive insights and inform business decisions. This often involves data-intensive queries that require both robust compute (
Servers & VMs) and high-throughput access to storage.
The network path, from the initial Internet/WAN connection through to the ToR Switches that connect to individual servers, dictates the quality of experience for End Users and the efficiency of Applications. Slow network paths translate to frustrated users, delayed insights, and inefficient AI model training.
The Flow of Traffic: North-South vs. East-West
Understanding the End Users / Applications context highlights two fundamental traffic patterns within a data center:
- North-South Traffic: This refers to traffic flowing into or out of the data center, generally between an
End User(external) and anApplication(internal), passing through theEdge RoutersandFirewall Cluster. Traditional three-tier network architectures were optimized for this type of traffic (client-server). - East-West Traffic: This refers to traffic flowing between different servers or applications within the data center—for example, a web server communicating with an application server, an application server querying a database, or multiple GPUs exchanging data during AI training.
'Modern workloads are east–west heavy', and theSpine-Leafarchitecture is specifically designed to handle this high volume of internal communication withconsistent latencyandECMP scaling.
The dominance of east-west traffic in modern workloads is a primary reason why data center network design has evolved dramatically, moving away from legacy models towards more distributed, high-bandwidth fabrics.
The Interplay and the Imperative of Design
Every interaction, every query, every inference journey through the data center network path. Consider:
- An
End Useron theInternet/WANaccesses a web application. - The request hits the
Edge Routers, passes through theFirewall Cluster. - It then traverses the
Core / Spine L3 Switchesto aLeaf / Aggregationswitch. - From there, it goes to a
ToR Switch, and finally reaches aWeb Serverrunning on aVMorContainer. - This
Web Servermight then communicate (east-west) with anApplication Server, which in turn queries aDatabase(over theStorage Network), and perhaps even interacts with anAI/MLmodel for personalized results. - All this internal traffic flows efficiently over the high-speed
Spine-Leaffabric. - Finally, the response travels reverse to the
End User.
This complex dance underscores why Data center network architecture determines throughput under real load because it controls hop count, congestion behavior, and failover—not just port speed. A suboptimal design can lead to tail-latency spikes, packet loss, and escalating operational overhead, severely impacting the End User experience and Application performance.
For any organization, the ability to seamlessly deliver digital services and process vast amounts of data relies entirely on the efficiency and resilience of this intricate network path. It’s no longer about simply connecting devices; it’s about architecting a competitive advantage.
Architectural Choices and Strategic Considerations
The simplified diagram of the data center network path showcases a highly optimized, modern architecture. However, data center network design is not a one-size-fits-all endeavor. The choices made at the architectural level profoundly impact performance, scalability, and operational efficiency.
Spine-Leaf (Clos) Architecture: The Modern Standard
As illustrated in our simplified network path, the Spine-Leaf architecture (a type of Clos network) has become the de facto standard for modern data centers. The web search results strongly reiterate this dominance.
Leaf–Spine (Clos) designs dominate.Spine–leafisBest for Modern, general-purpose DCs; high east–west traffic.Predictable latency: every leaf is exactly two hops away, which simplifies performance planning.ECMP scaling: multiple equal paths keep throughput balanced and resilient.Failure isolation: a spine or leaf can fail without collapsing the entire network.- Google’s
Jupiternetwork has successfully evolved usingClos topologiesanddirect-connect topologyapproaches.
This design paradigm directly addresses the overwhelming shift towards east–west traffic within data centers, ensuring that server-to-server communication, which is often the most voluminous, is handled with maximum efficiency and minimum latency. Concerns like high oversubscription, under-sized uplinks, weak upstream design are minimized with proper Spine-leaf implementation.
Three-Tier Architecture: When it Still Makes Sense
While Spine-leaf dominates, the legacy Three-tier (access/aggregation/core) architecture still has its place.
Best for Smaller or stable environments; legacy designs.When a Three-Tier Still Makes Sensesuggests its applicability forsmaller to midsize workloads, particularly wherenorth-south trafficis predominant andeast-west growthislimited.- However, it suffers from
more variable (more hops)latency profileandlimited at scaleeast–west scaling, leading toaggregation congestion, chokepoints, unpredictable latencyas east-west traffic grows.
For some specialized or smaller deployments, its Low–moderate operational complexity might still be advantageous, but generally, the trend is away from this model for general-purpose high-throughput environments.
Overlay Networks (VXLAN/EVPN): Logical Segmentation and Mobility
Modern data center networks aren’t just about physical topology; Logical controls play an equally critical role. Overlays (VXLAN/EVPN) are fundamental to providing advanced network capabilities over the underlying physical fabric.
Overlays (VXLAN/EVPN)provideSegmentation, MAC/IP mobility, multi-tenant routing options.- VXLAN (Virtual Extensible LAN): Extends Layer 2 networks over a Layer 3 underlay, allowing for greater scalability in terms of the number of virtual networks (VLANs) and enabling VM mobility across an entire data center fabric without reconfiguring the network.
- EVPN (Ethernet VPN): Provides a control plane for VXLAN, allowing for efficient distribution of MAC addresses and IP routes, improving scalability and enabling advanced features like active-active multi-homing.
Most commonly on an eBGP underlay for policy control and scale. TheeBGP(external BGP) running on theunderlayprovides robust routing for the physical network, whileVXLAN/EVPNcreates virtual networks asoverlaysthat are independent of the physical topology.This blueprint for how traffic moves through your data center—physically (devices and cabling) and logically (routing, segmentation, and policy)is critical.
These overlays are crucial for multi-tenancy, network segmentation for security, and enabling the flexible workload placement demanded by cloud environments and container orchestration platforms.
AI/ML Readiness: Ethernet RoCE vs InfiniBand
The explosive growth of AI and Machine Learning workloads introduces specific networking demands.
AI/ML Workloads: Ethernet RoCE vs InfiniBandhighlights a key architectural choice.- Remote Direct Memory Access (RDMA): AI/ML frameworks often benefit significantly from RDMA, which allows direct memory access between servers without involving the CPU, drastically reducing latency and increasing throughput.
- InfiniBand: Traditionally the high-performance interconnect of choice for HPC and AI clusters, offering extremely low latency and high bandwidth, inherently supporting RDMA.
- RoCE (RDMA over Converged Ethernet): Enables RDMA capabilities over standard Ethernet networks. This allows organizations to leverage their existing Ethernet infrastructure for AI/ML workloads, potentially reducing costs and complexity compared to deploying a separate InfiniBand network.
Congestion control tuning criticalfor both, as AI/ML traffic patterns can be bursty and sensitive to packet loss.High-throughput environments demand sustained and repeatable performance.
The decision between InfiniBand and RoCE often depends on the scale, performance requirements, and budget constraints of the AI/ML workload.
Optics and Cabling: The Physical Foundation
No discussion of network path is complete without mentioning the physical infrastructure of optics and cables.
400G today, 800G emerging, 1.6T with CPO on the horizon. The relentless demand for higher bandwidth in data centers drives continuous innovation in optical technologies.- Fiber Optic Cables: Dominant for high-speed connections within and between data center components, offering superior bandwidth and distance compared to copper.
- Transceivers: Convert electrical signals to optical signals for transmission over fiber. The speed of these transceivers dictates the port speed of switches (e.g.,
10/25/50/100GforToR Switches).
These physical components underpin the entire network, and their proper selection and deployment are critical to avoid bottlenecks and ensure the capacity for future growth.
The strategic architectural choices, from the network topology to the specific protocols and cabling, are foundational to how efficiently and effectively a data center operates. They define the capabilities that directly translate into competitive advantage for the businesses and applications they host.
The Digital Performance Imperative: Why the Network Path is the Product
In the relentless march of digital transformation, the data center network path has transcended its traditional role as a mere connectivity layer. It has evolved into a strategic asset, a differentiator, and, in essence, the very product of modern digital infrastructure. This shift is driven by several converging factors: the explosion of data, the relentless pursuit of real-time insights, the distributed nature of cloud-native applications, and the insatiable demands of AI and HPC workloads.
Microseconds Matter: The Latency Imperative
The statement “microseconds matter” is not hyperbole; it’s a fundamental truth in today’s digital economy.
- For financial trading, a difference of microseconds can mean millions in profit or loss.
- For online retail, every millisecond of latency can translate into decreased conversion rates and customer dissatisfaction.
- For autonomous systems, real-time decision-making is literally a matter of safety.
- For AI/ML training,
tail-latency spikescan prolong training times and waste expensive compute resources.
A poorly designed network path with excessive hops or congestion chokepoints directly translates into higher latency, undermining the performance of applications and the competitiveness of the business. The consistent (fixed hop count) nature of Spine–leaf architectures directly addresses this imperative.
Redundancy and Deterministic Performance: The Pillars of Trust
Business continuity is non-negotiable. Organizations cannot afford downtime, whether planned or unplanned. The network path is central to achieving this level of resilience.
- Redundancy: From
HA PairEdge RouterstoECMP balanceacross theSpine-Leaffabric, every layer of the network path is designed to eliminatesingle points of failure.Failovermechanisms are not an afterthought; they are engineered into the very fabric of the networkto ensure service continuity even in the face of fiber cuts or network failures. - Deterministic Performance: Modern applications require predictable behavior. A network that delivers fluctuating performance—sometimes fast, sometimes slow—is as detrimental as one that is consistently slow.
Deterministic performancemeans that traffic flows reliably and predictably, enabling applications to meet their service level objectives (SLOs) without unexpectedpacket lossorqueueing and drops. This predictability is a hallmark of well-designedClosorfabric-basednetworks.
Scalability and Elasticity: Built for Tomorrow’s Demands
The digital landscape is in a constant state of flux. Data volumes double, user bases expand, and new technologies emerge at an unprecedented pace. The network path must not only cope with today’s demands but be built for growth, not just today.
- Elastic Scaling: Architectures like
Spine-LeafenableStrong (add spines/leaves)scaling. Thisincremental capacity deliveryallows data centers to expand gracefully and efficiently, rather than requiring disruptive and costly overhauls.A data center network architecture *is* the blueprint for how traffic moves through your data center—physically (devices and cabling) and logically (routing, segmentation, and policy). It determines path length, congestion behavior, failure domains, and how easily you can scale without redesign. - Resource Allocation:
SDNandNetwork Automationprovide the agility to dynamically allocate network resources, ensuring that bandwidth and connectivity can be provisioned in real-time to meet the fluctuating demands of virtualized and containerized workloads.
Operational Visibility: Knowledge is Power
You can’t manage what you can’t see. Operational visibility into the network path is paramount for troubleshooting, performance optimization, and proactive maintenance.
- Monitoring tools (
SIEM,IDS/IPS,Monitoringsystems) provide real-time insights intotraffic engineering,queueing and drops,oversubscription ratios, andupstream path diversity. - This visibility allows administrators to
know exactly what’s happening, in real time, enabling them to identify and resolve potentialbottlenecksbefore they impactend usersorapplications.
From Infrastructure to Competitive Advantage
The implications of a robust, intelligently designed network path extend far beyond the IT department.
- Business Continuity: Ensures that critical operations remain functional, protecting revenue and reputation.
- Competitive Agility: Enables rapid deployment of new services and features, allowing businesses to respond quickly to market demands.
- Innovation Enabler: Provides the foundation for adopting cutting-edge technologies like
AI/ML,IoT, and advanced analytics, which are entirely dependent on high-performance networking. - Cost Efficiency: While initial investment may be significant, optimized traffic flow, reduced
operational overhead, and efficient resource utilization lead to long-term cost savings.
The network path is no longer just “pipes and wires.” It is strategic infrastructure that directly impacts an organization’s ability to innovate, compete, and thrive in the digital age. It enables the Hypervisors, Containers, Databases, and AI/ML engines to perform at their peak, ultimately delivering a superior experience for Users and Applications. A data center without an optimized network path is like a powerful engine shackled by a clogged fuel line—the potential is there, but performance is profoundly constrained.
Unlocking Your Optimal Data Center Network Path with IoT Worlds
Navigating the intricate landscape of data center network architecture, from selecting the right spine-leaf topology to implementing advanced SDN controls and ensuring AI/ML readiness, is a complex endeavor. The decisions you make about your network path have profound implications for your business continuity, operational efficiency, and competitive edge. Without expert guidance, organizations risk building infrastructure that can become a bottleneck rather than an enabler.
At IoT Worlds, we specialize in demystifying this complexity. Our expert consultants possess in-depth knowledge across all layers of the Data Center Network Path, honed by understanding industry best practices and emerging technologies. We don’t just see switches and routers; we see the arteries of your digital business, and we are dedicated to optimizing their flow.
We can help your organization:
- Assess and Optimize Existing Infrastructures: We’ll
validate throughput end-to-end, analyze your current network path, identifybottlenecks,oversubscription ratios, and areas for performance enhancement, ensuring your network is operating at its peak. - Design Future-Proof Architectures: Craft bespoke network designs—whether it’s a
Spine-Leaf,Clos, or a hybrid approach—that perfectly align with yourperformance requirements,scalability needs, andbusiness objectives. We ensure your network isbuilt for growth, not just today. - Enhance Security and Resilience: Implement robust
Firewall Clusters,IDS/IPS, andDDoS Protectionstrategies, alongside high-availability designs likeHA PairsforEdge RoutersandECMP balance, to safeguard your data and ensure uninterrupted operations. - Integrate Advanced Technologies: Guide you through the complexities of
SDNforNetwork Automationandtraffic engineering, and help you make informed decisions aboutEthernet RoCE vs InfiniBandfor yourAI/MLworkloads. - Improve Operational Visibility: Deploy comprehensive
monitoringandSIEMsolutions to ensure you havereal-timeinsights intoqueueing and dropsand overall network health, allowing for proactive management.
Don’t let an unoptimized network path hinder your digital aspirations. Your infrastructure isn’t just IT; it’s a non-negotiable component of business success. Partner with IoT Worlds to ensure your data center network path is a true accelerator of your organizational goals, delivering the low latency, redundancy, scalability, deterministic performance, and operational visibility that modern enterprises demand.
To unlock the full potential of your data center network and transform it into a competitive advantage, send an email to info@iotworlds.com today. Let us empower your organization to make informed, strategic decisions that drive efficiency, resilience, and unparalleled performance in the digital world.