The Industrial Cybersecurity Imperative: Beyond Flat Networks
In today’s rapidly evolving industrial landscape, Operational Technology (OT) cybersecurity has moved from a niche concern to a top-tier organizational imperative. The interconnectedness driven by Industry 4.0, Industrial Internet of Things (IIoT), and digital transformation initiatives has blurred the lines between traditionally air-gapped systems and the wider enterprise network. This convergence, while offering unprecedented efficiencies and innovations, also introduces a complex web of cyber risks.
Many organizations acknowledge the critical need for robust OT cybersecurity. They understand the potential for disastrous consequences – from production downtime and financial losses to environmental damage and threats to human safety – if their industrial control systems (ICS) are compromised. However, a significant gap often exists between recognizing the problem and properly implementing effective security architectures. One of the most fundamental yet often overlooked aspects of this implementation is the strategic adoption of IEC 62443 Zones and Conduits.
Historically, many OT networks were designed for reliability and uptime, often at the expense of robust security measures. This led to “flat network architectures” where devices across different functionalities and criticality levels resided on the same network segment. While this approach might have sufficed in a less connected era, it presents an unacceptable level of risk in the face of modern, sophisticated cyber threats. A single point of entry or a compromised device in a flat network can allow an attacker to propagate across the entire system, leading to widespread disruption. The consequences of such an attack, whether from ransomware, a targeted nation-state attack, or even an insider threat, can be catastrophic.
The challenge, then, lies in transitioning from these legacy, vulnerable architectures to secure, resilient industrial systems. This is where IEC 62443, the international standard for securing industrial automation and control systems (IACS), provides a crucial framework. At its core, IEC 62443 advocates for a risk-based approach to security, with the Zones and Conduits model serving as its foundational principle for network segmentation and trust boundary enforcement. This model moves away from the inherent weaknesses of flat networks by establishing clearly defined security boundaries and controlling all communication pathways between them.
The transition to a Zones and Conduits architecture is not merely a theoretical exercise; it is a practical, actionable strategy for mitigating risk, limiting the blast radius of potential incidents, and ensuring the continued safe and reliable operation of critical industrial processes. By systematically segmenting the network and meticulously managing communication, industrial organizations can build a resilient defense-in-depth strategy that can withstand even advanced cyber threats.
The Evolution of OT Cybersecurity Architectures
For decades, the Purdue Enterprise Reference Architecture, commonly known as the Purdue Model, served as the de facto standard for segmenting industrial control systems. It effectively separated business systems from control systems, aiming to reduce the impact of IT-side issues on OT operations and simplify architecture communication across diverse teams. This model, with its hierarchical layers from enterprise to process control, provided a useful conceptual framework.
However, the world of OT has evolved dramatically since the Purdue Model’s inception. Modern industrial environments are characterized by complex multi-site architectures, reliance on advanced connectivity like SD-WAN and 5G, the adoption of virtualization and container platforms, and the increasing necessity of remote access for vendors and support. Furthermore, the proliferation of Industrial IoT (IIoT) devices, edge computing, and cloud analytics has introduced new data flows and integration requirements that the traditional Purdue Model, on its own, struggles to address comprehensively.
This is not to say the Purdue Model is obsolete. Rather, it needs to be “revisited” and integrated with contemporary frameworks. The question is no longer whether Purdue is relevant, but how to leverage its strengths in conjunction with modern security standards like IEC 62443. The IEC 62443 Zones and Conduits model provides the necessary sophistication and flexibility to address the security challenges of today’s interconnected OT environments, effectively complementing and enhancing the conceptual segmentation laid out by the Purdue Model. It offers a more granular, risk-based approach to security that aligns with the dynamic nature of modern industrial operations.
Understanding the IEC 62443 Framework
The IEC 62443 standard is not a single document but a comprehensive family of standards designed to address cybersecurity for Industrial Automation and Control Systems (IACS). It provides a holistic approach covering policies, system design, component capabilities, and operational procedures throughout the entire lifecycle of industrial systems. Importantly, it offers a common language for all stakeholders involved in industrial cybersecurity, from architects and engineers to security teams and vendors, fostering a unified understanding of security requirements and best practices.
At its core, IEC 62443 emphasizes a risk-based approach to industrial cybersecurity. This means that security measures are not applied uniformly but are tailored to the specific risks, criticality, and sensitivity of different parts of the industrial system. This pragmatic approach ensures that resources are allocated effectively, focusing on the areas that pose the greatest potential for harm.
One of the most significant contributions of IEC 62443 is its Zones and Conduits model. This model offers a practical and structured way to implement OT network segmentation and establish trust boundaries, forming the backbone of a robust defense-in-depth strategy. Unlike a simple checklist, IEC 62443 is a framework that guides organizations toward repeatable and defensible security engineering practices for their industrial systems. It moves organizations beyond ad-hoc or “best-effort security” to a systematic and engineered approach to protecting their critical assets.
The Foundational Concepts: Zones and Conduits
Before diving into a practical example, it’s crucial to firmly grasp the definitions of Zones and Conduits as articulated by IEC 62443. These two concepts are the cornerstones of effective industrial network segmentation and play a pivotal role in limiting the impact of cyber incidents.
What is a Zone?
A Zone, in the context of IEC 62443, is a logical or physical grouping of assets (devices, applications, people, or networks) that share similar security characteristics and requirements. This includes factors such as:
- Security Requirements: The specific cybersecurity controls needed to protect the assets within the zone.
- Risk Level: The potential for adverse impacts if the assets within the zone are compromised.
- Criticality: The importance of the assets to the overall operational process, safety, and business continuity.
- Function: Assets that perform similar operational roles or contribute to a common function within the industrial process.
Essentially, a Zone establishes a perimeter where a consistent level of trust and security applies. All assets within a Zone are considered to have a similar security posture and are protected by a common set of security policies. The idea is that if an attacker manages to breach one asset within a Zone, the damage is contained within that specific Zone, rather than allowing lateral movement across the entire network.
It’s important to note that Zones are not necessarily defined by physical location. They can be logical groupings that span across different physical locations, as long as the assets within them share the same security posture. Furthermore, Zones can be further divided into sub-zones to achieve more granular segmentation and refined security control, allowing for a hierarchical approach to security within larger, more complex industrial environments.
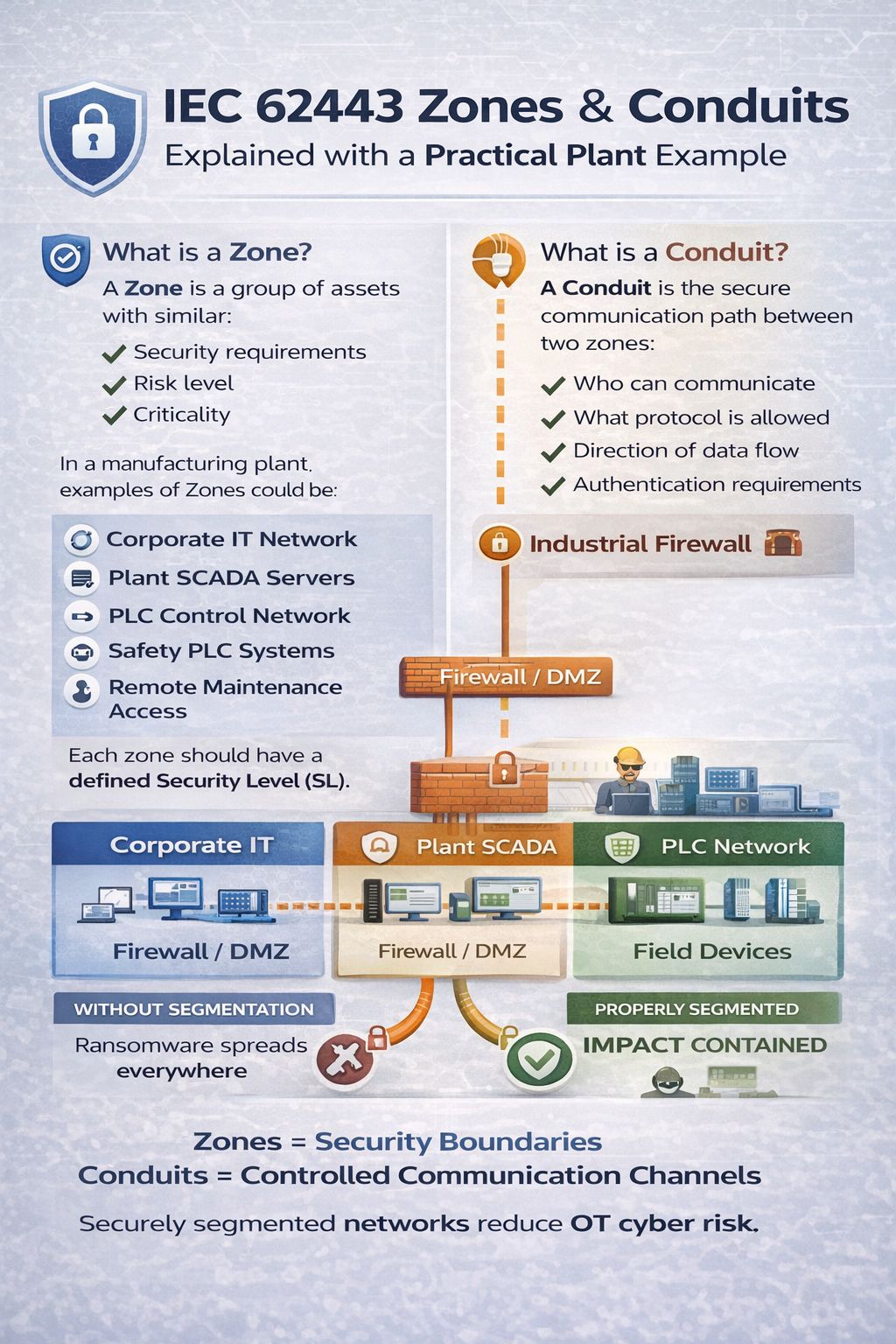
Examples of Zones in a manufacturing plant, as highlighted in the provided image, include:
- Corporate IT Network Zone: This zone houses typical enterprise IT assets such as ERP systems, email servers, business applications, and user workstations. It has different security requirements and risk profiles compared to OT systems, primarily focusing on data confidentiality and integrity.
- Plant SCADA Servers Zone: This zone encompasses the supervisory control and data acquisition (SCADA) servers, human-machine interfaces (HMIs), historians, and other critical applications that monitor and control the industrial process at a higher level. Its security requirements prioritize availability and integrity of control data.
- PLC Control Network Zone: This zone contains Programmable Logic Controllers (PLCs), Distributed Control Systems (DCS), and other controllers directly responsible for executing control logic and interfacing with field devices. The paramount security requirement here is the integrity and availability of control functions to ensure safe and continuous operations.
- Safety PLC Systems Zone: This is a highly critical zone dedicated to Safety Instrumented Systems (SIS) and Safety PLCs. Given their direct role in preventing hazardous situations and ensuring personnel safety, this zone demands the highest level of security integrity and availability, often with independent and redundant controls.
- Remote Maintenance Access Zone: This zone is specifically designed to accommodate secure remote access for vendors, integrators, or internal support teams. Due to the inherent risks associated with remote connections, this zone requires stringent authentication, authorization, and monitoring controls, often involving jump hosts and multi-factor authentication.
- IIoT / Gateway Network Zone: As IIoT adoption grows, a dedicated zone for IIoT gateways, sensors, and data aggregation platforms becomes essential. This zone manages the secure ingestion and transfer of data from operational devices to higher-level analytics or cloud platforms, balancing connectivity with security.
Each Zone should have a defined Security Level (SL). This Security Level specifies the required protection against different types of cyber threats and is determined through a thorough risk assessment. The IEC 62443 standard defines several Security Levels, allowing organizations to tailor their security investments based on the criticality of the assets within each Zone.
What is a Conduit?
A Conduit is the secure and controlled communication path between two or more Zones. It is not just a cable or a network segment; rather, it represents the entire set of technical and procedural controls that govern the communication flow between these segmented areas. Conduits are crucial because they enforce the security policies established for the communicating Zones, preventing unauthorized access or uncontrolled data exchange.
Key attributes controlled by a Conduit include:
- Who can communicate: Which specific systems or users are authorized to initiate or receive communication across the conduit. This involves access control lists (ACLs) and user authentication.
- What protocol is allowed: Specifying which communication protocols (e.g., Modbus TCP, OPC UA, HTTP, specific industrial protocols) are permitted to traverse the conduit. All other protocols are explicitly denied.
- Direction of data flow: Defining whether communication is unidirectional (e.g., data flowing only from OT to IT) or bidirectional, and precisely which data can flow in each direction. This is often achieved through technologies like data diodes or highly granular firewall rules.
- Authentication requirements: Ensuring that only authenticated devices, applications, or users can establish communication across the conduit. This includes mechanisms like strong passwords, certificates, or multi-factor authentication.
In essence, if a Zone is a “Security Boundary,” then a Conduit is a “Controlled Communication Channel.” It embodies the principle of “least-privilege networking,” meaning only the genuinely required connections exist, and everything else is blocked by default. This “deny by default” policy is a fundamental tenet of robust industrial cybersecurity.
Conduits typically implement a suite of security technologies to enforce these controls, including:
- Firewalls (Industrial Firewalls): These are the primary enforcers of conduit policies, filtering traffic based on source, destination, port, and protocol. Industrial firewalls are specifically designed to handle OT protocols and environments.
- Demilitarized Zones (DMZs): Often used in conduits between IT and OT, a DMZ acts as a neutral network segment that provides an additional layer of security. Systems in a DMZ are exposed to both sides but are isolated from both the core IT and core OT networks, allowing for controlled data exchange without granting direct access.
- Proxies and Protocol Brokers: These devices can terminate and re-initiate communication sessions, inspect protocol payloads, and translate between different protocols, adding an additional layer of security and control.
- VPN Connections: Essential for secure remote access, VPNs encrypt and tunnel communication through untrusted networks, ensuring confidentiality and integrity.
- Intrusion Detection/Prevention Systems (IDS/IPS): These systems monitor conduit traffic for suspicious activities or known attack signatures, providing real-time threat detection and, in some cases, automated prevention.
It’s crucial to understand that while Zones can contain sub-zones for hierarchical segmentation, Conduits cannot have “sub-conduits”. A Conduit is the complete set of controls governing the link between two Zones.
The Practical Application: A Manufacturing Plant Example
To truly understand the power of Zones and Conduits, let’s walk through a practical example in a manufacturing plant, expanding on the scenario presented in the image. This example will highlight how a properly segmented architecture dramatically reduces cyber risk compared to a flat network.
Imagine a typical manufacturing facility operating without proper network segmentation – a common scenario for many legacy plants. In this “flat network” environment, the Corporate IT network, Plant SCADA servers, PLC control network, and field devices are all interconnected with minimal or no effective security boundaries in between.
The “Flat Network” Scenario: A Recipe for Disaster
In a flat network:
- Direct IT-to-PLC Communication: It’s not uncommon to find situations where IT workstations or even unmanaged devices on the corporate network can directly communicate with PLCs on the plant floor.
- No DMZ: The critical point of interface between the business network and the operational network (often a firewall) might be configured with overly permissive rules, or simply not exist as an effective buffer.
- Shared Credentials: The same user accounts or highly privileged credentials might be used across both IT and OT systems, creating a single point of failure.
- Open Protocols: A wide range of protocols, many of which are insecure, might be allowed to traverse freely across the network.
The Consequence: If a ransomware attack, for instance, originates in the Corporate IT network (e.g., via a phishing email on a user’s workstation), it can easily spread laterally across the entire organization. Without segmentation, this malware can quickly reach the Plant SCADA servers, then propagate to the PLC Control Network, and finally impact the Field Devices.
- Corporate IT: User workstations, file servers, and business applications are encrypted.
- Plant SCADA: HMIs become inoperable, historians are corrupted, and operators lose visibility into the process.
- PLC Network: PLCs might be commanded to shut down, alter processes, or even be bricked, leading to immediate production stoppage.
- Field Devices: Actuators and sensors cease functioning correctly, potentially causing safety incidents or physical damage to equipment.
The result is a widespread operational shutdown, significant financial losses, damage to reputation, and potentially severe safety or environmental impacts. The “blast radius” of the incident is the entire plant, as illustrated by the “Ransomware spreads everywhere” diagram in the image.
The “Properly Segmented” Scenario: Containing the Impact
Now, let’s apply the IEC 62443 Zones and Conduits model to the same manufacturing plant. We will define distinct Zones based on shared security requirements, risk levels, and criticality, and then establish secure Conduits between them.
1. Define the Zones:
- Corporate IT Network Zone: This zone includes all typical enterprise IT assets. Its primary security focus is on data confidentiality and integrity, with typical office application and internet access requirements.
- Plant SCADA Servers Zone: Dedicated to SCADA servers, historians, engineering workstations, and critical OT support applications. This zone requires high availability and integrity for control data, with restricted internet access.
- PLC Control Network Zone: Encompasses PLCs, DCS controllers, and specialized industrial protocols. The highest priority here is the integrity and availability of control commands and process input/output.
- Field Devices Zone: This zone includes the sensors, actuators, motors, drives, and other endpoint devices directly interacting with the physical process. Security focuses on preventing unauthorized manipulation and maintaining device integrity.
- Remote Maintenance Access Zone: A dedicated, isolated zone for secure third-party and internal remote connectivity, characterized by strict access controls and monitoring.
- Safety PLC Systems Zone: A highly isolated zone for safety controllers and related systems, often with physical separation and unique control measures.
2. Establish Conduits with Enforcement Points:
Now, let’s define the secure communication paths (Conduits) between these Zones, using various technical controls as enforcement points.
- Conduit 1: Corporate IT Network Zone ↔ Plant SCADA Servers Zone (via Firewall / DMZ)
- Enforcement Point: A robust enterprise-grade firewall and an industrial DMZ.
- Control: This conduit allows highly restricted data flows. For example, historical data from the SCADA historian might be securely transferred to a corporate analytics platform, or system patches might be pushed from IT to SCADA servers (but only after rigorous scanning and approval). Direct arbitrary access from IT to SCADA is blocked. The DMZ hosts systems that facilitate this controlled exchange without granting direct access to either core network.
- Policies:
- Who: Only specific, authorized IT security tools or designated corporate applications.
- Protocol: Limited to secure protocols like SFTP, HTTPS (for specific web applications), and potentially authenticated database connections.
- Direction: Predominantly unidirectional for data flowing from OT to IT (e.g., historical data), with controlled bidirectional paths for approved management traffic.
- Authentication: Strong authentication (e.g., certificates, multi-factor) required for any management access.
- Conduit 2: Plant SCADA Servers Zone ↔ PLC Control Network Zone (via Industrial Firewall)
- Enforcement Point: A specialized industrial firewall.
- Control: This conduit is critical for the actual operation of the plant. It allows SCADA systems to send commands to PLCs and receive process data.
- Policies:
- Who: Only authorized SCADA servers, HMIs, and engineering workstations.
- Protocol: Strictly limited to industrial control protocols (e.g., Modbus TCP, EtherNet/IP, OPC UA) and possibly remote desktop (RDP) for specific, authorized engineering access to configured jump hosts within the SCADA zone.
- Direction: Bi-directional, but with precise rules on which PLCs can be accessed by which SCADA components, and which specific data points can be exchanged.
- Authentication: Ideally, device authentication for PLCs and strong user authentication for engineering access.
- Conduit 3: PLC Control Network Zone ↔ Field Devices Zone (often intrinsic to the design)
- Enforcement Point: While less a distinct “firewall” in many cases, this conduit is enforced by the physical layer, specialized industrial switches/routers, and often the inherent security features (or lack thereof) of the field devices themselves.
- Control: This allows PLCs to read sensor data and send commands to actuators.
- Policies:
- Who: Only connected PLCs.
- Protocol: Device-specific or tightly controlled industrial protocols.
- Direction: Typically bi-directional for control loops.
- Authentication: Often limited by device capabilities, but secure configuration and physical tampering protection are paramount.
- Conduit 4 (Lateral): Remote Maintenance Access Zone ↔ Relevant OT Zones
- Enforcement Point: Dedicated firewalls, jump servers (bastion hosts), multi-factor authentication systems, VPN concentrators.
- Control: This conduit is established on-demand and is highly secured. It only allows authorized remote users (e.g., OEM technicians) to access specific systems within, for example, the Plant SCADA Servers Zone or PLC Control Network Zone, and only for authorized durations.
- Policies:
- Who: Pre-authorized, authenticated remote users with specific roles.
- Protocol: Limited to RDP, SSH, or specific vendor-required secure protocols, always tunneled through a VPN.
- Direction: Controlled access to specific endpoints.
- Authentication: Mandatory multi-factor authentication, session recording, and strict logging.
The Outcome: When a similar ransomware attack occurs in this properly segmented network:
- Corporate IT: The attack might still impact the Corporate IT Network Zone, encrypting business systems.
- Conduit 1 (Firewall / DMZ): However, the rigid controls of the Conduit between Corporate IT and Plant SCADA will prevent the ransomware from propagating directly into the OT environment. The firewall and DMZ act as effective barriers, denying the unauthorized traffic.
- Plant SCADA: The Plant SCADA Servers Zone remains operational, maintaining visibility and control over the process.
- PLC Network & Field Devices: These zones are completely unaffected due to the segmentation.
The result is that the “Impact is contained.” Production continues, safety systems remain functional, and critical operations are preserved. The cybersecurity team can then focus on remediating the Corporate IT breach without the added pressure of a plant-wide operational outage. This drastically reduces downtime, financial impact, and potential safety risks.
This practical example vividly demonstrates why Zones and Conduits are not just theoretical constructs but are instruments of practical risk reduction. They provide a structural resilience that is simply unattainable in a flat network.
Why Zones and Conduits Matter Beyond Basic Segmentation
The strategic implementation of Zones and Conduits extends far beyond simply drawing lines on a network diagram. It underpins a comprehensive cybersecurity posture for OT environments, delivering tangible benefits and addressing several critical vulnerabilities often found in industrial settings.
1. Limiting the Attack Surface and Blast Radius
Perhaps the most immediate and profound impact of adopting Zones and Conduits is the significant reduction in both the attack surface and the potential “blast radius” of a cyber incident.
- Reduced Attack Surface: By eliminating direct communication paths and allowing only operationally necessary traffic, the number of potential entry points for an attacker is drastically curtailed. Each conduit acts as a choke point where traffic is inspected and filtered, making it harder for malicious payloads to reach critical assets. Attackers can’t simply scan a flat network and find open vulnerabilities everywhere; they face segmented barriers at every turn.
- Limited Blast Radius: As demonstrated in the manufacturing plant example, if an attack successfully breaches one zone, the clear boundaries and strict controls of the conduits largely prevent it from spiraling out of control and affecting the entire infrastructure. This localized containment means that critical operations can often continue, even while an incident is being managed in another part of the network. This directly translates to reduced downtime, lower financial losses, and minimized safety risks. This concept is fundamental to the defense-in-depth strategy, where no single point of failure can compromise the entire system.
2. Enforcing Least-Privilege Networking
The principle of least privilege, a cornerstone of cybersecurity, dictates that systems and users should only have the minimum access rights necessary to perform their legitimate functions. Zones and Conduits are instrumental in enforcing this principle at the network level.
- Deny by Default: Conduits operate on a “deny by default” policy. This means all communication between zones is blocked unless explicitly permitted. This is a far more secure approach than an “allow all” policy with exceptions, as it inherently stops unforeseen or unauthorized traffic.
- Granular Control: Within each conduit, administrators have granular control over exactly who can communicate, using what protocol, and in which direction. This prevents, for example, a general IT workstation from directly accessing a PLC, even if that workstation is on the corporate network and an approved user is logged in. Access is strictly tied to the operational necessity and security profile of the communicating zones.
3. Enhancing Visibility and Monitoring
Proper segmentation naturally enhances an organization’s ability to monitor its network for suspicious activities.
- Choke Points for Inspection: Each conduit acts as a network “choke point” where all inter-zone traffic must pass. This makes it an ideal location to deploy monitoring tools such as Intrusion Detection Systems (IDS), logging mechanisms, and protocol analyzers. By focusing monitoring efforts at these critical junctions, security teams can gain deep insights into allowed and denied traffic flows, quickly identifying anomalies or attempted breaches.
- Reduced Noise: In a flat network, the sheer volume of unfiltered traffic can make it incredibly difficult to spot malicious activity. With segmentation, the expected traffic patterns within each conduit are well-defined, making deviations much easier to detect.
- Auditable Integrations: The explicit definition of zones and conduits means that all communication pathways are documented and auditable. It becomes clear “who can talk to whom, and why,” which is invaluable for compliance, incident response, and continuous improvement.
4. Facilitating Compliance and Risk Management
IEC 62443 itself is a recognized international standard for OT cybersecurity, and implementing Zones and Conduits is a direct path to achieving compliance and demonstrating a mature security posture.
- Structured Risk Assessment: The zone-based approach naturally aligns with risk management frameworks. Organizations can conduct detailed risk assessments for each zone, identifying specific threats and vulnerabilities pertinent to the assets within that boundary. This allows for targeted security controls and resource allocation.
- Security Levels (SL): As mentioned, each zone can be assigned a Target Security Level (SL-T) based on its risk profile. The Zones and Conduits model provides the architectural framework to achieve and maintain that SL-T, and to assess the Achieved Security Level (SL-A) after implementation.
- Regulatory Alignment: Many industry-specific regulations and governmental guidelines increasingly reference or align with IEC 62443. Adopting Zones and Conduits positions organizations favorably for audits, certifications, and compliance with evolving global cybersecurity and regulatory expectations, particularly in critical infrastructure sectors.
5. Supporting Modern OT Architectures
The inherent flexibility and scalability of the Zones and Conduits model make it well-suited to support the complexities of modern OT environments, which often go beyond traditional hierarchical structures.
- Hybrid Cloud and IIoT Integration: When integrating IIoT devices, edge computing, or cloud analytics, Zones and Conduits provide a structured way to manage these new, often external, data flows securely. A dedicated IIoT/Gateway Zone and secure conduits to cloud environments (perhaps through an industrial DMZ) can ensure sensitive OT data is shared safely without exposing the core control network.
- Remote Access: The concept of a dedicated Remote Maintenance Access Zone with highly controlled conduits is a direct answer to the business requirement for secure remote access for vendors and support teams. This isolation is crucial for mitigating one of the most common vectors for OT attacks.
- Virtualization and Containerization: As virtualization platforms move into OT, robust segmentation via Zones and Conduits ensures that these new compute environments are securely integrated and managed, preventing their compromise from impacting critical control systems.
In essence, while the motivations for applying Zones and Conduits might arise from a need to address direct threats like ransomware, their benefits extend to creating a more robust, auditable, and resilient industrial infrastructure – an absolute necessity in the era of Industry 4.0.
Designing and Implementing Zones and Conduits: A Methodical Approach
Implementing Zones and Conduits is not a one-time project but an ongoing process that requires careful planning, systematic execution, and continuous monitoring. It typically involves a phased approach, starting with assessment and moving through design, implementation, and ongoing management.
1. Initial Assessment and Risk Analysis
Before any network changes are made, a thorough understanding of the current state of the industrial environment is paramount.
- Asset Inventory: Create a comprehensive inventory of all OT assets, including PLCs, HMIs, SCADA servers, engineering workstations, network devices, and field devices. Document their function, location, criticality, and the data they process or generate.
- Network Mapping: Develop an accurate network topology map that shows all connections, communication paths, and existing security devices. This can reveal hidden connections or “shadow IT” that could undermine segmentation efforts.
- Data Flow Analysis: Document critical data flows. Understand what data is exchanged between which systems, for what purpose, and how frequently. This helps in defining the operational necessity for communication pathways.
- Risk Assessment and Cyber-PHA: Conduct a detailed risk assessment for the entire OT environment. This should go beyond IT-centric risk assessments to specifically evaluate operational risks, safety implications, and the impact of cyber incidents on physical processes. A Cyber-Process Hazard Analysis (Cyber-PHA) is highly recommended before segmentation to proactively identify and mitigate cyber-related process risks. Identify critical functions, potential attack vectors, and desired Security Levels (SL-T) for different parts of the system. This step is crucial for defining the boundaries and security requirements of future zones.
2. Zone Definition
Based on the assessment, begin defining your Zones. This is an iterative process driven by the principles of shared security requirements, risk, criticality, and function.
- Group Assets: Cluster assets with similar characteristics into potential zones. For instance, all PLCs controlling a specific production line might form one zone. SCADA servers for the entire plant might form another.
- Consider Consequence: A key factor in grouping assets is the consequence of their compromise. Assets whose compromise would lead to similar levels of downtime, financial loss, or safety risk should ideally be in the same zone or highly protected within a sub-zone.
- Functional Boundaries: Align zones with operational functions. For example, a “Batch Process Control Zone,” a “Utilities Zone,” or a “Packaging Line Zone” could be practical functional groupings.
- Assign Security Levels (SL-T): For each proposed zone, assign a Target Security Level (SL-T) based on the risk assessment. Higher criticality zones will naturally require higher SL-Ts.
3. Conduit Design
With zones defined, the next step is to design the Conduits that will allow necessary communication while maintaining security.
- Document Required Data Flows: Review the documented data flows and identify which communications are absolutely essential between the newly defined zones. Any communication not explicitly required must be denied.
- Determine Control Points: Identify the appropriate technical controls for each conduit. This will typically involve industrial firewalls, DMZs, intrusion detection systems (IDS), and potentially protocol gateways or data diodes.
- Specify Rules: For each conduit, meticulously define:
- Source and Destination IP addresses/subnets: What systems are allowed to initiate/receive connections.
- Allowed Protocols and Ports: Only the precise protocols and ports necessary for the required data flow.
- Directionality: Is communication unidirectional or bidirectional? If bidirectional, specify exact sub-paths.
- Authentication and Authorization: Requirements for users or devices attempting to traverse the conduit.
- Logging and Monitoring: How traffic through the conduit will be logged and monitored for anomalies.
- Deny by Default: Design all conduits with a “deny by default” policy. This means only explicitly permitted traffic is allowed; everything else is blocked.
4. Implementation and Testing
Once the design is complete, proceed with careful, phased implementation.
- Phased Rollout: Implement segmentation incrementally, zone by zone, or conduit by conduit, to minimize disruption to operations.
- Configuration of Security Devices: Configure firewalls, IDS/IPS, and other security devices according to the detailed conduit designs. This requires deep technical expertise in both networking and OT protocols.
- Network Address Translation (NAT): Often employed in industrial networks to obfuscate internal IP addresses from external networks, NAT can be a component of conduit configuration.
- Validation Testing: Thoroughly test each newly established conduit to ensure that:
- Only authorized traffic is allowed to pass.
- Unauthorized traffic is indeed blocked.
- Operational processes continue unimpeded.
- All necessary applications and services function correctly.
- Compensating Countermeasures: Where native security measures are insufficient to meet the desired SL-T for a zone or conduit, implement compensating countermeasures. These can be additional technical controls, procedural safeguards, or personnel training.
5. Operational Management and Continuous Improvement
Implementing Zones and Conduits is an ongoing commitment, not a one-time fix.
- Continuous Monitoring: Actively monitor all conduits for suspicious activity, policy violations, and anomalous traffic patterns. Implement Security Information and Event Management (SIEM) systems to aggregate and analyze logs from firewalls and IDS.
- Regular Audits: Periodically audit firewall rules and conduit configurations to ensure they remain correct, optimized, and aligned with evolving operational needs and threat landscapes.
- Policy Updates: Regularly review and update security policies and conduit configurations to account for changes in the industrial environment, new threats, or updated compliance requirements. This includes managing changes to data flows, new asset deployments, or software updates.
- Incident Response Planning: Ensure that incident response plans are updated to reflect the segmented architecture. Knowing how to respond to an incident within a specific zone and how to maintain operations in other zones is critical.
- Staff Training: Train OT and IT personnel on the Zones and Conduits architecture, their roles in maintaining security, and how to identify and report potential security incidents.
- Lifecycle Management: Consider how security requirements change over the lifecycle of assets and systems within zones. Decommissioning, upgrades, and new deployments must all adhere to the established security framework.
Aligning with the Purdue Model: While IEC 62443 provides the granular architectural and control details, it can coexist effectively with the Purdue Model’s conceptual hierarchy. The Purdue Model’s levels (e.g., Level 3 Manufacturing Operations, Level 2 Control Systems) can serve as high-level zones, with IEC 62443 then used to define sub-zones and the precise conduits between them, adding the necessary security rigor and detail. This hybrid approach helps bridge the gap between abstract architectural concepts and concrete security implementation. For example:
- Purdue’s Level 3: Could align with the “Plant SCADA Servers Zone” and “Remote Access Zone.”
- Purdue’s Level 2: Would logically encompass the “PLC Control Network Zone” and “Safety PLC Systems Zone.”
- Purdue’s Level 1 & 0: Would fall under the “Field Devices Zone.”
By following this methodical approach, organizations can systematically build a robust, resilient cybersecurity architecture that protects their critical industrial operations effectively against an ever-evolving threat landscape.
Common Pitfalls to Avoid in Zones and Conduits Implementation
While the benefits of IEC 62443 Zones and Conduits are clear, successful implementation requires careful attention to detail and awareness of common challenges. Avoiding these pitfalls is crucial for realizing the full security potential of this architecture.
1. Inadequate Initial Assessment and Planning
- Skipping Asset Inventory and Data Flow Analysis: Without a comprehensive understanding of all assets and their communication patterns, zones and conduits will be based on assumptions rather than reality. This leads to misconfigurations, operational disruptions, or, worse, overlooked security gaps.
- Insufficient Risk Assessment: A superficial risk assessment may lead to assigning incorrect Security Levels (SL-T) to zones, resulting in either over-engineering (wasting resources) or under-engineering (leaving critical assets exposed).
- Lack of Stakeholder Involvement: Excluding OT engineers, operations personnel, and even vendors from the planning phase can lead to designs that are impractical, inhibit critical operations, or fail to account for unique process requirements.
2. Over-reliance on “A Firewall” as a Conduit
- Treating Firewalls as the Only Control: While firewalls are central to conduits, they are not the sole component. A conduit is the complete set of technical and procedural controls. Neglecting aspects like intrusion detection, strong authentication, protocol inspection, and robust logging means the conduit is incomplete and potentially vulnerable.
- Default “Allow All” Rules: Starting with overly permissive firewall rules and gradually tightening them is a risky approach. The best practice is “deny by default,” where only explicitly authorized traffic is permitted.
- Generic Firewall Rules: Failing to specify granular rules (source, destination, port, protocol, direction) can create overly broad allowances that undermine the purpose of the conduit. For example, allowing “any” traffic from the IT network to the OT network through a single port, even if that port is used by an OT protocol, creates a wide-open vulnerability.
3. Poorly Defined Zone Boundaries
- Zones Based on Convenience, Not Security: Grouping assets together simply because they are physically co-located, rather than based on shared security requirements, risk, and criticality, defeats the purpose of logical segmentation.
- Overlapping Zones or Ambiguous Boundaries: If it’s unclear which zone an asset belongs to, or if a single asset falls into multiple zones without clear rules, it creates confusion and security weaknesses.
- Too Many or Too Few Zones: An architecture with too few zones might be easy to manage but offers minimal containment. Too many zones, on the other hand, can create unnecessary complexity and management overhead. The right balance is key.
4. Neglecting Operational Realities
- Impact on Production: Implementing segmentation without rigorously testing the impact on operational processes can lead to unexpected shutdowns or performance degradation. Changes should be phased and thoroughly validated.
- Inadequate Bandwidth Planning: Introducing firewalls or other security devices can add latency or reduce throughput. Proper network engineering and capacity planning are essential to avoid performance bottlenecks.
- Ignoring Legacy Systems: Older OT systems often lack modern security features and may not support advanced authentication or secure protocols. Special considerations, such as dedicated segmentation and protocol conversion gateways, are necessary for these assets.
5. Lack of Ongoing Management
- “Set It and Forget It” Mentality: Cybersecurity is not a static state. Changes in the industrial environment (new equipment, software updates, process modifications), evolving threats, and personnel changes require continuous adjustment of zones and conduits. Stale firewall rules or unmonitored conduits are serious vulnerabilities.
- Inconsistent Security Policies: Failing to maintain uniform security policies within a zone can lead to internal vulnerabilities that negate the boundary protection.
- Ignoring Monitoring and Alerting: Without robust monitoring of conduit traffic and a mature alerting system, even the best segmentation won’t detect an active attack or policy deviation. An IDS that triggers alerts that no one responds to is as good as no IDS at all.
- Developer and Vendor Access: Remote access for third-party vendors and internal development teams is a common requirement but also a major attack vector. Failing to implement dedicated, tightly controlled “Remote Access Zones” and securing these conduits with strong multi-factor authentication, jump hosts, and session monitoring is a significant risk.
6. Disconnecting from the Incident Response Plan
- Segmentation without Response: A brilliantly segmented network is only half the battle. If the incident response team doesn’t understand the zone and conduit architecture, or if the plan doesn’t account for how to operate, isolate, and recover within this framework, the benefits of segmentation during a crisis will be diminished.
By proactively addressing these potential pitfalls, organizations can ensure that their investment in IEC 62443 Zones and Conduits translates into a truly resilient and defensible OT environment. It requires a holistic view that combines technical expertise with operational understanding and continuous vigilance.
The Future of OT Cybersecurity: Beyond the Perimeter
As industrial environments continue their relentless march towards digitalization and hyper-connectivity under the banner of Industry 4.0, the importance of robust cybersecurity architectures will only amplify. The IEC 62443 Zones and Conduits model is not merely a transient best practice but a foundational element that will continue to evolve and remain critical in this future landscape.
Several key trends underscore the enduring relevance and increasing sophistication required in implementing Zones and Conduits:
1. Zero Trust Principles in OT
The “Zero Trust” security model, which dictates “never trust, always verify,” is gaining traction in OT. Zones and Conduits inherently align with this principle by challenging the notion of inherent trust within a network segment. Every communication request across a conduit is authenticated and authorized, regardless of its origin. As OT environments mature, we can expect to see an even greater emphasis on micro-segmentation within zones and stronger identity and access management solutions integrated into conduit enforcement points.
2. Convergence of IT and OT Teams and Technologies
The operational efficiency promised by IT/OT convergence also brings with it shared security responsibilities. The language provided by IEC 62443, particularly the clear definitions of Zones and Conduits, helps bridge the communication gap between IT and OT professionals. Future implementations will increasingly require collaborative efforts, integrating IT’s networking and security expertise with OT’s deep process knowledge. This convergence will also see the adoption of more advanced IT security tooling, adapted for OT, within conduit monitoring and enforcement.
3. Increased IIoT and Cloud Integration Complexity
The proliferation of IIoT devices generating vast amounts of data for cloud analytics introduces new security challenges. Dedicated IIoT Zones, often with highly specialized conduits to cloud platforms via industrial DMZs, will become standard. These conduits will require advanced security measures such as secure gateways, mutual authentication, encryption in transit, and robust data integrity checks to ensure that data flows securely without compromising the integrity of the core control systems. The inherent complexity of managing numerous IIoT endpoints will also push for automated policy enforcement within conduits.
4. The Rise of Software-Defined Networking (SDN) and Network Virtualization
Traditional hardware-based segmentation can be rigid. With the emergence of SDN and network virtualization in OT, the ability to dynamically define and enforce zone and conduit policies through software will become more prevalent. This offers enhanced flexibility, scalability, and automated response capabilities. Virtual firewalls and security groups can be deployed and managed much faster, adapting to changing operational needs without extensive physical network reconfigurations.
5. Threat Intelligence and Adaptive Security
Future iterations of Zones and Conduits will be more responsive to dynamic threat landscapes. Integration with global threat intelligence feeds will allow for adaptive conduit policies, automatically blocking known malicious IPs or patterns. Behavioral analytics at conduit enforcement points will identify abnormal communication patterns that deviate from baselines, signaling potential intrusions or misconfigurations that require immediate attention.
6. Cybersecurity as a Priority in Design (Security by Design)
Instead of retrofitting security onto existing, sometimes vulnerable, architectures, the emphasis will shift further towards “security by design.” New industrial systems and digital transformation projects will incorporate IEC 62443 Zones and Conduits from the initial planning stages. This proactive approach ensures that security is an intrinsic part of the system’s foundation, rather than an afterthought, ultimately leading to more secure, reliable, and compliant operations.
The core principles of isolating assets based on risk, limiting communication to only what is necessary, and enforcing strong controls at all interfaces will remain paramount. The specifics of how these principles are applied will continue to evolve with technology, but the fundamental concepts of Zones and Conduits, as championed by IEC 62443, will remain indispensable for building the resilient industrial control systems of tomorrow. For any organization embarking on or continuing its digital transformation journey, mastering these concepts is not just a recommendation, but a strategic imperative.
Conclusion: Securing Your Industrial Future with IoT Worlds
The industrial landscape is undergoing a profound transformation, driven by unprecedented connectivity and the promise of Industry 4.0. While these advancements offer immense opportunities for efficiency and innovation, they simultaneously expose Operational Technology (OT) environments to a growing array of sophisticated cyber threats. The era of flat networks and perimeter-only defenses is unequivocally over. Surviving and thriving in this new reality demands a proactive, structured, and resilient approach to cybersecurity.
The IEC 62443 Zones and Conduits model provides precisely this framework. It is the gold standard for segmenting industrial networks, establishing clear security boundaries, and meticulously controlling communication pathways. As we’ve explored through a practical manufacturing plant example, adopting this architecture transforms a vulnerable, flat network—where a single breach can cause widespread devastation—into a properly segmented, resilient system where impacts are contained, and critical operations can continue even in the face of an attack.
At its heart, the Zones and Conduits model is about:
- Risk Reduction: By limiting lateral movement and reducing the attack surface.
- Operational Resilience: By ensuring that a compromise in one area doesn’t propagate throughout the entire plant.
- Compliance and Trust: By providing a structured, auditable approach to securing critical infrastructure.
- Enabling Innovation: By allowing secure integration of modern technologies like IIoT and cloud computing without compromising core operations.
Many organizations talk about OT cybersecurity, and they understand the gravity of the threats. However, far fewer have successfully implemented the robust Zones and Conduits architecture that truly delivers practical risk reduction and builds the backbone of OT resilience. This is where specialized expertise becomes invaluable.
Are you ready to move beyond theoretical discussions and implement a truly secure, resilient industrial cybersecurity architecture?
At IoT Worlds, we specialize in guiding organizations through the complexities of OT cybersecurity, from comprehensive risk assessments and meticulous zone/conduit design to expert implementation and ongoing managed security services. Our team understands the nuances of industrial control systems, the intricacies of IEC 62443, and the critical balance between security and operational continuity.
Don’t let your industrial future be jeopardized by inadequate cybersecurity. Take the decisive step towards a secure, resilient future.
Contact us today to discuss how we can help you design, implement, and optimize an IEC 62443 Zones and Conduits architecture tailored to your unique operational needs.
Email us at info@iotworlds.com to schedule a consultation and secure your industrial future.