In the dynamic landscape of modern business, cybersecurity is no longer a peripheral concern; it’s a foundational pillar of operational resilience and trust. Many organizations mistakenly believe that achieving cybersecurity maturity is simply a matter of acquiring the latest, most sophisticated security tools. While tools are undoubtedly important, they are merely instruments. The true strength of a security program lies in its underlying framework: the clear, practiced, and enforced documentation that guides its every action.
The most robust security environments aren’t built on technology alone. They are forged through a commitment to strategic planning, thorough preparation, and continuous refinement, all encapsulated within solid documentation. This documentation transforms theoretical security concepts into practical, actionable playbooks that empower an organization to defend itself effectively. It’s about moving security from a theoretical concept to actual, measurable execution, especially under pressure.
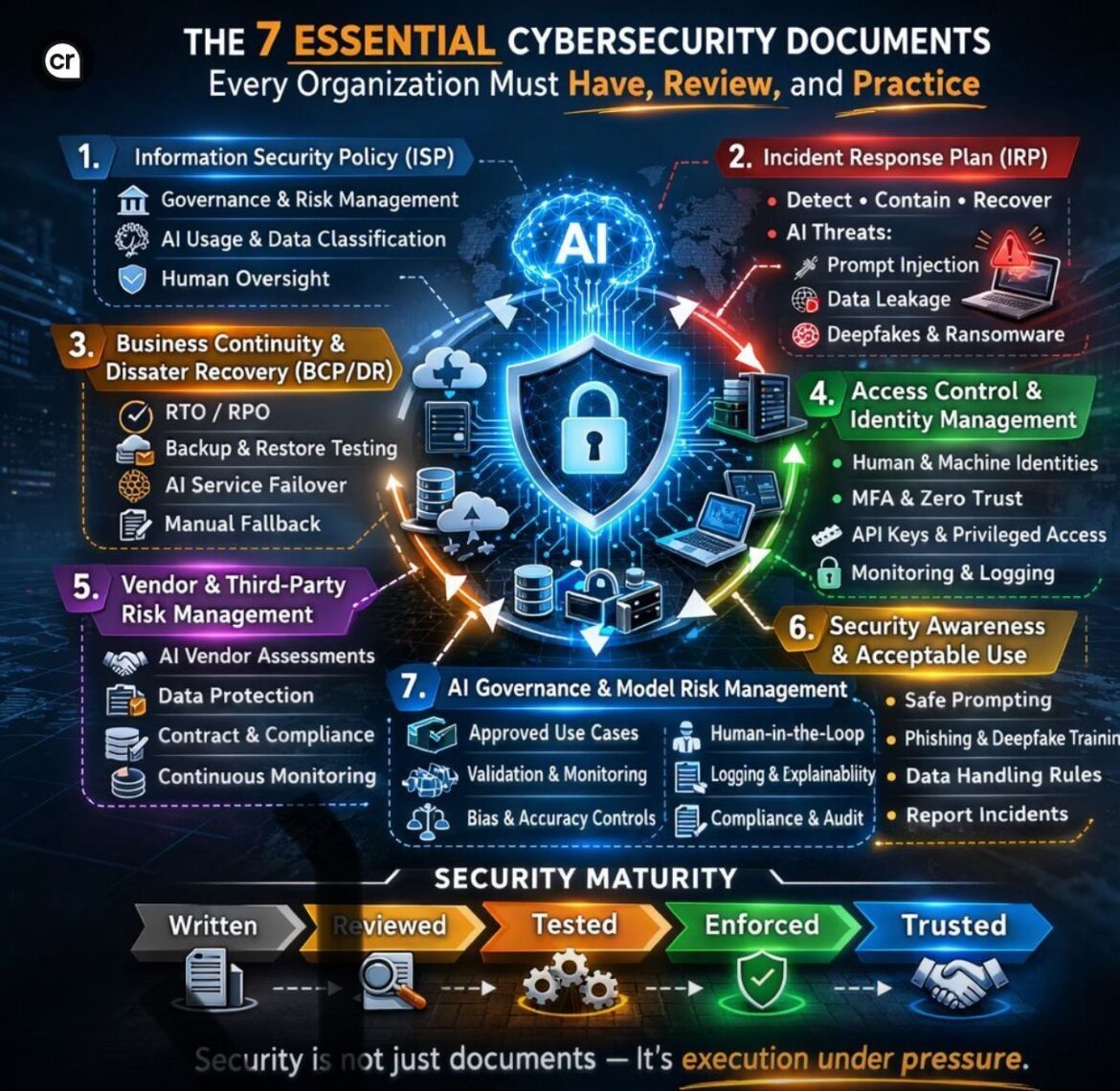
Every organization, regardless of size or industry, should possess a set of seven essential cybersecurity documents. These aren’t just compliance checkboxes; they are the bedrock upon which a truly secure and resilient enterprise is built. They provide direction, assign accountability, and ensure consistency when navigating the complex and ever-evolving threat landscape, particularly with the emergence of AI-driven threats.
The Foundation of Defense: Understanding Security Maturity
Before delving into the seven essential documents, it’s crucial to grasp the concept of security maturity. It’s a journey, not a destination, marked by distinct stages that transform static policies into dynamic, protective mechanisms.
Security maturity doesn’t solely stem from the act of writing policies. It evolves through a progressive five-stage process:
- Written: This initial stage involves the drafting and formalization of security policies and procedures. It’s the blueprint, but without further action, it remains just that – a piece of paper.
- Reviewed: Once written, documents must undergo rigorous review by relevant stakeholders. This ensures clarity, accuracy, and alignment with organizational objectives and regulatory requirements. This stage helps eliminate ambiguities and integrates diverse perspectives.
- Tested: This is where theory meets reality. Security documents must be tested through drills, simulations, and real-world exercises. This stage identifies weaknesses, validates assumptions, and allows teams to practice their roles, refining their responses before an actual incident occurs.
- Enforced: Policies are only as effective as their enforcement. This stage involves the consistent application of rules, the implementation of controls, and accountability for adherence. Enforcement ensures that security practices become embedded in the organizational culture.
- Trusted: The pinnacle of security maturity. When an organization reaches this stage, its security mechanisms are not only well-documented, reviewed, tested, and enforced, but they are also deeply integrated and inspire confidence across all levels of the organization. Employees, partners, and customers trust that the organization is genuinely secure and capable of handling threats effectively.
The fundamental question every leadership team must confront is: “If a cyber incident happened today, would our documented plans actually work in the real world?” The answer to this question often reveals the true state of an organization’s security maturity.
Let’s explore the seven essential cybersecurity documents that shepherd an organization through these crucial stages, ensuring robust defense against modern threats, including those amplified by artificial intelligence.
1. Information Security Policy (ISP): The Organizational Compass
The Information Security Policy (ISP) is the cornerstone of any cybersecurity program. It’s not merely a lengthy document; it’s the organization’s high-level commitment to safeguarding its information assets. The ISP sets the overarching principles, objectives, and responsibilities for information security across the entire enterprise. It dictates the “what” and “why” of security, serving as the ultimate authority for all subsequent, more detailed security documents.
Governance and Risk Management
At its core, the ISP establishes the organizational structure for security governance. This includes defining roles and responsibilities for security leadership, outlining decision-making processes, and detailing the framework for managing security risks. A well-crafted ISP ensures that security is integrated into business operations, not treated as a standalone IT function. It embraces a proactive approach to identifying, assessing, and mitigating risks. We emphasize that security policies “provide clear direction, accountability, and consistency,” making a security program “defendable” by demonstrating defined expectations and governance.
AI Usage and Data Classification
In an era increasingly defined by Artificial Intelligence, the ISP must explicitly address AI usage within the organization. This involves outlining acceptable use cases for AI technologies, defining ethical guidelines, and detailing data governance principles related to AI inputs and outputs. Crucially, the ISP should cover data classification — categorizing data based on its sensitivity and criticality. This classification then informs the level of protection required for each data type, ensuring that highly sensitive information, whether processed by humans or AI, receives appropriate safeguards.
Human Oversight
A critical component of the ISP, especially concerning AI, is the mandate for human oversight. While AI offers tremendous advantages, human intervention, review, and ultimate responsibility remain paramount. The ISP should outline processes for human review of AI-driven decisions, mechanisms for overriding automated actions if necessary, and clear lines of accountability for AI system performance and ethical adherence. This reinforces the principle that technology serves humanity, and not the other way around.
2. Incident Response Plan (IRP): Preparedness for Adversity
When a cyber breach inevitably occurs, speed and precision are paramount. An Incident Response Plan (IRP) is the blueprint that guides an organization’s actions from detection to recovery. It’s an urgent operational document that outlines the roles, responsibilities, procedures, and communication strategies required to effectively manage a security incident. The goal is to minimize damage, reduce recovery time, and restore normal operations as swiftly as possible. As we note, an IRP “defines the organizational rules and accountability model for handling security incidents.”
Detect, Contain, Recover
The IRP is typically structured around key phases:
- Detection: How security incidents are identified, whether through automated monitoring, user reports, or external intelligence.
- Containment: The immediate steps taken to limit the spread and impact of an incident, such as isolating affected systems or accounts.
- Eradication: Removing the root cause of the incident and eliminating any lingering threats.
- Recovery: Restoring affected systems and data to their pre-incident state, often involving backups and reconfigurations.
- Post-Incident Activity: A crucial phase for learning and improvement, involving analysis of the incident, identification of lessons learned, and updates to policies and procedures.
AI Threats: Prompt Injection, Data Leakage, Deepfakes & Ransomware
The modern IRP must specifically account for emerging AI-driven threats.
- Prompt Injection: Attacks that manipulate AI models through carefully crafted input prompts, potentially leading to unauthorized data access or malicious outputs. The IRP needs to define detection mechanisms and response strategies for such manipulation.
- Data Leakage: AI systems, particularly large language models, can inadvertently expose sensitive information through their responses or training data. The IRP should include procedures for identifying and mitigating AI-related data leakage, along with forensic steps to assess the extent of exposure.
- Deepfakes & Ransomware: The IRP must address the use of deepfake technology in sophisticated social engineering and phishing attacks, as well as the increasing sophistication of AI-powered ransomware. Response procedures should include forensic analysis techniques for AI-generated artifacts and strategies for negotiating or mitigating AI-enhanced extortion attempts.
A robust IRP moves beyond general guidelines, providing detailed, actionable playbooks for various incident types, turning policy into practical action.
3. Business Continuity & Disaster Recovery (BCP/DR): Sustaining Operations
Downtime, whether from a cyberattack, natural disaster, or system failure, is incredibly costly. A Business Continuity Plan (BCP) and Disaster Recovery (DR) plan work in tandem to ensure an organization can maintain essential functions during and after disruptive events. The BCP focuses on sustaining critical business operations, while the DR plan details the technical steps to recover IT infrastructure and data. Together, they aim to minimize the period of disruption and facilitate a swift return to normal.
RTO/RPO Targets
Central to BCP/DR are two critical metrics:
- Recovery Time Objective (RTO): The maximum tolerable duration of time that a computer system, network, or application can be down after a failure or disaster. It’s the target time for restoring a business process to an operational state.
- Recovery Point Objective (RPO): The maximum acceptable amount of data loss measured in time. For example, an RPO of 1 hour means that if a disaster occurs, the organization can afford to lose up to 1 hour of data.
These objectives guide the selection of recovery strategies and investments in resilient infrastructure. Clear RTO/RPO targets are negotiated with business units and documented, serving as benchmarks for recovery success.
Backup & Restore Testing
The best backup strategy is useless without rigorous, regular testing of restoration procedures. The BCP/DR document must specify schedules and methodologies for comprehensive backup and restore testing scenarios. This includes testing various data types, application environments, and storage locations to ensure data integrity and the ability to recover effectively. Untested backups are a significant risk exposure.
AI Service Failover and Manual Fallback
In an increasingly AI-driven environment, BCP/DR plans must expand to cover AI services specifically. This involves strategies for AI service failover, where critical AI models and platforms can automatically or manually switch to redundant systems in the event of a primary system failure. Furthermore, the plan should include provisions for manual fallback procedures – detailing how human operators can temporarily take over tasks normally performed by AI, or how less sophisticated, human-driven alternatives can be deployed to maintain essential services until AI systems are restored. This ensures continuity even when advanced AI capabilities are unavailable.
4. Access Control & Identity Management: The Gatekeepers
Security begins with identity. The Access Control and Identity Management document outlines the policies and procedures governing who can access what resources within an organization. It’s about granting the right level of access to the right entities, at the right time, and under the right conditions. This document is crucial for preventing unauthorized access and mitigating insider threats.
Human & Machine Identities
Beyond human users, the proliferation of IoT devices, cloud services, and microservices means an organization must manage a vast array of machine identities. This policy must define how both human users and automated systems (e.g., applications, services, IoT devices) are identified, authenticated, and authorized to interact with organizational resources. It involves defining naming conventions, credential management, and lifecycle processes for all digital identities.
MFA & Zero Trust
- Multi-Factor Authentication (MFA): The document mandates the use of MFA wherever possible, requiring users to provide two or more verification factors to gain access to a resource. This significantly reduces the risk of credential compromise.
- Zero Trust Principles: Embracing a Zero Trust architecture is paramount. This principle dictates “never trust, always verify.” Access is granted on a least-privilege basis, strictly monitored, and continuously re-evaluated, regardless of whether the user or device is inside or outside the traditional network perimeter. The policy outlines how Zero Trust principles are applied across the organization.
API Keys & Privileged Access
The policy must address the secure management of API keys, which are critical for inter-application communication and can pose significant risks if compromised. This includes guidelines for key generation, rotation, storage, and revocation. Furthermore, privileged access management (PAM) receives special attention, detailing heightened security controls for accounts with elevated permissions, such as robust authentication, session monitoring, and just-in-time access provisions.
Monitoring & Logging
Continuous monitoring and comprehensive logging are essential for detecting anomalous access patterns and potential breaches. The document specifies how access events are logged, where logs are stored, how long they are retained, and who is responsible for reviewing them. It also describes the alert mechanisms for suspicious activities, reinforcing the proactive posture of the access control system.
5. Vendor & Third-Party Risk Management: Extending the Perimeter
In today’s interconnected business ecosystem, organizations rarely operate in isolation. They rely on a sprawling network of vendors, suppliers, and third-party service providers. This reliance, while beneficial, introduces a significant attack surface. The Vendor & Third-Party Risk Management document outlines the processes for assessing, managing, and monitoring the security posture of all external entities that access or process organizational data or systems. Your security is only as strong as your weakest partner.
AI Vendor Assessments
The rise of AI introduces new complexities to third-party risk. This document must include specific criteria for assessing AI vendors, focusing on aspects like the security of their AI models, assurance of data privacy within AI services, the explainability and transparency of their AI algorithms, and their commitment to ethical AI practices. Due diligence goes beyond traditional IT security to encompass the unique risks associated with machine learning and large language models.
Data Protection
A core element of third-party risk management is ensuring data protection across the supply chain. The policy details requirements for vendors handling sensitive data, including encryption standards, data residency requirements, incident notification clauses, and data disposal protocols. It ensures that the organization’s data remains protected even when entrusted to external parties.
Contract & Compliance
Legal agreements with vendors are critical for enforcing security standards. This section outlines the inclusion of robust security clauses in contracts, covering performance metrics, audit rights, liability, and compliance with relevant regulations (e.g., GDPR, HIPAA, CCPA). It establishes clear expectations and legal recourse if security failures occur.
Continuous Monitoring
Vendor security is not a one-time assessment. The document mandates continuous monitoring of third-party security postures, which can involve regular security reviews, vulnerability assessments, security questionnaires, and leveraging intelligence feeds to track vendor-related breaches or vulnerabilities. This ensures that evolving risks are promptly identified and addressed.
6. Security Awareness & Acceptable Use: Empowering the Human Element
People remain the most targeted attack vector in cybersecurity, often unwittingly. The Security Awareness & Acceptable Use document is designed to educate employees, contractors, and other stakeholders about their roles and responsibilities in maintaining security. It establishes clear guidelines for the permissible use of organizational IT resources and data, turning every individual into an active participant in the organization’s defense. As we states, “Security must be integrated into the corporate strategy, fostering a culture where everyone… actively supports security and privacy compliance.”
Safe Prompting
With the pervasive use of AI, this document must include guidelines for “safe prompting” when interacting with AI tools. This involves instructing users on what types of information should not be entered into public or unauthorized AI models, best practices for crafting prompts that minimize the risk of data leakage, and awareness of the potential for AI models to retain inputted data.
Phishing & Deepfake Training
Training programs outlined in this document must evolve beyond traditional phishing awareness to include deepfake detection. Employees need to be educated on how to identify increasingly sophisticated phishing attempts, including those leveraging AI-generated voice or video to impersonate individuals. Simulated deepfake attacks can be integrated into training to enhance realism and preparedness.
Data Handling Rules
Clear, concise data handling rules are essential. This section specifies how different classifications of data should be stored, transmitted, shared, and disposed of. It covers everything from protecting intellectual property to complying with personal data regulations, reducing the risk of accidental or malicious data exposure.
Report Incidents
A crucial aspect of security awareness is fostering a culture where employees feel empowered and encouraged to report suspicious activities or potential security incidents without fear of reprisal. The document outlines the procedures for reporting, emphasizing the importance of timely reporting to enable swift incident response.
7. AI Governance & Model Risk Management: Navigating the AI Frontier
As artificial intelligence rapidly integrates into business operations, dedicated governance and risk management for AI itself become imperative. This document establishes the framework for the responsible, ethical, and secure development, deployment, and operation of AI systems. It’s about ensuring that AI adoption accelerates innovation without introducing unacceptable risks.
Approved Use Cases
This section defines the criteria and processes for approving AI use cases within the organization. It ensures that AI is applied strategically and responsibly, evaluating potential benefits against inherent risks, particularly concerning privacy, fairness, and security. It prevents ad-hoc, unregulated deployment of AI systems.
Validation & Monitoring
AI models, unlike traditional software, can drift in performance and introduce bias over time. This document outlines rigorous procedures for model validation, performance monitoring, and recalibration. It specifies metrics for assessing model accuracy, reliability, and fairness, ensuring that AI systems continue to operate as intended and do not degrade over time.
Bias & Accuracy Controls
Addressing bias and ensuring accuracy are critical ethical and operational considerations for AI. The policy details mechanisms for identifying, mitigating, and documenting biases in training data and model outputs. It also establishes acceptable accuracy thresholds and outlines procedures for independent auditing of AI system decisions and behaviors.
Human-in-the-Loop
Similar to human oversight in the ISP, the Human-in-the-Loop (HITL) concept ensures that there are clearly defined points in AI-driven workflows where human review and decision-making are required. This document specifies when and how human intervention occurs, particularly for high-stakes decisions or scenarios where AI performance is uncertain.
Logging & Explainability
For AI systems to be governable, their operations must be transparent and auditable. This section mandates comprehensive logging of AI system inputs, outputs, decisions, and system performance metrics. Furthermore, it addresses “explainability” – the ability to understand and articulate how an AI model arrived at a particular decision, which is crucial for troubleshooting, compliance, and building trust.
Compliance & Audit
AI systems introduce new dimensions to regulatory compliance. This policy ensures that AI initiatives adhere to relevant industry standards, data protection laws, and emerging AI regulations. It also outlines processes for internal and external audits of AI systems to verify compliance, assess risk, and ensure ethical operation. The AWS IoT Lens, for example, emphasizes “security governance” and defining “security policy so that it can be written into verifiable checks using policy as code techniques,” also noting that “IoT applications should work in coordination with the security governance team for the organization.”
The Path to Security Maturity: Moving Beyond Documentation
While these seven documents are indispensable, simply having them written down is merely the first step. True security maturity, as previously discussed, is achieved through a deliberate progression:
- Written: The policies exist.
- Reviewed: Stakeholders have scrutinized and approved them.
- Tested: They’ve been put through their paces in simulations and drills, revealing strengths and weaknesses. This is where the rubber meets the road, transforming theoretical knowledge into practical capability.
- Enforced: The policies are actively implemented, adhered to, and violators are held accountable. This demonstrates an organizational commitment to security.
- Trusted: The entire organization, from the leadership team to individual employees, trusts that these documents and the processes they define will protect the organization when it matters most.
Security is not just a stack of papers; it’s execution under pressure. It’s the ability of a team to rally, follow established protocols, and mitigate a threat effectively when chaos threatens. The question is not only “Do we have these documents?” but more profoundly, “Would they actually work when the stakes are highest?” This continuous cycle of writing, reviewing, testing, enforcing, and building trust is what elevates an organization’s cybersecurity posture from reactive firefighting to proactive, resilient defense.
The IoT Worlds Advantage
Navigating the complexities of cybersecurity, especially with the rapid evolution of AI and the expansive landscape of IoT, requires specialized expertise. Crafting, reviewing, testing, and enforcing these seven essential cybersecurity documents, and truly embedding them into your organizational culture, is a significant undertaking. It demands a deep understanding of evolving threats, regulatory landscapes, and cutting-edge technologies.
At IoT Worlds, we specialize in helping organizations like yours move beyond theoretical security to practical, measurable, and trusted defense strategies. Our experts can assist you in developing robust cybersecurity frameworks, tailoring these essential documents to your unique operational context, and guiding you through the critical stages of security maturity – from written to trusted. We provide the strategic insight and practical guidance needed to ensure your cybersecurity isn’t just about tools, but about leadership, preparedness, and flawless execution.
Don’t leave your organization’s defense to chance. Ensure your security posture is battle-tested and resilient.
Unlock your organization’s full cybersecurity potential. Contact us today to learn how IoT Worlds can help you implement, test, and enforce a world-class security program.
Email us at info@iotworlds.com to schedule a consultation.