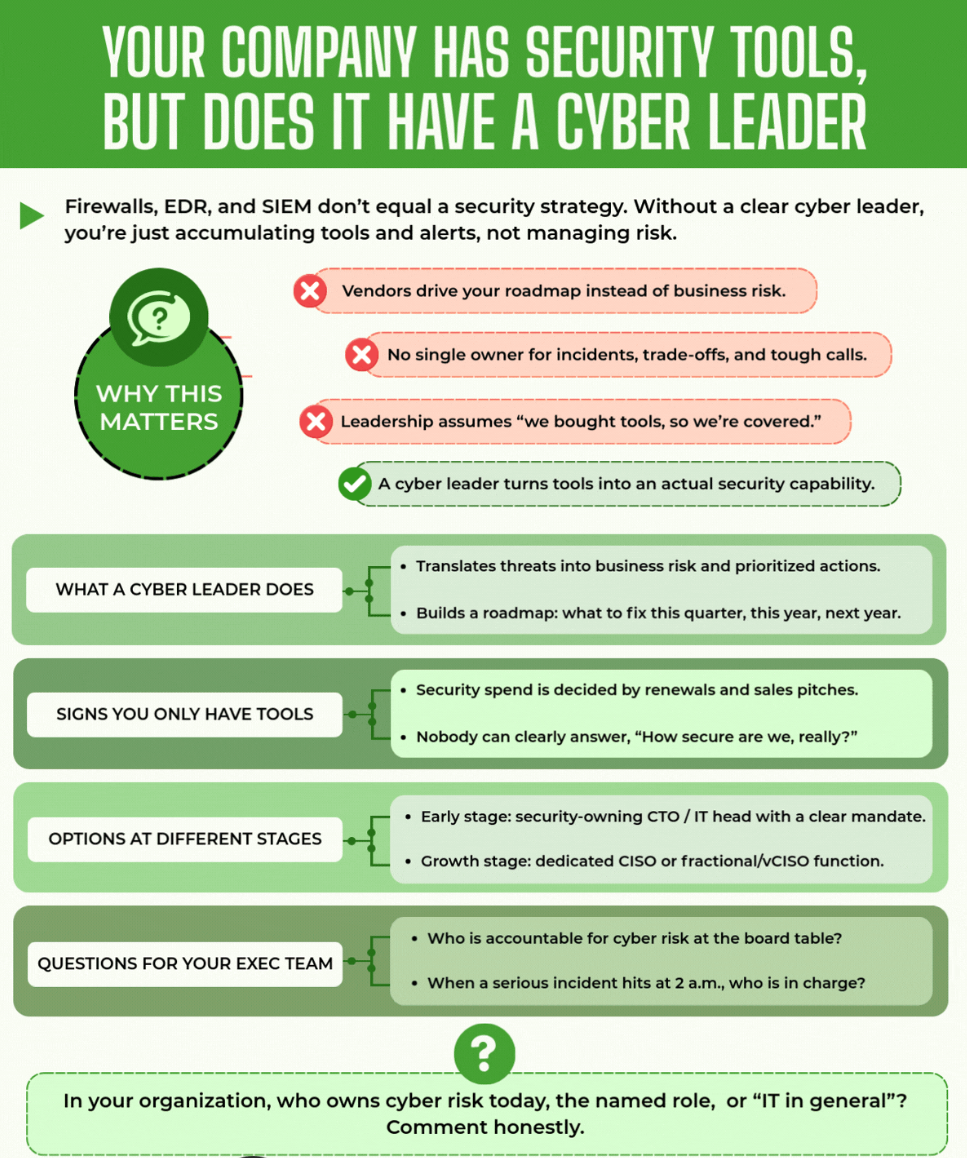
In the ever-evolving landscape of digital threats, organizations often find themselves in an arms race, acquiring an arsenal of cybersecurity tools—firewalls, Endpoint Detection and Response (EDR) systems, Security Information and Event Management (SIEM) platforms, email security solutions, and more. On paper, it appears to be a robust defense, a sign of maturity. Yet, when fundamental questions about actual security posture, top cyber risks, or incident recovery speed are posed, silence often ensues. This silence is not merely an absence of an answer; it’s a resounding signal of a critical gap: a leadership gap in cybersecurity.
This article argues that the true differentiator in modern cybersecurity is not the quantity or sophistication of tools, but the presence of clear, decisive cybersecurity leaders. These individuals transform a collection of technologies into a coherent, business-aligned security capability, moving organizations from a reactive, tool-dependent state to a proactive, risk-managed one.
The Illusion of Tool-Based Security: Why More Tools Don’t Always Mean More Security
The allure of a new security tool is powerful. Marketing promises comprehensive protection, advanced detection, and effortless compliance. Companies invest heavily, believing that each new acquisition strengthens their perimeter. However, a significant problem arises when this investment isn’t guided by a strategic vision or overseen by dedicated leadership.
When Vendors Drive Your Roadmap
Without a dedicated cybersecurity leader, the security roadmap often becomes dictated by vendors. Their sales pitches and renewal cycles, rather than a clear understanding of the organization’s unique business risks, shape purchasing decisions. This leads to a patchwork of disparate systems, each with its own alerts, dashboards, and management complexities, but lacking a unified purpose. The focus shifts from mitigating actual business risk to simply deploying the latest technology. This vendor-driven approach can result in significant budget allocation to tools that may not even align with the organization’s most pressing vulnerabilities or strategic objectives.
The Problem of Distributed Accountability
Incidents, trade-offs, and critical decisions require a single, clear owner. In environments lacking strong cybersecurity leadership, incidents can devolve into “Slack chaos” or endless email chains, with no one empowered to make the final call. This fragmented accountability prolongs response times, exacerbates damages, and erodes trust. When tough decisions about incident containment, data recovery, or communication strategy need to be made under pressure, the absence of a designated authority can be catastrophic. The problem is not merely about finding someone to blame, but about having a pre-defined process and empowered individual to navigate complex, high-stakes situations.
The Dangerous Assumption: “We Bought Tools, So We’re Covered”
Perhaps the most insidious byproduct of a tool-centric approach is the false sense of security it instills in leadership. The assumption that simply purchasing advanced firewalls, EDR, and SIEM means the organization is “covered” is a dangerous fallacy. These tools are only as effective as the strategy behind them, the expertise managing them, and the leadership integrating them into the broader business context. This complacent mindset hinders further investment in critical areas like security training, process development, and, most importantly, human capital in the form of dedicated cyber leadership.
The Consequence: Accumulating Alerts, Not Managing Risk
Ultimately, without a clear cyber leader, organizations are not managing risk; they are accumulating tools and alerts. The “noise” generated by a multitude of security systems can overwhelm security operations centers (SOCs), leading to alert fatigue and the potential for genuine threats to be overlooked. The sheer volume of data, devoid of intelligent prioritization and contextual analysis, becomes a burden rather than an asset. This reactive firefighting approach diverts resources from proactive measures, perpetuating a cycle of vulnerability.
The Defining Role of Cybersecurity Leaders
A true cyber leader transforms this chaotic landscape into a structured, proactive defense strategy. They bridge the gap between technical tools and business objectives, providing clarity, direction, and accountability.
Translating Threats into Business Risk and Prioritized Actions
One of the most critical functions of a cybersecurity leader is to translate complex technical threats into understandable business risks. They don’t just speak about malware strains or CVEs; they articulate the potential impact on revenue, operational uptime, customer trust, and regulatory compliance. This translation is essential for securing executive buy-in and allocating resources effectively. By quantifying risk in business terms, leaders can justify necessary investments and ensure that security initiatives align with organizational priorities. For example, instead of merely stating “we have a phishing problem,” a leader explains, “phishing attacks could lead to a $X million loss in intellectual property this quarter, impacting our competitive edge.”
Furthermore, they prioritize actions based on these identified risks. With limited resources, not every vulnerability can be addressed simultaneously. A leader makes informed decisions about which risks matter most this quarter, this year, and next year, creating a pragmatic roadmap for mitigation. This involves a deep understanding of the organization’s critical assets, threat landscape, and risk appetite.
Building a Comprehensive Security Roadmap
Beyond immediate incident response, a cybersecurity leader is responsible for building a long-term strategic roadmap. This roadmap outlines not just what tools to acquire, but how they will be integrated, what processes will govern their use, and how security will evolve to meet future threats and business needs. It’s a living document that adapts to changes in the threat landscape, regulatory requirements, and organizational growth. This roadmap ensures that security investments are sequential, logical, and contribute to an overarching defense posture, rather than being ad-hoc purchases. It also defines milestones and metrics to track progress, allowing for continuous improvement and accountability.
Owning Incidents End-to-End, Including Communication
When an incident inevitably occurs, the cyber leader is the central point of contact and decision-maker. They own the incident response process from detection to resolution, ensuring swift containment, thorough investigation, and effective recovery. Crucially, they also manage all internal and external communication. This includes informing executive leadership, engaging legal counsel, coordinating with public relations, and potentially notifying affected customers or regulatory bodies. This single point of ownership ensures consistency, accuracy, and timely dissemination of information, minimizing reputational and financial damage.
We emphasize that effective incident response is a sign of operational maturity, particularly for IoT systems where traditional IT playbooks fall short due to the unique characteristics of connected devices, such as physical interaction, remote accessibility challenges, and potential physical impact of compromise. This highlights the critical need for a leader who can adapt strategies to unique organizational contexts.
Building People-Led Defense, Not Product Dependency
While tools are essential, a truly robust security posture is built on people and processes. A cybersecurity leader invests in talent development, fosters a security-aware culture, and champions continuous training. They understand that no tool, however advanced, can fully compensate for human error or lack of awareness. By empowering individuals with the knowledge and skills to identify and respond to threats, and by establishing clear, repeatable processes, they build a resilient defense that is not solely reliant on product features. This also includes cultivating a culture of proactive threat intelligence sharing, where internal teams are encouraged to report suspicious activities and learn from past incidents.
We assert that the shift from reactive remediation to predictive resilience is the new wave in cyber defense, significantly enabled by AI’s ability to find anomalies in real-time. This emphasizes how effective leaders leverage technology to empower their teams, moving beyond mere reactive responses.
The Silence is a Signal: Signs You Only Have Tools, Not Leadership
The absence of strong cybersecurity leadership often manifests in clear, observable symptoms within an organization. Recognizing these signals is the first step towards addressing the leadership gap.
Security Spend Decided by Renewals and Sales Pitches
One of the most telling signs of a leadership vacuum is when security budget allocations are primarily driven by tool renewals and vendor sales pitches rather than strategic necessity. Without a leader to articulate a clear vision and prioritize investments based on risk, decisions become reactive and opportunistic. This can lead to overspending on redundant functionalities or underinvestment in critical, less glamorous, but equally vital areas like security awareness training or robust incident response planning. The budget becomes a reflection of vendor influence, not organizational risk posture.
Inability to Answer: “How Secure Are We, Really?”
The inability of key stakeholders, from IT managers to executive leadership, to confidently and articulately answer the question, “How secure are we, really?” is a flashing red light. This question probes beyond the mere existence of security tools; it asks about their effectiveness, their integration, and their alignment with the organization’s risk profile. A leader provides this clarity through regular risk assessments, performance metrics, and transparent communication. Without leadership, the answer remains vague, often relying on anecdotal evidence or an unverified assumption that “everything’s running, so we must be secure.”
Incidents Turn into Slack Chaos
When a security incident strikes, the organization’s true security posture is revealed. If an incident triggers widespread panic, disorganized communication on collaboration platforms like Slack, and a frantic search for who is responsible or what to do next, it’s a clear indicator of a leadership void. A well-led organization has predefined incident response plans, clearly assigned roles, and established communication protocols, all orchestrated by a cyber leader. The chaos of an uncontrolled incident can lead to prolonged downtime, data loss, and significant reputational damage.
No One Makes the Final Call
In the crucible of a cyber incident or during complex security strategy discussions, difficult trade-offs often arise. Should a system be taken offline immediately, even if it disrupts business operations? Should sensitive customer data be reported, even if it triggers negative publicity? Without a designated decision-maker, these critical choices can be delayed, debated endlessly, or worse, left unmade. A cybersecurity leader is empowered to make these tough calls, balancing security imperatives with business continuity, and accepting accountability for the outcomes.
Boards Hear “We’re Fine” Without Clarity
Executive boards and stakeholders require clear, concise, and business-focused updates on cybersecurity posture. If board reports consist of vague assurances of being “fine” or overly technical jargon that lacks strategic context, it signals a lack of leadership in communicating risk. A cyber leader translates complex security information into actionable intelligence for the board, highlighting top risks, progress on mitigation, and the overall trajectory of the security program. This enables informed governance and strategic oversight.
The Cyber Leader’s Toolkit: What They Do That Tools Never Will
Dedicated cybersecurity leaders bring a unique set of strategic and interpersonal skills that no software or hardware solution can replicate. They are the architects of a resilient defense, not just the custodians of technology.
Tying Security to Revenue, Uptime, and Trust
A leader understands that cybersecurity is not merely a cost center but a critical enabler of business success. They articulate how robust security directly contributes to revenue by protecting intellectual property, maintaining customer loyalty, and enabling secure digital transactions. They connect security measures to operational uptime, demonstrating how proactive defense minimizes costly disruptions. Crucially, they emphasize the vital role of security in building and preserving trust—with customers, partners, and regulators. This business-centric approach moves security from a technical concern to a strategic imperative.
Deciding Which Risks Matter This Quarter
Effective risk management is about making choices. A cybersecurity leader doesn’t try to mitigate every conceivable risk simultaneously. Instead, they leverage quantitative and qualitative risk assessments to identify the most significant threats to the organization’s critical assets and business objectives for a given period. They then prioritize these risks, allocating resources and effort to address those with the highest likelihood and potential impact. This pragmatic approach ensures that security efforts are focused, efficient, and deliver the greatest return on investment.
Owning Incidents End-to-End, Including Communication
As previously discussed, the leader’s role in incident response is paramount. They orchestrate the entire process, from initial detection and containment to eradication, recovery, and post-incident analysis. Their ownership extends to meticulously managing all communications, both internally and externally. This includes crafting messages for employees, customers, partners, and potentially regulatory bodies or the media. Clear, consistent, and empathetic communication during a crisis is essential for maintaining trust and minimizing long-term damage.
IoT Worlds points out that modern cybersecurity involves a proactive understanding of adversaries and a continuous cycle of defense, detection, and response, all of which are orchestrated by a leader during an incident.
Building People-Led Defense, Not Product Dependency
While security tools form the technological backbone, the human element remains the strongest, yet often weakest, link. A cyber leader focuses on empowering people. This involves:
- Security Awareness Training: Implementing continuous, engaging training programs that go beyond basic phishing tests to educate employees on recognizing threats, understanding policies, and adopting secure behaviors.
- Talent Development: Investing in the skills and professional growth of the security team, ensuring they have the expertise to manage advanced tools and respond to sophisticated threats.
- Fostering a Security Culture: Encouraging every employee, from the mailroom to the boardroom, to view security as a shared responsibility rather than solely an IT function. This proactive approach cultivates vigilance and reduces the organization’s vulnerability to social engineering and internal threats.
Options for Establishing Cybersecurity Leadership at Different Stages
The journey to establishing robust cybersecurity leadership looks different for organizations at various stages of growth and maturity. There isn’t a one-size-fits-all solution, but strategic options exist.
Early Stage: Security-Owning CTO / IT Head with a Clear Mandate
For startups and smaller enterprises, a dedicated, full-time CISO might not be immediately feasible. In these instances, the Chief Technology Officer (CTO) or the Head of IT can assume the mantle of cybersecurity leadership. However, this demands a clear and unequivocal mandate. Their responsibilities must explicitly include cybersecurity strategy, risk management, and incident response, extending beyond traditional IT operations. They need adequate resources, budget authority, and direct access to executive leadership to be effective. This role requires a shift in focus from purely technical enablement to strategic risk oversight. Key characteristics of this role include:
- Strategic Alignment: Ensuring security initiatives are directly aligned with business goals and growth objectives, prioritizing protection for revenue-generating processes and intellectual property.
- Risk Assessment and Prioritization: Conducting regular, simplified risk assessments to identify and address the most critical vulnerabilities without over-investing in unnecessary tools.
- Foundational Security Establishment: Implementing core security controls such as strong access management, basic network segmentation, regular backups, and employee security awareness programs.
- Incident Response Planning (Basic): Developing and regularly testing a lean, effective incident response plan tailored to the organization’s size and potential threat landscape, designating clear roles for limited staff.
- Vendor Management: Evaluating security aspects of third-party tools and services, ensuring contracts include appropriate security clauses and due diligence is performed on vendors.
- Communication: Clearly articulating risks and security needs to leadership in business terms, making the case for necessary security investments in a constrained environment.
This early-stage leader serves as the crucial bridge between nascent security efforts and the broader business strategy, laying the groundwork for future maturity.
Growth Stage: Dedicated CISO or Fractional/vCISO Function
As organizations mature and grow in complexity, a dedicated cybersecurity leader becomes imperative.
Dedicated CISO
A dedicated Chief Information Security Officer (CISO) is a full-time executive responsible for the entire cybersecurity program. This role is typically seen in mid-sized to large enterprises, offering comprehensive strategic leadership and operational oversight. A CISO operates at the executive level, reporting directly to the CEO, CIO, or even the board. Their responsibilities include:
- Strategic Vision and Roadmap: Developing and executing a multi-year cybersecurity strategy aligned with business objectives, regulatory requirements, and the evolving threat landscape. They continuously refine this roadmap based on emerging threats and organizational changes.
- Risk Management Framework: Establishing and maintaining a robust risk management framework, including regular assessments, quantification of cyber risks, and oversight of mitigation efforts. They communicate residual risk to executive management and the board.
- Policy and Compliance: Developing, implementing, and enforcing comprehensive cybersecurity policies, standards, and procedures. Ensuring compliance with relevant industry regulations (e.g., GDPR, HIPAA, PCI DSS) and internal governance requirements.
- Incident Response and Crisis Management: Leading the organization’s incident response team, developing playbooks, conducting drills, and managing all facets of a security incident from detection to post-mortem analysis and communication. Their leadership is crucial for minimizing damage and ensuring rapid recovery.
- Security Architecture and Technology Strategy: Guiding the selection, implementation, and integration of security technologies (EDR, SIEM, firewalls, DLP, IAM, etc.) to build a multi-layered defense. They ensure technology choices align with the overall security strategy and architectural principles.
- Security Operations Management: Overseeing security operations, including threat detection, vulnerability management, penetration testing, and security monitoring. Ensuring the security operations center (if applicable) is effective and efficient.
- Security Awareness and Training: Championing a strong security culture across the organization through continuous awareness programs and specialized training for technical staff.
- Budget Management: Managing the cybersecurity budget, justifying investments, and ensuring optimal allocation of resources to achieve strategic security objectives.
- Stakeholder Communication: Regularly communicating cyber risk, security posture, and strategic initiatives to executive leadership, the board of directors, auditors, and external partners. This involves translating complex technical details into business-relevant insights.
Fractional/Virtual CISO (vCISO)
For growth-stage companies that require executive-level cybersecurity expertise but are not yet ready for a full-time CISO, a fractional or virtual CISO (vCISO) offers a compelling solution. A vCISO is an external cybersecurity expert who provides strategic guidance and leadership on a part-time or retainer basis. This model offers several advantages:
- Cost-Effectiveness: Provides access to high-level security expertise without the overhead of a full-time executive salary and benefits. This is particularly appealing for organizations with evolving security needs or limited budgets.
- Expertise on Demand: VCLS bring a wealth of diverse experience from working with multiple organizations across various industries. They are often up-to-date with the latest threats, technologies, and regulatory requirements.
- Strategic Guidance: Focuses on developing a strategic security roadmap, assessing risks, implementing governance, and coaching internal teams rather than day-to-day operational tasks.
- Objectivity: As an external resource, a vCISO can provide an unbiased assessment of the organization’s security posture and recommendations, free from internal politics or biases.
- Flexibility and Scalability: Engagements can be tailored to the organization’s specific needs and scaled up or down as required, offering flexibility as the company grows.
- Board-Level Communication: Can effectively communicate cyber risk and strategic initiatives to the executive team and board, fulfilling the governance requirements of a CISO.
A vCISO ideally works closely with existing IT teams to elevate their capabilities, institutionalize best practices, and guide the organization towards a more mature security posture, eventually helping to onboard and transition to a full-time CISO when the organization is ready. In both scenarios—dedicated CISO or vCISO—the key is the presence of a strategic leader who actively manages cyber risk and defines the security narrative, rather than letting tools or external sales pitches define it.
Critical Questions for Your Executive Team
To assess the current state of cybersecurity leadership within your organization, executive teams must engage in candid self-reflection. These questions cut to the core of accountability and incident preparedness.
Who is Accountable for Cyber Risk at the Board Table?
This question goes beyond identifying who manages cybersecurity operations. It asks who among the organization’s highest leadership—the board of directors or executive committee—is ultimately responsible for overseeing and understanding the organization’s cyber risk posture. Is there a designated board member or committee lead who regularly receives detailed, business-relevant updates on cyber threats, risk levels, and strategic mitigation efforts? The answer reveals whether cybersecurity is viewed as a fundamental business risk requiring governance at the highest level, or merely an operational IT concern.
When a Serious Incident Hits at 2 a.m., Who Is in Charge?
This is the ultimate stress test for any organization’s incident response capability. A serious cyber incident—a ransomware attack, a major data breach, a critical system outage—doesn’t adhere to business hours. When it strikes in the middle of the night, does your organization have a clear, pre-defined chain of command? Is there a designated individual, empowered with the authority and resources to mobilize teams, make critical decisions, and initiate recovery efforts? Or will it be a scramble, with multiple parties attempting to coordinate without clear leadership? The answer to this question reveals the maturity of your incident response planning and the presence (or absence) of true cybersecurity leadership.
We highlight the increasing attack surface due to the convergence of IT, OT, and IoT, making it even more crucial to have clear accountability and leadership when incidents occur, as these can have physical world impacts.
The Imperative of Leadership: You Can’t Outsource Ownership
In an era defined by persistent cyber threats and interconnected digital ecosystems, the stark reality is that organizations can outsource software, managed services, and even some operational security functions. However, they cannot outsource ownership. The ultimate responsibility for an organization’s cybersecurity posture, its resilience, and its ability to recover from incidents resides internally.
A cybersecurity leader embodies this ownership. They represent the conscience, the strategist, and the accountable party for all things cyber. They translate the abstract world of threats into tangible business impact, build a roadmap for sustained defense, and navigate the chaos of incidents with clarity and authority. Without this critical leadership, even the most sophisticated security tools become mere ornaments—expensive, complex, and ultimately ineffective in the face of determined adversaries.
The question is no longer “Do we have enough security tools?” but “Do we have the security leadership necessary to wield those tools effectively and protect our most valuable assets?” The future of your organization’s security—its revenue, its uptime, its trust—hinges on finding that answer.
Is your organization struggling with a leadership gap in cybersecurity? Are you accumulating tools but lacking direction? IoT Worlds offers expert consultancy services to help organizations like yours identify and implement the strategic cybersecurity leadership you need to build a truly resilient defense. From risk assessment and roadmap development to fractional CISO services and incident response planning, we help you transform your security posture from reactive to strategic.
Reach out to us today to schedule a consultation and begin building a security foundation driven by clear vision and decisive leadership.
Email: info@iotworlds.com