The Industrial Internet of Things (IIoT) is rapidly transforming industries, promising unprecedented levels of efficiency, productivity, and innovation. However, this revolutionary leap also introduces a host of complex security challenges. The convergence of operational technology (OT) and information technology (IT), coupled with the unique vulnerabilities of IIoT devices, necessitates a robust and adaptive security governance model. Without proper safeguards, the very benefits IIoT offers can become significant liabilities, leading to operational disruptions, data breaches, and even physical harm.
This article delves into a comprehensive IIoT security governance framework, outlining critical dimensions and providing practical strategies to safeguard your industrial operations. We will examine the inherent vulnerabilities across the IIoT stack, from the device level to the cloud, and present a structured approach to mitigate these risks.
The Evolving Threat Landscape in IIoT
The industrial sector has traditionally relied on air-gapped or isolated networks for its operational technology (OT) systems. However, the advent of IIoT has blurred these boundaries, connecting critical industrial assets to the wider internet and exposing them to a new spectrum of cyber threats. Understanding the distinct characteristics of IIoT and OT device vulnerabilities is the first step toward effective security.
IIoT Devices: The Exposed Frontier
IIoT devices, often designed for specific functions and deployed in large numbers, present a unique set of security challenges. Their reliance on over-the-air (OTA) communication, wireless protocols, and cloud connectivity significantly increases their exposure to attacks.
- Internet Exposure: Unlike traditional, isolated OT systems, IIoT devices are frequently connected to the internet to facilitate data transmission, remote monitoring, and control. This direct exposure makes them discoverable targets for malicious actors.
- Limited Security Resources: Many IIoT devices are resource-constrained, meaning they have limited processing power, memory, and energy. This can restrict the implementation of robust security features like complex encryption algorithms, extensive logging, or sophisticated intrusion detection systems.
- Wireless and Cloud Dependency: The use of Wi-Fi, Bluetooth, LoRaWAN, and cellular (5G/4G) for connectivity, along with reliance on cloud platforms for data storage, processing, and application hosting, introduces multiple points of vulnerability. Each wireless protocol has its own security considerations, and cloud security becomes a shared responsibility.
OT Devices: Legacy Vulnerabilities in a Connected World
Traditional OT devices, such as PLCs (Programmable Logic Controllers) and HMIs (Human-Machine Interfaces), were not originally designed with modern cybersecurity threats in mind. While historically less exposed to the internet, their integration into IIoT ecosystems highlights inherent weaknesses.
- Lack of Data Encryption: Many legacy OT protocols and devices do not inherently support encryption, transmitting data in plain text. This makes them susceptible to eavesdropping and manipulation if an attacker gains access to the network.
- Legacy Protocols: Older, proprietary protocols often lack built-in security features and were designed for trusted, closed environments. Integrating these into internet-connected IIoT systems can create significant security gaps.
- Physical Vulnerabilities: Traditional OT systems sometimes lack robust physical access controls, making them vulnerable to tampering or unauthorized device modification.
The convergence of IT and OT, termed IT/OT convergence, further complicates the security landscape when considering IIoT. This merging of previously disparate systems expands the attack surface, requiring a holistic approach to security that accounts for the unique characteristics and risks of both environments. Organizations must adapt their strategies to protect critical infrastructure, often targeted by sophisticated threat actors.
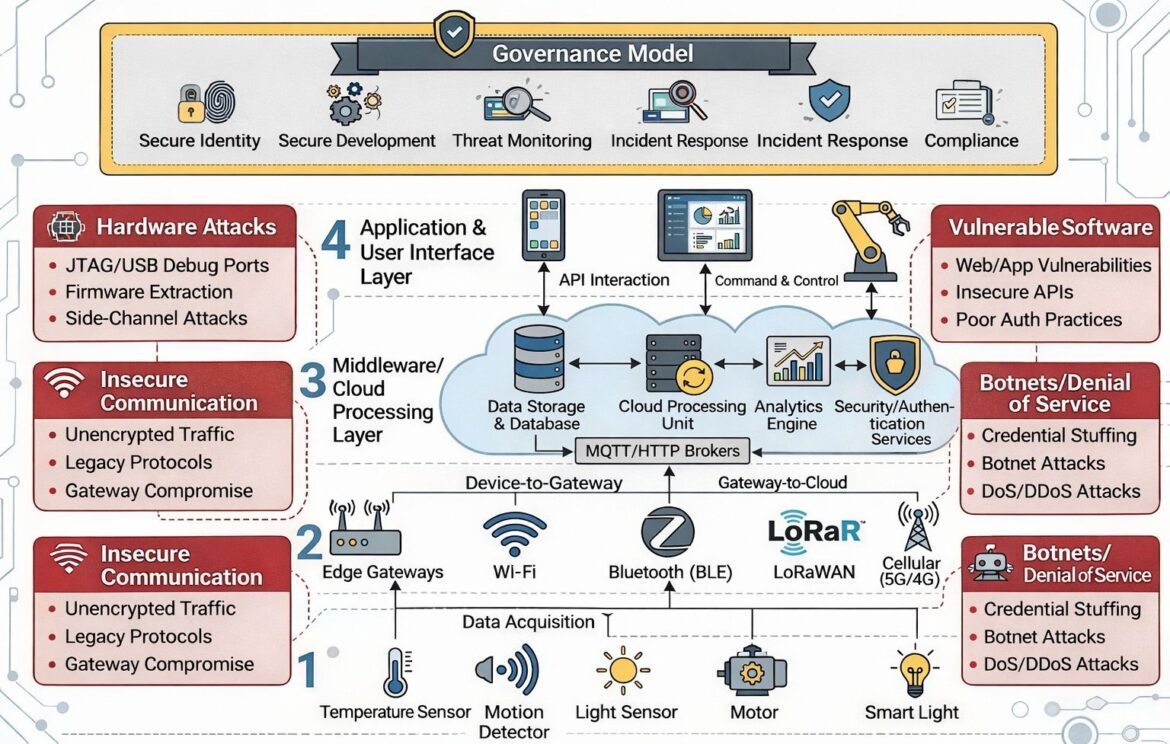
The Six Pillars of IIoT Impact: A Layered Security Model
Effective IIoT security governance requires a multi-layered approach that addresses vulnerabilities at each stage of the IIoT architecture. Drawing from the provided framework, we can identify four distinct layers and two overarching critical dimensions that are vital for comprehensive protection.
Layer 1: Data Acquisition – Securing the Sensors
This foundational layer comprises the physical sensors and actuators (temperature sensors, motion detectors, light sensors, motors, smart lights) that collect data from the physical world and often initiate commands. These devices are the “eyes and ears” of the IIoT system.
Potential Vulnerabilities:
- Insecure Communication (Device-to-Gateway): The communication between these edge devices and the next layer (edge gateways) is a prime target.
- Unencrypted Traffic: If data from sensors is transmitted without encryption, it can be intercepted and read by unauthorized parties. This could reveal sensitive operational data or allow for the injection of false readings.
- Legacy Protocols: Some sensors might use older, insecure protocols that are easily exploited.
- Gateway Compromise: If the edge gateway is compromised, all data flowing through it, even from secure sensors, can be at risk.
- Physical Tampering: As physical devices, sensors are susceptible to direct manipulation. An attacker could tamper with a sensor to provide false data, disable its function, or extract sensitive information.
- Firmware Vulnerabilities: Like any embedded system, sensors run firmware, which can have exploitable bugs or default credentials.
Mitigation Strategies:
- Secure by Design: Implement security from the initial design phase, incorporating secure boot, hardware-level encryption capabilities, and tamper-detection mechanisms.
- Strong Authentication for Devices: Employ mutual authentication between sensors and gateways to ensure only authorized devices can communicate.
- Secure Communication Protocols: Utilize robust, encrypted communication protocols for device-to-gateway communication (e.g., TLS/SSL). Where legacy protocols are unavoidable, implement compensating controls like network segmentation and intrusion detection.
- Physical Security: Securely mount sensors and implement physical access control measures to prevent unauthorized tampering. Regularly inspect devices for signs of compromise.
- Default Credential Management: Ensure all default credentials are changed to strong, unique passwords immediately upon deployment.
Layer 2: Edge Gateways and Connectivity – The Network’s First Line of Defense
Edge gateways act as the aggregation points for data from numerous sensors, translating various protocols and often performing localized processing before forwarding data to the cloud. This layer also encompasses the diverse connectivity mechanisms like Wi-Fi, Bluetooth (BLE), LoRaWAN, and Cellular (5G/4G).
Potential Vulnerabilities:
- Insecure Communication: Similar to Layer 1, but at a broader scale, communication from edge gateways to the cloud can be vulnerable.
- Unencrypted Traffic: Data transmitted from gateways to the cloud without encryption is exposed.
- Legacy Protocols: Gateways might still be bridging legacy sensor protocols, and the aggregation point could expose these weaknesses.
- Gateway Compromise: Compromised gateways can lead to data exfiltration, device manipulation, or serve as a pivot point for attacks deeper into the network.
- Network Vulnerabilities:
- Weak Wi-Fi Security: Improperly configured Wi-Fi networks (e.g., WEP, weak WPA2) can be easily breached.
- Bluetooth Exploits: BLE, while energy-efficient, can have vulnerabilities if not implemented securely.
- LoRaWAN/Cellular Interception: Although generally more secure, these wireless technologies still require proper configuration and monitoring to prevent interception or denial-of-service attacks.
- Firmware/Software Vulnerabilities: Edge gateways are essentially small computers; their operating systems and applications can have exploitable flaws.
- Botnets/Denial of Service (DoS/DDoS) Attacks: Due to their internet exposure and potential for weaker security than enterprise servers, edge gateways can be targeted for botnet recruitment or direct DoS/DDoS attacks, disrupting operations.
- Credential Stuffing: Attackers use stolen credentials from other breaches to gain unauthorized access.
- Botnet Attacks: Compromised devices are used as part of a larger botnet for coordinated attacks.
Mitigation Strategies:
- Robust Gateway Hardening: system hardening in OT environments, which is highly applicable to edge gateways. This includes:
- Least Functionality: Disable all unnecessary services, ports, and features.
- Application Allowlisting: Only permit approved applications to run.
- Strong Authentication and Access Control: Implement multi-factor authentication (MFA) for gateway access and strict role-based access control (RBAC).
- Regular Patching and Updates: Keep gateway firmware and software up-to-date to address known vulnerabilities.
- Secure Configuration Management: Use golden images and automated configuration tools to ensure consistent and secure deployments.
- Network Segmentation: Isolate IIoT networks from enterprise IT networks and segment different IIoT functional zones to limit the lateral movement of attacks.
- Managed Wireless Connectivity: Implement enterprise-grade Wi-Fi with strong encryption (WPA3 where available), and properly secure Bluetooth and LoRaWAN deployments. For cellular connectivity, leverage secure APNs and VPNs.
- Intrusion Detection/Prevention Systems (IDS/IPS): Deploy IDS/IPS at the network edge to detect and block malicious traffic targeting gateways.
- DDoS Protection: Implement solutions that can detect and mitigate DoS/DDoS attacks targeting IIoT infrastructure.
Layer 3: Middleware/Cloud Processing Layer – The Brains of the Operation
This layer represents the backend infrastructure where IIoT data is stored, processed, analyzed, and managed. It typically includes data storage and databases, cloud processing units, analytics engines, and security/authentication services. MQTT/HTTP brokers often facilitate communication within this layer and between gateways and the cloud.
Potential Vulnerabilities:
- Insecure Communication (Gateway-to-Cloud):
- Unencrypted Traffic: Data transfer between gateways and the cloud must be encrypted to prevent interception.
- Legacy Protocols: If legacy protocols are somehow extended to cloud communication without proper encapsulation, they introduce risk.
- Data Storage and Database Vulnerabilities:
- SQL Injection, NoSQL Injection: Common web application vulnerabilities can affect databases.
- Inadequate Access Controls: Weak authentication or authorization mechanisms for database access.
- Data at Rest Encryption: Lack of encryption for stored data makes it vulnerable if the storage medium is compromised.
- Cloud Processing Unit & Analytics Engine Vulnerabilities:
- Configuration Errors: Misconfigurations of cloud services are a leading cause of breaches.
- Unpatched Software: Vulnerabilities in the operating systems or applications running on cloud instances.
- Insecure APIs: APIs used for interacting with cloud services can be exploited if not properly secured. The 2021 Verkada breach, where attackers gained super-admin access due to poorly secured APIs, serves as a stark reminder.
- Security/Authentication Services Vulnerabilities:
- Weak Authentication (e.g., single factor): Passwords alone are often insufficient.
- Identity Theft: Compromised user credentials granting access to the entire system.
- Improper Session Management: Vulnerabilities in how user sessions are managed.
- Botnets/Denial of Service (DoS/DDoS) Attacks: The cloud infrastructure itself can be targeted to disrupt services.
- Credential Stuffing: Targeting cloud platform user accounts.
Mitigation Strategies:
- Cloud Security Best Practices: Adhere to cloud provider security recommendations and frameworks (e.g., NIST, CSA). Implement a shared responsibility model, understanding what the cloud provider secures and what remains the customer’s responsibility.
- Data Encryption: Encrypt data both in transit (using TLS/SSL for MQTT/HTTP brokers) and at rest (disk encryption for databases and storage).
- Strong API Security:
- API Authentication and Authorization: Implement robust API keys, OAuth tokens, and strict access policies.
- Input Validation: Sanitize all API inputs to prevent injection attacks.
- Rate Limiting: Protect APIs from brute-force and denial-of-service attempts.
- Regular API Audits: Continuously scan and test APIs for vulnerabilities.
- Database Security: Implement strong access controls, encryption, regular backups, and patch management for databases.
- Identity and Access Management (IAM): Centralize identity management, enforce multi-factor authentication (MFA) for all administrative and privileged access, and apply the principle of least privilege.
- Vulnerability Management: Regularly scan cloud applications and infrastructure for vulnerabilities and apply patches promptly.
- Logging and Monitoring: Implement comprehensive logging for all cloud activities and integrate with security information and event management (SIEM) systems for real-time threat detection.
Layer 4: Application & User Interface Layer – The Human Interaction Point
This top layer represents the applications and user interfaces (e.g., mobile apps, web dashboards, HMI screens) through which users interact with the IIoT system, issuing commands, monitoring operations, and analyzing data. API interactions also occur heavily at this layer.
Potential Vulnerabilities:
- Vulnerable Software: This encompasses any software directly interacting with users or providing application functionality.
- Web/App Vulnerabilities: Standard web application vulnerabilities like cross-site scripting (XSS), cross-site request forgery (CSRF), broken access control, and insecure deserialization.
- Insecure APIs: As highlighted in the Verkada breach, exposed and poorly secured APIs are a critical attack vector, allowing unauthorized access to sensitive data and systems.
- Poor Authentication Practices: Weak password policies, absence of MFA, or flawed authentication flows can allow attackers to compromise user accounts.
- Hardware Attacks (Specific to User Devices): While listed generally, issues like JTAG/USB debug ports, firmware extraction, and side-channel attacks on user devices (e.g., an engineering workstation used for HMI programming) are relevant here. These attacks can compromise the user’s interface to the IIoT system.
Mitigation Strategies:
- Secure Software Development Lifecycle (SSDLC): Integrate security into every stage of application development, from design to deployment and maintenance.
- Input Validation and Output Encoding: Prevent injection attacks and cross-site scripting.
- Strong Authentication and Authorization: Implement MFA for all users, enforce strong password policies, and utilize role-based access control (RBAC) to limit user privileges to only what is necessary.
- API Gateway and Management: Deploy API gateways to centralize API security, including authentication, authorization, rate limiting, and traffic monitoring.
- Regular Security Testing: Conduct frequent penetration testing, vulnerability scanning, and code reviews for all applications and APIs.
- Controlled Access to Engineering Workstations and HMI Devices: System hardening for HMIs and engineering workstations is paramount. This includes:
- Golden Images: Use standardized, hardened images for all workstations.
- MFA-backed Access: Access via jump hosts with MFA.
- Strict Toolchain Governance: Control and validate all software installed.
- Project Backup/Version Control: Securely manage all code and configurations.
- Logging: Monitor all programming actions.
- User Training and Awareness: Educate users about phishing, social engineering, and safe browsing practices.
Critical IIoT/Industrial Security Dimensions: Beyond the Layers
Beyond the four architectural layers, two critical dimensions underpin the entire IIoT security posture: Device Security and Network & Connectivity Security. These dimensions are not confined to a single layer but permeate the entire industrial ecosystem.
Critical Dimension 1: Device Security – Ensuring Hardware & Firmware Integrity from the Start
Device security focuses on the inherent trustworthiness of the physical devices themselves, from the lowest-level sensors to edge gateways and beyond. It involves protecting both the hardware and the embedded software (firmware).
Why it’s Critical: If a device’s hardware or firmware is compromised at any point, the integrity of all data it produces and all commands it executes becomes questionable. This can lead to system-wide failures and facilitate deeper intrusions. The 2025 coordinated cyberattack on Polish energy facilities, exploiting default credentials on industrial edge devices and RTUs to upload malicious firmware, vividly illustrates this.
Key Aspects of Device Security:
- Secure Boot: Ensure that only cryptographically signed and trusted firmware can be loaded and executed on a device. This prevents unauthorized or malicious code from running at startup.
- Firmware Integrity and Updates:
- Code Signing: All firmware updates must be digitally signed by a trusted authority to verify their authenticity and prevent tampering.
- Over-the-Air (OTA) Updates: Implement secure OTA update mechanisms that encrypt update packages, authenticate the source, and ensure integrity checks.
- Rollback Protection: Prevent attackers from forcing a device to revert to an older, vulnerable firmware version.
- Hardware Tamper Detection: Integrate physical security measures to detect and alert on unauthorized access to device internals.
- JTAG/USB Debug Ports: Secure or disable these debugging interfaces in production environments, as they can be used for firmware extraction or direct memory access.
- Side-Channel Attacks: Defend against techniques that exploit physical characteristics (e.g., power consumption, electromagnetic emissions) to extract cryptographic keys or other sensitive information.
- Hardware Root of Trust (HRoT): Utilize hardware-based security modules (e.g., TPMs, hardware security modules HSMs) to establish a trusted computing base, store cryptographic keys securely, and perform secure boot validations.
- Default Credential Elimination: Ensure devices are shipped without default passwords or that they enforce a mandatory password change on first boot.
Critical Dimension 2: Network & Connectivity Security – Protecting Communications & Protocols
This dimension focuses on securing the pathways through which IIoT devices communicate, encompassing both wired and wireless connections, as well as the protocols used for data exchange.
Why it’s Critical: The integrity and confidentiality of data in transit are paramount. If network communications are compromised, sensitive operational data can be intercepted, commands can be manipulated, and attackers can gain unauthorized access to the IIoT ecosystem. The JLR cyberattack (Sept 2025), which forced Jaguar Land Rover to shut down global IT and manufacturing systems due to inadequate network segmentation and visibility, underscores the impact of network security failures.
Key Aspects of Network & Connectivity Security:
- Network Segmentation and Micro-segmentation:
- Logical Isolation: Divide the IIoT network into smaller, isolated zones (e.g., by function, criticality, or device type). This limits the blast radius of an attack.
- Demilitarized Zones (DMZs): Use DMZs to create buffer zones between different network segments and external networks.
- Zero Trust Architecture: Assume no user or device is implicitly trusted, regardless of its location within the network.
- Secure Communication Protocols:
- Encryption in Transit: Enforce TLS/SSL for all sensitive communications, including MQTT, HTTP, and API calls.
- VPNs: Utilize Virtual Private Networks (VPNs) for secure remote access and encrypted tunnels between network segments.
- IPsec: Implement IPsec for secure network-layer communication where appropriate.
- Intrusion Detection and Prevention Systems (IDS/IPS): Deploy network-based IDS/IPS solutions to monitor traffic for malicious activity and automatically block threats.
- Firewalls: Implement and properly configure industrial firewalls to control traffic flow between network segments and the internet.
- Protocol Anomaly Detection: Monitor network traffic for deviations from normal behavior, which can indicate an attack on legacy or proprietary protocols.
- Wireless Security:
- Strong Encryption: Use WPA3 (or WPA2-Enterprise) for Wi-Fi networks with strong authentication.
- MAC Filtering: Restrict access to wireless networks based on device MAC addresses (though this is not a primary security control).
- Guest Networks: Isolate guest wireless networks from the IIoT infrastructure.
- Visibility and Monitoring: Implement tools for real-time visibility into network traffic, connected devices, and communication patterns. Regularly analyze network logs.
The dynamic nature of threats necessitates continuous adaptation. Consider solutions like D3O-IIoT, a deep reinforcement learning model that dynamically coordinates deception techniques (honeypots, moving target defense) based on real-time threat monitoring to enhance industrial IoT security [nature.com]. Such proactive, learning-based approaches offer a significant advantage over static defense mechanisms.
The Overarching Governance Model: Strategy and Compliance
A robust governance model is the bedrock of enduring IIoT security. It defines the policies, processes, and responsibilities necessary to manage security risks across the entire lifecycle of IIoT deployment. This overarching framework ensures that security is not an afterthought but an integral part of operations.
1. Secure Identity
Managing identities in an IIoT environment extends beyond human users to include devices, applications, and services. A secure identity framework ensures that only authenticated and authorized entities can access resources.
- Device Identity: Each IIoT device must have a unique and verifiable identity. This can be achieved through certificates issued by a Public Key Infrastructure (PKI) or hardware-based identifiers.
- Strong Authentication: Implement multi-factor authentication (MFA) for all human users accessing IIoT systems, especially those with administrative privileges. For devices, rely on certificates or cryptographic keys for mutual authentication.
- Centralized Identity and Access Management (IAM): Consolidate user and device identities into a central system to manage access policies consistently across the IIoT ecosystem.
- Role-Based Access Control (RBAC): Grant users and devices only the minimum level of access required to perform their functions, adhering to the principle of least privilege.
- Lifecycle Management of Identities: Establish processes for provisioning, de-provisioning, and revoking identities for both users and devices.
2. Secure Development
Security must be embedded into the development process of all IIoT components, from firmware and embedded software to cloud applications and user interfaces.
- Security by Design: Integrate security considerations from the initial design phase of devices, applications, and cloud architecture.
- Secure Coding Practices: Train developers in secure coding techniques and enforce the use of static and dynamic application security testing (SAST/DAST) tools.
- Threat Modeling: Conduct threat modeling early in the development cycle to identify potential attack vectors and design appropriate controls.
- Vulnerability Management in Development: Proactively identify and remediate vulnerabilities in code, third-party libraries, and open-source components.
- Supply Chain Security: Vet all hardware and software components from suppliers to ensure their security posture.
3. Threat Monitoring
Continuous monitoring is essential to detect, analyze, and respond to security incidents in real-time. This involves collecting and analyzing security logs and events from across the IIoT environment.
- Centralized Logging: Aggregate logs from devices, gateways, cloud services, and applications into a Security Information and Event Management (SIEM) system.
- Real-time Analytics: Utilize advanced analytics, including machine learning and behavioral anomaly detection, to identify suspicious activities that might indicate an attack.
- Asset Inventory: Maintain an up-to-date and accurate inventory of all IIoT devices, their configurations, and their network connections. You cannot protect what you cannot see [deviceauthority.com].
- Vulnerability Scanning: Regularly scan IIoT devices, networks, and applications for known vulnerabilities.
- IoT/OT Specific Intelligence: Integrate threat intelligence feeds that focus on industrial control systems and IIoT attack patterns.
4. Incident Response
Having a well-defined incident response plan is crucial for effectively managing and recovering from cyberattacks.
- Preparation: Develop an incident response plan, establish a dedicated incident response team, and conduct regular tabletop exercises to test the plan.
- Detection and Analysis: Define clear triggers and procedures for detecting security incidents and thoroughly analyzing their scope and impact.
- Containment, Eradication, and Recovery: Implement strategies to limit the damage of an attack, remove the threat, and restore affected systems to normal operation.
- Post-Incident Analysis: Conduct a thorough post-mortem analysis to identify root causes, learn from the incident, and improve security controls.
- Communication Plan: Establish clear communication protocols for internal and external stakeholders during an incident.
5. Compliance
Adhering to relevant industry standards, regulations, and best practices is vital for maintaining a strong security posture and avoiding legal penalties.
- Regulatory Adherence: Comply with industry-specific regulations (e.g., NERC CIP for energy, GDPR for data privacy) and general cybersecurity frameworks (e.g., NIST Cybersecurity Framework, ISO 27001).
- Internal Policies and Procedures: Develop and enforce internal security policies that reflect industry best practices and regulatory requirements.
- Auditing and Reporting: Regularly audit IIoT systems and processes against compliance mandates and generate reports for stakeholders.
- Data Privacy: Implement measures to protect sensitive data collected by IIoT devices, ensuring compliance with data privacy regulations. Solutions integrating blockchain for data integrity assurance and access control can be particularly valuable [nature.com].
The Future of IIoT Security: AI, Machine Learning, and Deception
The threat landscape for IIoT is constantly evolving, necessitating equally dynamic security approaches. Traditional rule-based defenses are often too static to cope with sophisticated, adaptive attacks. Emerging technologies like artificial intelligence (AI) and machine learning (ML), particularly in areas like deep reinforcement learning and deception orchestration, represent the next frontier in IIoT security.
Dynamic Deception Orchestration
Advanced threats can bypass conventional security measures. Dynamic deception techniques, such as honeypots and moving target defense, can misdirect attackers, gather intelligence on their methods, and provide valuable time for defense systems to react. Deep reinforcement learning models, like D3O-IIoT, can analyze real-time threat data to dynamically deploy these deception techniques, maximizing their effectiveness while minimizing false positives and resource overhead [nature.com]. This involves a sophisticated balance of attack mitigation, deception engagement, and resource optimization.
AI and ML for Anomaly Detection and Predictive Security
AI and ML algorithms are increasingly being used to analyze vast quantities of IIoT data for anomalies that could indicate an attack. This includes:
- Behavioral Baselines: Establishing normal operational baselines for device behavior, network traffic, and data patterns.
- Anomaly Detection: Identifying deviations from these baselines that may signal a compromise or an impending attack.
- Predictive Security: Using ML to anticipate potential attack vectors and vulnerabilities based on historical data and current threat intelligence.
Blockchain for Enhanced Integrity and Trust
Blockchain technology offers a decentralized and immutable ledger that can enhance data integrity, secure communication, and provide transparent audit trails within IIoT ecosystems. Its application in workload analysis and intrusion detection frameworks can significantly bolster security in fog computing environments.
- Data Integrity: Blockchain can ensure the integrity of sensor data, providing tamper-proof records for critical operational parameters.
- Secure Access Control: Decentralized identity management and access control mechanisms powered by blockchain can enhance the security of IIoT device interactions.
- Supply Chain Transparency: Blockchain can provide verifiable provenance for IIoT devices and components, mitigating risks associated with the supply chain.
Conclusion
The promise of intelligent operations through IIoT is immense, but its realization hinges on the implementation of a robust and proactive security governance model. The convergence of IT and OT, the distinct vulnerabilities of IIoT devices, and the ever-evolving threat landscape demand a multi-layered approach that addresses security from the ground up. By meticulously securing each layer of the IIoT architecture – from data acquisition to cloud processing and user interfaces – and by adopting a comprehensive governance model encompassing secure identity, development, threat monitoring, incident response, and compliance, organizations can build resilient and trustworthy industrial ecosystems.
The future of IIoT security will increasingly rely on intelligent, adaptive solutions driven by AI, machine learning, and innovative approaches like dynamic deception and blockchain. Embracing these advanced technologies, coupled with a commitment to continuous improvement and adherence to best practices, will be paramount in transforming factories into truly intelligent and secure operations. Preventing incidents like the Polish energy facility attack or the JLR and Verkada breaches requires constant vigilance and a strategic investment in cybersecurity at every level.
Unlock the Full Potential of Your IIoT Implementation with IoT Worlds
Are you ready to fortify your industrial operations against the escalating cyber threats of the IIoT era? IoT Worlds specializes in delivering comprehensive IIoT security solutions tailored to your unique industrial environment. From architecting secure device-to-cloud communications to implementing robust governance models and leveraging cutting-edge AI-driven defenses, our experts are here to guide you.
Don’t let security vulnerabilities hinder your path to operational excellence. Protect your critical infrastructure, safeguard your data, and ensure the continuity of your intelligent operations.
Contact us today to discuss your IIoT security needs and discover how we can help you build a resilient and secure industrial future.
Email us at info@iotworlds.com to take the first step towards an uncompromised IIoT journey.