The Evolving Landscape of Operational Technology Security
In an increasingly interconnected world, Operation Technology (OT) environments, which control critical industrial processes, have become prime battlegrounds in the cyber realm. Historically, the focus of cybersecurity efforts has leaned heavily on Information Technology (IT) networks, assuming OT was a separate, isolated domain. This assumption, however, is a dangerous relic of a bygone era. Today, adversaries are not merely looking to disrupt; they are seeking to control, manipulate, and weaponize the very infrastructure that underpins our society. This shift demands a radical re-evaluation of how we perceive, protect, and defend OT.
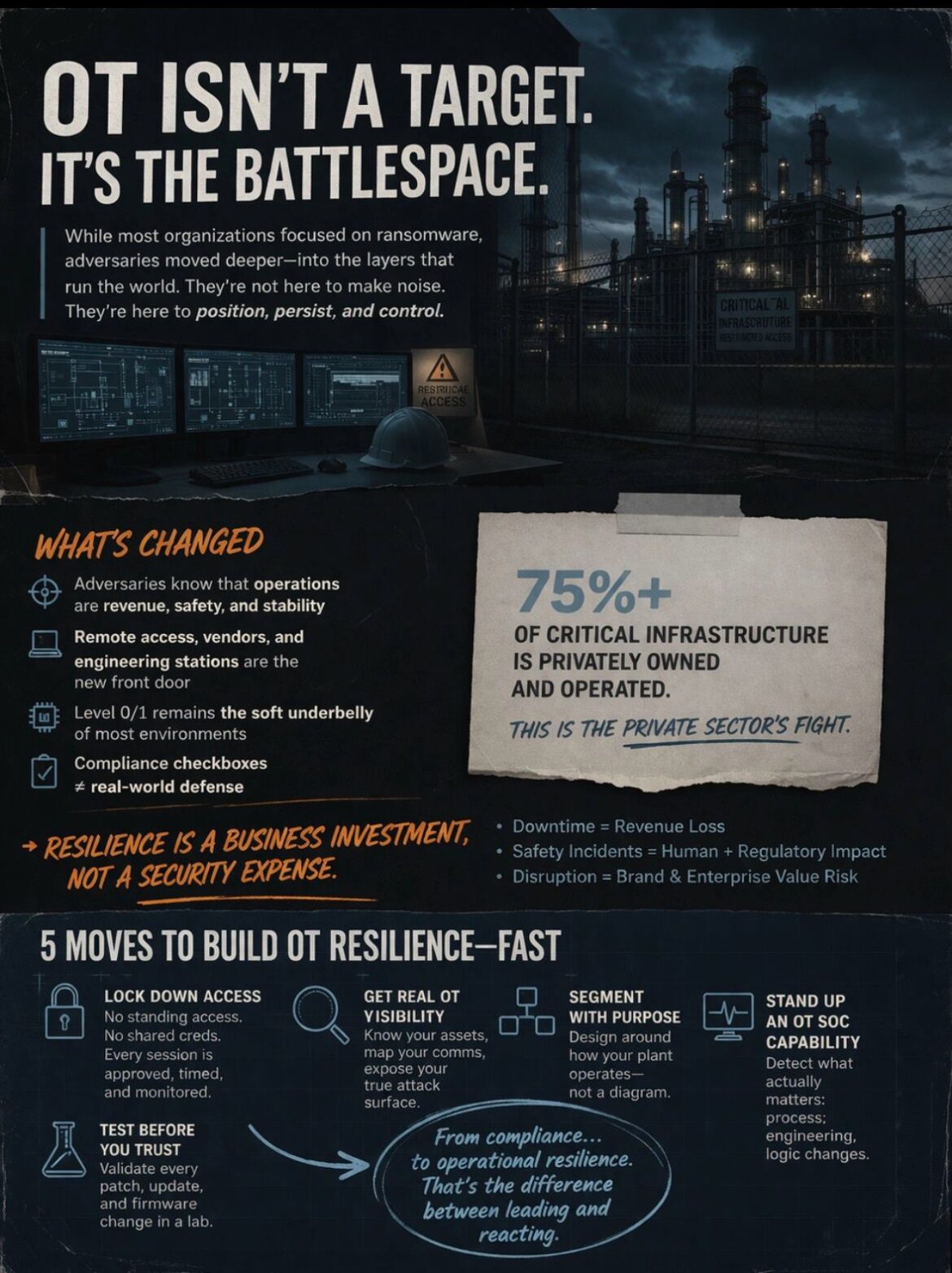
The concept of OT as a “target set” is fundamentally flawed. It implies a static objective, a fixed point of attack. The reality is far more dynamic. OT is the battlespace—an active, fluid environment where strategic advantage is gained not through brute force, but through subtle positioning, persistent access, and quiet manipulation. This ongoing conflict is not confined to the digital sphere; its consequences reverberate through physical infrastructure, economic stability, and national security.
From Ransomware to Strategic Control: A Paradigm Shift in Adversary Tactics
For years, the most prominent cyber threat to businesses, both IT and a limited extent OT, was ransomware. These “smash-and-grab” attacks aimed for immediate financial gain through data encryption and extortion. While ransomware remains a significant concern, a more insidious and sophisticated form of cyber warfare is emerging in the OT domain, particularly against critical infrastructure.
Adversaries are no longer content with merely disrupting operations for a quick payoff. Their objectives have evolved to encompass strategic control. This means they are investing in long-term campaigns designed to establish persistent access within OT environments, learn operational intricacies, and ultimately gain the ability to manipulate industrial control systems (ICS) at will. This shift from transient disruption to enduring control represents a profound escalation in the nature of the threat.
The motivations behind this new strategic approach are multifaceted. Nation-states may seek to pre-position themselves for future geopolitical conflicts, enabling them to degrade an adversary’s industrial capacity or exert leverage during diplomatic negotiations. Organized crime groups might target OT for espionage, intellectual property theft, or to establish a foundation for more sophisticated extortion schemes that go beyond simple data encryption. Regardless of the specific motivation, the common thread is a desire for comprehensive and sustained control over critical operational processes.
The Private Sector’s Unavoidable Frontline
A crucial and often overlooked aspect of this evolving battlespace is the ownership and operation of critical infrastructure. More than 75% of critical infrastructure — encompassing sectors like energy, water, transportation, and manufacturing — is owned and operated by the private sector. This staggering statistic fundamentally redefines the responsibility for OT security. It unequivocally declares that the defense of these vital systems is not solely the government’s burden; it is unequivocally the private sector’s fight.
This reality presents both challenges and opportunities. On one hand, many private companies may not be adequately prepared for the sophisticated and persistent nature of these advanced threats. They may lack the resources, expertise, or even the regulatory imperative to invest sufficiently in robust OT security measures. On the other hand, the private sector’s agility, innovation, and direct understanding of their operational environments can be powerful assets in building effective defenses.
The notion that governments will swoop in to defend every critical infrastructure component is a dangerous illusion. While government agencies play a vital role in intelligence gathering, threat sharing, and policy development, the fundamental responsibility for securing the machines that power, feed, and sustain nations rests squarely on the shoulders of the private entities that own and operate them. This calls for a profound cultural shift, moving away from a reliance on external protection to an internalized commitment to proactive, resilient OT security.
What Has Changed: Understanding the Evolved Threat Landscape
The operational technology security landscape has shifted dramatically, driven by adversaries who possess a deeper understanding of industrial processes and leverage new pathways into critical environments. This evolution necessitates a fundamental re-evaluation of traditional security approaches and an urgent adoption of strategies designed to counter these sophisticated threats.
Adversaries’ Deep Understanding of Operations
One of the most significant changes is the adversaries’ heightened understanding of how OT operations equate to tangible business value. They recognize that an organization’s revenue, safety, and national stability are intrinsically linked to the uninterrupted and correct functioning of its operational technology. This insight moves beyond basic IT disruption and targets the very core of industrial output and societal function.
Rather than merely attempting to shut down systems, adversaries are now focused on manipulating them. They understand that by quietly altering a control parameter, delaying a process, or subtly corrupting sensor data, they can achieve far more devastating and long-lasting effects than a simple denial-of-service attack. This deep operational understanding allows them to craft attacks that are highly specific, difficult to detect, and capable of causing significant economic damage, environmental harm, or even loss of life. Their objective is not just to break things, but to control them.
Remote Access, Vendor Pathways, and Engineering Workstations: The New Front Doors
The traditional isolation of OT networks has become a myth. The drive for efficiency, remote diagnostics, and integrated supply chains has opened up numerous “front doors” into operational environments. Remote access solutions, essential for vendors providing maintenance and support, and engineering workstations, crucial for programming and configuring control systems, have paradoxically become major vectors for attack.
These entry points are often less rigorously secured than corporate IT networks. Shared credentials, lax access controls, and unmonitored connections create significant vulnerabilities. Adversaries are actively targeting these pathways because they offer direct access to the most sensitive parts of the OT network, bypassing layers of IT security that may be in place. Once inside, they can move laterally, establish persistence, and begin their quiet manipulation of control environments. The convenience these access methods offer must be weighed against the profound security risks they introduce, demanding a more robust and granular approach to managing them.
Level 0/1: The Under-protected and Over-trusted Underbelly
Within the Purdue Model of industrial control system architectures, Levels 0 and 1 represent the foundational layers: the sensors, actuators, Remote Terminal Units (RTUs), and Intelligent Electronic Devices (IEDs) that directly interact with physical processes. These are the “nuts and bolts” of operational technology, often considered the most critical components. Ironically, they remain the most under-protected and over-trusted elements within many OT environments.
The belief that these low-level devices are inherently secure due to their perceived isolation or simplicity is a dangerous misconception. Many are designed for reliability and longevity, not robust cybersecurity. They often lack advanced security features, are difficult to patch, and may communicate using unencrypted legacy protocols. Adversaries, recognizing this vulnerability, are increasingly targeting these devices. By compromising Level 0/1, they can directly manipulate physical processes, generate false readings, or even trigger dangerous conditions. The over-trust placed in these foundational layers provides a fertile ground for sophisticated attacks, circumventing higher-level network defenses that might be present.
“Compliance-Driven Security” Lagging Real-World Threat Behavior
A significant challenge in the OT security domain is the reliance on “compliance-driven security.” Many organizations approach cybersecurity as a checklist exercise, aiming to meet minimum regulatory requirements rather than proactively addressing the dynamic and evolving threat landscape. While compliance frameworks provide a baseline for security practices, they often lag behind real-world adversary behavior.
Adversaries are not bound by compliance standards. They constantly innovate, identifying new vulnerabilities and developing novel attack techniques. If an organization’s security strategy is solely focused on ticking compliance boxes, it will inevitably find itself playing catch-up, reacting to threats rather than anticipating and mitigating them. This reactive posture is particularly dangerous in OT, where the consequences of a successful attack can be catastrophic. Moving beyond mere compliance to a robust, threat-informed security strategy is not just advisable; it is imperative for survival in the current battlespace.
What Needs to Happen: Building Proactive OT Resilience
The gravity of the current threat landscape demands immediate and decisive action. Organizations can no longer afford to defer critical OT security investments and strategic shifts. Building resilience in operational technology environments requires a multi-faceted approach that moves beyond traditional IT security paradigms and specifically addresses the unique characteristics and risks inherent in industrial control systems.
Lock Down Access Like It Matters
Access control in OT environments must be elevated to a paramount concern, reflecting its critical importance. The days of standing remote access, shared credentials, and unsupervised connections are over. These practices represent unacceptable vulnerabilities that adversaries are actively exploiting.
A robust access control strategy must incorporate the principle of least privilege, ensuring that individuals and systems only have the access necessary to perform their legitimate functions. This translates to:
- No more standing remote access: Remote connections to OT networks should only be established when absolutely necessary, for defined periods, and under strict monitoring.
- No more shared credentials: Unique, strong credentials must be enforced for every individual and system accessing OT resources. Multi-factor authentication (MFA) must be implemented for all remote access and privileged user accounts.
- Time-bound, monitored, approved sessions only: All remote and local privileged access sessions must be explicitly approved, time-limited, and subject to continuous monitoring. This includes recording session activities, reviewable by security teams, to ensure accountability and detect anomalies.
- Logging critical actions: Any action that could alter the operational state of equipment—such as pushing logic changes, updating firmware, or modifying setpoints—must be logged with the same rigor and auditability as a financial transaction. This provides an indisputable record of who did what, when, and where, essential for forensic analysis and accountability.
Implementing these measures requires robust identity and access management (IAM) solutions tailored for OT, along with a strong emphasis on operational procedures and employee training. It’s about instilling a culture where access is treated as a highly valuable and protected commodity, not a convenience.
Get Real Visibility into OT—Not Assumptions
You cannot defend what you don’t fully understand or comprehensively enumerate. Many organizations still rely on outdated spreadsheets, anecdotal knowledge, or vendor diagrams for their OT asset inventory and network topology. This reliance on assumptions creates critical blind spots that adversaries can easily exploit. Achieving real visibility into OT environments is the foundational step for effective security.
This requires moving beyond passive network discovery to active, comprehensive mapping of the entire OT landscape:
- Accurate Asset Inventory: A complete and continuously updated inventory of all devices, controllers, sensors, actuators, and software configurations within the OT network is essential. This includes details such as make, model, firmware version, operating system, patch level, and ownership. This inventory should be automated and continuously reconciled to reflect changes.
- Communications Mapping: Understanding how devices communicate with each other, which protocols are used, and what data flows across the network is critical. This mapping reveals interdependencies, potential attack paths, and abnormal communication patterns. It helps in identifying unauthorized connections or deviations from normal operational behavior.
- Threat Surface Enumeration: Based on the asset inventory and communications mapping, organizations must realistically assess their threat surface. This involves identifying potential vulnerabilities in devices, configurations, and network architecture, and understanding how these could be exploited by various threat actors. This goes beyond generic vulnerability scans and considers the specific operational context and criticality of each component.
The goal is to establish an “operational truth”—a real-time, accurate representation of the OT environment that serves as the single source of truth for all security and operational decisions. This visibility is enabled by specialized OT security tools that can safely interact with industrial protocols and devices to gather the necessary data without disrupting operations.
Segment with Purpose, Not Theory
Network segmentation is a well-established security principle, but in OT, it often falls short due to a theoretical rather than practical application. The Purdue Enterprise Reference Architecture is an excellent conceptual model, but it is not a control blueprint. Simply drawing lines on a diagram based on the Purdue model without understanding the actual plant operations can be ineffective or even detrimental.
Effective OT segmentation must be purpose-built, designed to reflect the actual operational realities of the industrial process:
- Micro-segmentation: Instead of broad network zones, organizations should aim for micro-segmentation, creating smaller, isolated segments based on specific functions, criticality, and communication requirements. This limits the lateral movement of adversaries once they gain initial access, containing the impact of a breach.
- Reflect Plant Operations: Segmentation boundaries should align with the actual P&ID (Piping and Instrumentation Diagram) and process flow, rather than arbitrary IT network divisions. For example, separating different production lines, safety instrumented systems (SIS), or critical control elements ensures that a compromise in one area does not automatically propagate to another.
- Control over Communication Flows: Beyond network separation, segmentation must involve strict control over allowed communication flows between segments. This means implementing industrial firewalls and access control lists that only permit explicitly authorized protocols, ports, and source/destination IP addresses, effectively white-listing legitimate operational traffic.
- Continuous Validation: Segmentation schemes are not static. As plant operations evolve, so too must the segmentation strategy. Regular reviews and validation are necessary to ensure that the segmentation accurately reflects current operational needs and remains effective against evolving threats.
The purpose of segmentation in OT is to minimize blast radius, enforce least privilege communication, and create choke points where security controls can be effectively applied and monitored. It’s about designing a resilient architecture that can withstand partial compromises without leading to catastrophic failure.
Build an OT SOC Capability (Even If It’s Small)
For too long, organizations have attempted to shoehorn OT security monitoring into existing IT Security Operations Centers (SOCs). This approach is fundamentally flawed because the context, protocols, and threats in OT are distinctly different from IT. What constitutes “normal” behavior in an IT network is often irrelevant or even misleading in an OT environment. Building an OT SOC capability, even if initially small or augmenting an existing team, is crucial for effective threat detection and response.
An OT SOC must be purpose-built to understand and detect anomalies specific to operational technology:
- Process Anomaly Detection: This is paramount. An OT SOC needs to detect deviations in process variables (e.g., temperature, pressure, flow rates) that are outside normal operating parameters or sudden changes in setpoints. These anomalies could indicate malicious manipulation even if no traditional cyber alerts are triggered.
- Engineering Actions Monitoring: Unauthorized or abnormal engineering actions are a significant indicator of compromise. This includes changes to ladder logic, firmware updates initiated outside of maintenance windows, unusual program downloads to PLCs, or modifications to HMI configurations. These actions often bypass traditional network security and require deep OT protocol awareness.
- Unauthorized Changes in Control Logic: The integrity of control logic is critical. An OT SOC must have the capability to monitor for, detect, and alert on any unauthorized changes to PLC programs, RTU configurations, or safety controller logic. This requires baselining normal configurations and continuously comparing them against operational reality.
- Contextualized Alerts: Rather than generating a flood of generic alerts, an OT SOC must provide contextualized insights. Alerts should include operational details, such as the specific asset involved, its function, the process affected, and the potential impact on safety or production. This enables faster, more informed decision-making.
This capability usually involves specialized OT security platforms that integrate with industrial control systems, gather contextual data, and apply OT-specific analytics and threat intelligence. It requires a team with a blend of cybersecurity and operational expertise, understanding both packets and process.
Test Before You Trust
The mantra in OT environments has always been “if it ain’t broke, don’t fix it” due to the high costs and risks associated with downtime. This conservative approach, while understandable, has often led to a reluctance to patch, update, or even thoroughly test new components. In today’s threat environment, this hesitancy has become a critical vulnerability. The principle of “test before you trust” is immutable for maintaining OT security and operational integrity.
Every change, update, or new component introduced into the OT environment must undergo rigorous validation in a controlled, isolated lab environment before deployment:
- Firmware and Patch Validation: All firmware upgrades and security patches must be tested in a representative testbed that mirrors the production environment as closely as possible. This ensures compatibility, stability, and absence of adverse effects on interconnected systems and processes.
- Vendor Update Verification: Software updates, configuration changes, and new components from vendors must be thoroughly vetted. This includes not just functional testing but also security analysis to identify potential vulnerabilities introduced by the changes.
- DAST/SAST Mindset for OT: Applying a Development Application Security Testing (DAST) and Static Application Security Testing (SAST) mindset to OT means systematically analyzing the code and runtime behavior of industrial applications and control logic for security flaws. While challenging due to proprietary nature, this approach can uncover vulnerabilities before they are exploited.
- Uptime is Non-Negotiable, So Validation Has to Be Disciplined: The critical nature of OT operations means that downtime is not an option. This makes disciplined, systematic validation even more crucial. A well-designed test environment and a standardized validation process minimize the risk of introducing instability into the production environment due to security updates or new deployments.
Investing in a dedicated OT test lab, or partnering with organizations that provide such facilities, is no longer a luxury but a fundamental requirement. This disciplined approach ensures that security enhancements do not inadvertently compromise operational stability, fostering trust in the security posture.
The Business Reality: Resilience as an Investment
Protecting Operational Technology goes far beyond technical implementations; it is fundamentally a business imperative. While security professionals often focus on the “bits and bytes,” business leaders need to understand the profound financial, regulatory, and reputational implications of OT insecurity. Framing OT security as a capital expenditure for tools misses the entire point; it is a strategic investment in resilience, governance, and the very sustainability of the enterprise.
This Isn’t About Tools; It’s About Culture and Governance
The conversation about OT security often devolves into debates about which security products to buy. While tools are necessary enablers, they are not the solution in themselves. Throwing technology at the problem without addressing underlying cultural and governance issues is akin to buying the best locks for a house with an open front door and no one watching.
Effective OT security is rooted in a robust culture of security, driven from the top down. This means:
- Leadership Commitment: The board and executive leadership must champion OT security, allocate adequate resources, and integrate it into overall business strategy.
- Cross-Functional Collaboration: Breaking down silos between IT, OT, engineering, and business units is critical. Security decisions should involve all stakeholders who understand the operational implications.
- Clear Policies and Procedures: Comprehensive, well-documented policies and procedures for security operations, incident response, access management, and change control are essential. These must be regularly reviewed and updated.
- Training and Awareness: All personnel, from plant operators to executives, must receive regular training on OT security best practices and their role in maintaining a secure environment.
- Governance Framework: Establishing a clear governance framework that defines roles, responsibilities, accountability, and decision-making processes for OT security ensures consistent application and oversight.
Tools are components of a security program; culture and governance are the architecture that makes the program effective and sustainable. Without a strong foundation of culture and governance, even the most advanced tools will fail to deliver true resilience.
The True Costs of OT Insecurity
Business leaders often require a clear articulation of risk in financial terms. The consequences of an OT security incident are not abstract; they translate directly into tangible business losses and long-term damages that far outweigh the investment in proactive security.
- Downtime = Immediate Revenue Loss: Unlike IT system outages which might be inconvenient, OT downtime often means a complete halt in production. For an industrial facility, every hour of stopped operations can translate into millions of dollars in lost revenue, missed targets, and unfulfilled orders. This direct impact on the bottom line is often the most compelling argument for investing in OT resilience.
- Safety Incidents = Regulatory + Human Impact: A compromised OT system can lead to severe safety incidents, ranging from equipment malfunction to explosions, chemical spills, or widespread power outages. Such incidents result in significant human impact – injuries or fatalities – which carries immense ethical responsibility and attracts severe regulatory scrutiny. Fines, legal liabilities, and potential criminal charges can cripple an organization.
- Operational Disruption = Brand + Enterprise Value Hit: Beyond immediate financial losses and safety concerns, sustained operational disruption severely damages a company’s brand reputation and enterprise value. Loss of public trust, erosion of customer confidence, and negative media coverage can have long-lasting effects, impacting stock prices, investor confidence, and market share. The ability to guarantee reliable, safe operations is a cornerstone of brand integrity in critical infrastructure sectors.
Resilience is a Business Investment, Not a Security Expense
Shifting the perception of OT security from a cost center to a critical business investment is paramount. When framed correctly, it becomes clear that investments in OT resilience directly contribute to the core business objectives:
- Production Uptime: Robust OT security measures minimize the risk of disruptions, ensuring continuous operational availability and maximizing output. This directly impacts profitability and market competitiveness.
- Safety Assurance: By protecting control systems from malicious manipulation or accidental errors, OT security directly contributes to the safety of personnel, the community, and the environment. This reduces regulatory exposure and enhances social license to operate.
- Regulatory Exposure: Proactive OT security postures demonstrably reduce the risk of non-compliance with industry-specific regulations and governmental mandates. This avoids costly fines, legal battles, and reputational damage.
- Insurance Posture: Organizations with mature OT security programs are often viewed more favorably by insurance providers, potentially leading to lower premiums or more comprehensive coverage for cyber risks. A strong security posture demonstrates due diligence and proactive risk management.
By tying OT security directly to these core business metrics, the conversation moves from a “cyber problem” to a board-level priority. It becomes clear that investing in resilience is not merely about avoiding negatives, but about actively protecting and enhancing the enterprise’s long-term value and operational sustainability. It is an investment in the future, safeguarding critical assets and ensuring the continued delivery of essential services.
The Bottom Line: From Compliance to Operational Resilience
We are currently operating in a threat environment where the calculus of attack has fundamentally changed. Adversaries, particularly those targeting operational technology, no longer need to destroy systems to achieve their objectives. Their aim is more subtle, more pervasive: they simply need to control. This paradigm shift demands an equally profound change in how critical infrastructure operators approach security.
The traditional mindset of “Are we compliant?” is no longer sufficient. While compliance provides a foundational baseline, it often represents the minimum standard, a snapshot in time. In a dynamic and hostile battlespace, minimum standards are quickly surpassed by adaptive adversaries. The question that truly matters, the one that defines an organization’s preparedness and fortitude, is: “Can we operate through disruption?”
This question encapsulates the essence of resilience. It acknowledges that perfect prevention is an unattainable myth, especially in complex OT environments. Instead, it focuses on the ability to withstand, adapt to, and recover from cyber incidents, minimizing impact and ensuring continuity of essential operations. Resilience is not merely about preventing breaches; it is about building systems and processes that can absorb shocks, maintain critical functions, and rapidly restore full capabilities when an incident occurs.
Moving from a compliance-driven approach to one focused on operational resilience requires:
- Proactive Threat Intelligence: Understanding the evolving tactics, techniques, and procedures (TTPs) of relevant threat actors, and proactively building defenses against them.
- Continuous Monitoring and Detection: Implementing robust systems to detect subtle anomalies, unauthorized changes, and suspicious behaviors within OT networks, not just generic IT alerts.
- Robust Incident Response: Developing and regularly exercising comprehensive incident response plans specifically tailored for OT, including containment, eradication, recovery, and post-incident analysis.
- Secure by Design: Integrating security into the entire lifecycle of OT systems, from procurement and design to deployment and decommissioning.
- Redundancy and Failover: Designing systems with inherent redundancy and failover capabilities to ensure that a compromise in one component does not lead to complete system failure.
- Cultural Shift: Fostering a pervasive culture where every individual understands their role in maintaining operational resilience and is empowered to report potential issues.
This shift from a reactive, compliance-focused posture to a proactive, resilience-driven strategy is the fundamental difference between organizations that will lead in this new threat era and those that will merely react, often to their detriment. It is the difference between safeguarding our critical infrastructure and leaving it vulnerable to the quiet manipulations of those who seek control.
The stakes could not be higher. The integrity of our economies, the safety of our communities, and the stability of our nations hinge on the ability of critical infrastructure operators to embrace this strategic imperative. It’s time to stop running away from OT security challenges and instead embrace the role of defenders in this critical battlespace.
Is your company ready to secure the operational technology that underpins your success?
At IoT Worlds, we understand the unique complexities and critical importance of OT security. We specialize in helping organizations like yours navigate the evolving threat landscape, build robust resilience, and implement strategies that move beyond mere compliance to true operational integrity. Don’t leave your critical infrastructure vulnerable.
Contact us today to discuss how we can help you defend your OT environment and ensure your business can operate through any disruption.
Email us at info@iotworlds.com and let’s start building a more resilient future, together.