In today’s hyper-connected world, cybersecurity is no longer a niche IT concern; it’s a fundamental business imperative. Gone are the days when a simple firewall and antivirus software were sufficient to protect an organization’s digital assets. The threat landscape has evolved dramatically, with cybercriminals employing increasingly sophisticated tactics, often powered by artificial intelligence, to exploit vulnerabilities. To combat these relentless and ever-evolving threats, organizations must adopt a robust, multi-layered defense strategy. This approach, often referred to as “defense-in-depth,” emphasizes the deployment of various security controls that work in concert to anticipate, detect, and respond to threats effectively.
This comprehensive guide will explore the six core layers of cybersecurity controls that every organization, regardless of size or industry, must understand and implement. These controls are not mutually exclusive; rather, they are designed to complement each other, creating a formidable barrier against cyberattacks and ensuring business continuity.
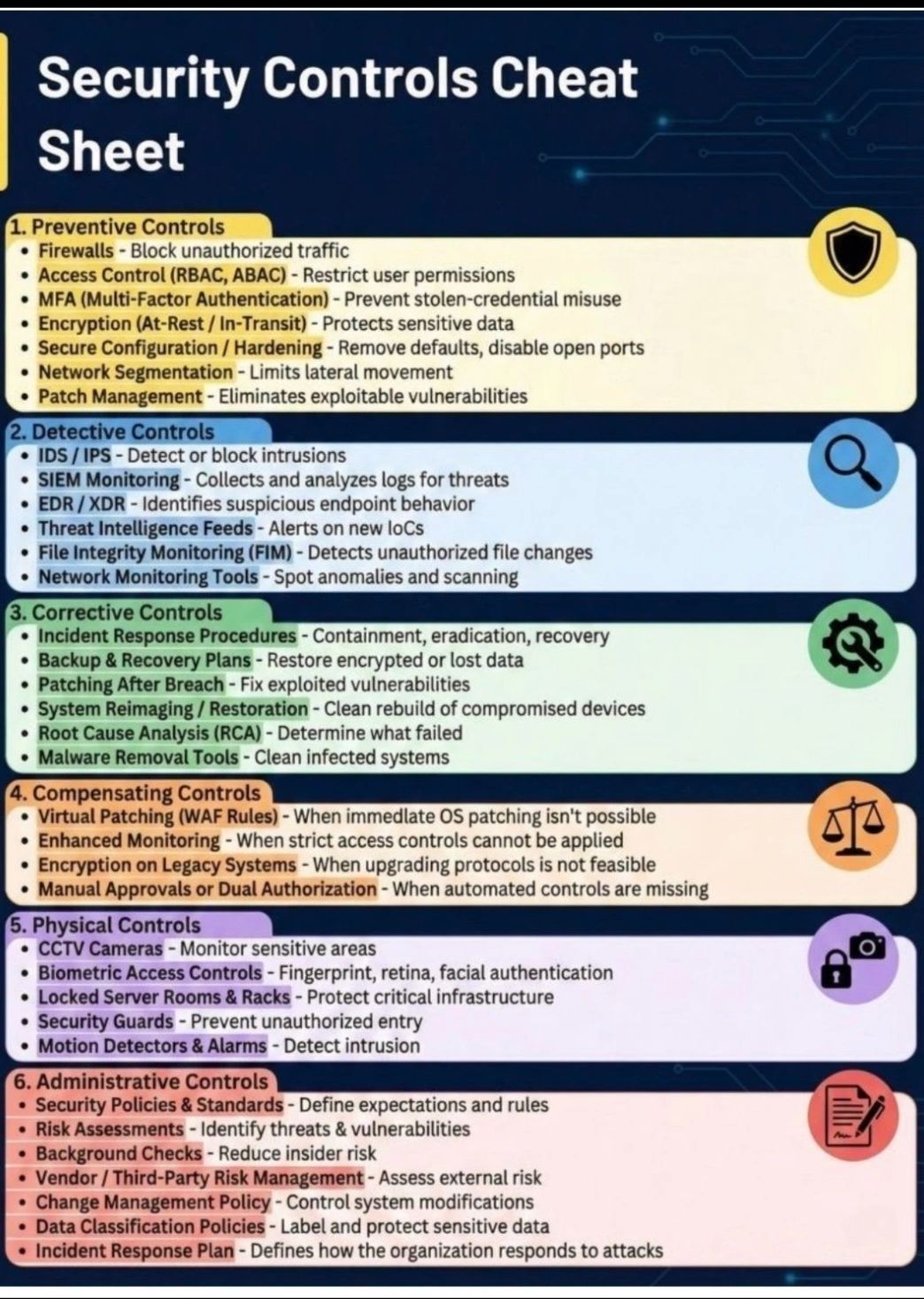
The Foundation of Digital Defense: Understanding the Cybersecurity Control Types
Before delving into the specific layers, it’s crucial to understand the fundamental categories of cybersecurity controls. These categories provide a framework for classifying and understanding the purpose of each security measure.
Preventive Controls: Stopping Threats Before They Start
Preventive controls are proactive measures designed to deter attacks and minimize the likelihood of a security incident occurring. Think of these as the first line of defense, aiming to block unauthorized access, prevent malware execution, and reduce the attack surface. They are critical for establishing a secure baseline and mitigating known risks.
Detective Controls: Identifying Anomalies and Incidents Early
Even with robust preventive controls in place, some threats may inevitably bypass them. Detective controls are designed to identify unauthorized activities, system anomalies, and security incidents as quickly as possible. These controls act as an early warning system, alerting security teams to potential breaches and allowing for timely intervention.
Corrective Controls: Restoring Systems After an Incident
When a security incident does occur, corrective controls come into play. Their primary purpose is to minimize the damage caused by an incident, restore affected systems and data to their normal operational state, and prevent similar incidents from happening again. These controls are essential for business resilience and disaster recovery.
Compensating Controls: Bridging Security Gaps
Compensating controls are alternative or supplementary security measures implemented when a primary control is impractical or impossible to deploy. They are designed to provide an equivalent level of security to the primary control, ensuring that no significant vulnerabilities remain unaddressed. These are particularly useful in complex or legacy environments.
Physical Controls: Safeguarding the Tangible
While much of cybersecurity focuses on the digital realm, the physical security of an organization’s assets is equally vital. Physical controls are measures taken to protect the physical environment where IT systems and data are housed. An attacker with physical access can potentially bypass many digital safeguards, making robust physical security indispensable.
Administrative Controls: The Human and Policy Layer
Administrative controls form the backbone of any effective cybersecurity program. These are the policies, procedures, standards, and guidelines that govern how an organization manages security. They focus on people, processes, and governance, ensuring that all security efforts are coordinated, consistent, and aligned with organizational objectives.
The Six Essential Layers of Cybersecurity Controls
Now, let’s explore each of the six critical layers of cybersecurity controls in detail, examining their components and significance in building a resilient defense.
1. Preventive Controls: Building the First Line of Defense
Preventive controls are the proactive measures organizations take to prevent security incidents from occurring in the first place. They are your digital locks and gates, designed to keep threats out.
Firewalls: The Network’s Gatekeepers
Firewalls are arguably the most fundamental preventive control. They act as a barrier between your internal network and external networks (like the internet), controlling inbound and outbound network traffic based on predefined security rules.
- Packet Filtering Firewalls: These examine network packets individually and allow or deny them based on source and destination IP addresses, port numbers, and protocols.
- Stateful Inspection Firewalls: More advanced, these not only filter packets but also track the state of active connections, making them more effective at blocking unauthorized communication.
- Application-Layer Firewalls (Proxies): These operate at the application layer, understanding specific application protocols and providing more granular control over traffic, often inspecting the actual content of communications.
- Next-Generation Firewalls (NGFWs): These integrate traditional firewall functionalities with additional features like intrusion prevention systems (IPS), deep packet inspection, and application awareness, offering more comprehensive protection.
Access Control: Restricting User Permissions
Access control mechanisms ensure that only authorized individuals and systems can access specific resources. This is a critical principle of least privilege, meaning users should only have the minimum access necessary to perform their job functions.
- Role-Based Access Control (RBAC): Permissions are assigned to roles, and users are assigned to roles. This simplifies management and ensures consistency. For example, all employees in the “Accounting” role might have access to financial software, but not HR records.
- Attribute-Based Access Control (ABAC): This offers more granular control by using attributes of the user, resource, and environment to determine access. For instance, a user might only access a document if they are in a specific department, at a particular time of day, and on a company-issued device.
- Discretionary Access Control (DAC): The owner of a resource determines who can access it and what permissions they have.
- Mandatory Access Control (MAC): Access decisions are made by a central authority based on sensitivity labels (e.g., “Top Secret”) assigned to subjects and objects.
Multi-Factor Authentication (MFA): Beyond Passwords
Usernames and passwords alone are often weak points in security. MFA adds layers of verification, requiring users to present two or more different types of credentials from independent categories of verification to gain access. This significantly reduces the risk of stolen credentials being used for unauthorized access.
- Knowledge Factors: Something the user knows (e.g., password, PIN).
- Possession Factors: Something the user has (e.g., smartphone for an OTP, hardware token).
- Inherence Factors: Something the user is (e.g., fingerprint, facial recognition, voice recognition).
Encryption (At-Rest / In-Transit): Protecting Sensitive Data
Encryption transforms data into an unreadable format (ciphertext), protecting it from unauthorized access. Even if an attacker gains access to encrypted data, they cannot easily understand it without the decryption key.
- Encryption At-Rest: Protects data stored on devices (hard drives, databases, cloud storage). If a database server is stolen, the data remains protected.
- Encryption In-Transit: Protects data as it moves across networks (e.g., via SSL/TLS for web traffic, VPNs). This is crucial for securing communications between users and servers, or between different systems.
Secure Configuration / Hardening: Eliminating Vulnerabilities
Many security breaches exploit default configurations or known vulnerabilities in software and hardware. Secure configuration, or hardening, involves modifying default settings, disabling unnecessary services, removing insecure protocols, and applying security best practices to reduce the attack surface.
- Removing Default Passwords: Always change default administrator passwords immediately.
- Disabling Unnecessary Services & Ports: Close any ports or services not absolutely required for the system’s function to minimize potential entry points.
- Implementing Principle of Least Privilege: Configure systems and applications to run with the minimum necessary permissions.
- Regular Audits: Periodically review system configurations to ensure compliance with security policies and best practices.
Network Segmentation: Limiting Lateral Movement
Network segmentation divides a computer network into smaller, isolated segments. This limits the “blast radius” of a security breach. If one segment is compromised, the attacker’s ability to move laterally to other parts of the network is significantly restricted.
- VLANs (Virtual Local Area Networks): Logical grouping of network devices, allowing for separation without requiring separate physical infrastructure.
- Firewalls Between Segments: Deploying internal firewalls to control traffic flow between different network segments.
- Micro-segmentation: Even more granular segmentation, often down to individual workloads, using software-defined networking (SDN) principles.
Patch Management: Eliminating Exploitable Vulnerabilities
Software vulnerabilities are a constant reality. Patch management is the systematic process of identifying, acquiring, testing, and applying software updates (patches) to address security flaws and bugs. A robust patch management program is crucial for closing known security gaps that attackers frequently target.
- Automated Patching Tools: Utilize tools to streamline the patching process across many systems.
- Regular Vulnerability Scanning: Continuously scan systems for missing patches and newly discovered vulnerabilities.
- Testing Patches: Before deploying patches broadly, test them in a controlled environment to prevent introducing new issues.
2. Detective Controls: Uncovering Threats in Action
Detective controls are the security camera, alarm system, and watchful eyes of your organization. Their goal is to identify security incidents as they happen or shortly thereafter, enabling a rapid response.
IDS/IPS: Detecting or Blocking Intrusions
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) monitor network traffic and system activity for malicious patterns or policy violations.
- Intrusion Detection Systems (IDS): An IDS monitors network traffic for suspicious activity and known threats, generating alerts when it detects something anomalous. It doesn’t actively block traffic but provides vital information for incident response.
- Network-based IDS (NIDS): Monitors traffic across an entire network.
- Host-based IDS (HIDS): Monitors individual host systems for suspicious activity.
- Intrusion Prevention Systems (IPS): An IPS goes a step further than an IDS. When it detects a malicious signature or anomalous behavior, it actively takes steps to prevent the intrusion, such as dropping malicious packets, blocking offending IP addresses, or resetting connections.
SIEM Monitoring: Collecting and Analyzing Logs for Threats
Security Information and Event Management (SIEM) systems collect and aggregate logs and event data from various security devices, applications, and systems across an organization’s infrastructure. They then analyze this data in real-time to identify security threats, compliance issues, and suspicious activities.
- Log Aggregation: Centralizing log data from firewalls, servers, endpoints, applications, and more.
- Correlation: Identifying relationships between seemingly disparate events to spot attack patterns.
- Alerting: Generating alerts for security teams when predefined rules or anomaly detection identifies a potential threat.
- Reporting: Providing compliance and security posture reports.
EDR/XDR: Identifying Suspicious Endpoint Behavior
Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) solutions focus on securing endpoint devices (laptops, desktops, servers, mobile devices).
- Endpoint Detection and Response (EDR): EDR solutions continuously monitor endpoints for malicious activity, collect detailed telemetry data, and use analytics to identify suspicious behaviors. They provide capabilities for investigation, threat hunting, and remediation on individual endpoints.
- Extended Detection and Response (XDR): XDR is an evolution of EDR, expanding its scope beyond just endpoints to integrate and correlate security data from a wider range of sources, including networks, cloud environments, email, and identity systems. This provides a more unified and comprehensive view of threats across the entire digital estate, improving detection accuracy and speed.
Threat Intelligence Feeds: Alerts on New IoCs
Threat intelligence feeds provide organizations with up-to-date information on emerging threats, attack techniques, and indicators of compromise (IoCs). These feeds act as an early warning system, allowing organizations to proactively defend against new threats.
- IoCs (Indicators of Compromise): IP addresses, domain names, file hashes, and other artifacts associated with known malicious activity.
- Attack Signatures: Patterns of malicious activity that can be used to detect and block threats.
- Vulnerability Information: Details on newly discovered vulnerabilities and how to mitigate them.
File Integrity Monitoring (FIM): Detecting Unauthorized File Changes
File Integrity Monitoring (FIM) systems monitor critical system and application files for unauthorized modifications. Malicious actors often alter system files, configuration files, or data files as part of an attack. FIM detects these changes, alerting security teams to potential tampering or compromise.
- Baseline Creation: Establishing a trusted baseline of critical file characteristics (hash, size, permissions).
- Continuous Monitoring: Regularly comparing current file states against the baseline.
- Alerting: Notifying administrators of any deviations or unauthorized changes.
Network Monitoring Tools: Spotting Anomalies and Scanning
Network monitoring tools continuously observe network traffic and device behavior to identify unusual patterns, performance issues, and potential security threats. These tools are essential for maintaining network health and detecting malicious activities like port scanning, unauthorized data transfers, or denial-of-service attacks.
- Traffic Analysis: Inspecting network traffic for suspicious patterns or unauthorized protocols.
- Baseline Behavioral Analysis: Establishing normal network behavior and flagging deviations.
- Vulnerability Scanning: Actively scanning network devices for known vulnerabilities and misconfigurations.
- Packet Sniffing: Capturing and analyzing network packets for deeper investigation into potential threats.
3. Corrective Controls: Recovering and Learning from Incidents
Corrective controls are activated after a security incident has occurred. Their primary goal is to minimize damage, restore business operations, and learn from the incident to prevent future occurrences.
Incident Response Procedures: Containment, Eradication, Recovery
A well-defined Incident Response Plan (IRP) is paramount for efficiently handling security incidents. It outlines the steps an organization will take from initial detection to full recovery.
- Preparation: Developing the IRP, establishing an incident response team, and acquiring necessary tools.
- Identification: Detecting the incident and determining its scope and nature.
- Containment: Limiting the damage and preventing the incident from spreading further (e.g., isolating compromised systems).
- Eradication: Removing the root cause of the incident (e.g., patching vulnerabilities, removing malware).
- Recovery: Restoring affected systems and data to normal operations.
- Post-Incident Activity: Analyzing the incident, identifying lessons learned, and updating security measures.
Backup & Recovery Plans: Restoring Encrypted or Lost Data
Data loss, whether due to a cyberattack (like ransomware), system failure, or human error, can be catastrophic. Comprehensive backup and recovery plans are essential corrective controls.
- Regular Backups: Implement automated, frequent backups of critical data and systems.
- Offsite & Offline Backups: Store copies of backups in secure, geographically separated locations and consider immutable or offline backups to protect against ransomware.
- Recovery Testing: Periodically test backup restoration procedures to ensure they are effective and data can be recovered reliably.
- Data Redundancy: Employing redundant systems or storage solutions to ensure data availability.
Patching After Breach: Fixing Exploited Vulnerabilities
If an attacker exploited a specific vulnerability, patching that vulnerability immediately after containment and eradication is a crucial corrective step to prevent re-exploitation. This often involves applying emergency patches or implementing temporary mitigation measures.
System Reimaging / Restoration: Clean Rebuild of Compromised Devices
In cases of severe compromise, especially with rootkit infections or deeply embedded malware, simply removing the malware might not be sufficient. System reimaging or restoration involves wiping compromised devices and rebuilding them from trusted, clean images. This ensures that no remnants of the attack persist.
Root Cause Analysis (RCA): Determining What Failed
After an incident, conducting a thorough Root Cause Analysis (RCA) is vital. This process aims to identify the underlying cause of the security incident, not just the symptoms. Understanding the root cause allows organizations to implement effective, long-term corrective actions.
- Identifying Contributing Factors: Analyzing all elements that led to the incident.
- “Five Whys” Technique: Asking “why” repeatedly to drill down to the fundamental cause.
- Documentation: Recording findings and recommendations for future prevention.
Malware Removal Tools: Cleaning Infected Systems
Specialized malware removal tools are corrective controls used to detect, quarantine, and eliminate various types of malicious software from infected systems. These tools are critical for cleaning up systems after a malware infection has been identified.
- Antivirus/Anti-Malware Software: Daily use for detection and removal.
- Forensic Toolkits: More advanced tools for deep scanning and analysis of compromised systems.
- Sandboxing: Running suspicious files in an isolated environment to analyze their behavior safely.
4. Compensating Controls: Filling the Gaps
Compensating controls are security measures deployed to address a deficiency in a primary control or when a specific control cannot be fully implemented due to technical, operational, or business constraints. They ensure that an equivalent level of security is maintained.
Virtual Patching (WAF Rules): When Immediate OS Patching Isn’t Possible
Sometimes, immediate patching of an operating system or application isn’t feasible due to various reasons (e.g., system criticality, vendor approval, testing requirements). Virtual patching uses security devices, often Web Application Firewalls (WAFs), to intercept and inspect traffic, blocking known exploit attempts for unpatched vulnerabilities.
- Web Application Firewalls (WAFs): Protect web applications from common attacks like SQL injection and cross-site scripting by filtering out malicious traffic before it reaches the vulnerable application.
- Intrusion Prevention Systems (IPS): Can also provide virtual patching capabilities by blocking attack patterns targeting unpatched systems.
Enhanced Monitoring: When Strict Access Controls Cannot Be Applied
If strict access controls cannot be fully implemented for certain sensitive systems (e.g., legacy systems with hardcoded credentials), enhanced monitoring becomes a compensating control. This involves increasing the level of scrutiny and logging for access to these systems to detect any unauthorized activity quickly.
- Increased SIEM Logging: Sending more detailed logs from the sensitive system to the SIEM for analysis.
- Real-time Alerts: Configuring immediate alerts for any anomalous access attempts or activities within the system.
- Dedicated Security Personnel: Assigning specific team members to monitor these systems more closely.
Encryption on Legacy Systems: When Upgrading Protocols Is Not Feasible
Older systems or protocols might not support modern, strong encryption standards. When upgrading these protocols is not feasible, implementing encryption at a different layer or using a compensating encryption solution can protect the data.
- Full Disk Encryption: Encrypting the entire disk of a legacy server.
- Application-Layer Encryption: Encrypting sensitive data within the application before it’s stored or transmitted, even if the underlying protocol is less secure.
- VPNs: Using a Virtual Private Network to encrypt traffic to and from legacy systems even if the system itself doesn’t support modern transport encryption.
Manual Approvals or Dual Authorization: When Automated Controls Are Missing
In situations where automated security controls are absent or insufficient, manual processes can serve as compensating controls. This often involves human review and approval steps to ensure that critical actions are authorized and legitimate.
- Manual Review of Access Requests: Human oversight for granting access to sensitive resources.
- Dual Authorization for Financial Transactions: Requiring two individuals to approve high-value transactions.
- Segregation of Duties: Ensuring no single individual can complete a critical task without oversight.
5. Physical Controls: Securing the Tangible Infrastructure
Physical security is the bedrock upon which digital security rests. Without adequate physical controls, an attacker can bypass even the most sophisticated digital defenses by gaining direct access to hardware.
CCTV Cameras: Monitoring Sensitive Areas
Closed-Circuit Television (CCTV) cameras are crucial for monitoring sensitive physical areas, such as data centers, server rooms, and building entry points. They provide visual deterrence, surveillance, and forensic evidence in case of a physical security breach.
- Strategic Placement: Positioning cameras to cover all critical entry and vulnerable points.
- High-Resolution Recording: Ensuring clear images for identification.
- Retention Policies: Storing footage for a sufficient period for investigations.
Biometric Access Controls: Fingerprint, Retina, Facial Authentication
Biometric access controls use unique biological characteristics to verify identity at physical access points, offering a stronger form of authentication than traditional keys or access cards.
- Fingerprint Scanners: Common for access to restricted areas.
- Retinal Scanners: Highly secure, often used in high-security environments.
- Facial Recognition: Used for entry or verification in certain settings.
Locked Server Rooms & Racks: Protecting Critical Infrastructure
Securing physical access to server rooms, data centers, and even individual server racks is fundamental. This prevents unauthorized individuals from tampering with or stealing critical hardware.
- Reinforced Doors and Walls: Building secure perimeters for server rooms.
- Access Control Systems: Using card readers, keypads, or biometrics for entry.
- Locked Racks: Securing individual server racks to protect equipment within a larger data center.
Security Guards: Preventing Unauthorized Entry
Human security guards provide an active presence, deterrence, and the ability to respond directly to physical threats or unauthorized entry. They can monitor CCTV, patrol premises, and enforce physical security policies.
- 24/7 Monitoring: Ensuring constant vigilance in critical areas.
- Incident Response: Responding to alarms and suspicious activities.
- Visitor Management: Controlling and logging visitor access.
Motion Detectors & Alarms: Detecting Intrusion
Motion detectors and alarm systems provide automated detection of unauthorized movement or entry into restricted areas. They alert security personnel and can trigger other responses, such as locking down areas or activating additional surveillance.
- Infrared Motion Sensors: Detecting movement based on heat signatures.
- Door and Window Sensors: Triggering alarms upon unauthorized opening.
- Integration with CCTV: Triggering camera recording upon detection.
6. Administrative Controls: Governing Security Policies and Practices
Administrative controls are the organizational directives, policies, procedures, and management practices that guide the implementation and enforcement of all other security controls. They are crucial for establishing a security-aware culture and ensuring compliance.
Security Policies & Standards: Defining Expectations and Rules
Security policies are high-level statements that define an organization’s commitment to security and outline its security objectives. Standards provide more detailed requirements for implementing these policies.
- Acceptable Use Policy: Defines how employees can use organizational IT resources.
- Password Policy: Specifies requirements for password complexity, length, and change frequency.
- Data Handling Policy: Dictates how sensitive data should be stored, processed, and transmitted.
- Clean Desk Policy: Requires employees to keep sensitive information off their desks when away.
Risk Assessments: Identifying Threats & Vulnerabilities
Regular risk assessments are administrative controls that systematically identify, analyze, and evaluate potential security risks to an organization’s assets. This process helps prioritize security investments and develop appropriate mitigation strategies.
- Asset Identification: Cataloging all critical information assets.
- Threat Identification: Listing potential threats (e.g., malware, insider threats, natural disasters).
- Vulnerability Identification: Pinpointing weaknesses in systems, processes, or configurations.
- Impact and Likelihood Analysis: Assessing the potential consequences and probability of each risk.
Background Checks: Reducing Insider Risk
Performing background checks on new hires, especially those in sensitive roles, is a preventive administrative control to mitigate insider threats. It helps identify individuals who may pose a security risk based on past behavior or criminal history.
- Criminal Records Checks: Verifying an applicant’s legal history.
- Employment Verification: Confirming past work experience and references.
- Credit Checks: For roles involving financial responsibility.
Vendor / Third-Party Risk Management: Assessing External Risk
Organizations often rely on third-party vendors and service providers. Vendor risk management is an administrative control that assesses and mitigates the security risks introduced by these external relationships. This ensures that third parties adhere to the organization’s security standards.
- Due Diligence: Evaluating a vendor’s security posture before engagement.
- Security Clauses in Contracts: Including specific security requirements and audit rights in agreements.
- Ongoing Monitoring: Regularly reviewing vendor compliance and security performance.
Change Management Policy: Controlling System Modifications
A change management policy is a critical administrative control that governs how changes to IT systems, applications, and configurations are proposed, reviewed, approved, tested, and implemented. This prevents unauthorized or poorly planned changes from introducing vulnerabilities or disruptions.
- Formal Change Request Process: All changes must follow a defined workflow.
- Impact Assessment: Evaluating the potential security and operational impact of a change.
- Rollback Plan: Having a plan to revert changes if unforeseen issues arise.
Data Classification Policies: Label and Protect Sensitive Data
Data classification is an administrative control that categorizes an organization’s data based on its sensitivity, value, and regulatory requirements. This allows for the appropriate application of security controls to protect different types of data more effectively.
- Classification Levels: Defining categories like “Public,” “Internal,” “Confidential,” “Restricted,” or “Top Secret.”
- Handling Guidelines: Specifying how each data classification level should be stored, transmitted, and accessed.
- Ownership: Assigning responsibility for maintaining data classification.
Incident Response Plan: Defining How the Organization Responds to Attacks
While incident response procedures are a corrective control, the creation and maintenance of the Incident Response Plan itself is an administrative control. It ensures that the organization has a structured and practiced approach to dealing with security incidents, minimizing chaos and maximizing effectiveness during a crisis.
- Clear Roles and Responsibilities: Defining who does what during an incident.
- Communication Protocols: Establishing how internal and external stakeholders will be informed.
- Playbooks: Detailed step-by-step guides for different types of incidents.
- Regular Testing & Drills: Practicing the plan to ensure its effectiveness.
Industry Insights: Why These Controls Matter Now More Than Ever
The landscape of cyber threats is not static; it’s a rapidly evolving battleground. The importance of these layered controls has never been more pronounced, especially in the context of recent technological advancements and shifting organizational priorities.
The Accelerating Threat Landscape: AI-Driven Sophistication
Cyber threats are no longer simple phishing attempts. The advent of AI and machine learning has empowered attackers with unprecedented capabilities:
- Automated Phishing: AI-powered tools can generate incredibly convincing and highly personalized phishing emails, making them harder for humans to detect.
- Deepfakes: AI-generated audio or video can be used to impersonate executives or critical personnel, enabling sophisticated social engineering and fraud.
- Adaptive Malware: Malware that can learn, evolve, and evade detection based on its environment, making traditional signature-based defenses less effective.
- Increased Attack Volume: The sheer volume of cyberattacks has more than doubled in recent years, overwhelming organizations that lack robust, multi-layered defenses.
This AI-driven sophistication means that relying on a single security solution is akin to bringing a knife to a gunfight. Only a comprehensive, layered approach can stand a chance against these advanced persistent threats.
Adopting Zero Trust and AI-Powered Defenses
The cybersecurity paradigm is shifting, with Zero Trust and AI-powered defenses emerging as foundational strategies.
- Zero Trust Architecture: This principle fundamentally challenges the traditional “trust-but-verify” model. Instead, it asserts “never trust, always verify.” Every user, device, and application attempting to access resources, whether inside or outside the network perimeter, must be authenticated and authorized. This drastically limits lateral movement and minimizes the impact of a breach. Implementing Zero Trust inherently necessitates a strong emphasis on access control, multi-factor authentication, network segmentation, and continuous monitoring – all elements of the layered controls discussed.
- AI-Powered Defenses: While AI fuels attacks, it also empowers defense. AI and machine learning are increasingly integrated into security controls for:
- Enhanced Detection: AI can analyze vast amounts of data (logs, network traffic, endpoint behavior) to identify subtle anomalies and unknown threats that human analysts might miss.
- Automated Response: AI can automate initial response actions, such as isolating a compromised endpoint or blocking malicious traffic, speeding up reaction times and reducing the burden on security teams.
- Predictive Analytics: AI can analyze historical data to predict future attack vectors and proactively strengthen defenses.
Integrating these modern strategies requires a deep understanding and sophisticated implementation of all six layers of security controls, particularly detective and administrative controls that support continuous monitoring and policy enforcement.
Skills and Training: A Top Enterprise Priority
The rapid evolution of cyber threats and defense technologies has created a significant cybersecurity skills gap. Organizations increasingly recognize that their people are both their strongest asset and their most vulnerable point.
- Security Awareness & Human Layer (NIST-Inspired): While not explicitly listed as a control type in the given image, the human element is crucial and overlaps significantly with Administrative Controls. Security awareness training empowers employees to identify and report phishing attempts, adhere to security policies, and understand their role in protecting organizational assets. The NIST Special Publication 800-53, Revision 5 recognizes “Security Awareness and Training (AT)” as a critical control family, underscoring its importance [csrc.nist.rip]. Other frameworks like “the 7 Layers of Cybersecurity” explicitly identify “Security Awareness & Human Layer” as a distinct, vital layer [blog.cybernod.com]. This layer ensures that administrative controls, such as data classification policies and incident response procedures, are understood and followed by all personnel.
- AI Security Expertise: With the rise of AI-driven threats and defenses, organizations desperately need professionals skilled in AI security – understanding how to secure AI systems, detect AI-generated attacks, and leverage AI for defense.
- Continuous Education: Cybersecurity professionals must continuously update their skills to stay ahead of the curve, encompassing everything from foundational network security to advanced threat hunting and cloud security.
Investing in skills and training directly strengthens the effectiveness of all six layers of controls. A well-trained workforce can better implement preventive measures, interpret detective alerts, execute corrective actions, and adhere to administrative policies.
Practical Takeaways for Security Professionals
For cybersecurity professionals, the challenge lies not just in understanding these controls but in integrating and optimizing them within their unique organizational contexts.
Integrate Controls Across People, Process, and Technology
Security is not solely about deploying tools. It’s a holistic ecosystem where people, processes, and technology must work in harmony.
- People: Every employee is a part of the security chain. Comprehensive training (administrative control) ensures that personnel understand policies and can contribute to prevention and detection.
- Process: Well-defined procedures (administrative controls) for incident response, change management, and risk assessment are vital for consistent and effective security operations.
- Technology: The various preventive, detective, corrective, and compensating controls (firewalls, SIEM, EDR, encryption, etc.) are the technological enablers. Without the right processes and trained people, even the most advanced technology will fall short.
Embrace AI-Assisted Detection and Response While Understanding Its Risks
Leverage AI’s power to enhance your security posture, but do so with a critical understanding of its limitations and potential pitfalls.
- Augment Human Capabilities: See AI as a powerful assistant that can process vast amounts of data and identify patterns faster than humans, freeing up security analysts for more complex tasks.
- Guard Against AI Biases and Blind Spots: AI models can sometimes produce false positives or miss novel attacks if not properly trained or monitored. Regular human oversight and validation are crucial.
- Secure the AI Itself: Ensure your AI models and platforms are secured against adversarial AI attacks, where attackers try to manipulate the AI’s learning process or its decisions.
Adopt Zero Trust Principles to Minimize Unauthorized Access and Lateral Movement
The Zero Trust model is a paradigm shift that should underpin all security architecture decisions.
- Verify Explicitly: Always authenticate and authorize based on all available data points, including user identity, device health, location, and the sensitivity of the resource being accessed.
- Least Privilege Access: Grant users the minimum access necessary for the shortest possible duration. This directly ties into robust access control (preventive control) and identity and access management (often considered a seventh layer in some models [blog.cybernod.com]).
- Assume Breach: Design your defenses with the assumption that a breach will happen. This emphasizes strong segmentation (preventive control) and detective controls to limit damage and facilitate rapid response.
Continuously Update Your Risk Management Framework to Address Real-World Threats
The threat landscape is dynamic, and so too must be your risk management approach.
- Regular Risk Assessments: Conduct frequent and thorough assessments to identify new threats, vulnerabilities, and changes in your organizational environment.
- Threat Intelligence Integration: Continuously ingest and apply threat intelligence (detective control) to inform your risk assessments and adapt your defenses.
- Lessons Learned from Incidents: Use post-incident analysis (corrective control) to identify gaps in your controls and update your risk management framework accordingly.
- Adapt to Regulatory Changes: Stay abreast of evolving compliance requirements and adjust your controls to meet new mandates.
Conclusion: Cybersecurity as a Strategic Business Function
Cybersecurity is no longer a peripheral IT function; it is a strategic business imperative. The layered defense strategy, built upon the six core types of security controls—preventive, detective, corrective, compensating, physical, and administrative—provides a robust framework for protecting an organization’s digital assets and business value.
The escalating sophistication of AI-driven cyber threats, coupled with the imperative to adopt modern security paradigms like Zero Trust and AI-powered defenses, underscores the critical importance of a holistic, adaptive security posture. Organizations that invest in integrating these controls across people, process, and technology, embrace continuous learning, and view security as an ongoing strategic function will be best positioned to thrive in the face of evolving cyber risks.
Don’t just react to threats; anticipate them. Build a resilient defense that protects your organization’s future. For expert guidance on architecting and implementing a robust cybersecurity strategy tailored to your unique needs, contact us today.
Strengthen your digital defenses with IoT Worlds. Email us at info@iotworlds.com to discuss your cybersecurity challenges.