The operational technology (OT) landscape is undergoing a profound transformation. What was once a domain of isolated, air-gapped systems is now a hyperconnected, intelligent, and AI-enabled environment. This IT/OT convergence, while promising unprecedented efficiency and innovation, has simultaneously ushered in a new era of complex cybersecurity challenges. In 2026 and beyond, securing OT environments is not merely an integration challenge; it’s a strategic imperative for every organization operating critical infrastructure or manufacturing facilities.
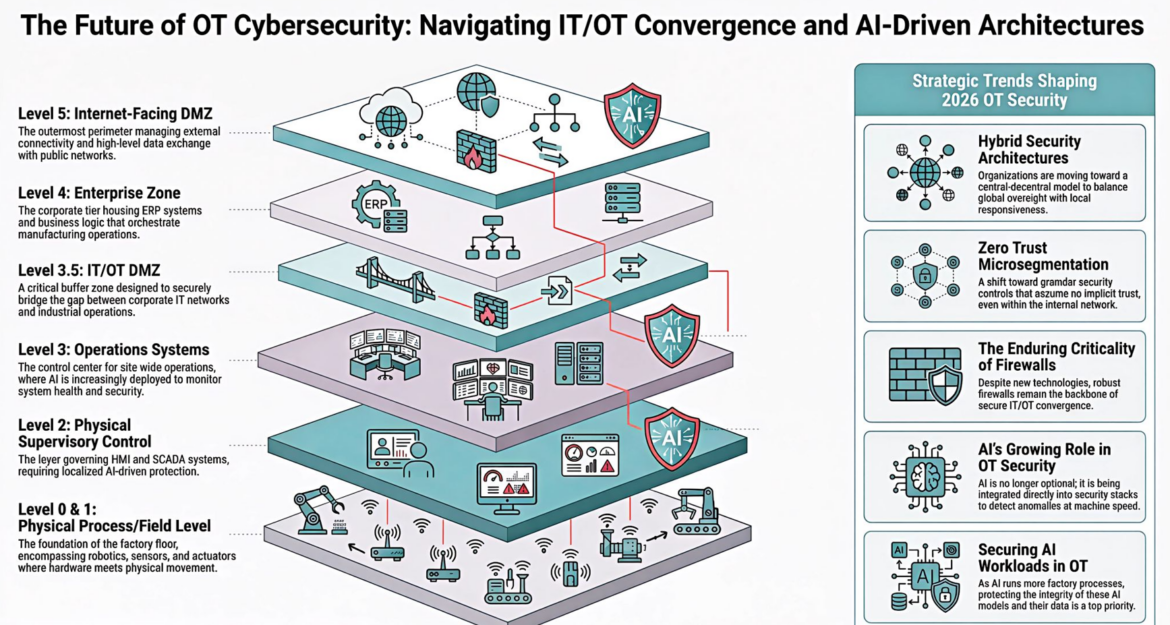
The traditional “air-gap” security model for OT is a relic of the past, replaced by a layered, interconnected digital nervous system. Every sensor, PLC, SCADA system, and enterprise resource planning (ERP) component now participates in this unified ecosystem. This pervasive connectivity means that every single layer, from the physical process floor to internet-facing demilitarized zones (DMZs), represents a potential attack surface. Proactive and sophisticated cybersecurity strategies are no longer optional but essential for maintaining operational integrity, business continuity, and national security.
This article delves into the critical shifts defining OT cybersecurity, exploring the architectural evolution, the emergence of advanced security paradigms like Zero Trust, the enduring role of traditional defenses, and the indispensable integration of Artificial Intelligence (AI) — both as a security enabler and a new attack vector to be secured.
The Converged Industrial Stack: A New Attack Surface
The modernization of industrial operations, driven by Industry 4.0 initiatives and the quest for real-time insights, has blurred the lines between Information Technology (IT) and Operational Technology (OT). This convergence has created a complex, multi-layered architecture where digital and physical worlds intertwine. Understanding each layer’s role and its inherent vulnerabilities is fundamental to building a robust OT cybersecurity posture.
Level 0 & 1: Physical Process/Field Level
This foundational layer represents the heart of industrial operations. It encompasses the physical process and field devices that directly interact with the physical world. This includes:
- Sensors: Devices that measure physical parameters like temperature, pressure, flow, and level.
- Actuators: Components that execute commands to control physical processes, such as opening valves or starting motors.
- Robotics: Automated machines performing tasks in manufacturing or other industrial settings.
- Programmable Logic Controllers (PLCs): Industrial computers that automate specific processes, often receiving input from sensors and sending commands to actuators.
These devices are the direct interface with physical movement and processes. While traditionally isolated, modern implementations see these devices increasingly connected, often via wireless technologies or industrial Ethernet, making them susceptible to manipulation if security is not rigorously applied from the ground up. An attack here could lead to physical damage, production halts, or safety incidents.
Level 2: Physical Supervisory Control
Above the physical process level lies the supervisory control layer, which governs Human-Machine Interfaces (HMI) and Supervisory Control and Data Acquisition (SCADA) systems.
- HMI: Graphical user interfaces that allow operators to monitor and control industrial processes.
- SCADA systems: Control systems used to monitor and control industrial processes across large geographical areas. They collect data from field devices and present it to operators.
This layer is critical for real-time monitoring and control. Compromises at this level can enable attackers to alter operational parameters, manipulate displays to mask malicious activity, or even shut down entire operations. The image highlights the increasing deployment of localized AI-driven protection at this level, indicating a shift towards using AI to secure highly sensitive control functions.
Level 3: Operations Systems
This layer houses the control center for site-wide operations, where broader process management and data aggregation occur. It includes Manufacturing Execution Systems (MES) and other systems responsible for managing production workflows, scheduling, and quality control.
AI is increasingly deployed here to monitor system health and security across the entire site. This means AI can analyze large datasets from various industrial processes to detect anomalies, predict potential failures, and identify unusual patterns that might indicate a cyber intrusion. However, this also introduces the challenge of securing the AI systems themselves.
Level 3.5: IT/OT DMZ
The IT/OT Demilitarized Zone (DMZ) is a critical buffer designed to securely bridge the gap between corporate IT networks and industrial operations. It acts as a controlled gateway, preventing direct communication between the IT and OT environments while enabling necessary data exchange. This is where protocols are translated, data is filtered, and security policies are enforced to protect the sensitive OT network from potential threats originating in the more open IT network. A proper IT/OT DMZ is not just a firewall; it’s a carefully engineered security zone with intrusion detection/prevention systems (IDPS), data diodes, and strict access controls.
Level 4: Enterprise Zone
The Enterprise Zone represents the corporate IT network, housing ERP systems, business process management (BPM) tools, and other business logic that orchestrate manufacturing operations at a higher level. This layer typically manages orders, inventory, logistics, and financial data. While not directly controlling physical processes, a compromise here could indirectly impact OT by disrupting production schedules, manipulating supply chains, or initiating fraudulent activities that affect industrial output.
Level 5: Internet-Facing DMZ
This outermost perimeter manages external connectivity and high-level data exchange with public networks, including cloud services, external partners, and remote access solutions. While essential for global business operations and accessing cloud-based services, this layer presents the highest exposure to internet-borne threats. Strong perimeter defenses, secure remote access solutions, and continuous threat intelligence are paramount here to prevent attacks from propagating into the internal network and eventually reaching the OT environment.
The shift to a layered, connected, and AI-enabled industrial stack means that organizations must adopt a holistic security approach, understanding that an attack on any layer can potentially cascade through the entire system.
Strategic Trends Shaping 2026 OT Security
The evolving threat landscape and the increasing complexity of converged IT/OT environments necessitate a re-evaluation of traditional OT security strategies. Several strategic trends are reshaping how organizations approach security in 2026, moving beyond perimeter defense to a more integrated, intelligent, and adaptable posture.
Hybrid Security Architectures
The paradigm for OT security is shifting from rigid, centralized models to hybrid (central-decentral) security architectures. This evolution acknowledges the inherent need for both global governance and local operational responsiveness.
What it means:
Organizations are moving towards a model where overarching security policies, compliance frameworks, and threat intelligence are centrally managed and distributed across the enterprise. However, the implementation, monitoring, and immediate response mechanisms are often decentralized, allowing local sites and operational units to maintain agility and address immediate threats without significant delays. This balances the need for consistent security standards across a global footprint with the unique requirements and real-time demands of individual operational sites.
Why it matters:
This hybrid approach recognizes that a “one-size-fits-all” security model is inadequate for diverse OT environments. Global governance ensures consistency and leverages economies of scale for security investments, while local responsiveness enables rapid incident handling and adaptation to site-specific risks, significantly reducing mean time to detect (MTTD) and mean time to respond (MTTR) within critical operational contexts.
Zero Trust Microsegmentation
A fundamental shift in trust models is underway with the adoption of Zero Trust and Microsegmentation in OT environments. This paradigm challenges the long-held assumption that everything inside the network can be trusted.
What it means:
- Zero Trust: This security model operates on the principle “never trust, always verify.” It assumes that no user, device, or application, whether inside or outside the network perimeter, should be implicitly trusted. Every access request is rigorously authenticated, authorized, and continuously monitored.
- Microsegmentation: This involves dividing the network into small, isolated segments, each with its own granular security controls. This limits the lateral movement of attackers by restricting communication between different segments to only what is explicitly permitted. For OT, this means segmenting different process areas, control systems, and even individual devices.
Why it matters:
In converged IT/OT environments, where a breach in one segment can quickly spread, Zero Trust microsegmentation provides critical defense-in-depth. It reduces the attack surface, contains breaches to isolated segments, and enforces strict identity-based access controls, making it significantly harder for attackers to move unhindered through the network. This is particularly crucial for controlling east-west traffic – communication between devices within the same network – which is often overlooked by traditional perimeter defenses.
The Enduring Criticality of Firewalls
Despite the emergence of advanced technologies like AI-driven detection and Zero Trust, the enduring criticality of firewalls remains undeniable. Firewalls are foundational to any robust security architecture.
What it means:
Robust firewalls continue to serve as the bedrock of network security, particularly at critical junctions like the IT/OT DMZ. They enforce traffic filtering rules, allowing only authorized communications to pass between network zones. In converged environments, firewalls are essential for:
- Layered Zone Architecture: Creating distinct security zones (e.g., separating the Enterprise Zone from the IT/OT DMZ, and the IT/OT DMZ from the Operations Systems).
- Clear Segmentation Discipline: Enforcing granular policies at each boundary to control traffic flow and prevent unauthorized access or malicious activity from propagating.
Why it matters:
Firewalls, when properly configured and maintained, provide a critical first line of defense and play a vital role in network segmentation. They are essential for enforcing access policies, filtering malicious traffic, and preventing unauthorized connections, even in the presence of more sophisticated security mechanisms. Neglecting firewall fundamentals in the rush to adopt new technologies can leave significant vulnerabilities exploited by attackers.
AI’s Growing Role in OT Security
Artificial Intelligence is transitioning from a niche application to an indispensable component of OT security. AI’s growing role in OT security is no longer optional; it is deeply embedded across various aspects of the security stack.
What it means:
AI capabilities are being integrated directly into security tools and platforms to provide real-time, large-scale analysis and proactive threat detection. This includes:
- Anomaly Detection in Operations: AI algorithms learn normal operational behaviors and deviations that could indicate a malfunction, a cyber attack, or an insider threat.
- Predictive Monitoring in SCADA: AI analyzes SCADA data to predict equipment failures, security vulnerabilities, or unusual control commands.
- AI-assisted SOC Intelligence: Security Operations Centers (SOCs) leverage AI to sift through vast amounts of security event data, correlate alerts, prioritize threats, and automate initial responses, enabling security analysts to focus on complex investigations.
Why it matters:
The sheer volume and velocity of data generated in modern OT environments are beyond human capacity to analyze effectively. AI provides the ability to detect anomalies and respond to threats at machine speed, thereby improving the efficiency and effectiveness of OT cybersecurity defenses. It enables proactive identification of emerging threats and reduces the window of opportunity for attackers.
Securing AI Workloads in OT
As AI becomes integral to operational processes, a new critical concern emerges: Securing AI Workloads in OT. The integrity of AI models and their data is paramount, as AI increasingly influences production decisions.
What it means:
This trend focuses on protecting the AI systems themselves, recognizing that compromised AI can have devastating consequences for OT operations. Key aspects include:
- Model Integrity: Ensuring that AI models (e.g., for predictive maintenance, process optimization, or anomaly detection) have not been tampered with or poisoned with malicious data.
- Data Pipeline Validation: Rigorously validating the data flowing into and out of AI models to ensure its accuracy, integrity, and authenticity.
- Hardening Edge Inference Systems: Securing AI models deployed at the “edge” (close to the physical process) against physical and cyber attacks, as these systems directly influence real-time operations. This includes securing the hardware, software, and communication channels.
- AI Lifecycle Governance: Establishing robust governance frameworks for the entire AI lifecycle, from development and training to deployment, monitoring, and retirement, ensuring security considerations at every stage.
Why it matters:
If an attacker can compromise an AI model in OT, they could manipulate physical processes without directly breaching the underlying control systems. Maliciously altered AI could cause equipment damage, produce faulty products, or even create safety hazards. Securing AI workloads is a critical step to maintain trust in automated operations and prevent a new generation of cyber-physical attacks.
Architectural Evolution: The Layered Defense Paradigm
The shift from the traditional air-gapped model to a layered, interconnected industrial stack necessitates a paradigm shift in security architecture. This involves adopting a defense-in-depth strategy that integrates security controls across every level of the Purdue Model (or its modern interpretations), from the field level to the cloud.
Integrating Security into the Fabric of OT
Rather than treating security as an add-on, it must beintegrated into the fabric of OT operations from design to deployment. This means:
- Secure-by-Design Principles: Incorporating security considerations at the earliest stages of system design and development for OT devices and networks.
- Continuous Vulnerability Management: Regularly identifying, assessing, and mitigating vulnerabilities across all OT assets, including legacy systems that may not have been designed with modern cybersecurity in mind.
- Patch Management: Establishing robust processes for applying security patches to OT software and firmware, acknowledging the unique challenges of change management in production environments.
The Role of Cross-Functional Teams
Effective OT cybersecurity cannot operate in a silo. It requires close collaboration between IT and OT teams. The convergence of technologies demands a convergence of expertise.
- Shared Understanding: IT professionals bring cybersecurity best practices, while OT professionals bring deep knowledge of industrial processes, safety requirements, and system constraints. This shared understanding is crucial for developing effective and practical security solutions.
- Unified Incident Response: Developing integrated incident response plans that address both IT and OT aspects of a cyber-physical attack, ensuring rapid and coordinated recovery efforts.
- Training and Skill Development: Investing in cross-training programs to bridge the knowledge gap between IT and OT, creating a workforce capable of managing converged environments. This means blending traditional security analyst skills with industrial process knowledge.
Governance and Strategic Reflection for 2026 and Beyond
Beyond technical implementations, effective OT cybersecurity hinges on robust governance, strategic foresight, and a commitment to continuous improvement. The future belongs to organizations that secure intelligence, not just infrastructure.
Building Resilience through Governance
Governance in OT cybersecurity encompasses the policies, procedures, and organizational structures that ensure security objectives are met.
- Risk Management Frameworks: Implementing comprehensive risk management frameworks tailored to OT environments, identifying critical assets, assessing threats and vulnerabilities, and developing mitigation strategies.
- Compliance and Regulation: Adhering to relevant industry standards and regulatory requirements (e.g., ISA/IEC 62443, NIS2 Directive) to ensure a baseline level of security.
- Security Ownership and Accountability: Clearly defining roles and responsibilities for OT cybersecurity within the organization, from leadership to individual operators.
AI in the SOC: Enhancing Intelligence and Response
The modern OT Security Operations Center (SOC) is increasingly relying on AI-assisted intelligence to manage complex threat landscapes.
- Threat Intelligence Integration: AI can process vast amounts of global threat intelligence, correlating it with local OT context to identify emerging threats relevant to specific industrial operations.
- Automated Triage and Response: AI can automate the initial triage of security alerts, filter out false positives, and even initiate automated containment measures for known threats, allowing human analysts to focus on more sophisticated attacks.
- Behavioral Analytics: AI-driven behavioral analytics can detect deviations from normal user and system behavior, identifying potential insider threats or compromised accounts that might bypass traditional signature-based detection.
However, it is crucial to remember that automation in safety-critical environments requires human judgment for contextual decision-making, as the stakes include physical process integrity and human lives. Human-AI frameworks that balance autonomy with oversight are gaining momentum.
The Importance of Lifecycle Accountability
In a rapidly evolving threat landscape, cybersecurity is not a one-time project but an ongoing process demanding lifecycle accountability.
- Continuous Monitoring: Implementing 24/7 monitoring of OT networks and systems to detect threats in real-time.
- Regular Audits and Assessments: Conducting periodic security audits, penetration testing, and vulnerability assessments to evaluate the effectiveness of controls and identify new weaknesses.
- Adaptation and Improvement: Continuously adapting security strategies and technologies in response to new threats, evolving attack techniques, and changes in the operational environment.
Overcoming Challenges in the Converged OT Landscape
While the benefits of IT/OT convergence and AI integration are undeniable, they also present significant challenges for OT cybersecurity. Addressing these requires proactive strategies and a commitment to innovation.
Legacy Systems and Patching Dilemmas
Many OT environments still rely on legacy systems that were not designed with modern cybersecurity in mind. These systems often run outdated operating systems, lack basic security features, and are difficult or impossible to patch without disrupting operations.
- Mitigation Strategies: Implementing compensating controls like network segmentation, virtual patching, and rigorous access control can protect legacy assets when direct patching is not feasible. Asset inventory and vulnerability management are crucial starting points.
- Modernization Roadmaps: Developing long-term modernization roadmaps that gradually replace vulnerable legacy systems with secure, modern alternatives.
Talent Gap and Skill Shortages
There’s a significant talent gap in the cybersecurity industry, particularly for professionals with combined IT and OT expertise. This shortage makes it challenging for organizations to build and maintain effective OT security teams.
- Upskilling and Reskilling: Investing in training programs to upskill existing IT and OT personnel, fostering cross-functional expertise.
- Managed Security Services: Partnering with specialized managed security service providers (MSSPs) that possess expertise in OT cybersecurity to augment internal capabilities.
Data Privacy and Supply Chain Risks
The increased connectivity in OT environments raises concerns about data privacy and exposes organizations to supply chain risks.
- Data Governance: Establishing clear data governance policies for OT data, including classification, access controls, and retention periods.
- Third-Party Risk Management: Thoroughly vetting the security practices of all third-party vendors and suppliers involved in the OT supply chain, including hardware manufacturers and software providers.
- Securing AI Supply Chain: As AI becomes more prevalent, securing the AI supply chain – from data acquisition to model deployment – becomes critical to prevent the introduction of vulnerabilities or malicious manipulation.
Conclusion: Securing the Intelligent Industrial Future
The year 2026 marks a critical juncture for OT cybersecurity. The convergence of IT and OT, coupled with the pervasive integration of AI, has created an industrial landscape that is both incredibly powerful and inherently vulnerable. The future of industrial operations hinges on the ability of organizations to navigate this complex environment with sophisticated, proactive, and resilient cybersecurity strategies.
The journey requires a multifaceted approach:
- Architectural Transformation: Moving towards hybrid security architectures, meticulously implementing Zero Trust microsegmentation, and reaffirming the foundational role of robust firewalls.
- AI Integration: Leveraging AI for anomaly detection, predictive monitoring, and enhanced SOC intelligence, while simultaneously prioritizing the security of AI workloads themselves.
- Strategic Governance: Embracing robust risk management, ensuring regulatory compliance, fostering cross-functional leadership, and establishing lifecycle accountability.
For enterprises, understanding these trends is not just about assessing cyber posture; it’s about safeguarding physical assets, protecting intellectual property, ensuring business continuity, and fulfilling societal responsibilities. For cybersecurity vendors, aligning offerings with these evolving needs is crucial to remain competitive. The new industrial revolution, powered by IT/OT convergence and AI, comes with a steep price if security is not prioritized from the outset. We must secure intelligence, not just infrastructure.
Is your organization ready to proactively secure its intelligent industrial future?
At IoT Worlds, we specialize in guiding businesses through the complexities of OT cybersecurity, IT/OT convergence, and AI integration. Our expert consultants help you assess your current posture, design resilient architectures, implement cutting-edge security solutions, and build the strategic governance required to protect your critical operations in an AI-driven world. Don’t let the expanded cyber attack surface put your operations at risk.
Contact us today for a personalized consultation and fortify your defenses:
Email: info@iotworlds.com