The world of cybersecurity is a thrilling, ever-evolving frontier, where innovation meets vigilance, and the stakes couldn’t be higher. From protecting critical infrastructure to safeguarding personal data, the professionals in this field are the unsung heroes of the digital age. But amidst the myriad of roles, responsibilities, and specializations, a question often arises: “Which cybersecurity job is the coolest?”
The truth is, the “coolest” job is a deeply personal one, influenced by individual passions, aptitudes, and motivations. What one person finds exhilarating, another might find daunting. This article will delve into the diverse and dynamic roles within cybersecurity, exploring what makes each unique and highlighting why the field is brimming with exciting opportunities for every kind of digital defender. We’ll consider factors like intellectual challenge, impact, visibility, and evolving demand, offering a comprehensive look at the careers that are not only in high demand but also genuinely fascinating.
The Allure of Cybersecurity: More Than Just a Salary
Before we dive into specific roles, it’s essential to understand the overarching appeal of a career in cybersecurity. It’s a field driven by a constant battle of wits, where professionals are tasked with anticipating, countering, and recovering from sophisticated threats. This intrinsic challenge, coupled with the tangible impact on society and business, creates a stimulating and rewarding professional journey.
High Demand and Evolving Opportunities
The cybersecurity landscape is characterized by a persistent talent gap. There were approximately 3.5 million unfilled cybersecurity jobs globally by the end of 2021, a number that has remained steady through 2025. This acute demand translates into significant career opportunities, competitive salaries, and a wide array of choices for aspiring professionals.
Furthermore, the rapid advancements in technology, particularly in areas like Artificial Intelligence (AI) and the Internet of Things (IoT), are continuously reshaping the cybersecurity paradigm. This means new roles are constantly emerging, and existing ones are evolving, ensuring that the field remains dynamic and engaging for years to come. For instance, the rise of AI has led to an explosion in demand for roles like “AI Security Engineer” and “AI Governance Lead,” even if the specific titles and definitions are still being ironed out.
The Intellectual Playground
For those who thrive on problem-solving, continuous learning, and intellectual stimulation, cybersecurity offers an unparalleled playground. Each day presents new puzzles to solve, new threats to analyze, and new defenses to build. The need to stay ahead of malicious actors requires constant skill development and a deep understanding of complex systems, making it an ideal field for those with an insatiable curiosity.
Impact and Purpose
Beyond the technical challenges, many cybersecurity professionals find immense satisfaction in the profound impact of their work. Protecting critical infrastructure, patient records, financial systems, and personal privacy provides a strong sense of purpose. Whether it’s preventing a major data breach or safeguarding a nation’s power grid, cybersecurity professionals play a crucial role in maintaining the security and stability of our increasingly digital world.
The Many Faces of Cool: Exploring Diverse Cybersecurity Roles
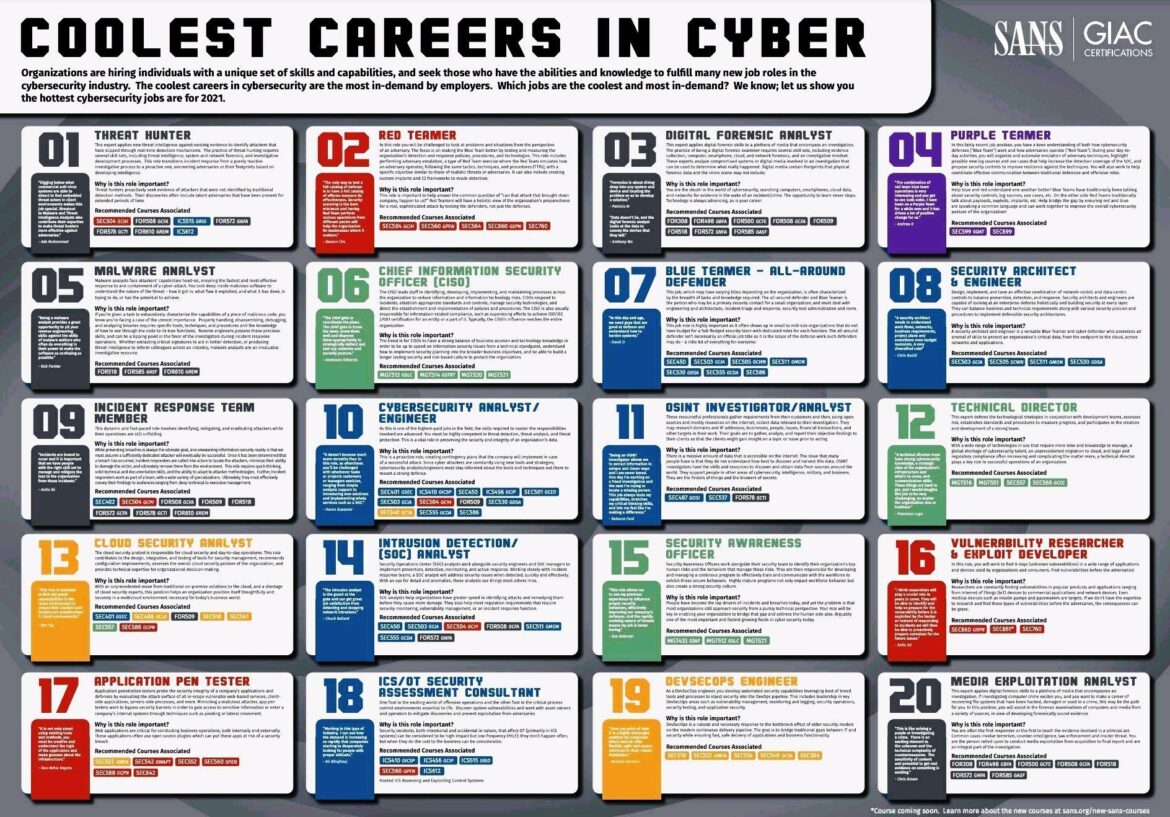
Let’s now explore a range of cybersecurity jobs, highlighting why each might be considered the “coolest” by different individuals. The following roles are representative of the breadth and depth of the cybersecurity landscape, embodying various aspects of technical expertise, strategic thinking, and practical application.
The Offensive Specialists: Ethical Hacking and Red Teaming
For many, the idea of being paid to legally “break into” systems holds an undeniable appeal. Ethical hackers and red teamers are the offensive specialists of the cybersecurity world, tasked with simulating real-world attacks to identify vulnerabilities before malicious actors can exploit them.
Ethical Hacker
An Ethical Hacker, often dubbed the “coolest job”, tests an organization’s cybersecurity defenses. This role combines a deep understanding of technology with a knack for problem-solving, requiring individuals to think like an adversary to uncover weaknesses.
Why it’s cool:
- Legal “Hacking”: The thrill of uncovering vulnerabilities without legal ramifications.
- Constant Challenge: Every system presents a unique puzzle to solve, demanding creativity and adaptability.
- Direct Impact: Directly contributes to strengthening an organization’s security posture.
Red Teamer
A Red Teamer takes ethical hacking a step further, conducting comprehensive, multi-layered simulated attacks that mimic realistic threat scenarios. This goes beyond simply finding vulnerabilities; it involves evaluating an organization’s overall defensive capabilities and response mechanisms.
Why it’s cool:
- Strategic Thinking: Involves planning and executing complex campaigns that test the human, process, and technological aspects of security.
- Advanced Techniques: Utilizes sophisticated tools and methodologies to bypass security controls.
- Realistic Simulation: Provides invaluable insights into an organization’s true security readiness.
The Defensive Guardians: Incident Response and Blue Teaming
On the other side of the digital battlefield are the defensive guardians – incident responders and blue teamers – who are dedicated to protecting systems and data from attacks, detecting intrusions, and leading the recovery effort following a security incident.
Incident Response Team Member
When a cyberattack strikes, the Incident Response Team is on the front lines. These professionals are responsible for identifying, mitigating, and eradicating threats while minimizing damage and ensuring a swift return to normal operations.
Why it’s cool:
- High-Stakes Problem Solving: Operates under pressure to contain and resolve critical security incidents.
- Digital Forensics: Utilizes investigative skills to analyze attack methods, identify compromised systems, and gather evidence.
- Direct Protection: Plays a vital role in protecting an organization’s assets and reputation during a crisis.
Blue Teamer – All-Around Defender
A Blue Teamer encompasses a broad range of defensive roles, working proactively to build robust security architectures, monitor for threats, and respond to incidents. This can include security analysts, security engineers, and security operations center (SOC) personnel.
Why it’s cool:
- Proactive Defense: Focuses on prevention and detection, building resilient systems that can withstand sophisticated attacks.
- Continuous Improvement: Constantly refines security controls and processes to adapt to evolving threats.
- Broad Skillset: Requires expertise across various security domains, from network security to endpoint protection.
The Strategic Architects: Security Architecture and Governance
Building a strong cybersecurity posture requires strategic foresight and a deep understanding of an organization’s overall risk profile. Security architects and governance leads are instrumental in designing secure systems and establishing robust security frameworks.
Security Architect & Engineer
A Security Architect designs and implements network-centric and data-centric security controls, ensuring that security is baked into systems from the ground up. They combine a strong technical background with a strategic vision to create secure and resilient infrastructures.
Why it’s cool:
- Foundation Builder: Lays the groundwork for an organization’s entire security posture.
- Innovation: Integrates cutting-edge security technologies into complex systems.
- High-Level Impact: Influences the overall security strategy and direction of an organization.
Chief Information Security Officer (CISO)
The CISO holds significant responsibility, leading the development, implementation, and maintenance of an organization’s information security program. This role requires a blend of technical expertise, business acumen, and leadership skills to manage risk and ensure compliance.
Why it’s cool:
- Executive Leadership: Operates at the highest levels of an organization, influencing strategic decisions.
- Broad Scope: Oversees all aspects of information security, from technical controls to policy and compliance.
- Business Impact: Directly contributes to the organization’s overall success by managing cybersecurity risk.
The Specialized Protectors: OT/ICS Security and AI Security
As technology continues to advance and converge, highly specialized cybersecurity roles are emerging to protect critical and unique environments.
OT/ICS Security Specialist / Engineer
Operational Technology (OT) and Industrial Control Systems (ICS) are the backbone of modern society, controlling everything from power grids and water treatment plants to manufacturing lines. An OT/ICS Security Specialist protects these vital systems from cyber threats. This field requires a unique blend of IT security knowledge and an understanding of industrial processes and protocols.
Why it’s cool:
- Protecting Critical Infrastructure: Directly safeguards essential services that impact human life and societal function.
- Unique Technical Challenges: Deals with heterogeneous, often legacy systems, and specialized industrial protocols like Modbus, DNP3, and OPC UA.
- Physical World Impact: A security failure can have tangible, real-world consequences, from physical damage to environmental harm, making the work profoundly impactful.
- AI-Resistant Specialty: OT/ICS security is highly resistant to AI displacement due to physical presence requirements, safety-critical liability, and the absence of viable AI tools for proprietary industrial protocols.
AI Security Engineer / AI Governance Lead
With the explosive growth of Artificial Intelligence, new cybersecurity challenges have emerged. AI Security Engineers and AI Governance Leads are at the forefront of securing AI systems, ensuring their integrity, preventing malicious manipulation, and addressing ethical implications. This is a rapidly evolving field with high demand and significant wage premiums.
Why it’s cool:
- Cutting-Edge Technology: Works with the latest advancements in AI and machine learning.
- New Frontier: Defines best practices and develops innovative solutions for securing AI systems.
- High Demand and Impact: Crucial for the responsible development and deployment of AI across industries.
The Investigative Minds: Digital Forensics and OSINT
For those with a penchant for investigation and unraveling digital mysteries, roles in digital forensics and Open Source Intelligence (OSINT) offer a compelling career path.
Digital Forensic Analyst
When a cyber incident occurs, a Digital Forensic Analyst steps in to meticulously collect, preserve, and analyze digital evidence. Their work is crucial for understanding how attacks happened, identifying perpetrators, and supporting legal proceedings.
Why it’s cool:
- Digital Detective Work: Utilizes advanced tools and techniques to reconstruct digital events and uncover hidden clues.
- Problem-Solving: Each case presents a unique puzzle, requiring keen analytical skills and attention to detail.
- Justice and Accountability: Plays a vital role in bringing cybercriminals to justice and preventing future attacks.
OSINT Investigator / Analyst
An OSINT Investigator leverages publicly available information from the internet and other sources to gather intelligence for cybersecurity purposes. This can include threat intelligence, vulnerability research, and supporting incident response efforts.
Why it’s cool:
- Information Gathering: Excels at extracting valuable insights from vast amounts of public data.
- Cross-Disciplinary: Combines cybersecurity knowledge with research skills, often delving into sociology, psychology, and geopolitics.
- Proactive Threat Intelligence: Helps organizations anticipate and prepare for emerging threats.
The Human Element: Security Awareness and Application Security
Beyond the technical controls, the human factor remains a critical component of cybersecurity. Roles focused on security awareness and application security address vulnerabilities introduced through human behavior and software development.
Security Awareness Officer
A Security Awareness Officer is responsible for educating employees about cybersecurity best practices, fostering a security-conscious culture, and mitigating risks associated with human error. This role is crucial for building a strong defense in depth.
Why it’s cool:
- Behavioral Psychology: Understands how to influence human behavior to improve security.
- Creative Communication: Develops engaging training programs and campaigns to promote security awareness.
- Broad Impact: Empowers every employee to become a part of the security solution.
Application Pen Tester / Vulnerability Researcher & Exploit Developer
Application Penetration Testers assess the security of software applications, identifying vulnerabilities that could be exploited by attackers. Vulnerability Researchers and Exploit Developers go even deeper, discovering new vulnerabilities in software and developing proof-of-concept exploits.
Why it’s cool:
- Direct Impact on Software Security: Ensures that the applications we rely on are robust against attacks.
- Continuous Learning: Stays abreast of the latest software vulnerabilities and exploitation techniques.
- Creative Problem Solving: Thinks outside the box to uncover hidden weaknesses in code.
The Convergence Roles: Cloud Security and DevOps
As IT infrastructure shifts towards cloud-native architectures and agile development methodologies, new cybersecurity roles are emerging to address the unique challenges of these environments.
Cloud Security Analyst
With the increasing adoption of cloud services, a Cloud Security Analyst specializes in securing cloud environments, ensuring data privacy, compliance, and protection against cloud-specific threats.
Why it’s cool:
- Emerging Technology: Works with cutting-edge cloud platforms and services.
- Scalable Impact: Secures vast and dynamic cloud infrastructures.
- Continuous Evolution: Adapts to the rapidly changing landscape of cloud security.
DevSecOps Engineer
A DevSecOps Engineer integrates security practices into the entire software development lifecycle, automating security controls and ensuring that security is a continuous process from design to deployment.
Why it’s cool:
- Automation and Efficiency: Streamlines security processes and reduces manual effort.
- Collaborative Environment: Works closely with development and operations teams to build secure software.
- Proactive Security: Shifts securityleft, embedding it early in the development pipeline.
The Future of Cybersecurity: New Horizons and Evolving Skillsets
The cybersecurity landscape is not static; it’s a dynamic field that is constantly evolving in response to new technologies, emerging threats, and shifting regulatory environments. Looking ahead, several trends will continue to shape the “coolest” jobs in cybersecurity.
The Rise of AI in Cybersecurity
Artificial Intelligence is both a tool and a target in cybersecurity. While AI can enhance threat detection and response capabilities, it also introduces new attack vectors and ethical considerations. The demand for professionals who can secure AI systems, develop AI-powered security tools, and understand the implications of AI in cyber warfare will continue to soar. This includes roles in AI security, machine learning security, and AI governance.
OT/ICS Security: A Strategic Imperative
The convergence of IT and OT environments, coupled with the increasing digitalization of industrial processes, has made OT/ICS security a top priority. Protecting critical infrastructure from cyberattacks is a national security concern, and the demand for skilled OT/ICS security professionals will only intensify. This unique specialization, combining IT security with industrial automation knowledge, will remain a “cool” and highly impactful field. We highlight the critical need for specialized skills in this area for 2026.
Quantum Security: Preparing for the Post-Quantum Era
As quantum computing advances, it poses both opportunities and threats to current cryptographic standards. Quantum security specialists will be crucial in developing post-quantum cryptography, securing quantum systems, and understanding the implications of quantum technology for cybersecurity. This will be a frontier role, demanding groundbreaking research and innovation.
Cyber-Physical Security: Bridging the Divide
The increasing interconnectedness of the digital and physical worlds means that cyber-physical security will become even more critical. This involves protecting systems that interact with the physical environment, such as autonomous vehicles, smart cities, and medical devices. Professionals in this area will blend cybersecurity expertise with knowledge of physics, engineering, and robotics.
How to Find Your “Cool” in Cybersecurity
The beauty of cybersecurity lies in its vastness and diversity. There’s a niche for almost every interest and skill set. To find your “cool” cybersecurity job, consider the following:
- Self-Reflection: What aspects of technology do you genuinely enjoy? Do you prefer offensive or defensive strategies? Are you drawn to technical deep dives or strategic leadership? Do you want to work with cutting-edge AI, or protect foundational industrial systems?
- Skill Development: Identify the skills required for the roles that pique your interest and actively pursue training and certifications. Resources from organizations like SANS/GIAC provide structured learning paths for many cybersecurity specializations.
- Continuous Learning: Cybersecurity is a field of constant evolution. Embrace a mindset of lifelong learning to stay relevant and ahead of emerging threats.
- Networking: Connect with professionals in the field, attend industry events, and join online communities. Their insights and experiences can be invaluable in guiding your career path.
- Hands-on Experience: Practical experience is paramount. Participate in cybersecurity competitions, contribute to open-source projects, or seek internships to gain real-world skills.
Conclusion: Your Passion Defines “Cool”
Ultimately, the coolest cybersecurity job is the one that aligns with your passions, challenges your intellect, and provides you with a sense of purpose and fulfillment. Whether it’s the thrill of ethical hacking, the intricate puzzle of digital forensics, the strategic defense of critical infrastructure, or the cutting-edge work of securing AI, the cybersecurity field offers an abundance of opportunities for a rewarding and impactful career. The sector is booming, with unprecedented demand and continuous innovation, making it an opportune time to enter or advance within this vital domain.
As the digital world continues to expand and evolve, so too will the need for dedicated and skilled cybersecurity professionals. The future is bright for those who choose to stand on the front lines of digital defense, shaping the security landscape and protecting the world around us.
Ready to explore the evolving landscape of OT/ICS cybersecurity and other critical security domains?
Contact us today to learn how IoT Worlds can help you navigate these complex challenges and secure your interconnected future.
Email us at info@iotworlds.com and let’s start a conversation about protecting your most valuable assets.