The world of Industrial IoT (IIoT) is often viewed through the lens of high-bandwidth sensors and complex edge computing. However, the backbone of modern digital transformation, traceability, and supply chain visibility remains a technology that has been quietly evolving for decades: Radio Frequency Identification (RFID).
As enterprises transition toward Industry 4.0, understanding RFID fundamentals is no longer optional for project managers, engineers, or digital transformation leaders. This comprehensive guide explores the physics, architecture, and strategic integration of RFID systems, bridging the gap between physical assets and the digital enterprise (WMS, ERP, and MES).
The Physics of Radio Frequency Identification
At its core, RFID is a wireless communication technology that uses electromagnetic fields to automatically identify and track tags attached to objects. Unlike barcodes, RFID does not require a direct line of sight and can read hundreds of items simultaneously.
The Anatomy of an RFID System
Every RFID deployment consists of three primary physical components and a vital software layer:
- The Tag (Transponder): Consists of an integrated circuit (IC) and an antenna.
- The Reader (Interrogator): A device that emits radio waves and receives signals back from the tag.
- The Antenna: The interface that converts electrical signals into electromagnetic waves.
- The Middleware: The software layer that filters raw data and integrates it into business systems.
Coupling Mechanisms: Inductive vs. Radiative
The way energy is transferred from the reader to the tag dictates the performance and range of the system.
Inductive Coupling (Near-Field)
Used primarily in Low Frequency (LF) and High Frequency (HF) systems. The reader’s antenna creates a magnetic field. When a tag enters this field, it draws energy via induction to power its chip and modulate the field to send data back. This is highly effective near water or metal but is limited to short distances.
Radiative Coupling (Far-Field)
Used in Ultra-High Frequency (UHF) systems. The reader emits electromagnetic waves that “propagate” through the air. The tag captures a portion of this energy and “backscatters” a signal to the reader. This allows for long-read ranges (up to 12+ meters) and high-speed data transfer.
Frequency Spectrum: LF, HF, NFC, and UHF
Choosing the right frequency is the most critical decision in an RFID project. Each band has unique characteristics regarding read range, data rate, and environmental interference.
Low Frequency (LF): 125 – 134 kHz
LF systems were among the first to be commercialized. They operate via inductive coupling and have a very short read range (usually less than 10 cm).
- Pros: Highly resistant to interference from metal and liquids.
- Cons: Extremely slow data transfer rates and higher tag costs due to copper coil requirements.
- Primary Use Cases: Animal tracking (microchips), car immobilizers, and basic access control in harsh industrial environments.
High Frequency (HF): 13.56 MHz
HF RFID is the standard for secure, proximity-based communication. It offers a moderate read range (up to 1 meter) and better data speeds than LF.
- Pros: Global standardized frequency; excellent for secure data transmission.
- Cons: Sensitivity to large metal objects.
- Near-Field Communication (NFC): A subset of HF RFID designed for two-way communication between smartphones and tags. NFC is the gold standard for contactless payments and consumer engagement.
Ultra-High Frequency (UHF): 860 – 960 MHz
UHF (specifically Rain RFID) is the workhorse of the logistics and retail industries. It employs radiative coupling and offers massive read ranges and high-speed bulk reading.
- Pros: Can read hundreds of tags per second at distances of over 10 meters; low cost per tag.
- Cons: Highly sensitive to “RF-opaque” materials like water (which absorbs signals) and metal (which reflects them).
- Regional Variations: Frequency bands differ slightly by geography (e.g., 865-868 MHz in Europe vs. 902-928 MHz in the US), requiring “Global” tags for international shipping.
Hardware Architecture: Tags, Antennas, and Readers
The synergy between hardware components determines the reliability of an RFID “Read Zone.”
Tag Classification: Passive, Active, and BAP
Tags are categorized by how they are powered:
- Passive Tags: Have no internal battery. They remain “dormant” until powered by the reader’s signal. They are inexpensive and can last indefinitely.
- Active Tags: Contain a battery and a transmitter. They broadcast their signal autonomously, offering ranges of 100+ meters. They are expensive and used for high-value asset tracking (e.g., shipping containers).
- Battery-Assisted Passive (BAP): Contain a battery to power the chip’s internal logic, but still use backscatter for communication. This improves read reliability in difficult environments.
Antenna Layouts and Polarization
The antenna’s job is to shape the RF field. Its “Polarization” must match the tag’s orientation for optimal performance.
Linear Polarization
The radio waves travel in a single plane (vertical or horizontal).
- Advantage: Longer range and higher power density.
- Requirement: The tag must be aligned perfectly with the antenna.
Circular Polarization
The radio waves rotate as they travel.
- Advantage: It will read tags in any orientation (horizontal, vertical, or tilted).
- Trade-off: Shorter read range compared to linear antennas of the same size.
Reader Configuration: Fixed vs. Handheld
- Fixed Readers: Mounted at “choke points” (dock doors, conveyor belts). They provide consistent, automated data capture.
- Handheld Readers: Integrated with mobile computers for manual inventory counts, search-and-find tasks, and “exception” handling.
Integration Challenges: Physics vs. Logic
Implementing RFID is not “plug-and-play.” It requires balancing environmental physics with digital logic.
Environment and Material Interference
The “enemies” of RFID are liquids and metals.
- Absorption: Water (content in food, chemicals, or the human body) absorbs UHF signals, killing the read range.
- Reflection: Metal reflects RF waves, causing “multipath” interference or creating “dead zones.”
- Mitigation: Specialist “on-metal” tags use a spacer or ceramic backing to prevent the metal from detuning the antenna.
Anti-Collision and Read Rates
In a warehouse, a reader might see 500 tags simultaneously.
- Tag Collision: Occurs when multiple tags respond at the same time. RFID protocols (like EPC Gen2) use “Slotted Aloha” algorithms to negotiate which tag speaks when.
- Reader Collision: Occurs when overlapping fields from two readers interfere. This is managed via “Dense Reader Mode” and synchronization.
Read Range Optimization (d)
The theoretical read range of a passive UHF system can be approximated by the Friis Transmission Equation. While complex, the simplified relationship is:
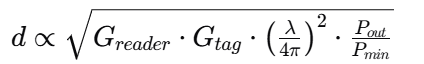
Where:
- G is Antenna Gain.
- λ is Wavelength.
- Pout is Transmitter Power.
- Pmin is the minimum power required to wake the tag.
Project managers must optimize these variables through site surveys and hardware selection.
Strategic Use Cases: UHF for Logistics
In the logistics sector, UHF RFID provides the “granular visibility” required for Just-In-Time (JIT) manufacturing and omnichannel retail.
Dock Door Automation
When a pallet passes through a dock door equipped with fixed UHF readers, the system automatically verifies the contents against the Advanced Shipping Notice (ASN).
- Value: Eliminates manual scanning, reduces shipping errors, and accelerates the “Receive-to-Stock” cycle.
- Challenge: Implementing “Shielding” to ensure the reader doesn’t accidentally read tags inside the warehouse while a truck is being loaded.
Real-Time Inventory and “The Last Mile”
Retailers use UHF RFID to maintain 99% inventory accuracy. Handheld readers allow staff to count a store’s stock in minutes rather than hours. This data is fed into the WMS to trigger replenishment and enable “Buy Online, Pick Up In-Store” (BOPIS) services.
Strategic Use Cases: HF/NFC for Access Control and Authentication
Where UHF excels in volume and distance, HF excels in security and proximity.
Secure Access Control
HF (13.56 MHz) is used for corporate badges and secure facility entry.
- Encryption: Unlike standard UHF tags, HF chips (such as MIFARE or HID iClass) support cryptographic keys, preventing “tag cloning.”
- Proximity: The short read range is a security feature; it ensures the user intentionally presented their card to the reader.
Brand Protection and Anti-Counterfeiting
Luxury brands embed NFC tags into products. A consumer can tap their smartphone against a handbag or bottle of wine to verify its authenticity through a digital certificate stored on the blockchain. This creates a direct-to-consumer marketing channel that persists after the sale.
The Role of Middleware: From Raw Data to Business Intelligence
An RFID reader generating 1,000 reads per second creates “data noise.” Middleware is the critical layer that cleanses this data.
Data Filtering and Grouping
Middleware identifies that the 10,000 “pings” from a single tag over 10 seconds represent just one “Event” (e.g., Tag X entered Portal Y at 10:00 AM). It filters out “stray reads” from tags that just happened to be near the field but were not the target.
IT-OT Interoperability
The Middleware translates low-level reader protocols (like LLRP – Low-Level Reader Protocol) into high-level enterprise languages (JSON, XML, or MQTT). This allows the RFID system to communicate directly with an SAP ERP or an Azure IoT Hub, enabling a “Digital Twin” of the entire supply chain.
Design and Layout: Planning for Success
A successful RFID deployment requires a “Site Survey” and phased testing.
- Process Mapping: Identify exactly where an “automated read” adds value. Don’t tag everything; tag where visibility is lost.
- Tag Placement Testing: Test tags on the specific packaging. The “center-of-gravity” isn’t always the best spot; factors like moisture content in the product matter.
- Proof of Concept (PoC): Test with 10 tags in a controlled environment.
- Pilot: Test a single dock door or a single production line in the real world to identify environmental interference.
- Full Scale: Standardize hardware and roll out across the enterprise.
Conclusion: The Future of Connected Assets
RFID Fundamentals are the building blocks of a transparent enterprise. By bridging the gap between physical movement and digital records, RFID enables companies to move from reactive management to predictive optimization. Whether it is UHF for the global supply chain or HF for secure authentication, the technology provides the “Ground Truth” that AI and Big Data analytics require to be effective.
As the costs of tags continue to fall and the sensitivity of readers continues to rise, the integration of RFID into the broader Internet of Things (IoT) ecosystem will only accelerate. The question is no longer if you should use RFID, but how you will integrate it to gain a competitive edge.
Transform Your Business with IoT Worlds
Navigating the complexities of RFID integration, IT-OT convergence, and Industrial IoT requires more than just hardware—it requires strategic vision and technical expertise. At IoT Worlds, we help Fortune 500 companies and growing SMEs design, secure, and deploy world-class IoT ecosystems.
Whether you need a comprehensive RFID site survey, a cybersecurity audit for your OT infrastructure, or a roadmap for your digital transformation, our team of expert consultants is ready to guide you.
Contact us today to schedule a consultation.
Email: info@iotworlds.com
Let’s build the future of connected industry together.

