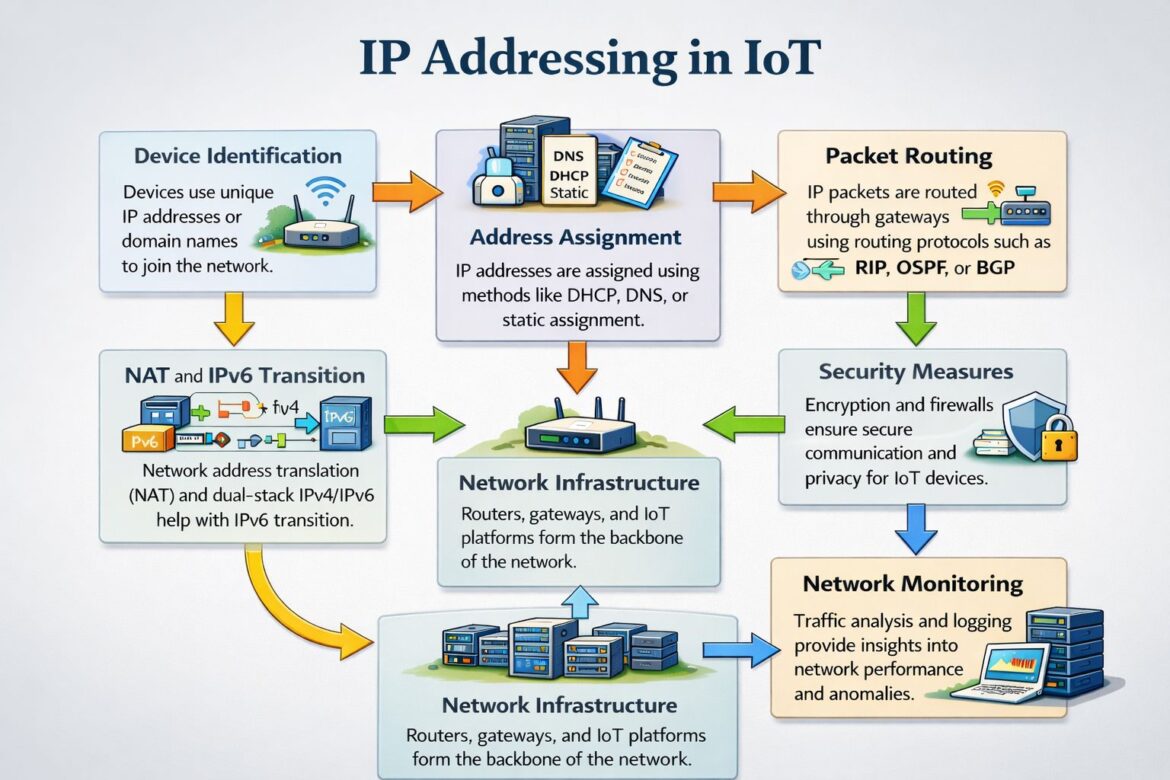
The Internet of Things (IoT) is no longer a futuristic concept; it’s a present-day reality rapidly transforming industries, homes, and cities worldwide. From smart thermostats in our living rooms to complex industrial sensors monitoring factory floors, billions of devices are now interconnected, generating unprecedented volumes of data and enabling a new era of automation and intelligence. At the heart of this intricate web of connectivity lies IP addressing – the fundamental mechanism that allows every single IoT device to be uniquely identified, communicate with other devices, and participate in the global internet.
In large-scale IoT ecosystems, IP addressing transcends mere identification. It becomes the bedrock for structured communication, ensuring efficient routing of data packets, and enabling robust security and seamless device management. As the number of connected devices continues its exponential growth, understanding and implementing sound IP addressing strategies are paramount for building resilient, scalable, and secure IoT architectures. This comprehensive article delves into the critical aspects of IP addressing in IoT, exploring its nuances, challenges, and best practices for success.
The Pillars of IoT Connectivity: Unique Identification and Communication
Every device within an IoT network, regardless of its size or function, requires a unique identity to be recognized and interacted with. This identity is primarily established through its IP address. Just as a physical address directs mail to a specific house, an IP address guides data packets to their intended IoT device. Without unique identification, the entire concept of a connected “thing” would crumble.
Unique Device Identification Using IPv4/IPv6
The two primary protocols governing IP addressing are IPv4 (Internet Protocol version 4) and IPv6 (Internet Protocol version 6).
The Enduring Legacy of IPv4
IPv4 has served as the backbone of the internet for decades. It utilizes a 32-bit addressing scheme, providing approximately 4.3 billion unique addresses. While this number seemed vast at the internet’s inception, the explosion of connected devices, particularly with the advent of IoT, has brought IPv4 to its limits.
An IPv4 address is typically represented as four decimal numbers separated by dots (e.g., 192.168.1.1). These addresses are further divided into network and host portions, determined by a subnet mask. This division allows for the creation of smaller, manageable networks within a larger IP address space.
Despite its limitations, IPv4 remains widely deployed due to its entrenchment in existing infrastructure. However, the scarcity of available IPv4 addresses has necessitated various workarounds, such as Network Address Translation (NAT), which we will discuss later.
The Future-Proofing Power of IPv6
IPv6 was developed to address the inherent limitations of IPv4, primarily the exhaustion of address space. It employs a 128-bit addressing scheme, offering an astronomically large number of unique addresses – approximately 3.4×1038. This immense address space virtually eliminates the concern of address scarcity for the foreseeable future, making it an ideal candidate for the ever-expanding IoT landscape.
An IPv6 address is typically represented as eight groups of four hexadecimal digits separated by colons (e.g., 2001:0db8:85a3:0000:0000:8a2e:0370:7334). IPv6 also introduces several enhancements beyond just address space, including improved routing efficiency, built-in security features (IPsec), and simplified auto-configuration.
For IoT, the vastness of IPv6 addresses offers significant advantages:
- Global Addressability: Every single IoT device can have a unique, globally routable IP address, simplifying direct communication and eliminating the need for complex NAT configurations.
- Simplified Device Management: Direct end-to-end connectivity streamlines remote management, monitoring, and troubleshooting of individual devices.
- Enhanced Security: Built-in IPsec provides robust cryptographic protection for data packets, contributing to a more secure IoT ecosystem.
- Scalability: The virtually limitless address space ensures that IoT deployments can scale to accommodate billions, even trillions, of devices without hitting IP address bottlenecks.
Dynamic or Static Address Allocation Mechanisms
Once a device is identified, it needs an IP address assigned to it. This assignment can occur through dynamic or static mechanisms, each with its own set of advantages and disadvantages.
Dynamic Host Configuration Protocol (DHCP)
DHCP is the most common method for dynamic IP address allocation in modern networks, including many IoT environments. It automates the process of assigning IP addresses, subnet masks, default gateways, and DNS server information to devices as they connect to the network.
Here’s how DHCP typically works:
- Discovery: When an IoT device connects to a network, it broadcasts a DHCP Discover message to locate a DHCP server.
- Offer: The DHCP server responds with a DHCP Offer message, proposing an available IP address and other configuration parameters.
- Request: The IoT device sends a DHCP Request message to accept the offered IP address.
- Acknowledgement: The DHCP server sends a DHCP Acknowledge message, confirming the IP address assignment and the lease duration.
The lease duration specifies how long the device can use the assigned IP address. Before the lease expires, the device will typically attempt to renew it. If renewal fails, the device must obtain a new IP address.
Advantages of DHCP in IoT:
- Simplified Administration: DHCP significantly reduces the administrative burden of manually configuring IP addresses for a large number of IoT devices.
- Efficient Address Management: It dynamically allocates and reclaims IP addresses, preventing address conflicts and optimizing address space utilization.
- Flexibility: Devices can easily move between networks and obtain new IP configurations automatically.
Disadvantages of DHCP in IoT:
- Dependence on DHCP Server: The availability and proper functioning of the DHCP server are critical. If the server goes down, new devices cannot obtain IP addresses.
- Lack of Permanent Identification (by IP): While a device can typically retain the same IP across lease renewals, its IP address is not truly static. For certain applications requiring a consistent IP for a specific device, this can be a drawback.
- Security Concerns: Rogue DHCP servers can be a security risk, potentially leading to unauthorized IP assignments or denial-of-service attacks.
Static IP Address Assignment
Static IP addressing involves manually configuring a fixed IP address for each IoT device. This means the device will always use the same IP address every time it connects to the network.
Advantages of Static IP in IoT:
- Consistent Identification: Ideal for devices that require constant, predictable access, such as critical infrastructure sensors, security cameras, or servers.
- Simplified Troubleshooting: Knowing the exact IP address of a device simplifies diagnosis and remote access.
- Enhanced Security (in some contexts): By explicitly defining which devices can use which IP addresses, it can contribute to a more controlled network environment.
Disadvantages of Static IP in IoT:
- High Administrative Overhead: Manually configuring and managing hundreds or thousands of IoT device IP addresses is immensely time-consuming and error-prone.
- Scalability Challenges: As the number of devices grows, static IP management becomes unfeasible.
- Address Conflicts: Careful planning is essential to avoid assigning the same IP address to multiple devices, which can lead to network disruptions.
- Requires Expertise: Network administrators need a thorough understanding of network topology and subnetting to effectively manage static IP assignments.
The choice between dynamic and static IP addressing for IoT largely depends on the specific application, scale of deployment, and operational requirements. For consumer IoT devices and large-scale deployments with less critical individual device accessibility, DHCP is often the preferred choice. For mission-critical devices or those requiring direct, persistent access, static IP addresses may be more suitable, often within carefully segregated network segments.
Routing Efficiency: Guiding Data Through the IoT Maze
Once an IoT device has an IP address, its data needs to travel efficiently across the network to its destination, whether that’s a cloud platform, another IoT device, or a central gateway. This is where routing comes into play. Efficient routing is crucial for ensuring low latency, high throughput, and reliable communication in IoT ecosystems.
Efficient Routing Through Gateways and Edge Networks
IoT networks often feature a hierarchical architecture. At the lowest level are the end-devices, which typically communicate with a local gateway. The gateway acts as an intermediary, aggregating data from multiple devices, performing local processing (edge computing), and then forwarding the aggregated or processed data upstream to the cloud or other central systems.
The Role of IoT Gateways
IoT gateways are fundamental to efficient routing in many IoT deployments. They bridge the gap between resource-constrained IoT devices and the broader internet.
Key functions of an IoT gateway related to routing:
- Protocol Translation: IoT devices often use various short-range communication protocols (e.g., Zigbee, Z-Wave, Bluetooth Low Energy, LoRaWAN) that are not IP-based. Gateways translate these protocols into IP for onward transmission.
- Data Aggregation and Filtering: Gateways can collect data from multiple devices, aggregate it, and filter out irrelevant information, reducing the amount of data sent upstream. This optimizes bandwidth usage and reduces cloud processing costs.
- Edge Computing: By performing local data processing and analytics, gateways reduce the reliance on the cloud for real-time decision-making, improving responsiveness and reducing latency.
- Security Enforcement: Gateways can implement local firewall rules, authentication, and encryption to protect the downstream IoT devices.
- Routing: Gateways act as local routers, directing traffic between connected IoT devices and to the wider network.
Routing Protocols
For efficient packet routing within and between networks, various routing protocols are employed. These protocols determine the best path for data packets to reach their destination.
- Routing Information Protocol (RIP): A distance-vector routing protocol that uses hop count as its metric. While simple, RIP is generally not well-suited for large, complex IoT networks due to its slow convergence and limited hop count (maximum 15 hops). It might find niche uses in very small, simple IoT segments.
- Open Shortest Path First (OSPF): A link-state routing protocol that is much more scalable and efficient than RIP. OSPF establishes a robust map of the network topology, allowing it to calculate the shortest path based on various metrics (e.g., bandwidth, delay). OSPF can be highly effective in larger IoT deployments, especially within enterprise networks connecting multiple IoT segments. Its rapid convergence and hierarchical capabilities make it suitable for more complex routing needs.
- Border Gateway Protocol (BGP): The inter-domain routing protocol of the internet. BGP is used to exchange routing information between different autonomous systems (AS_es), which are large, independent networks. While unlikely to be directly implemented on individual IoT gateways, BGP is crucial for how data from IoT cloud platforms and large-scale IoT backbones traverse the global internet. Cloud providers and large IoT service platforms use BGP to connect to other networks and ensure their IoT traffic reaches its destination efficiently across the global internet.
The choice of routing protocol depends heavily on the scale, topology, and performance requirements of the IoT deployment. Within a local IoT edge network, simpler protocols or static routes might suffice. For more complex and interconnected IoT architectures, dynamic routing protocols like OSPF become essential.
Scalability and Transition: Navigating the IPv4/IPv6 Divide
The sheer number of devices in IoT mandates solutions for scalability. This brings us to the critical strategies of Network Address Translation (NAT) and the ongoing transition from IPv4 to IPv6.
NAT and IPv6 Transition Strategies for Scalability
With the limited availability of IPv4 addresses, NAT became a widely adopted mechanism to allow multiple devices to share a single public IP address. However, for the future of IoT, a full transition to IPv6 is the ultimate solution for true scalability and direct addressability.
Network Address Translation (NAT)
NAT is a process where the private IP addresses of devices within a local network are mapped to a public IP address when they communicate with devices outside the local network (e.g., on the internet). This effectively “hides” the internal network’s structure from the outside world and allows many devices to share a limited number of public IPv4 addresses.
How NAT works in the context of IoT:
An IoT gateway often performs NAT. Internal IoT devices are assigned private IPv4 addresses (e.g., in the 192.168.x.x range). When these devices send data to a cloud service, the gateway translates their private source IP address to its own public IP address. When a response comes back, the gateway translates the destination public IP back to the original private IP of the IoT device.
Advantages of NAT in IoT:
- IPv4 Address Conservation: Crucial for extending the life of IPv4 by allowing numerous IoT devices to share a few public addresses.
- Security (Perceived): By obscuring the internal network topology, NAT can offer a basic layer of security, making it harder for external entities to directly target individual internal devices.
Disadvantages of NAT in IoT:
- Breaks End-to-End Connectivity: Devices behind NAT cannot be directly accessed from the internet without complex port forwarding configurations. This makes peer-to-peer communication between IoT devices difficult and complicates remote device management and troubleshooting.
- Increased Complexity: Maintaining NAT mappings, especially in dynamic environments, adds complexity to network management.
- Performance Overhead: NAT translation adds a slight delay and processing overhead to every packet.
- Application Protocol Incompatibility: Some older protocols or applications do not interact well with NAT environments.
Dual-Stack IPv4/IPv6 Support
The transition from IPv4 to IPv6 is not an overnight process. It’s a gradual evolution, and dual-stack implementation is a key strategy for ensuring interoperability during this transition period.
Dual-stack refers to a network device or host that runs both IPv4 and IPv6 protocols concurrently. This means it has both an IPv4 address and an IPv6 address and can communicate with other devices using either protocol.
Advantages of dual-stack in IoT:
- Seamless Transition: Allows IoT devices and infrastructure to communicate with both IPv4-only and IPv6-only networks.
- Interoperability: Ensures that existing IPv4-based systems can continue to function while new IPv6-enabled devices are integrated.
- Future-Proofing: Prepares the IoT ecosystem for a full IPv6 future without immediately abandoning legacy IPv4 investments.
Implementation of Dual-Stack in IoT:
IoT gateways, routers, and host devices can be configured to support dual-stack. This typically involves running both IPv4 and IPv6 protocol stacks, assigning both types of addresses, and ensuring that routing mechanisms can handle both. When a dual-stack device needs to communicate, it can choose whether to use IPv4 or IPv6 based on the destination’s capabilities or configured preferences.
IPv6 Transition Mechanisms
Beyond dual-stack, other mechanisms facilitate the IPv6 transition, especially for devices or networks that only support one protocol but need to communicate with the other.
- Tunnelling: Encapsulates IPv6 packets within IPv4 packets (or vice versa) to traverse an incompatible network segment. This allows IPv6 traffic to pass over an IPv4-only network.
- Translation (NAT64/DNS64): Allows IPv6-only clients to communicate with IPv4-only servers. NAT64 translates IPv6 packets to IPv4 packets and vice versa, while DNS64 synthesizes IPv6 addresses for IPv4-only hosts. This is particularly relevant for IoT devices that might be IPv6-native but need to access legacy IPv4 cloud services.
Strategically deploying these transition mechanisms ensures that the ever-growing number of IoT devices can leverage the scalability of IPv6 while maintaining compatibility with the existing IPv4 internet.
Fortifying the IoT Perimeter: Security Through IP Management
The interconnected nature of IoT makes it a prime target for cyberattacks. A single compromised device can serve as an entry point for malicious actors to infiltrate an entire network. Therefore, implementing robust security measures, deeply integrated with IP addressing and network policies, is paramount.
Secure Communication Through Encryption and Firewall Policies
Securing IoT communication involves multiple layers, ranging from encrypting data in transit to meticulously controlling network access through firewall policies.
Encryption Protocols
Encryption is the cornerstone of secure communication, transforming data into a scrambled format that can only be deciphered by authorized parties with the correct key. For IoT, this is critical to protect sensitive data collected by sensors, control commands sent to actuators, and device credentials.
Common encryption protocols and technologies in IoT:
- Transport Layer Security (TLS) / Secure Sockets Layer (SSL): These protocols are widely used to establish secure communication channels over a network. TLS/SSL encrypts the data exchanged between an IoT device and a server (e.g., a cloud platform), ensuring confidentiality and integrity. Many IoT platforms and message brokers (like MQTT brokers) leverage TLS for secure connections.
- Datagram Transport Layer Security (DTLS): A version of TLS adapted for datagram-based protocols (like UDP), which are often used in resource-constrained IoT environments due to their lower overhead. DTLS provides similar security guarantees to TLS for unreliable transport protocols.
- IPsec (IP Security): A suite of protocols that provide security services at the IP layer. IPsec can authenticate and encrypt every IP packet, providing strong end-to-end security. It’s often used for Virtual Private Networks (VPNs) and can be implemented directly on IoT devices or gateways, especially in IPv6 networks where it’s a mandatory component.
- Elliptic Curve Cryptography (ECC): A public-key cryptography approach that offers strong security with smaller key sizes compared to traditional RSA, making it suitable for resource-constrained IoT devices.
The implementation of encryption must be carefully considered, balancing security requirements with the computational and energy constraints of individual IoT devices. Strong encryption protects the data from eavesdropping and tampering as it traverses the network, regardless of the underlying IP addressing scheme.
Firewall Policies
Firewalls act as digital gatekeepers, controlling network traffic based on predefined security rules. In IoT, firewalls are essential for protecting devices from unauthorized access and preventing malicious traffic from entering or leaving the network.
Key aspects of firewall policies in IoT:
- Stateful Inspection: Modern firewalls track the state of network connections, allowing legitimate response traffic to pass through while blocking unsolicited incoming connections.
- Port Filtering: Restricting communication to only necessary ports (e.g., port 8883 for secure MQTT, port 443 for HTTPS) minimizes the attack surface.
- IP Address Filtering: Firewalls can be configured to allow or deny traffic based on the source or destination IP addresses. This is crucial for:
- Whitelisting: Only allowing communication from known and trusted IP addresses (e.g., IoT cloud platform IP ranges).
- Blacklisting: Blocking traffic from known malicious IP addresses.
- Network Segmentation: Isolating IoT devices into separate network segments with strict firewall rules between them prevents a compromise in one segment from easily spreading to others.
- Device-Specific Rules: Tailoring firewall rules for specific IoT devices based on their function and communication patterns. For example, a temperature sensor might only be allowed to send data to a specific central server, not receive arbitrary incoming connections.
- Intrusion Detection/Prevention Systems (IDS/IPS): Often integrated with firewalls, these systems monitor network traffic for suspicious patterns and can block attacks in real-time.
- Application Layer Firewalls (AL-Fs): For more advanced protection, AL-Fs can inspect the content of application-layer protocols (like HTTP or MQTT) to detect and block threats specific to those applications.
Effective firewall policies, combined with strong encryption, form a formidable defense against a wide range of cyber threats targeting IoT deployments. They are critical elements in an “assume breach” security posture, limiting the impact even if an attacker manages to gain a foothold.
The Watchful Eye: Continuous Network Monitoring
Beyond initial setup and configuration, continuous monitoring is vital for maintaining the health, performance, and security of any large-scale IoT ecosystem. IP addressing plays a crucial role in enabling effective monitoring, as every data flow originates from or targets a specific IP.
Continuous Network Monitoring for Performance and Anomaly Detection
Constant vigilance over network activities allows for proactive identification of issues, optimization of performance, and early detection of security breaches or abnormal device behavior.
Traffic Analysis and Logging
Comprehensive traffic analysis and logging provide the raw data necessary for effective network monitoring.
Key aspects of traffic analysis and logging in IoT:
- Packet Capture and Analysis: Specialized tools can capture and analyze network packets to understand communication patterns, identify protocol errors, and troubleshoot connectivity issues. This helps in verifying if data is flowing as expected between specific IP addresses.
- Flow Data (NetFlow/IPFIX): Devices like routers and switches can export flow data, which summarize network traffic sessions (source IP, destination IP, ports, protocols, timestamps, data volume). Analyzing flow data provides high-level insights into network usage, bandwidth consumption by different IoT devices, and overall traffic patterns. This helps identify which IP addresses are communicating most frequently or consuming the most resources.
- Device Logs: IoT devices themselves, gateways, and cloud platforms generate logs that record events, errors, and security alerts. These logs often include IP addresses associated with specific events. Centralized log management systems are essential for correlating these diverse logs and gaining a holistic view of the system.
- Protocol Analysis: Understanding the specific IoT protocols (e.g., MQTT, CoAP, AMQP) in use and analyzing their traffic helps optimize network configurations and troubleshoot application-level issues.
Performance Metrics
Monitoring key performance indicators (KPIs) is essential for ensuring the reliable operation of IoT devices and applications.
Important performance metrics related to IP addressing and connectivity:
- Latency: The time it takes for data to travel from an IoT device to its destination (e.g., cloud platform) and back. High latency can indicate network congestion, inefficient routing, or issues with specific gateways or IP paths.
- Throughput: The amount of data successfully transmitted over a network connection in a given period. Low throughput for an IoT device or gateway might suggest bandwidth limitations or network bottlenecks.
- Packet Loss: The percentage of data packets that fail to reach their destination. High packet loss directly impacts the reliability of IoT communication and can be indicative of network instability or routing problems.
- Jitter: Variation in the delay of received packets, which can affect real-time IoT applications (e.g., industrial control, video streaming).
- Uptime/Availability: The percentage of time that IoT devices, gateways, and network infrastructure are operational and reachable via their IP addresses.
- IP Address Conflicts: Monitoring for multiple devices claiming the same IP address, which can lead to severe network disruptions.
Anomaly Detection
Anomaly detection involves identifying deviations from expected network behavior, which can signal performance degradation, security incidents, or device malfunctions.
How IP addressing supports anomaly detection:
- Unexpected Traffic from an IP: If an IoT device’s IP address suddenly starts communicating with unusual destinations or sending unusually large volumes of data, it could indicate a compromise or a misconfiguration.
- Communication with Blacklisted IPs: Detecting attempts by IoT devices to communicate with known malicious IP addresses or C2 (command and control) servers is a critical security alert.
- Unusual Port Activity: An IoT device typically communicates on a limited set of ports. Activity on unexpected ports originating from or directed to an IoT device’s IP is suspicious.
- IP Spoofing: Monitoring systems can detect attempts by malicious actors to impersonate legitimate IoT devices by using their IP addresses.
- Geographical Anomalies: If an IoT device that is physically located in one region suddenly appears to be communicating from an IP address associated with a completely different geographical location, it’s a strong indicator of a potential security breach or IP address spoofing.
- Sudden Increase/Decrease in Connected Devices (by IP): A sudden, unexplained change in the number of unique IP addresses active on an IoT network segment might indicate device failures, unauthorized device insertions, or network issues.
By integrating IP addressing information into comprehensive monitoring and analytics platforms, organizations can gain deep insights into their IoT deployments, ensuring optimal performance, proactively addressing issues, and maintaining a robust security posture against evolving threats.
Critical Engineering Considerations for Robust IoT Architectures
As billions of devices connect to the internet, building scalable, secure, and resilient IoT architectures requires foresight and adherence to best practices in IP management.
IPv6 Adoption: A Mandate for Future-Proofing
The era of relying solely on IPv4 for massive IoT deployments is rapidly drawing to a close. IPv6 adoption is not merely an option but a critical engineering consideration for any organization planning for long-term scalability and efficiency.
Why IPv6 is Indispensable for IoT:
- Infinite Address Space: As discussed, IPv6 provides an unimaginable number of unique addresses, ensuring that every single IoT device, no matter how small or numerous, can have its own globally routable IP address. This eliminates the complexities and limitations introduced by NAT.
- End-to-End Connectivity: With native IPv6, every IoT device can communicate directly with any other device or service on the internet, simplifying architecture, enabling true peer-to-peer communication, and making remote management far more straightforward.
- Simplified Network Configuration: IPv6 supports stateless address auto-configuration (SLAAC) and DHCPv6, simplifying device onboarding and network management.
- Built-in Security (IPsec): IPsec is an integral part of the IPv6 protocol suite (though optional in IPv4). This means that strong encryption and authentication capabilities are inherent to IPv6 communication, enhancing overall IoT security.
- Efficient Routing: IPv6 headers are simpler and more efficient than IPv4 headers, leading to faster processing by routers and improved routing performance, which is beneficial for latency-sensitive IoT applications.
- Multicast Capabilities: Enhanced multicast support in IPv6 is excellent for group communication among IoT devices, enabling efficient distribution of data or commands to many devices simultaneously.
Organizations must actively plan their IPv6 transition strategies, which often involve dual-stack deployments in the short to medium term, gradually phasing out IPv4 components as infrastructure and devices become IPv6-native.
Subnet Planning: Organizing the Digital Estate
Effective subnet planning is analogous to urban planning for your digital cities (IoT networks). Just as well-planned city blocks improve traffic flow and resource distribution, well-designed subnets optimize network performance, enhance security, and simplify management.
Principles of Effective Subnet Planning for IoT:
- Logical Segmentation: Divide the larger IP address space (especially IPv6) into smaller, manageable subnets based on:
- Geographical Location: Separating devices in different buildings, cities, or regions.
- Device Type: Grouping similar devices (e.g., all smart streetlights in one subnet, all industrial robots in another).
- Functionality: Separating devices based on their role (e.g., sensors, actuators, control devices).
- Security Zones: Creating highly isolated subnets for critical devices or those handling sensitive data. This is where Zero Trust principles can be applied effectively.
- Right-Sizing Subnets: Allocating enough IP addresses within each subnet to accommodate current and future device growth, but not so many that the subnet becomes unmanageable or wasteful of address space (less of an issue with IPv6, but still good practice for clarity).
- VLSM (Variable Length Subnet Masking): For IPv4, using VLSM allows for more efficient use of the limited address space by creating subnets of varying sizes. While less critical for IPv6 due to its abundance, logical structuring remains important.
- Security by Design: Subnets are a fundamental tool for implementing network segmentation and microsegmentation. Firewall policies can be
applied at subnet boundaries to control traffic flow between different IoT segments, limiting lateral movement of attackers. - Ease of Management: A well-structured subnet scheme makes it easier to assign and track IP addresses, troubleshoot network issues, and apply consistent security policies across groups of devices.
- Scalability: Planned subnets should allow for future expansion without requiring a complete re-architecting of the IP address scheme. IPv6’s enormous address space makes this much simpler, as you can allocate very large prefixes for your entire IoT domain and then easily subdivide them.
For IPv6, a common practice is to allocate /64 prefixes to individual subnets, as this aligns with Stateless Address Autoconfiguration (SLAAC) and typically provides ample addresses (264 addresses per segment) for even the largest IoT clusters within a local segment.
Secure IP Management: The Core of IoT Resilience
Beyond just assigning IP addresses, the entire lifecycle of IP address management (IPAM) needs to be secure and well-governed.
Key Aspects of Secure IP Management:
- Centralized IP Address Management (IPAM) System: A dedicated IPAM solution is crucial for tracking and managing all assigned IP addresses, available pools, subnet allocations, and associated metadata (e.g., device type, location, owner). This prevents duplicate assignments and provides a single source of truth for network configuration.
- Access Control and Authentication: Strict access controls must be in place for IPAM systems and network infrastructure devices (routers, switches, DHCP/DNS servers). Only authorized personnel should be able to modify IP configurations or view sensitive network topology information.
- Network Access Control (NAC): Implementing NAC solutions ensures that only authorized and compliant IoT devices are allowed to connect to the network and obtain an IP address. NAC can verify device identity, software versions, and security posture before granting network access.
- DNS Security (DNSSEC): DNS (Domain Name System) translates human-readable domain names (e.g.,
iotworlds.com) into IP addresses. Protecting DNS from manipulation is critical. DNSSEC adds cryptographic signatures to DNS data, ensuring the authenticity and integrity of DNS responses, preventing techniques like DNS spoofing from redirecting IoT traffic to malicious sites. - DHCP Snooping and Dynamic ARP Inspection (DAI): These layer 2 security features help prevent common attacks against IP address allocation:
- DHCP Snooping: Prevents unauthorized (rogue) DHCP servers from assigning IP addresses and ensures that only legitimate DHCP server responses are forwarded.
- Dynamic ARP Inspection (DAI): Protects against ARP (Address Resolution Protocol) spoofing by validating ARP packets, ensuring that the IP-to-MAC address bindings are legitimate.
- Regular Audits and Reviews: Periodically auditing IP configurations, firewall rules, and access logs is essential to identify vulnerabilities, misconfigurations, and suspicious activities.
- Incident Response Planning: Having a clear plan for how to respond to IP-related security incidents (e.g., detecting an IP address conflict due to a malicious device, identifying a compromised device sending traffic to unexpected IPs) is crucial for minimizing downtime and impact.
Strong network fundamentals, rooted in meticulous IP addressing strategies, robust security measures, and diligent monitoring, are not mere technical details; they are the defining characteristics of strong IoT architectures ready to meet the demands of an interconnected world.
Conclusion: Building the Intelligent Future on Solid IP Foundations
The Internet of Things, with its promise of unprecedented automation, intelligence, and data-driven insights, stands on the intricate foundation of IP addressing. As we navigate a world where billions of devices are interconnected, the principles of unique device identification, efficient routing, and secure IP management are not just desirable – they are absolutely critical.
From the transition to the virtually limitless address space of IPv6, which promises direct endpoint communication and simplified architecture, to the rigorous application of subnet planning for organized and secure networks, every aspect of IP addressing forms a crucial layer in the overall resilience and capability of an IoT ecosystem. Without a well-thought-out IP strategy, IoT deployments risk becoming entangled, insecure, and ultimately unable to scale to their full potential.
The journey through the complexities of dynamic and static address allocation, the indispensable role of gateways in routing efficiency, the strategic use of NAT for present-day IPv4 conservation, and the visionary adoption of IPv6 for future-proofing, all underscore a singular truth: Strong network fundamentals define strong IoT architectures.
Moreover, the imperative of security means embedding encryption and stringent firewall policies at every level, controlling access based on IP identities, and relentlessly monitoring network traffic for performance anomalies and potential threats. It’s a continuous cycle of planning, implementation, and vigilance.
At IoT Worlds, we are at the forefront of shaping this intelligent future. Our expertise in crafting robust IP addressing strategies, designing scalable network architectures, and implementing impregnable security measures ensures that your IoT vision is built on the most solid foundations. We empower enterprises to unlock the full potential of their connected devices, turning complexity into seamless operation.
Don’t let IP addressing challenges stand between you and a truly transformative IoT deployment. Partner with IoT Worlds to design, implement, and manage a resilient, secure, and future-proof IoT infrastructure. For a consultation or to learn how we can bring your IoT projects to life, reach out to us today.
Email us at info@iotworlds.com