The industrial landscape is undergoing a profound transformation, driven by the convergence of Artificial Intelligence (AI) and the Internet of Things (IoT). At the heart of this revolution are autonomous agents – intelligent software entities capable of performing tasks, making decisions, and interacting with their environment. As these agents proliferate within manufacturing operations, the concept of identity, access, and governance becomes paramount. This article delves into the critical role of Identity and Access Management (IAM) as a foundational framework for understanding agent identity and explores how agents are fundamentally changing the game, demanding a shift from mere access control to a more nuanced governed agency.
The Foundations of Identity: What IAM Teaches Us
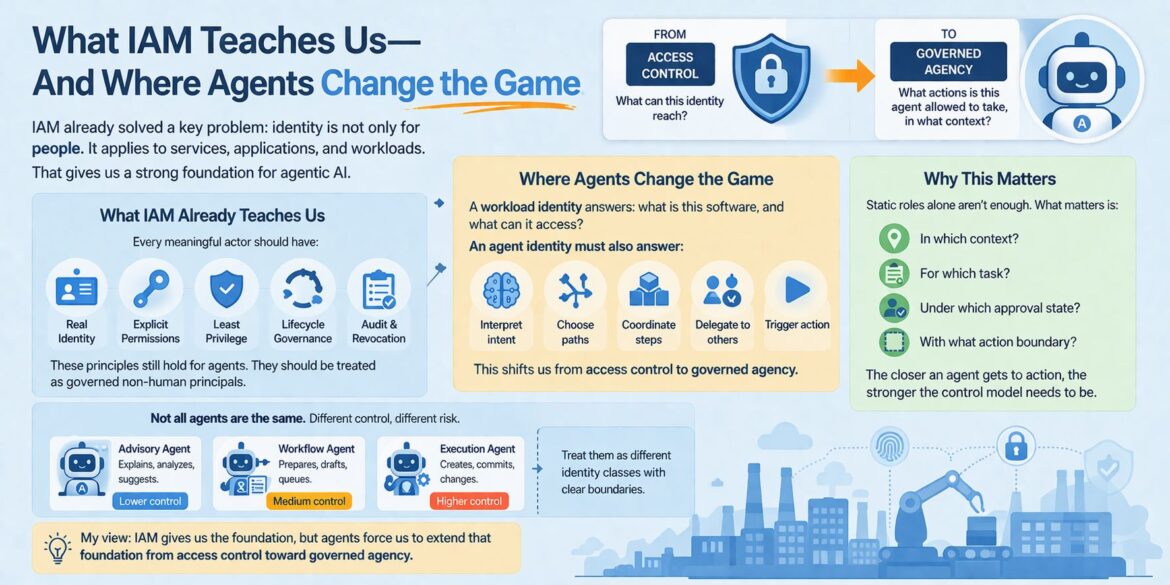
Identity and Access Management (IAM) has long been a cornerstone of cybersecurity and operational efficiency in IT and cloud environments. It has successfully addressed a crucial conceptual challenge: identity extends beyond human users. Services, applications, scripts, and various workloads also require distinct identities for secure and controlled operation. This foundational understanding provides an invaluable starting point for grappling with the complexities of agent identity.
Modern identity platforms already offer robust capabilities that are directly applicable to the emerging world of agentic AI. These include:
- Managed identities: Centralized management of digital identities for non-human entities.
- Federation: Enabling seamless and secure identity sharing across different systems and organizations.
- Access policies: Defining granular rules for what an identity can and cannot do.
- Lifecycle controls: Managing the entire lifespan of an identity, from creation to deactivation.
- Observability: Providing visibility into identity activities and access patterns.
These capabilities form a strong bedrock upon which we can build robust frameworks for managing agent identity.
Fundamental Principles of Identity
IAM has instilled several core principles that remain universally relevant, even in the context of advanced AI agents. Every meaningful actor, whether human or non-human, should adhere to these tenets:
A Real Identity
Just as individuals have unique identifiers, every agent within a manufacturing ecosystem must possess a distinct and verifiable digital identity. This identity serves as its passport, enabling it to be recognized, authorized, and held accountable for its actions. Without a clear identity, agents become anonymous entities, making it impossible to track their activities or attribute responsibilities. In complex manufacturing environments with numerous interconnected agents, maintaining distinct identities is crucial for operational transparency and troubleshooting. Consider an autonomous robotic arm on an assembly line. Its identity isn’t just about its physical presence but its digital signature that allows it to communicate with other machines, access production schedules, and record its work.
Explicit Permissions
Identity alone is insufficient; it must be coupled with explicit permissions. These permissions define the specific actions an agent is authorized to perform and the resources it can access. Generic, broad permissions are a significant security risk, especially in sensitive manufacturing settings. For example, an agent responsible for monitoring temperature in a cleanroom should only have read access to sensor data, not the ability to alter critical environmental controls. Explicit permissions ensure that agents operate within well-defined boundaries, preventing unauthorized actions and mitigating potential damage to production or intellectual property.
Least-Privilege Access
Building upon explicit permissions, the principle of least-privilege access dictates that an agent should only be granted the minimum level of access necessary to perform its designated tasks. This minimizes the attack surface and limits the potential impact of a compromised agent. If an agent only needs to read sensor data, it should not have write access to system configurations. Implementing least-privilege access requires a thorough understanding of each agent’s function and its interdependencies within the manufacturing workflow. This principle becomes even more critical as agents gain more autonomy and the potential for cascading system failures increases.
Lifecycle Governance
Agents, like any other digital entity, have a lifecycle. They are created, deployed, updated, and eventually decommissioned. Effective lifecycle governance ensures that identities and their associated permissions are managed throughout this entire process. When an agent’s role changes, its permissions must be updated accordingly. When an agent is retired, its identity and access rights must be revoked to prevent unauthorized persistence. Neglecting lifecycle governance can lead to orphaned identities that pose security vulnerabilities or operational inefficiencies. In dynamic manufacturing environments where agents are constantly being deployed and reconfigured, robust lifecycle governance is essential for maintaining control and security.
A Clear Path for Audit and Revocation
Accountability is paramount. Every agent’s actions must be auditable, allowing for a clear trail of its activities. This is crucial for compliance, forensic analysis in case of incidents, and performance monitoring. Furthermore, the ability to revoke an agent’s identity and permissions quickly and effectively is a critical safety net. If an agent malfunctions, becomes compromised, or is no longer needed, its access must be terminated immediately to prevent further harm. This swift revocation capability is a non-negotiable security measure, particularly in manufacturing contexts where physical processes and valuable assets are at stake.
These five principles, deeply ingrained in IAM best practices, provide a formidable starting point for governing agent identity. They emphasize that agents are not amorphous features but rather governed non-human principals requiring the same level of scrutiny and control as any other actor in an IT ecosystem.
Where Agents Change the Game: Beyond Access Control
While IAM provides a robust foundation, the advent of AI agents introduces a fundamentally new dimension that transcends traditional access control. A typical workload identity, such as a database service or a microservice, primarily answers two questions:
- What software is this?
- What can it access?
These questions are fundamental to securing systems and data flows. However, an agent identity, by its very nature, demands a deeper level of inquiry:
- What kinds of decisions or actions may this software originate?
This seemingly subtle difference is, in fact, profoundly significant. Agents are designed to be proactive, to interpret, to choose, to coordinate, and to trigger actions. Their role extends beyond mere data retrieval or API calls.
The New Dimensions of Agent Identity
The capabilities of AI agents introduce several critical considerations that extend beyond the traditional scope of IAM:
Interpret Intent
Agents are increasingly capable of understanding and interpreting human intent, even when presented with ambiguous or incomplete instructions. This ability allows them to move beyond rigid, pre-programmed responses and adapt to evolving situations. However, this also raises questions about how well an agent’s interpretation aligns with the user’s or system’s actual intent. How do we ensure that an agent’s understanding of a request leads to appropriate and safe actions? This requires a control model that monitors and, if necessary, intervenes in an agent’s interpretive process.
Choose Paths
Unlike deterministic software that follows predefined execution paths, intelligent agents often have the capacity to choose between multiple courses of action based on their understanding of the environment and their objectives. This decision-making capability is central to their utility. However, it also introduces a need for oversight. How do we ensure that an agent’s chosen path aligns with organizational policies, safety protocols, and ethical guidelines? The control model must encompass the evaluation and governance of these decision-making processes.
Coordinate Steps
Many complex tasks in manufacturing require the coordination of multiple steps and the interaction of various systems. Agents can be designed to orchestrate these complex workflows, delegating tasks and ensuring their sequential or parallel execution. This ability to coordinate introduces a new level of control required over the flow and sequence of operations. It asks whether an agent has the authority to initiate or manage dependencies across different systems.
Delegate to Others
A powerful aspect of agentic systems is their ability to delegate tasks to other agents or systems. An agent identifying a maintenance need might delegate the creation of a work order to another agent, or even directly to a human operator. This delegation capability underscores the interconnectedness of agent ecosystems and the need for a comprehensive identity framework that tracks not only the actions of individual agents but also the delegated actions and their origins.
Trigger Action
Ultimately, the goal of many agents is to trigger actions in the real world – whether it’s adjusting machinery, ordering raw materials, or dispatching maintenance teams. This transition from analysis to action is where the stakes become highest. The control model must be incredibly robust when an agent is empowered to initiate physical changes or significant operational events. This is the difference between an agent providing an alert and an agent initiating a system shutdown.
This fundamental shift from access control to governed agency is not merely a technical extension of existing IAM principles; it represents a conceptual leap. It acknowledges that agents are not passive entities but active participants with varying degrees of autonomy and influence.
Why Static Role Assignment Alone Is Insufficient
In traditional IAM, static role assignments are commonly used to define permissions. A user or service is assigned to a role (e.g., “administrator,” “read-only user”), and that role dictates their access rights. While effective for many scenarios, static role assignment falls short when dealing with the dynamic and contextual nature of agentic AI. What truly matters for an agent is not just whether it has access, but also:
In Which Context?
An agent’s permissions should be highly contextual. An agent might have permission to access sensitive production data during normal operating hours for performance optimization but should be restricted from that same data during system maintenance or in a non-production environment. The context could be time-based, location-based, or dependent on specific operational states. For instance, a quality control agent might have read access to sensor data only when a specific product batch is active on a particular production line.
For Which Task?
An agent’s purpose directly defines its necessary permissions. An agent tasked with anomaly detection needs read access to real-time sensor data but does not require write access to control systems. Conversely, an agent responsible for executing repair orders needs specific write permissions to control machinery. Defining permissions based on specific tasks ensures a more granular and secure control model. This is especially relevant in manufacturing where tasks are highly specialized.
Under Which Approval State?
Many critical actions in manufacturing require human oversight and approval. An agent might propose a change to a production parameter, but that change should only be executed after explicit human approval. The control model must incorporate approval workflows, ensuring that agents do not bypass necessary human checks and balances. This prevents unintended consequences and maintains a crucial human-in-the-loop for high-stakes decisions.
With What Action Boundary?
This refers to the permissible scope and scale of an agent’s actions. An agent might be allowed to adjust a minor parameter within a narrow range but not to initiate a major system reconfiguration. Defining clear action boundaries is crucial for preventing agents from exceeding their intended operational remit. For example, a temperature control agent might be allowed to adjust a thermostat within a safe operating range, but not to shut down the entire HVAC system.
The closer an agent gets to originating action, the stronger and more sophisticated the control model needs to become. This is where the distinction between different types of agents becomes critical.
The Spectrum of Agent Control and Risk
Not all agents are created equal, and their level of autonomy and potential impact varies significantly. Understanding this spectrum is crucial for designing appropriate governance frameworks.
Advisory Agents
These agents operate at the lowest end of the control and risk spectrum. Their primary function is to explain, analyze, and suggest. Examples include an agent that analyzes production data to identify inefficiencies, an agent that predicts potential equipment failures, or an agent that offers recommendations for optimizing energy consumption. These agents provide insights but do not directly trigger actions. Their control requirements are primarily focused on data access and ensuring the accuracy and integrity of their analyses. The risk associated with these agents is relatively low, as their output is typically reviewed by a human before any action is taken.
Workflow Agents
Workflow agents occupy the middle ground. They are designed to prepare, draft, and queue actions. This could include an agent that drafts a maintenance request based on sensor readings, an agent that queues a batch of new production orders, or an agent that initiates a data backup process. While they don’t directly execute changes, they set the stage for actions to occur. Their control requirements are higher than advisory agents, as their actions directly impact subsequent steps in a workflow. The risk is medium, as their outputs will typically undergo further review or approval before execution.
Execution Agents
At the highest end of the control and risk spectrum are execution agents. These agents are empowered to create, commit, and change systems directly. Examples include an agent that autonomously adjusts machine settings based on real-time feedback, an agent that commits a completed production batch to inventory, or an agent that automatically reorders raw materials when stock levels fall below a certain threshold. These agents operate with significant autonomy and directly impact physical processes or critical data. Their control model must be exceptionally robust, incorporating stringent safeguards, approval mechanisms, and real-time monitoring. The risk associated with execution agents is significant, as a malfunction or compromise could lead to production disruptions, safety hazards, or substantial financial losses.
It is imperative to treat these different identity classes with clear boundaries. A unified, one-size-fits-all approach to agent governance is insufficient and introduces unnecessary risks. Instead, a finely tuned framework that accounts for the varying degrees of autonomy, impact, and risk associated with each agent type is required.
An agent that merely explains an alarm is fundamentally different from an agent that automatically creates a work order, which in turn is vastly different from an agent that commits changes to the production schedule. Overlooking these distinctions in generic AI discussions can lead to underestimating risks and implementing inadequate control mechanisms. This becomes particularly critical when agents transition from purely conversational roles into operational ones, directly influencing the physical world of manufacturing.
The Imperative for Governed Agency in Manufacturing
The manufacturing sector stands to gain immensely from the integration of AI agents, promising increased efficiency, reduced downtime, optimized resource utilization, and enhanced quality control. However, these benefits can only be fully realized—and sustained—if agent deployments are underpinned by a robust framework of governed agency. The complexities and potential high stakes in manufacturing operations elevate the need for precise control and oversight beyond that of many other enterprise settings.
Operational Criticality and Real-World Impact
Manufacturing environments are characterized by complex, interconnected systems where a single anomaly or misstep can have cascading consequences. A malfunctioning agent in a financial system might lead to data errors; in manufacturing, it could result in:
- Production Stoppages: An agent errantly altering machine parameters could halt an entire assembly line, leading to significant financial losses and missed deadlines.
- Safety Hazards: An agent controlling robotics or critical infrastructure without proper governance could create dangerous situations for human workers.
- Quality Defects: An agent making unsupervised adjustments to a process could lead to the production of faulty goods, resulting in scrap, rework, and reputational damage.
- Supply Chain Disruptions: An agent incorrectly triggering orders or managing inventory could throw off supply chain logistics, impacting both upstream and downstream partners.
Given these real-world, tangible risks, the shift from mere access control to comprehensive governed agency is not just a best practice; it is an operational imperative.
The Problem of Context and Consequence
In manufacturing, the context of an action is often as important as the action itself. An agent might be authorized to send an alert under normal operating conditions, but the same alert, if sent during a critical system update, could be misinterpreted or cause further issues. Governed agency ensures that an agent’s actions are not only permissible what but also appropriate when and where.
Moreover, manufacturing systems frequently operate under strict regulatory and compliance frameworks (e.g., ISO standards, industry-specific safety regulations). An agent’s actions must be traceable, auditable, and demonstrably compliant. Governed agency provides the mechanisms to track agent decisions and actions, ensuring adherence to mandates and simplifying compliance reporting.
Beyond Role-Based Access: The Need for Dynamic Policies
Traditional Role-Based Access Control (RBAC) often struggles with the dynamic nature of agents. An agent’s function might evolve, its responsibilities might shift temporarily, or its operating environment might change. Static roles may not capture these nuances effectively.
Governed agency, in contrast, promotes a more dynamic policy-driven approach. This involves:
- Behavioral Models: Defining acceptable behavioral patterns for agents, going beyond simple access lists to include expected sequences of operations, decision-making logic, and communication protocols.
- Runtime Evaluation: Continuously evaluating an agent’s actions against defined policies and context in real-time. This allows for immediate intervention if an agent deviates from its authorized behavior or attempts an action outside its current context.
- Feedback Loops: Integrating feedback mechanisms where human operators or oversight systems can review agent decisions and actions, providing a layer of human intelligence and accountability. This also allows for the refinement of agent policies over time.
- Threat Detection and Response: Establishing robust systems to detect anomalous agent behavior that might indicate a compromise or malfunction. Governed agency implies the ability to isolate, suspend, or revoke an agent’s privileges instantaneously if suspicious activity is detected.
The Challenge of Interacting Agents and Swarm Intelligence
Modern manufacturing is increasingly leveraging systems where multiple agents interact and cooperate to achieve common goals (swarm intelligence). In such environments, the identity and governance of individual agents must be considered in relation to the collective. What happens if one agent in a swarm misinterprets an instruction, leading to a cascade of incorrect actions by others? Governed agency needs to extend to the interaction patterns and collective decision-making processes of agent swarms, ensuring that the overall system remains within controlled boundaries.
The Path Forward: Building on IAM for Agentic AI
The journey towards fully realized, secure, and efficient agentic AI in manufacturing will involve a continuous evolution of our identity and access management paradigms. What IAM has taught us about non-human identities, explicit permissions, least privilege, lifecycle governance, and audit trails provides an indispensable springboard.
However, the unique characteristics of AI agents — their ability to interpret, choose, coordinate, delegate, and trigger actions — demand an extension of this foundation. We must move beyond simply controlling what an agent can reach to governing what actions it can originate, in which context, for which task, under which approval state, and with what action boundary.
This proactive approach to agent identity security will differentiate leading manufacturers, allowing them to harness the transformative power of AI agents while mitigating the inherent risks. It will enable the creation of intelligent, autonomous systems that are both highly efficient and demonstrably safe, reliable, and compliant. The future of manufacturing is undeniably agent-driven, and the key to unlocking its full potential lies in mastering the art of governed agency.
Call to Action
Unlock the full potential of AI agents in your manufacturing operations with expert guidance. For tailored solutions in agent identity, access control, and governed agency, designed to secure and optimize your industrial processes, contact us today.
Email us at info@iotworlds.com to schedule a consultation and transform your manufacturing future.